Web application penetration testing helps teams find and fix exploitable gaps before criminals do, and the need for those tests is growing faster than many engineering teams expect. In 2024-25, the number of reported CVEs and weaponized vulnerabilities rose notably, and web application attacks remain a major vector in enterprise breaches.
Modern application portfolios combine public web apps, APIs, single-page apps, and third-party integrations, which means a single overlooked endpoint can multiply risk across cloud services, identity systems, and data stores.
The result is that organizations that rely solely on point-in-time scans or manual checklists are increasingly exposed to credential theft, injection attacks, and insecure AI-generated code.
What Are Web Application Penetration Testing Tools?
Web application penetration testing tools are purpose-built scanners, proxies, frameworks, and services that simulate attacker behavior against web frontends and APIs.
They combine automated DAST scans, optional SAST integrations, authenticated crawling, and, for the highest confidence, safe exploit validation or manual exploitation to demonstrate real-world impact.
Web app pentest tools operate at runtime (DAST) and sometimes complement static analysis (SAST) to find logic flaws, injection points, insecure auth flows, and exposed endpoints that unit tests and CI pipelines miss. Good tools also feed vulnerabilities into a vulnerability management workflow, export CVSS risk scores, and integrate with CI-CD pipelines so findings are visible early in the SDLC.
Why Web App Penetration Testing Is Important
Web app penetration testing is essential because web apps are a primary target, and failures have real business costs. Penetration testing reduces the risk that a single exploitable bug becomes a public breach, a regulatory fine, or a reputational incident.
Key reasons to run regular web app pentests:
- Early detection in the SDLC: DAST + SAST + manual validation catches different classes of bugs; using them together reduces escape-to-production risk.
- Compliance and audit readiness: many standards (PCI-DSS, ISO 27001, SOC 2, HIPAA) require periodic testing and audit-grade evidence; pentests deliver both.
- Risk prioritisation using CVSS and proofs-of-concept: triaged, CVSS-scored findings with PoCs enable faster, measurable remediation decisions.
- Reduce false positives through manual validation: automated scans produce noise; expert validation preserves engineering time and avoids chasing false alerts.
- Enable DevSecOps: Integrating scans and validated findings into CI-CD pipelines ensures security keeps pace with release velocity.
Together, these outcomes lower breach costs, accelerate secure releases, and provide operational controls that security and compliance teams can measure. For example, the global price of data breaches remains a multi-million-dollar problem, and faster detection and containment measurably reduce the financial impact.
Our Evaluation Criteria: What Makes a “Best” Web Application Pentesting Tool?
Choosing a web application pentesting tool ultimately comes down to how reliably it helps teams find real vulnerabilities and how easily it fits into existing engineering workflows. The best tools detect OWASP Top 10 risks, API flaws, misconfigurations, and logic-level weaknesses with an accuracy that keeps false positives low and developer trust high.
A strong tool also integrates naturally into modern DevSecOps pipelines, supporting authenticated API testing, CI/CD-triggered scans, and clean reporting that developers can actually act on. And because most organizations operate under compliance requirements, the output must be audit-ready, with clear severity scoring and documentation that meets ISO 27001, SOC 2, PCI-DSS, or HIPAA standards.
Finally, scalability matters. The “best” tool is one that grows with your asset base, covering multiple applications, environments, and teams without adding operational complexity.
Top 15 Web App Pentest Tools of 2026
- Astra’s Pentest
- Nmap
- Wireshark
- Metasploit
- Burp Suite
- Nessus
- Cobalt
- Probely
- Rapid7
- Indusface WAS
- Veracode
- OpenVAS
- Acunetix
- SQLMap
- John the Ripper
Free and Open-Source Tools - OWASP ZAP (Zed Attack Proxy)
- Burp Suite Community Edition
- Nikto
- Nmap + NSE (Nmap Scripting Engine)
- OWASP Amass
- Arachni
- Metasploit Framework
Comparison of Top Web App Pentesting Tools
| Feature / Attribute | Astra Pentest | Nmap | Burp Suite |
|---|---|---|---|
| Platform | Online | Command-line interface | Desktop application |
| Scanner Capacity | Unlimited continuous scans | Scans top 1000 ports by default | Web applications only |
| Manual Pentest | Available for web, mobile, API, and cloud | Basic network mapping and port scanning | Available for web applications |
| Accuracy | Zero false positives (manual verification) | May show false positives or inconsistent results | False positives possible |
| Vulnerability Management | Dynamic dashboard with continuous insights | Not available | Not available |
| Compliance Support | PCI-DSS, HIPAA, ISO27001, SOC2 | Indirect relevance | PCI-DSS, HIPAA, GDPR, OWASP Top 10 |
| Integrations | CI/CD tools, Slack, Jira, GitHub, and more | None | Limited |
| Customer Support | 24/7 expert support | Community-based only | Minimal assistance |
| Price | Starts at $199/month | Free | $449 per user per year |
| Free Trial | Starts at $7 | Fully free | Free Community Edition available |
Top 15 Web Application Penetration Testing Tools
By now you have formed a general idea about the different kinds of tools generally used by Penetration Testers. Now let us learn about the best web services pentest tools. The tools we list down here are all loaded with great capabilities, however, you have to choose the right ones according to your needs.
