Pentest, or pentesting or penetration testing, is a simulated cyberattack carried out by security professionals to identify exploitable vulnerabilities in your systems before real threat actors do.
The goal is to find weaknesses and show how far a threat actor could get if they found vulnerabilities first.
This distinction is what separates pentesting from vulnerability scanning. For example, a vulnerability scanner can only flag that your server is running an outdated version of OpenSSL, while pentesting will use that vulnerability as a foothold to see what else they can reach.
In simple terms, penetration testing can demonstrate how much damage a vulnerability could cause by providing a PoC.
Also, people often mix up both penetration testing and ethical hacking, but they’re entirely different. Ethical Hacking is a broader discipline that involves using offensive security skills to detect security gaps. Penetration testing is just one of the methods ethical hackers use as part of offensive security.
Why Do Companies Need Penetration Testing?
The honest answer depends on what they are actually trying to learn. If the question is “do we have unpatched systems?” an automated scanner answers that. If the question is “could an attacker breach us, and how far could they get,” then pentest is the solution that answers that. There are six reasons we consistently see organizations move from vulnerability scanning to penetration testing.
Detecting Exploitable Vulnerabilities
Automated vulnerability scanners are signature-based and dependency-oriented. They excel at identifying known CVEs and performing basic vulnerability chaining within a narrow scope, but fundamentally lack the ability to reason about emergent attack paths that require deep contextual correlation across multiple environments.
A skilled penetration tester, however, can combine a misconfigured IAM role with an exposed Instance Metadata Service (IMDS) endpoint to achieve full AWS account compromise, a complex attack path that automated tools typically fail to detect.
Third-Party Integration Risk Assessment
According to Verizon’s 2025 Data Breach Investigations Report, third-party breaches now account for almost 30% of all breaches. Penetration testing now plays a vital role in assessing the security of partner integrations and vendor-provided SaaS connectors. It identifies transitive trust weaknesses where a compromise in a seemingly low-risk third-party component can lead to full internal network access or sensitive data leakage.
Identifying Detection Gaps
Penesters actively try to bypass next-gen EDR/XDR solutions, web application firewalls, deception technologies, and SIEM correlation rules by various methods. In the end, it will expose blind spots in detection engineering and help security teams understand real dwell time and alert fatigue in their environment.
Achieving Compliance
PCI DSS 4.0 (Requirement 11.4), SOC 2 Type II, ISO 27001 Annex A, and HIPAA’s technical safeguard provisions carry explicit or implicit requirements for penetration testing. For organizations operating in financial services or healthcare, pen testing is an audit line item with contractual and legal consequences if absent.
Breach Economics
Typically, a web application pentest costs between $6,000 to $25,000, depending on scope and methodology. The average cost of a data breach across all industries is $4.88 million. There have been many instances where organizations paid six-figure regulatory fines for vulnerabilities that would have been found and fixed in a two-week pentest engagement.
Beyond direct costs, a breach is operationally catastrophic and could put the company in crisis mode for weeks.
Strict procurement condition
Enterprise security questionnaires now routinely include fields for penetration test date, methodology, scope, and findings severity distribution. Procurement and vendor security review teams at banks, healthcare systems, and large enterprises have made it a standard vendor qualification requirement.
Post-SolarWinds, security-conscious buyers understand that a vendor’s security posture is part of their own attack surface.
What are the types of Penetration Testing?
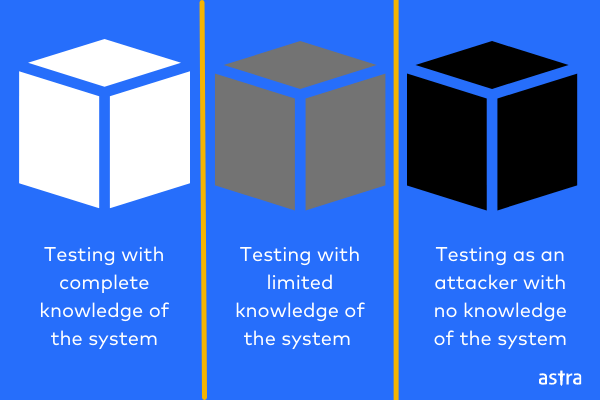
Penetration testing is classified in two ways: knowledge level (Black Box, White Box, Gray Box) and target-based. In this section, we’ll discuss the target-based categorization.
