A Drupal security audit is a comprehensive evaluation to identify and mitigate security vulnerabilities in a Drupal website, including code inspections, configuration checks, and business logic error checks.
On the other hand, a Drupal pentest is a simulated attack on a Drupal website to identify and exploit vulnerabilities, going beyond a security audit’s static analysis to actively test the system’s defenses. But why do you need either? Let’s take a deeper look.
Why Do You Need Drupal Security Audit & Penetration Testing?
Identify Vulnerabilities
Regular auditing helps uncover site vulnerabilities ahead of time, such as improper configurations, usage of outdated modules, and vulnerable third-party integrations, which attackers can exploit to gain unauthorized access to data or features.
Prevent Data Breaches
Security audits and Penetration tests simulate real-world attacks and help detect vulnerabilities and entry points that could allow attackers to gain unauthorized access to sensitive data, which can be leveraged for further exploitation.
Meet Compliance Requirements
Organizations with sites that handle sensitive data must comply with regulatory requirements like GDPR, HIPAA, or other relevant regulations. All compliances require regular security audits and website testing.
Lock down your security with our 10,000+ AI-powered test cases.
Discuss your security needs
& get started today!
Phases of a Drupal Penetration Testing
Information Gathering
The first phase is all about gathering information about the Drupal site being tested, such as the server version, third-party dependencies, and other installed modules.
Specialized tools like DroopeScan can scan Drupal websites for common vulnerabilities and misconfigurations, along with the third-party modules installed. In combination with tools like Wappalyzer, which help detect other technologies, potential attack vectors can be found to attack the site.
droopescan scan drupal -u example.org
Vulnerability Scanning
The next phase is to use all the gathered information and perform vulnerability scanning on potential endpoints and exposed web pages.
Tools like ZAP, OpenVAS, or Nikto can be used to perform complete vulnerability scanning. Nikto is a web server scanner that tests websites for security risks and vulnerabilities. OpenVAS performs an in-depth comparison of the site with a vulnerability database, providing a comprehensive overview of the security risk in the target site.
nikto -h <http://example.com>
Alternatively, tools like SQLmap or XSSer can be used to perform vulnerability scanning for SQL Injection and XSS on specific endpoints.
Exploitation
The exploitation phase is where all the findings from the previous phases are used to exploit these vulnerabilities to their full extent and determine the damage they can actually do to the affected component.
Tools like Metasploit can be exploited, as they automate attack simulation to execute specific payloads for a more targeted execution. Moreover, tools like BurpSuite can be used to manually test the site and its APIs to exploit weaknesses in the website’s application logic.
msf6 exploit (multi/http/drupal_druaplgeddon) > exploit
Reporting and Remediation
Once all the vulnerabilities are found and exploited, it is time to compile all the findings into a comprehensive report providing details of all the vulnerabilities and their risk levels.
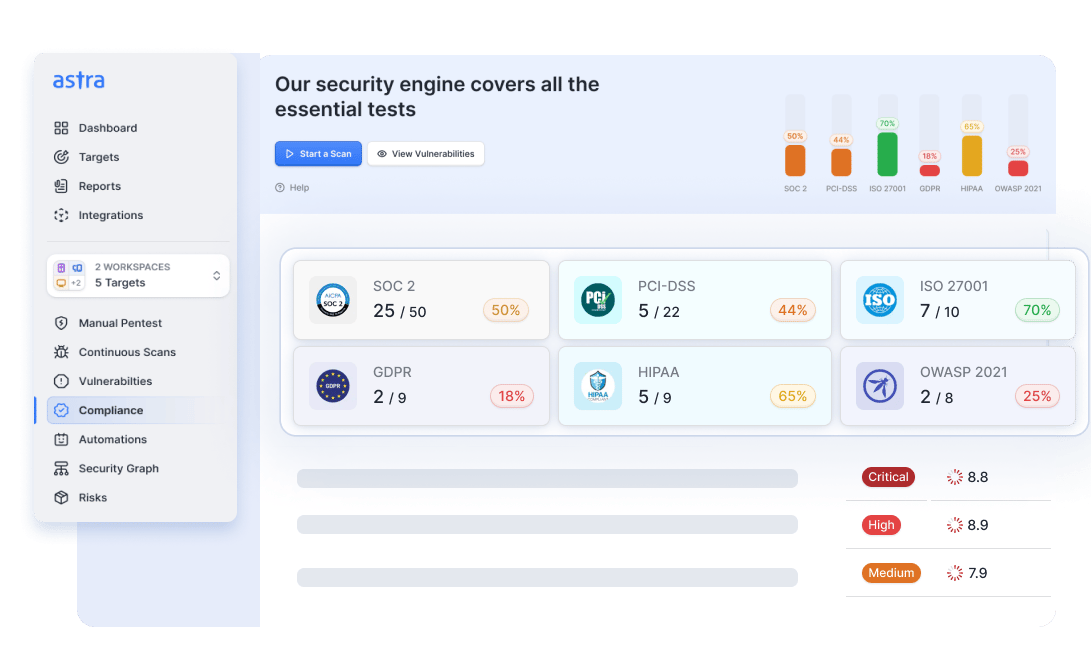
Tools like Astra Security can be used to access a full suite of manual pentests for various types of assets, along with expert-vetted scans, remediation assistance, and compliance-friendly reports.