1. Astra Pentest [Get Started]
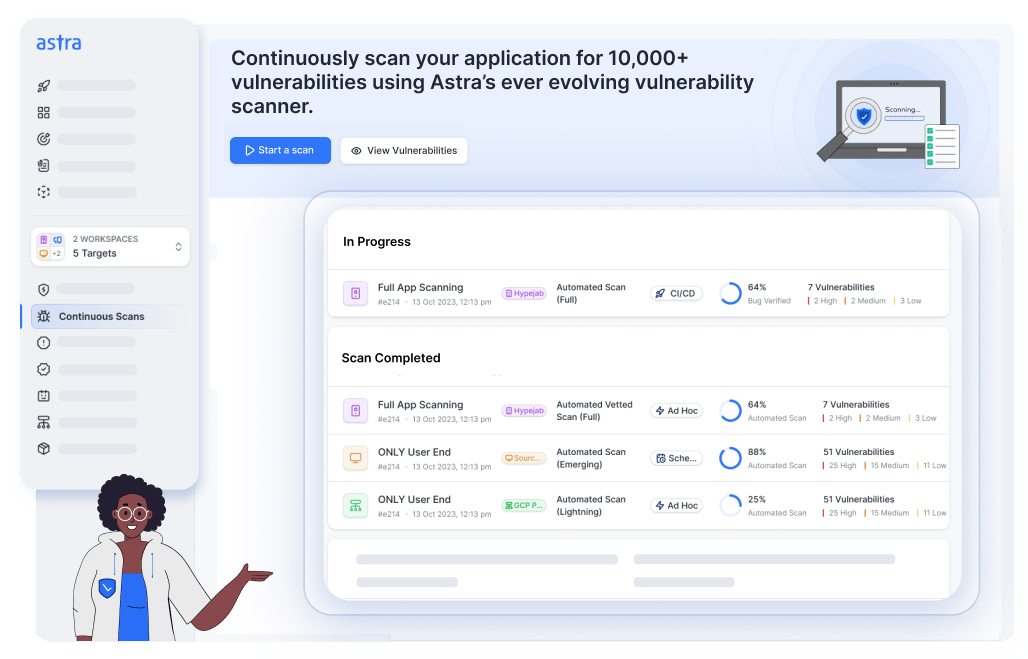
Features:
- Platform: Online
- Scanner Capacity: Unlimited continuous scans
- Manual pentest: Available for web app, mobile app, APIs, and cloud infrastructures
- Accuracy: Zero false positives
- Vulnerability management: Comes with dynamic vulnerability management dashboard
- Compliance: Helps you stay compliant with PCI-DSS, HIPAA, ISO27001, and SOC2
- Price: Starts at $199/month. Better pricing, tailored to you. Book a call to unlock it
Astra Pentest is a leading web application penetration testing company that offers PTaaS and continuous threat exposure management capabilities. Our comprehensive solutions blend automation and manual expertise to run 15,000+ tests and compliance checks, ensuring complete safety, irrespective of the threat and attack location.
With a 360° view of an organization’s security posture, continuous proactive insights, real-time reporting, and AI-first defensive strategies, we help CTOs shift left at scale. Our guaranteed zero false positives, seamless integrations, and expert support make cybersecurity simple, effective, and hassle-free for hundreds of businesses worldwide.
Still don’t believe us? Check out what 1000+ customers have to say about Astra!
Pros
- It can be integrated into the CI/CD pipeline.
- Ensure zero false positives through thorough manual vetting of scan results.
- Helps with cloud and API vulnerability management.
- Provide round-the-clock customer support.
Limitations
- Free trial starts at $7.