Target-based penetration testing categorizes tests according to the specific asset, system, or environment being assessed. Each type focuses on unique attack surfaces, tools, and vulnerabilities.
1. Cloud Penetration Testing
Cloud penetration testing analyzes the cloud computing environment for vulnerabilities that hackers could exploit. Based on the service model, cloud pentesting can be divided into three categories: Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and Software as a Service (SaaS).
- IaaS cloud pentesting evaluates cloud infrastructure assets, storage, and networks.
- PaaS pentesting assesses runtime environments, development tools, and databases.
- SaaS pentesting checks how the application stores data, transmits information, and checks how it authorizes users.
2. Network Penetration Testing
A network penetration test aims to find vulnerabilities in the network infrastructure, either on-premise or in cloud environments such as Azure and AWS. Penetration testing evaluates a wide range of areas, such as configurations, encryption, and outdated security patches.
3. API Penetration Testing
An Application Programming Interface (API) is a set of standards that lets applications communicate with each other. As such, API penetration testing helps find vulnerabilities that could result in attackers getting unauthorized access to data or functions.
4. Mobile Penetration Testing
Expert penetration testers test mobile applications to find security vulnerabilities which can then be reported to the developers. Mobile pentesting applies to Android, iOS, Native, and Hybrid applications.
5. Wireless Penetration Testing
Wireless pen testing evaluates the security of Wi-Fi networks, Bluetooth, and other RF-based communication channels. Pentesters assess encryption standards (WEP/WPA2/WPA3), test for susceptibility to rogue access points, evaluate SSID isolation controls, and simulate evil twin attacks.
Poorly secured wireless networks can bypass entire perimeter defenses, granting attackers direct access to internal segments, making this a critical component of any physical office or campus security assessment.
Penetration Testing Methodologies
Penetration testing methodologies are primarily differentiated by how much information and access the tester starts with. Choosing the right methodology directly impacts the quality and relevance of findings.
Black Box Pentest
Black-Box Pen test is a type of penetration testing in which the pentester has no prior knowledge or access to the target system. The pentester starts only with the target organization’s name, ROE, and the defined scope. All reconnaissance is conducted from public sources (e., OSINT, subdomain enumeration, etc).
A black box is the most faithful simulation of an opportunistic hacker. It validates what your perimeter looks like to someone who has never touched your systems before and surfaces internet-facing security gaps.
Its limitation is that a fraction of the engagement timeline is spent on recon, while a threat actor would skip it and gain access through phishing or other methods(e.g, data leaks).
Gray Box Pentest
Gray box pentest is a methodology in which the tester receives partial but legitimate access. This is the most realistic and effective methodology for modern web, mobile, and cloud applications. It applies adversarial pressure directly to the attack surface where most real-world breaches happen.
Its limitation is that it starts from a position of legitimate access. It will miss vulnerabilities that exist at the code level.
White Box Pentest
White-Box Pen test is a type of penetration testing in which the tester has full knowledge and complete access to the target, including source code, architecture, credentials, and internal documentation.
Pentesters here employ static analysis (SAST), dynamic analysis (DAST), and deep manual code review to identify implementation-level vulnerabilities. White box delivers the highest depth and coverage of any methodology.
Its limitation is realism. A white box pentest does not tell you what an external attacker would find or how quickly they would find it.
If your requirement is to understand external exposure or validate perimeter defenses, a white-box pentest alone does not meet that need.
Pro Tip: For most SaaS and cloud-native products, a gray-box approach should be the baseline methodology, as it offers the best balance of realism and thoroughness. Supplement it with white-box pentesting for high-risk modules, e.g., authentication systems, billing engines etc
Pentesting vs. Vulnerability Assessment
A Vulnerability Assessment (VA) and a Penetration Test (PT) are two essential but fundamentally different approaches to evaluating security posture.