Professional Drupal Penetration Test by Astra
Drupal security auditing and pen-testing are challenging tasks, especially for beginners. Even experienced users may find them cumbersome.
Astra Security offers professional Drupal Security audit & Penetration Testing tailored for your website by testing over 10000 test cases. Our Vulnerability Assessment & Penetration Testing (VAPT) program is conducted by security experts using the right mix of automated tools and human intelligence.
This Drupal security audit finds critical vulnerabilities like:
- Configuration and Deployment Misconfiguration.
- Drupal Core, Plugins & Theme Specific Vulnerabilities.
- Broken or Improper Authentication.
- Identifying Technical & Business Logic Vulnerabilities.
and many more in your system!
No other pentest product combines automated scanning + expert guidance like we do.
Discuss your security
needs & get started today!
Final Thoughts
Regular Drupal security and penetration testing is an essential practice to maintain the security posture of your Drupal site and the data it handles. Utilizing the right tools and methodologies allows you to protect your website from threats and risks and user data from attackers. It also helps you achieve regulatory compliance requirements and safeguard user trust.
FAQs
What is the timeline for Drupal Penetration Testing?
The timeline for Drupal Pentesting is 7-10 days. The rescan after fixing the vulnerabilities takes 3 more days. The timeline may differ slightly based on the scope of the test.
How much does penetration testing cost?
The cost for Drupal penetration testing ranges between $99 and $399 per month depending on the product, and the plan you are on.
Why choose Astra for Drupal Penetration Testing?
8000+ tests, adherence to global security standards, intuitive dashboard with dynamic visualization of vulnerabilities and their severity, security audit with simultaneous remediation assistance, multiple rescans, these are the features that give Astra an edge over all competitors.
Do I also get rescans after a vulnerability is fixed?
Yes, you get 1-3 rescans based on the type of Pentesting and the plan you opt for. You can avail these rescans within 30 days from the initial scan completion even after the vulnerabilities are fixed.








Hi there, is there any way I can secure drupal store? Just want to make sure that my site is safe.
Thanks for responding to the article. Drupal CMS is being used by various important organizations. In certain countries, it is used by governments also. This admiration can be attributed to its open-source framework and the spectrum of modules on Drupal. The modules enable site administrators to organize, customize and manage content easily on Drupal.
Is there any way I can block countries in drupal? If possible can you tell me how?
Thanks for responding to the article. Country blocking is a great & smart way to put your website off the radar for countries which do not cater to your needs. Most importantly, there are some countries which are notorious for sending attack vectors. Hence, blocking them would only be a prudent decision for your website. For more info, visit here: https://www.getastra.com/blog/category/cms/drupal-security/
I want to know more about file permissions in drupal? We have a drupal site and I don’t know much about file permissions.
Thanks for responding to the article. Drupal is an open source PHP written content management system. In other words, the source codes in Drupal are rewritable by everyone. If the Drupal file permissions aren’t set properly, it becomes really convenient for hackers to gain access to these files and then manipulate them.
My drupal site is redirecting to a strange website. How can I fix this? I am a bit worried.
Thanks for responding to the article. Don’t worry we got you covered. The Drupal redirect hack occurs after an attacker exploits the vulnerability in your website and modifies the site content to install malware. As a result, visitors to your website are redirected to spam and questionable links.
Hi , I am thinking of developing a drupal site. Are there any recommendations I need to follow?
Thanks for responding to the article. Our Drupal security checklist contains easy to implement steps for beginners and experts alike. Following this Drupal secure coding checklist will help you to protect your website from hackers and make your website stand out and shine. You can get the checklist here: https://webpro.getastra.com/checklist/drupal
I own a drupal site and am looking for a decent scanner that can protect it. What features does your plugin offer?
Thanks for responding to the article. Astra’s hacker tested firewall protects your website against SQLi, XSS, LFI, RFI, Bad Bots, Spam & 100+ threats in real time. Apart from OWASP’s top 10 threats found in websites, the firewall is tailored to protect against known CVE’s. Our intelligent firewall detects visitor patterns on your website & automatically blocks hackers with malicious intent. For more info visit here: https://www.getastra.com/features
Hi, looking to take a security audit for our drupal site. Can you tell me what tests will be performed and info about security issues?
Thanks for responding to the article. Sure, you can visit here for more info on tests that we will perform while audit and pricing info: https://www.getastra.com/drupal-vapt. Looking forward to securing your site.