Customer Review
“I appreciate Astra Pentest for their professionalism and expertise. Their pentesters are highly knowledgeable … The reports are detailed yet easy to understand, providing clear insights and actionable recommendations.” – Shudhanshu S
Best For
Continuous pentesting + PTaaS with manual validation and DevSecOps integration.
2. NMAP
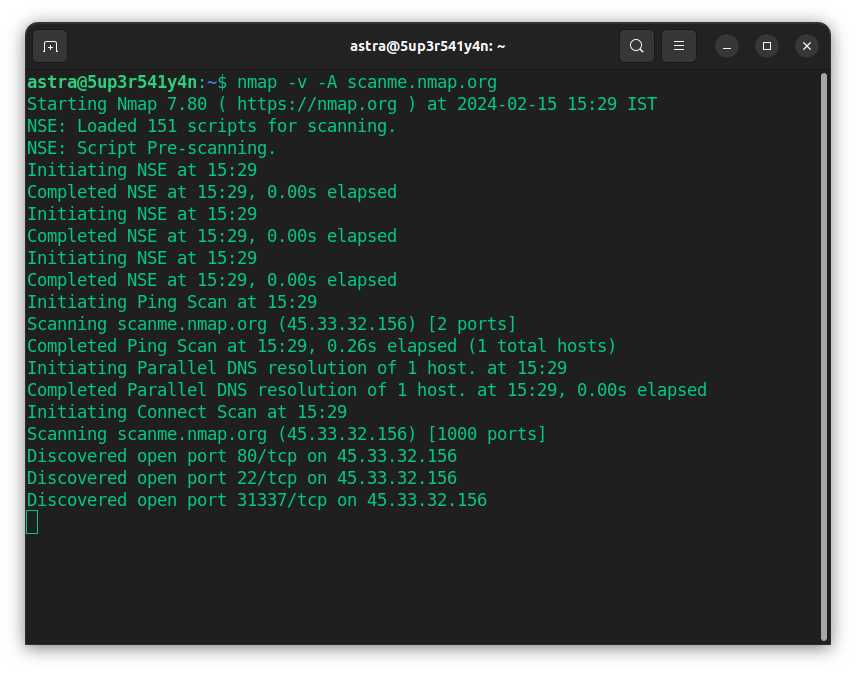
Features:
- Scanner Capacity: Usually scans the 1000 most popular ports of each network protocol
- Manual pentest: Network mapping and port scanning
- Accuracy: Occasionally shows false positives and faulty insights
- Vulnerability management: No
- Compliance: Indirectly relates to compliance reporting
- Price: Free
NMAP is short for Network Mapper. It is an open-source web application pentest tool that helps you map a network by scanning ports, discovering operating systems, and creating an inventory of devices and the services running on them.
It sends differently structured packets for different transport layer protocols which return with IP addresses and other information. You can use the tool for a large network with thousands of devices and ports.
Customer Review
““GUI front-end that brings Nmap’s power to the desktop … cross-platform … output persistence handles multiple formats … real-time topology mapping.” — Luca P., G2 reviewer.
Pros
- Shows open ports, running serves, and other critical facets of a network
- Freely available.
- Usable for large and small networks alike
Limitations
- The user interface can be improved.
- Might show different results each time.
Best For
Reconnaissance, network mapping, and attack surface discovery with NSE scripting.