A Vulnerability Assessment is primarily an automated, broad-scope process that scans systems, networks, applications, and cloud assets for known vulnerabilities. In contrast, a Penetration Test is a targeted, adversarial simulation. Pentesters combine automated tools with manual exploitation techniques to actively breach systems.
| Dimension | Vulnerability Assessment | Penetration Test |
|---|---|---|
| Method | Primarily automated scanning (authenticated & unauthenticated) | Automated scanning + manual exploitation & chaining |
| Scope | Broad asset discovery & enumeration | Targeted attack simulation across specific vectors |
| Depth | Known CVEs, misconfigurations, and version detection (banner grabbing) | Known + zero-day style exploits, business logic flaws, custom payloads |
| False Positives | High (relies on signature/version matching) | Very Low (proof via successful exploitation) |
| Output | Structured vulnerability list (CVE, CVSS v3.1, EPSS, remediation priority) | Detailed attack narrative, kill chain (MITRE ATT&CK), screenshots, PoC exploits, risk impact |
| Frequency | Continuous/weekly/monthly | Quarterly, bi-annual, or continuous (PTaaS) |
| Compliance Value | Good supporting evidence | Formally accepted by PCI-DSS, SOC 2, HIPAA, ISO 27001, FedRAMP |
In simpler term
- VA focuses on “what’s vulnerable,” while PT answers “what can an attacker actually do?”
- VA offers wide coverage with higher false positives; PT provides deeper validation with actionable intelligence.
Pro Tip: Use regular Vulnerability Assessments for continuous monitoring. Perform Penetration Tests (or PTaaS) quarterly/annually to validate defenses, meet strict compliance (PCI-DSS, SOC 2, HIPAA), and uncover hidden risks that scanners miss. Together, they form a complete security assessment strategy.
The Penetration Testing Process
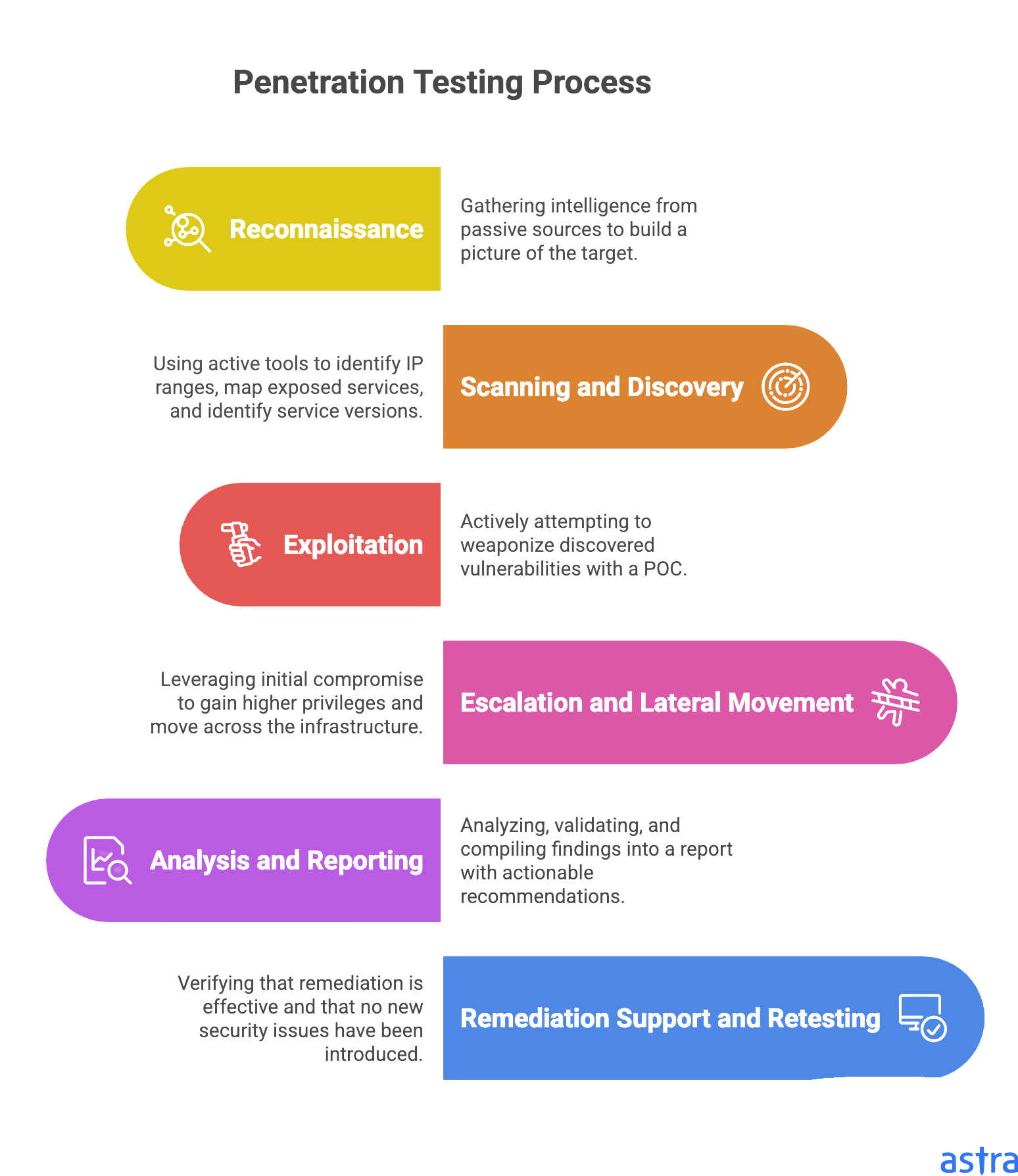
A penetration test is a structured exercise where a skilled pentester pokes at a target until they find something. It follows a defined methodology that mirrors how real threat actors operate, because replicating the adversary’s workflow is the only way to surface the vulnerabilities that actually matter.
Every phase has a specific technical objective, and the output of each phase shapes the work of the next.
Step 1: Reconnaissance
