An average website faces 94 attacks daily, and only 26% of all data breaches are attributed to web application hacks. The cyber threat landscape has worsened over the last couple of years, and keeping a continuous tap on all aspects of cybersecurity can be overwhelming.
This is where penetration testing steps in, but which is best for you? You need both automated and manual penetration testing to get a complete picture of your organization’s security posture and actionable insights to fix and prevent issues.
In this article, you will learn what a penetration test is, the difference between automated vs manual penetration testing, how automated and manual penetration testing serve your purpose, and how you can choose the perfect pentest partner.
| Feature | Automated Penetration Testing | Manual Penetration Testing |
|---|---|---|
| Testing Context & Depth | Standardized testing across known vulnerabilities. Excels at scale but limited business context | Deep business logic understanding; contextual attacks tailored to unique use cases |
| Speed | Initial testing in 1-5 hours; rapid first-pass coverage | 2+ days for medium applications. Thorough but time-intensive |
| Scale | Simultaneous testing across hundreds/thousands of applications | Limited by human capacity; typically one app at a time |
| Affordability | Higher upfront investment but lower cost per test at scale (meaning better ROI) | Higher cost per engagement as it requires certified experts (OSCP, CEH) |
| Accuracy (False Positives) | Higher false positive rates (10-30%); requires human triage | Minimal false positives; every finding is human-verified |
| Creative & Business Logic Attacks | Limited and struggles with custom business logic and context-dependent flaws | Best, as it finds price manipulation, workflow abuse, and authorization bypasses |
| Reporting Quality | Application-specific summaries with automated evidence; can infer remediation based on tech stack | Often templated as only the threat info changes. Also, compliance mapping is done manually |
| Skill-level Required | AI configuration and false positive triage; less specialized security knowledge needed | Certified ethical hackers (OSCP, CEH, eWPTXv2) with years of experience |
| Suitability | Static sites, CMS platforms, network VAPT, CI/CD integration, continuous monitoring | Complex web apps, custom platforms, regulated industries, and pre-launch critical tests |
| Rescan Efficiency | Targeted automated rescans on specific fixes; highly efficient | Time-intensive full retests |
What is Manual Penetration Testing?
Manual penetration testing is the process in which security engineers manually perform penetration testing to assess a system’s security posture.
They use hacker-style techniques to find ways to break into your system, evaluate the vulnerabilities in terms of impact and exploitability, and prepare a report documenting the vulnerabilities and how to reproduce and fix them.
Manual Penetration Testing Process
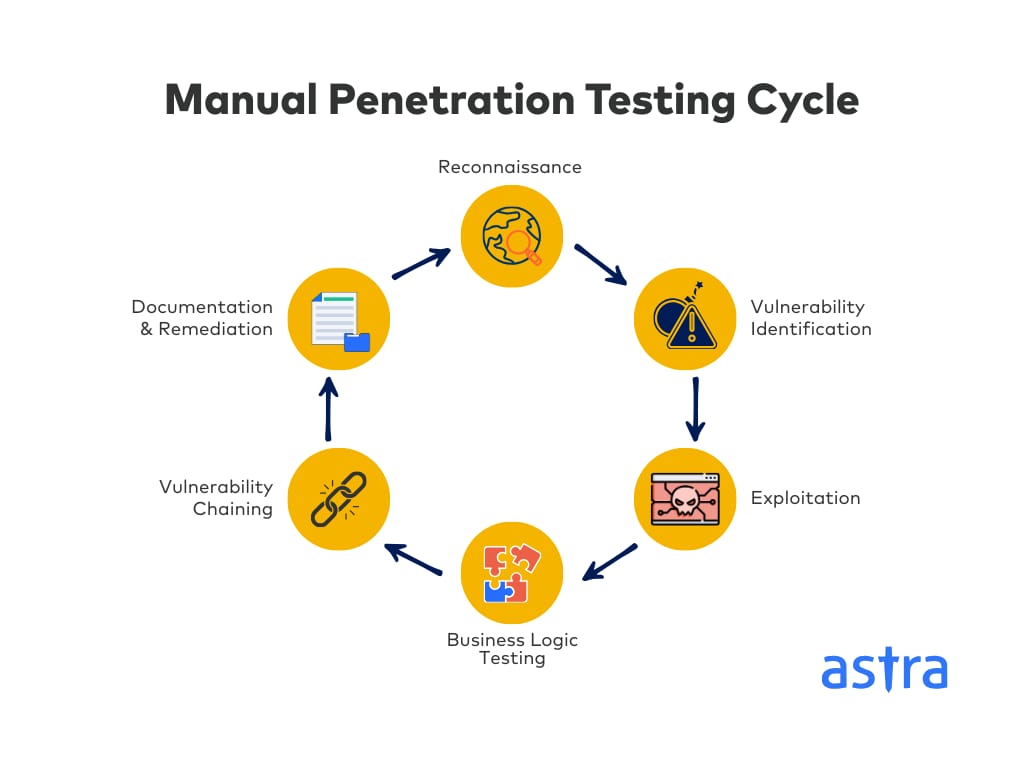
Manual penetration testing follows a structured approach that mimics how sophisticated hackers actually execute attacks. This includes:
- Reconnaissance & Info Gathering
Testers collect info about your target surface, consisting of domains, technologies, employee details, and public-facing assets, using OSINT methods to map the attack surface just like a real attacker.