3. WireShark
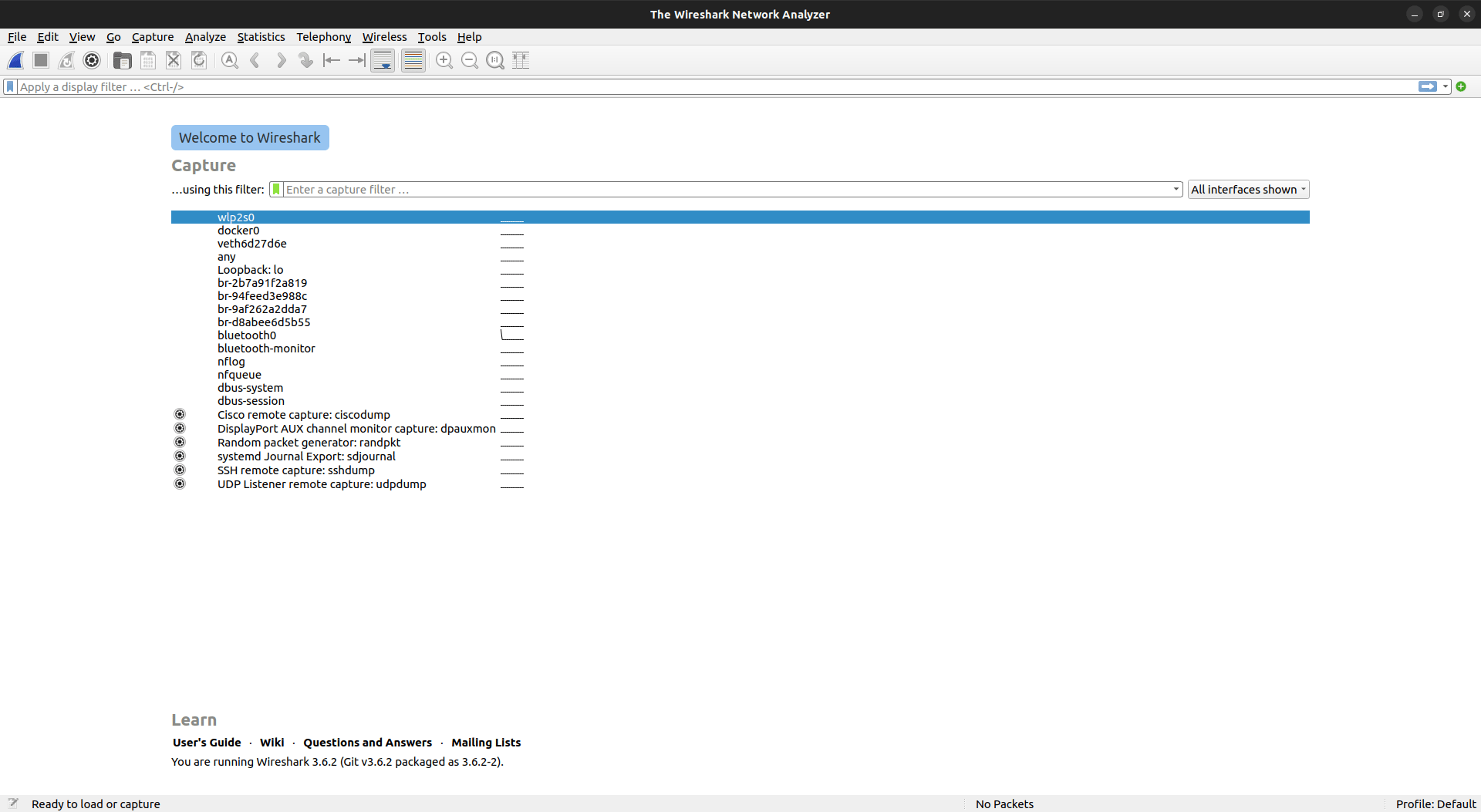
Features:
- Scanner Capacity: Captures live packet data from a network interface
- Manual pentest: Useful tool for pentesting
- Accuracy: Fairly accurate
- Vulnerability management: No
- Compliance: Indirectly relates to compliance reporting
- Price: Free
WireShark is one of the most famous open-source penetration testing tools for web applications that you can use for protocol analysis. It allows you to monitor network activities at a microscopic level. It is a growing platform with thousands of developers contributing worldwide.
WireShark is the industry standard for protocol analysis in many different sectors. If you know what you are doing, it is a great tool to use.
Pros
- Easy to install
- Open-source tool.
Limitations
- Can be difficult for beginners to navigate.
- Could improve its user interface.
Customer Review
“Wireshark is a powerful and feature-rich tool that allows deep packet inspection, protocol analysis, and real-time traffic monitoring. It’s easy to install across platforms and integrates well with tools like tcpdump, TShark, and Kali Linux, making it ideal for cybersecurity labs and network diagnostics. Despite its technical depth, it’s highly efficient once learned and supported by a strong community with excellent documentation.” – Nikhil S.
Best For
Best for deep network traffic analysis, protocol inspection, and identifying insecure communications during pentests.
Are your current tools missing critical vulnerabilities because they only scan superficially?