Before any active probing begins, pentesters put significant time into gathering intelligence from passive sources. The goal is to build a complete picture of the target’s attack surface(e.g, what is exposed, what technology stack is in use, etc.) without touching the target systems in any way that would trigger alerts.
For an external engagement, this means subdomain enumeration using passive DNS sources, certificate transparency logs (crt.sh, Censys), and permutation-based tooling like Amass.
Even GitHub and GitLab scraped to find accidentally committed AWS keys, database credentials, and internal API tokens.
Did you know? LinkedIn is often scraped during the reconnaissance phase by pentesters to identify the technology stack and extract information about the architecture mentioned in job postings.
Step 2: Scanning and Discovery
After passive reconnaissance is completed, pentesters move to active discovery. In this step, Nmap or similar tools are used to identify IP ranges, map exposed services, and identify service versions. Service fingerprinting is performed to determine what is actually running on each port and whether the version has known exploitable vulnerabilities.
This phase is where pentesters start forming hypotheses.
For example, an nginx server returning a different response time on certain paths than others suggests there may be a backend service worth probing.
An API endpoint present in the Swagger UI but absent from the official developer documentation suggests it was intended to be internal.
Step 3: Exploitation
In the exploitation phase, pentesters actively attempt to weaponize the vulnerabilities discovered during the previous phases with a POC. This stage involves crafting and sending payloads to the target to achieve specific objectives.
The goal is to demonstrate the real-world business impact of the vulnerability while staying within the ROE defined in the scope.
A classic example in cloud environments is exploiting an SSRF (Server-Side Request Forgery) vulnerability. Pentesters test it by forcing the vulnerable server to make a request to AWS’s Instance Metadata Service (IMDS) using the internal link-local address:
http://169.254.169.254/latest/meta-data/iam/security-credentials/If the SSRF is successful, the application will return the list of IAM role names attached to the underlying EC2 instance.
This confirms two critical things:
(1) the server can reach the AWS metadata service, and
(2) An IAM role is attached to the instance.