Today, this extends beyond IP scanning to include executive digital footprints and third-party integrations that create hidden entry points. - Vulnerability Identification & Analysis
Security experts manually probe your applications, APIs, and infra to identify threats, analyzing each finding for exploitability within the specific business context.
This isn’t limited to a specified checklist. It’s understanding what can actually be broken and why it matters to your business. - Exploitation & Privilege Escalation
Testers create custom exploits to validate vulnerabilities, attempting to escalate privileges and move laterally through systems to show real-world impact. This step separates on-paper vulnerabilities from actual business risks. - Business Logic Testing
Experts test application workflows for threats like payment bypasses, authorization issues, or price manipulation, i.e, attacks that require understanding how the business operates. - Vulnerability Chaining
These testers excel at chaining multiple low-severity findings into high-impact attack paths. For example, combining CSRF with SSRF to achieve RCE is a creative process requiring contextual reasoning that automated testing struggles with. - Documentation & Remediation Guidance
Lastly, testers provide detailed reports with reproducible steps, business impact analysis, severity score, and specific remediation advice tailored to your tech stack and environment.
Note: Typical manual chaining reaches level 2 depth often, with level 3 chaining happening in about 10% of cases when the impact justifies deeper investigation.
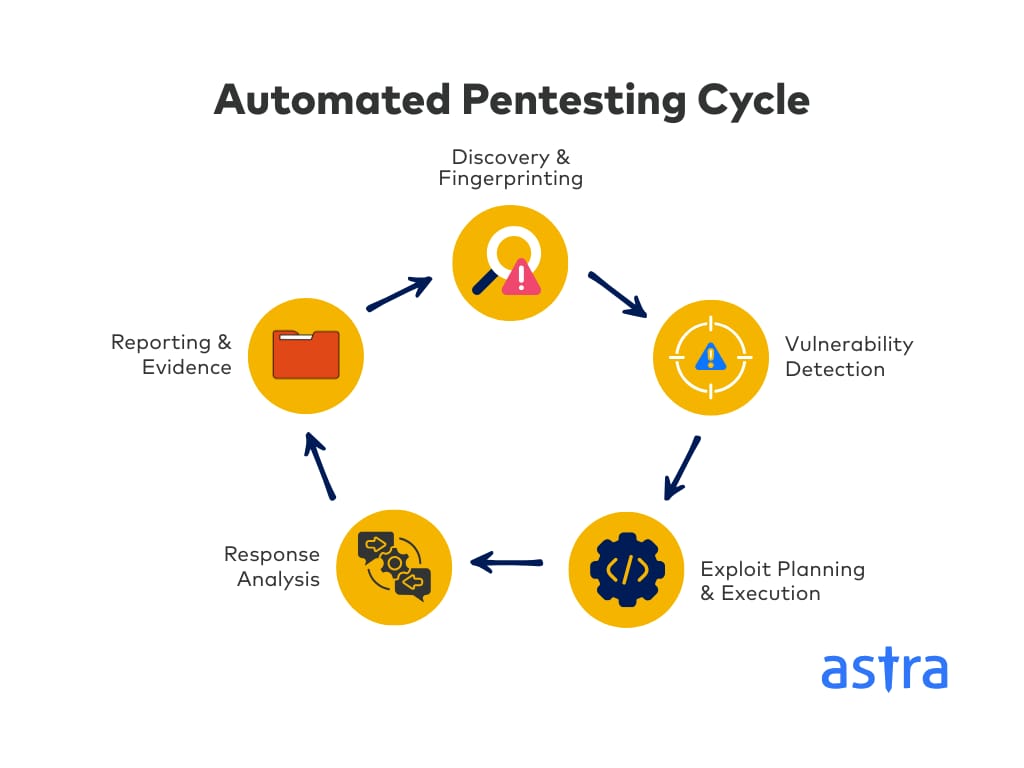
What is an Automated Penetration Testing?