4. Metasploit
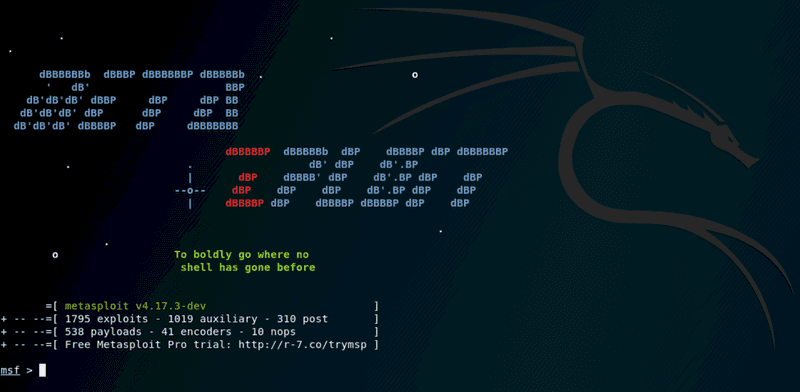
Features:
- Scanner Capacity: N/A
- Manual pentest: Metasploit contains an assortment of tools that can be used for pentesting
- Accuracy: N/A
- Vulnerability management: No
- Compliance: Indirectly relates to compliance reporting
- Price: Free
Metasploit is a Ruby-based open-source framework used by ethical and malicious actors to probe systematic vulnerabilities on networks and servers. The Metasploit framework also contains portions of fuzzing, anti-forensic, and evasion tools with listeners, encoders, post-exploitation code, and whatnot.
It is easy to install and can work on a wide range of platforms regardless of the languages they run on. The popularity and the wide availability of Metasploit among professional hackers make it an essential tool for Penetration Testers.
Pros
- Includes nearly 1677 exploits.
- Freely available online pentest tool.
- Easy to use.
Limitations
- Not beginner-friendly.
- Initial navigation can be difficult.
Customer Review
“What I enjoy best about Metasploit is that it contains an extensive database of exploits that can be tailored to match the individual needs of the user. Metasploit can also be readily connected with other security tools such as vulnerability scanners, network analyzers, and IDS/IPS systems.” – Yasir D.
Best For
Best for advanced exploit development, vulnerability validation, and chaining real-world attack scenarios.
5. Burp Suite
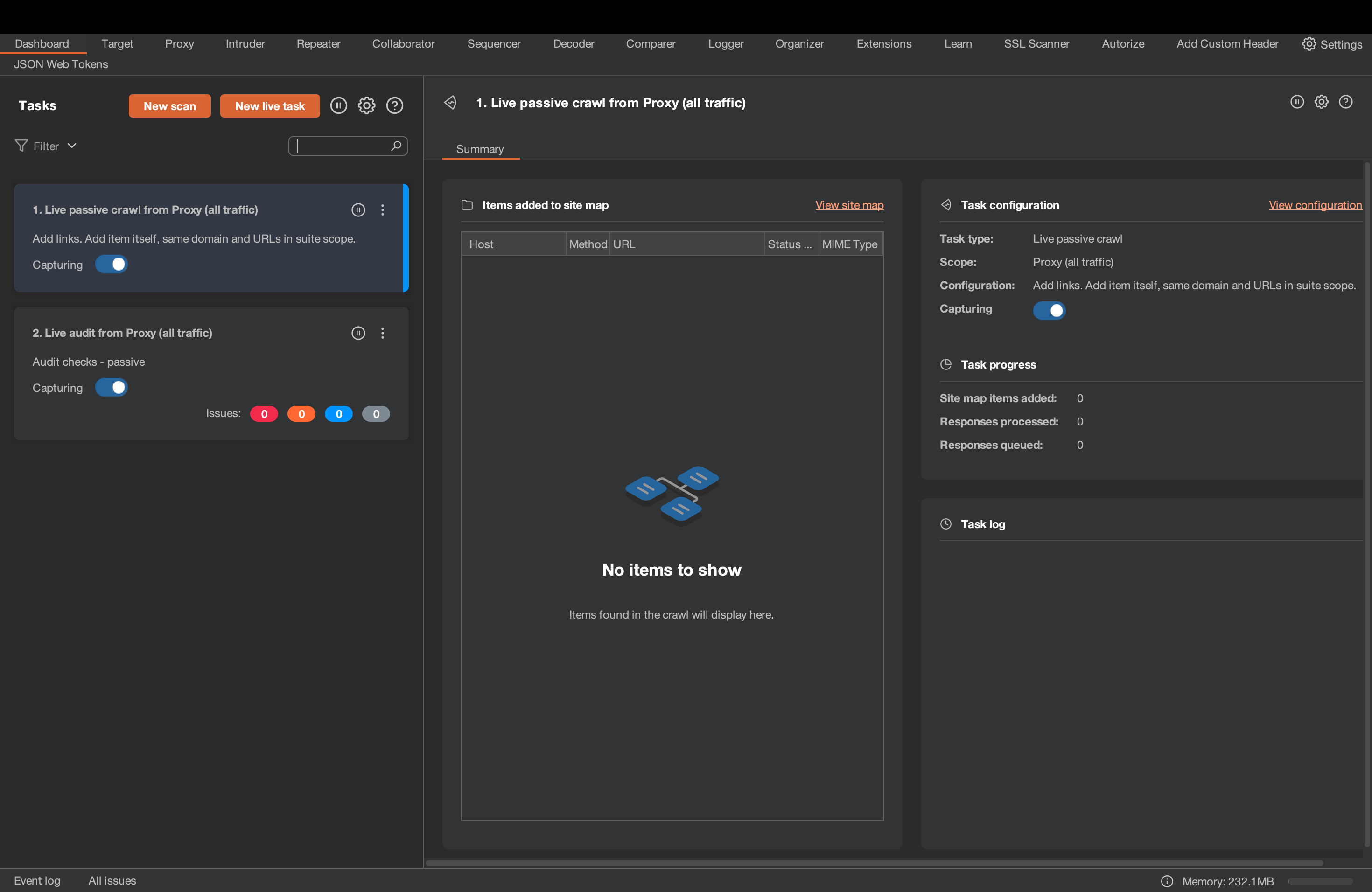
Features:
- Scanner Capacity: Web applications
- Manual pentest: Yes
- Accuracy: False positives possible
- Vulnerability management: No
- Compliance: PCI-DSS, OWASP Top 10, HIPAA, GDPR
- Price: $449/per user/per year
Burp Suite stands out as a top-tier web penetration testing tool, equipped with features for both manual and automated testing. It identifies vulnerabilities by intercepting and analyzing web traffic, automating tedious tasks, and performing fuzzing and brute-force attacks on login mechanisms.
This tool is highly effective at detecting common web vulnerabilities like SQL Injection, Cross-Site Scripting (XSS), and Insecure Direct Object References (IDORs). It offers both, a free community edition and a commercial edition.
Pros
- Provides advanced automated pentesting services.
- Provides step-by-step advice for every vulnerability found.
- Can crawl through complex targets with ease based on URLs and content.
Limitations
- Advanced solutions are commercialized and can be expensive.