Attackers then follow up by requesting the full temporary credentials using the role name:
http://169.254.169.254/latest/meta-data/iam/security-credentials/<role-name>This typically returns JSON containing the AccessKeyId, SecretAccessKey, and Token.
Step 4: Escalation and Lateral Movement
After achieving initial access, the next question is always: how much further can we go? This phase involves leveraging the initial compromise to gain higher privileges and move across the infrastructure.
In a web application context, this means moving from a standard user account to an administrative account, from one tenant’s data to another’s, from read access to write access, from application-level access to infrastructure-level access.
Continuing the SSRF Example from the Exploitation Phase:
Once the SSRF vulnerability successfully returns AWS IAM role credentials from the metadata service (http://169.254.169.254/latest/meta-data/iam/security-credentials/<role-name>), the pentester now possesses temporary but powerful AWS access keys. These credentials are then used outside the original vulnerable application with the AWS CLI or SDK to begin privilege escalation and lateral movement.
Common follow-on actions include enumerating S3 buckets, listing IAM policies to understand permissions, accessing other EC2 instances via Systems Manager, or even creating new resources for persistence.
In many cases, the stolen role has broad permissions (e.g., AdministratorAccess or PowerUser), turning a single SSRF into full account compromise.
This phase demonstrates the real business risk: a single SSRF vulnerability on a web app can lead to full cloud account takeover.
Step 5: Analysis and Reporting
After the active pentesting phase concludes, findings are analyzed, validated, and compiled into a report. Every finding includes a technical description of the vulnerability and exactly how it was exploited, a step-by-step reproduction procedure with specific request payloads, response content, and tool commands that let a developer reproduce the issue in their local environment.
In this phase, all findings are thoroughly analyzed, validated, de-duplicated, and prioritized based on severity and business impact. The raw technical results are then transformed into clear, actionable intelligence that both technical teams and management can understand.
Every finding in the report contains the following details:
- A clear technical description of the vulnerability.
- The exact exploitation process, including how it was chained with other issues.
- Step-by-step reproduction instructions with specific request payloads, HTTP requests, response content, tool commands (e.g., curl, AWS CLI, Burp Repeater), and screenshots.
- Business and technical impact assessment.
- Risk severity rating (Critical, High, Medium, Low) with CVSS score where applicable.
- Actionable remediation recommendations with secure code examples or configuration fixes.
At Astra Security, we go one step further. We map all identified vulnerabilities to relevant compliance standards and regulatory frameworks (such as ISO 27001, SOC 2, PCI-DSS, GDPR, HIPAA, etc.). This helps organizations understand exactly which security gaps are preventing them from achieving or maintaining compliance.
The goal of this phase is to provide a comprehensive document that drives effective remediation and strengthens the overall security posture of the application.
Step 6: Remediation support and Retesting
Once the client implements fixes for the reported vulnerabilities, the final phase focuses on verifying that the remediation is effective. In this stage, pentesters re-test every finding to confirm that the vulnerability has been properly resolved and that the fix does not introduce new security issues.
A common challenge in this phase is the use of incomplete fixes or workarounds.
For example, devs may patch the single SQL injection instance that was demonstrated without addressing the broader insecure query construction patterns across the codebase.
Also, rate limiting is applied only to the specific endpoint exploited in the current engagement, leaving functionally equivalent endpoints handling the same operation.
At Astra Security, after the client marks a finding as remediated, our team performs thorough retesting of each issue. We confirm that the specific exploit path is closed and check for common incomplete-fix patterns.
Our PTaaS (Penetration Testing as a Service) model transforms this into a continuous cycle rather than a one-time event. Clients receive ongoing security testing that runs in parallel with their development cycles, a collaborative findings platform that integrates directly into engineering ticketing systems (Jira, Linear, etc.), and retesting is included as a standard part of the engagement.
Best Penetration Testing Tools
Kali Linux
Kali Linux is the de facto standard operating environment for penetration testers. It’s a Debian-based Linux distribution maintained by Offensive Security that ships with over 600 security tools preinstalled. Every competent pentester works in Kali or an equivalent custom environment.