Automated pentesting is a fundamental shift from basic automated scanners that match patterns to find vulnerabilities to intelligent, adaptive testing.
Automated penetration testing (or autonomous pentesting) goes beyond basic vulnerability scanning. It uses AI agents and orchestration logic to plan multi-step attacks, adapt to application responses, chain vulnerabilities, and test continuously, mimicking how real hackers execute attacks but at a much higher speed and scale.
Expert’s Tip:
Many times, people confuse advanced automated scanners with automated pen testing. But that’s not exactly the truth. Here’s how they are different:
- Automated scanners detect known issues from static databases. AI agents in autonomous pentesting use trained AI to generate dynamic test cases, fingerprint technologies, and select exploits based on live application behaviour.
- Scanners run fixed scripts. Autonomous agents adapt their strategy in real-time, making decisions about next steps like a human would.
- Scanners offer a point-in-time snapshot. An Autonomous pentesting tool enables continuous, evolving validation that matches your development pace.
What are the Advantages and Disadvantages of Automated vs Manual Penetration Testing?
Manual Penetration Testing
The main advantage of manual penetration testing is its “human” element. Here are some advantages that create a major impact:
- Business Logic Testing: Firstly, human testers understand the application’s purpose and user workflows. This helps them detect flaws like payment bypasses, multi-step authorization issues, and business process manipulation that automated tools consistently miss.
- Near-Zero False Positives: Every reported vulnerability in your systems is validated and verified by security experts. This eliminates the noise and wasted developer time associated with false alarms.
- Creative Attack Scenarios: Human testers adapt public exploits, craft custom payloads, and think like adversaries, testing edge cases and combining seemingly unrelated issues into alarming attack chains.
- On-Point Remediation Guidance: Lastly, testers provide context-specific fixes tailored to your exact tech stack, architecture, and business requirements, not just generic copy-paste advice.
Disadvantages:
- Limited Scalability: Human capacity constraints mean you can’t continuously test every application, API, or deployment. This, in turn, creates coverage gaps in fast-moving environments.
- Higher Per-Engagement Cost: Certified security experts have premium rates, making frequent testing cost-prohibitive for many businesses.
Automated Penetration Testing
Though autonomous pentesting is somewhat restrictive in terms of depth, it excels at breadth, covering multiple target surfaces simultaneously. Here’s how it’s advantageous for large-scale organizations today:
- Massive Scale & Continuous Coverage: To start with, automated pentesting can test thousands of applications simultaneously and continuously. This ensures every deployment, API endpoint, and infra change gets security validation without human bottlenecks.
- Rapid Vulnerability Detection: Initial assessment via automated testing is completed in hours instead of days. This enables faster feedback loops in DevSecOps pipelines and reduces the window of exposure for newly deployed code.
- Consistent, Repeatable Testing: AI agents apply the same rigorous methodology across all assets, trained on continuously updated CVE databases. This helps ensure no known vulnerability category is overlooked due to human oversight.
- Cost-Effective at Scale: To top it all up, while upfront investment is significant in automated pentesting, per-test costs drop dramatically when running thousands of scans. This improves ROI for orgs with large application portfolios.
Disadvantages:
- High False Positive Rates: Automated pentesting generates significant noise with false positives ranging between 10-30%. This further requires human review and potentially frustrates development teams with invalid findings.
- Limited Business Logic Detection: Another crucial downside is that AI currently lacks the contextual understanding to identify application-specific workflow abuses, authorization bypasses, or creative attack scenarios unique to your business, requiring chaining of up to 3 levels.
Recommended Reading: A Comparison of the top 15 penetration testing service providers in one place.