Metasploit Framework
Metasploit is a penetration testing framework that maintains a library of exploit modules, payloads, and post-exploitation capabilities. It allows testers to rapidly confirm and demonstrate the exploitation of known CVEs without writing custom exploit code from scratch.
Metasploit is most useful for demonstrating the exploitability of known CVEs quickly and for post-exploitation workflows in network pen testing. The interesting web application findings, e.g., IDOR, broken auth, and business logic flaws, do not come from Metasploit. Those require manual testing with Burp Suite and custom tooling.
Nmap
Nmap sends crafted IP packets to target hosts and analyzes responses to map live hosts, open ports, running services, service versions, and probable operating systems across an entire network range. Its scripting engine, NSE, extends it with hundreds of scripts covering service enumeration, vulnerability detection, and targeted exploitation of specific misconfigurations.
Hydra
Hydra is a parallelized login cracker that supports a wide range of protocols: HTTP, HTTPS, FTP, SSH, SMB, RDP, database services, VoIP, and many others. In a penetration test, it is used to confirm whether an authentication interface has rate limiting and account lockout controls in place.
Burp Suite Professional
Burp Suite is the primary platform for web app pentest. Burp Suite operates as an intercepting proxy between the browser and the target application, allowing the tester to inspect, modify, and replay every HTTP/S request in real time. The majority of manual web application testing, business logic analysis, and authorization boundary testing runs through Burp across its core modules:
- Repeater resends and modifies individual requests with precise payload control, used for manual injection testing.
- Intruder automates parameterized attack sequences across defined input positions for brute force attacks.
- Scanner runs active and passive automated detection across the full OWASP Top 10 and common misconfigurations.
- Sequencer analyzes the statistical randomness of session tokens and CSRF identifiers to assess predictability and exploitability.
Wireshark
Wireshark captures and analyzes network traffic at the packet level, allowing testers to inspect exactly what is transmitted over the wire. It is very helpful in wireless penetration testing to capture the WPA2 four-way handshake for offline cracking, detecting cleartext credential transmission, and identifying protocol-level weaknesses.
It is also used in IoT Pentesting for analyzing proprietary protocol implementations and in internal network assessments for passive traffic analysis to identify sensitive data traversing the network without encryption.
How Penetration Testing and Compliance are Related?
Cybersecurity penetration testing and compliance are closely related. Every major compliance framework now mandates or strongly implies penetration testing in some form. Penetration testing (pen test) is one of the key ways organizations prove that their security controls actually work, which is a core requirement in most compliance frameworks.
PCI DSS v4.0
PCI DSS has the most explicit penetration testing requirements of any major compliance framework. Requirement 11.4.1 mandates that organizations define and implement a penetration testing methodology, conduct both external and internal testing at least once every 12 months and after any significant infrastructure or application change, and ensure every engagement covers both the network layer and the application layer.
Requirement 11.4.3 covers external penetration testing as a distinct and separately documented obligation, while Requirement 11.4.4 covers internal penetration testing with equal specificity.
HIPAA
The HIPAA Security Rule at 45 CFR §164.308(a)(8), the Evaluation standard, requires covered entities and business associates to perform periodic technical and non-technical evaluations in response to environmental or operational changes affecting the security of ePHI. The regulation does not use the words penetration testing, but it’s the only way to perform an evaluation of the security.
It’s important to note that OCR has levied fines exceeding one million dollars against healthcare organizations specifically for inadequate security testing programs, and there are some reports saying HIPAA gonna mandate pentesting sooner.
SOC 2 Type II
SOC 2 does not name penetration testing explicitly anywhere in the Trust Services Criteria, but the expectation has become effectively mandatory in practice for any organization pursuing Type II certification with a rigorous audit firm. CC7.1 requires that organizations monitor system operations to detect and respond to threats; CC6.1 requires that logical access controls operate as intended and be actively maintained; and CC6.8 requires controls to prevent unauthorized software from being installed and executed. Demonstrating any of these controls to an auditor without producing evidence of active pentesting has become increasingly difficult, as auditors now expect technical validation rather than paperwork.
GDPR
GDPR Article 32(1)(d) requires data controllers and processors to implement a process for regularly testing, assessing, and evaluating the effectiveness of technical and organizational measures for ensuring the security of processing. The language does not specify penetration testing by name, but requires a process that produces verifiable evidence that security controls actually work under realistic conditions. To produce verifiable evidence, penetration testing is the only solution.
Local Regulations
Apart from federal frameworks, state-level laws also mandate pentesting in some form. Regulators at every level have reached the same conclusion that a security program without active adversarial testing (pentesting)cannot credibly claim to be compliant.
Key examples include:
- 23 NYCRR 500 (NYDFS) – Requires annual penetration testing and bi-annual vulnerability assessments
- CCPA and CPRA (California) – Tie reasonable security to NIST standards that include penetration testing.
- Australia’s APRA CPS 234 and GCC cybersecurity frameworks have all moved toward explicit or strongly implied penetration testing requirements in recent regulatory cycles.
How to Choose a Penetration Testing Provider?
The quality difference between penetration testing providers is huge, often bigger than in any other cybersecurity service. Two firms can pentest the same application simultaneously and deliver dramatically different results in depth, accuracy, and business value.
Unfortunately, this gap isn’t visible during the sales conversation. So here are some tips that can help you in identifying and choosing a better pentester vendor in the market.
1. Demand Evidence of Manual Pentesting
Automated scanning rebranded as a penetration test is a common and profitable practice. Ask explicitly what percentage of the engagement timeline is manual testing versus automated tooling, and ask what the manual testing covers that the automated tooling does not.
If the answer is vague or the provider cannot describe specific manual techniques they use for business-logic testing or authorization boundary validation, the engagement will not uncover the findings that matter.
2. Ask Hard Questions About Remediation Support
What happens after the report is delivered? Can developers ask the testing team direct questions about specific findings? Is retesting included in the engagement fee, or is it an additional cost? These questions separate providers oriented toward outcomes from those oriented toward deliverables.
Some firms simply hand over the report and disappear. Strong post-engagement support is a clear sign of a mature and client-focused penetration testing provider.
3. Prioritize Industry-Specific Experience
Prioritizing industry-specific experience is critical for achieving ROI from penetration testing. A provider good at pentesting networks or e-commerce websites may lack the expertise needed for modern multi-tenant SaaS platforms or cloud-native applications.
Ask for examples of similar applications or industries they have tested recently. Providers familiar with your tech stack (e.g., React + Node.js, Kubernetes, serverless) will know the common pitfalls and attack vectors specific to your architecture. This knowledge and experience often lead to the discovery of high-impact vulnerabilities that generalist testers frequently miss.
Always align the provider’s expertise with your actual product and environment.
Final Thoughts
Penetration testing is a century-old art of testing ourselves like enemies before facing them. From the Prussian Kriegsspiel, a tabletop wargame that exposed critical security gaps and helped Prussia decisively defeat France in 1870, the practice of attacking your own defenses under controlled conditions spread across every domain. Eventually, this proven philosophy of “test by attacking” migrated into cybersecurity in the 1980s, giving birth to modern pentesting.
In both military strategy and cyber defense, the principle is clear: those who rigorously test their defenses through simulated attacks are far better prepared for actual threats.
As history has repeatedly proven, the best defense begins with a well-executed offense against yourself.
Penetration Testing FAQs
What is penetration testing, and why is it important?
Penetration testing is a simulated cyber attack on a system, network, or application to identify security vulnerabilities. It is important because it helps organizations to find security gaps before real attackers exploit them
How much time is required for a pentest?
The overall time of a pentest depends on factors such as the size of the environment, the size of the testing team, the type of test, etc. Reserve adequate time for the test and assign extra time for reporting. A good estimate would be 4 to 6 weeks, including the planning and reporting stage. The actual test takes around 2 to 3 weeks, depending on the complexity and size of the environment.
How does penetration testing work?