Automated vs Manual Penetration Testing: When to Use What? (2026)
The right approach between manual and automated penetration testing mostly depends on your specific security objectives and application characteristics. But here’s the approach you should mostly go for based on various security scenarios:
| Objective | Recommended Approach | Key Reason |
|---|---|---|
| Compliance & Pre-Audit (e.g., SOC 2, PCI-DSS) | Manual Penetration Testing | Mandatory for audit reports. Regulators require human-signed findings from certified experts. Essential for third-party vendor security assessments. |
| Pre-Launch & After Major Changes | Manual Penetration Testing | Critical for finding complex, business-logic flaws (e.g., payment bypasses) in revenue-critical apps that could severely damage reputation and trust. |
| DevSecOps & CI/CD Pipelines | Automated Penetration Testing | Provides immediate, non-blocking security feedback on every build. |
| High-Value Applications (Banking, Healthcare) | Manual Penetration Testing | Justified for apps handling sensitive data/finance. Mimics sophisticated, context-aware attackers through creative exploitation and logic testing. |
| Continuous Monitoring of Large Portfolios | Automated Penetration Testing | Enables scalable, continuous validation across hundreds of apps, APIs, and microservices, aligning with 24/7 threat actor probing. |
| 360-Degree Comprehensive Coverage | Hybrid Approach | Automated: For network VAPT, static sites, and infrastructure. Manual: For custom web apps with complex business logic. |
| Affordable & Scalable Security (SMBs/Startups) | Primarily Automated, Selective Manual Pentesting | Automated: Provides enterprise-grade continuous testing at scale. Manual: Can be applied selectively to the most critical 2-3 applications. |
Note: Many orgs. want their pentesting provider as part of third-party vendor vetting processes as their enterprise clients demand it. In such cases, manual penetration testing becomes non-negotiable as it provides the detailed, human-verified evidence needed to pass vendor security assessments.
Why a Hybrid Approach of Manual & Automated Penetration Testing is the Way to Go in 2026?
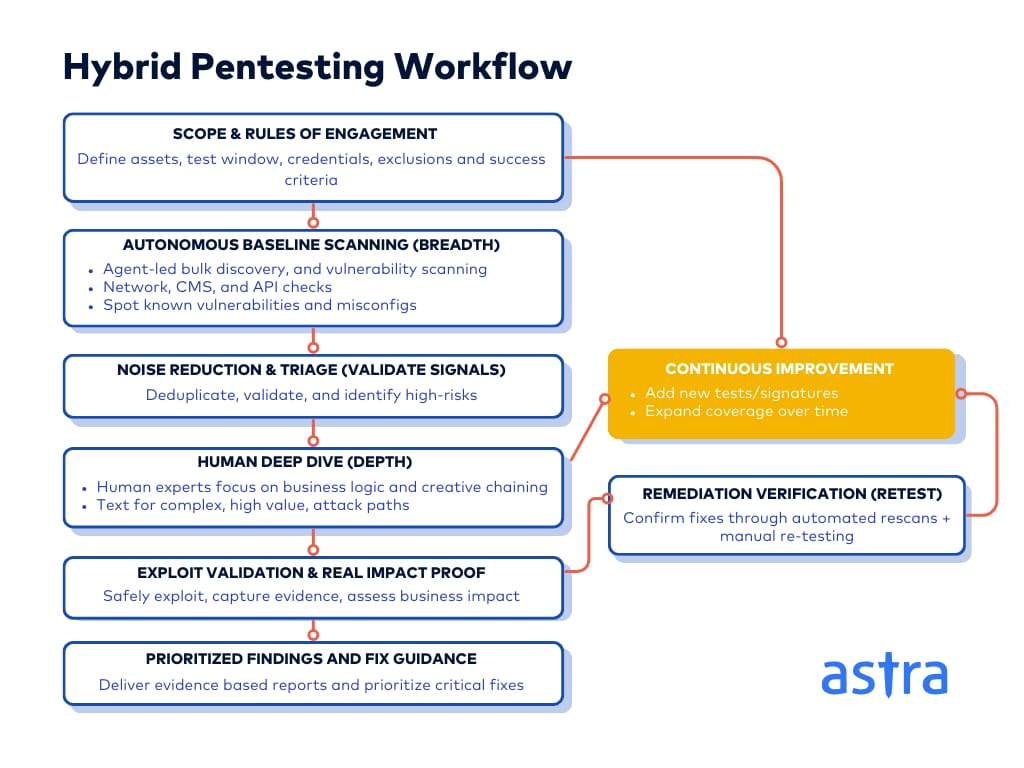
The manual vs automated pentesting debate is obsolete. 2026 demands both depth and breadth simultaneously. Automated pentesting gives you the scale to continuously validate thousands of assets. Manual expertise provides the business context that turns findings into real security. One without the other leaves dangerous gaps.