Penetration testing works by ethically hacking systems using the same tools and techniques as malicious attackers. Pentesters identify vulnerabilities, attempt to exploit them, and report findings with remediation recommendations. It simulates real-world attack scenarios to evaluate the effectiveness of existing security controls.
How is penetration testing performed?
Penetration testing is performed in structured phases: reconnaissance, scanning, gaining access, maintaining access, and covering tracks. Professional pentesters use manual and automated tools while following rules of engagement to safely identify and exploit weaknesses while upholding the CIA triad.
What is the difference between penetration testing and vulnerability assessment?
Penetration testing and vulnerability assessment are often used interchangeably. However, they are not the same. The key difference between vulnerability assessment and penetration testing is that vulnerability assessments search for potential weak points in your security. In contrast, penetration testing identifies weaknesses and then attempts to exploit them.
How to choose a penetration testing company?
Choose a company with proven experience, industry certifications (CREST, OSCP), clear methodology, and strong references. Verify they provide detailed reports, offer retesting, understand your industry, and maintain confidentiality through proper NDAs and insurance.
How often should you conduct a penetration test?
Organizations should conduct penetration testing at least once a year. However, high-risk industries or after major changes (new systems, updates, or acquisitions) should perform tests quarterly or biannually. Continuous pentesting is ideal for a mature security program
What is the purpose of penetration testing?
The purpose of penetration testing is to proactively identify and fix security vulnerabilities by simulating real cyberattacks. It helps organizations evaluate their defenses, meet compliance requirements, protect sensitive data, and reduce the likelihood and impact of security breaches.
Explore Our Penetration Testing Series
This post is part of a series on penetration testing.
You can also check out other articles below.

Chapter 1: What is Penetration Testing?
Chapter 2: Different Types of Pentest Testing
Chapter 3: Top 5 Pentest Methodology
Chapter 4: Top Pentest Companies to Consider in 2026
Chapter 5: Best Pentest Online Tools – Top List
Chapter 6: A Super Easy Guide on WordPress Pentest
Chapter 7: Average Penetration Testing Cost in 2026
Chapter 8: Pentest Reporting (Sample Report)
Chapter 9: Web App Pentest Guide
Chapter 10: Pentest Website Guide










Thorough, informative, and truly helpful post. Delivers what it promises in the title. Great work.
Does Penetration testing ensure PCI-DSS compliance?
It doesn’t. There are other procedures involved in the PCI-DSS compliance process than the pentest. Getting a pentest does improve your chances of nailing the PCI-DSS compliance audit for sure.
So, if I get a pentest today, how long will it be valid?
Usually, we recommend quarterly Penetration Testing. However, any major update on your software within that time will invalidate the pentest report.
This was helpful. However, I was looking for more detailed coverage of the Vulnerability Assessment part.
Thanks. We might actually have something for you. You’ll find a more detailed take on vulnerability assessment here. https://www.getastra.com/blog/security-audit/vulnerability-scanning/
How is this any different from ethical hacking?
Penetration testing is a focused procedure with a predefined scope. That means the security experts work under strict guidelines from the client organization and test only certain systems or certain areas of the business. Ethical hackers enjoy more freedom in terms of choosing the attack vectors as well as the techniques they apply. They usually take a broader approach to security testing where they employ every invasive and noninvasive tactic in their arsenal to try and exploit security loopholes.
Do you reckon that cyber security engineers will be replaced by AI?
Not in the foreseeable future. While the use of machine learning augments the security testing processes like vulnerability assessment and pentesting, it cannot yet cover for human instinct in terms of finding security errors.
Is it possible to automate the entire process of pentest?
Well, it really depends on what exactly you mean by pentest, and what you want to get out of it. If you are looking at a vulnerability scan, which is often passed as an automated pentest, then sure, you can schedule the scans, automate it, even integrate the scanner with your CI/CD to perform continuous scanning for new updates. But there will be false positives, and the scanner will miss some vulnerabilities, including business logic errors. If you want to find all vulnerabilities, with zero false positives and detailed guidelines to fix the vulnerabilities, you will have to go for manual pentest. There’s no way around it yet.