“The optimal strategy here is to use autonomous agents for bulk, standardized tasks such as network VAPT, CMS platforms, and first-pass API scanning. This clears the noise. Human experts can then focus exclusively on high-value targets requiring business logic testing and creative chaining. This division of labour can improve throughput 5-10x while controlling costs.”
This hybrid model is how you future-proof your business. Attackers use both automated tools and manual ingenuity. Your defense must do the same. Automated systems catch the latest technical flaws. Human testers find novel business logic attacks. Together, they build resilience against both today’s and tomorrow’s threats.
How Can Astra Security Help You Implement This Hybrid Approach to Your Advantage?
The Astra Security pentest suite is a complete and elegant solution for your penetration testing needs. The security team at Astra ensures near-zero false positives by manually exploiting the vulnerabilities.
The pentest report they produce is as thorough as it gets, yet easy to follow, thanks to the step-by-step guides and video POCs. You get best-in-class human support if the developers hit a roadblock while remediating the issues. The scope of collaboration between your team and the security experts is ample and smooth.

Here are some key features that set Astra Security apart:
- 15K+ unified test cases continuously updated to find vulnerabilities beyond OWASP and PTES standards
- Manual penetration testing by security experts ensures that near-zero false positives and critical business logic vulnerabilities are detected.
- Offensive Attack-AI Engine with continuously updated threat intelligence, combined with vulnerability resolution
- Human-led, AI-powered pentests for AI apps and LLM pipelines testing jailbreak prompts, indirect injections, model manipulation, and data leakage
- Scan behind logged-in pages without manually authenticating every time the session times out.
- In-house OSCP, CRT, CCSP, and eWPTXv2 certified experts detecting business logic flaws and payment bypasses
- A publicly verifiable pentest certificate helps you build customer trust.
Companies with sensitive information and internet-facing assets need a hybrid approach of automated and manual penetration testing. Astra Security’s pentest makes it super simple, pocket-friendly, and hassle-free to evaluate the security posture of your apps or network.
Final Thoughts
So, manual vs automated penetration testing in 2026? It’s the wrong question. You don’t choose one. You need both.
Manual testing delivers the depth, context, and creative exploitation critical for your vital applications and compliance mandates. Automated pentesting provides the continuous coverage and scale essential for modern, sprawling attack surfaces. Your security posture becomes the strongest when they work together.
Start by deploying automated pentesting for continuous baseline security across all assets. Then, strategically apply manual expertise to business-critical applications, pre-launch assessments, and areas requiring deep business logic testing. This hybrid model is how you maximize coverage, impact, and the value of every dollar in your security budget.
FAQs
Which is better, manual security testing or automated security testing?
There’s no single winner. Manual penetration testing offers in-depth tests and avoids false positives, while automated scans are faster and cover wider areas. They complement each other to create a strong security posture for your company.
Can automated pentesting find complex business logic flaws, or do we still need manual penetration testing?
No, traditional automated scanners reliably miss them. They scan for known code bugs but cannot understand your unique workflows or the “intent” behind features. Only manual testing provides the human creativity needed to spot flaws like price manipulation or authorization skips that attack the heart of your business.
How long does manual penetration testing take compared to automated, and how does this affect my release cycles?
Manual tests take weeks for a thorough assessment of a single application. Automated tools can deliver an initial scan in a few hours. This speed is critical for modern DevSecOps, allowing for security feedback on every build without stalling your release pipeline.
Can automated penetration testing completely replace manual testing?
Not in 2026. Modern AI tools are powerful for speed and scale, but they lack human intuition. True penetration testing requires creative thinking to chain vulnerabilities and understand business impact. These are areas where human expertise remains essential for high-stakes applications.
How do I implement a hybrid approach combining manual and automated penetration testing without managing multiple vendors?
Start with an automated vulnerability scan to quickly find common, known vulnerabilities across your entire environment. Then, have human experts perform intensive tests on the results and focus their time exclusively on complex business logic flaws and validating critical risks.