- Does not provide expert customer service and assistance.
Customer Review
“Burp Suite is incredibly user-friendly for a tool with such depth. The interface is well-organized, and even beginners can start intercepting and analyzing traffic with minimal setup. Real-time interception and request modification through the Proxy and Repeater tools are extremely powerful – they allow me to instantly test and validate web vulnerabilities as I discover them. The ability to view and manipulate requests and responses in real time makes it an essential tool in any web security assessment.” – Nikhil S.
Best For
Best for manual web application testing, request interception, and identifying common web vulnerabilities like XSS and SQL injection.
6. Nessus

Features:
- Scanner Capacity: Web applications
- Manual pentest: No
- Accuracy: False positives possible
- Vulnerability management: Yes (Additional Cost)
- Compliance: HIPAA, ISO, NIST, PCI-DSS
- Price: Starts at $4,236/year
Nessus is an automated website penetration testing tool by Tenable. It has been used by security professionals for vulnerability assessment since 1998. They aim to make vulnerability assessments simple and quick remediations. You can deploy it on a variety of platforms.
It’s easy to navigate and use UI, and simplified automation of scanning and reporting tasks makes it one of the leading choices for web app pentests.
Looking for reliable Tenable alternatives that offer advanced vulnerability management and compliance coverage?
Pros
- Helps find missing patches that are critical to maintaining security.
- Point-in-time analysis of security system.
- Helps achieve compliance with the scans.
Limitations
- Advanced support is only available upon additional payment.
- Takes time to complete scans.
- Can be an expensive solution.
Customer Review
“I think Tenable Nessus is a very popular toolset that stands out because of its usability, allowing me to learn and use it quickly without requiring extensive training or facing a steep learning curve. Its intuitive nature facilitates swift adoption, making it accessible for our team. Additionally, I value the ability to specify the range of IP address assets and perform both ad-hoc and scheduled scanning. This functionality is crucial for maintaining the integrity and security of our network infrastructure, and it helps us in managing and mitigating vulnerabilities efficiently.” – Herman
Best For
Best for automated vulnerability scanning and compliance-driven assessments across web applications and infrastructure.
7. Cobalt
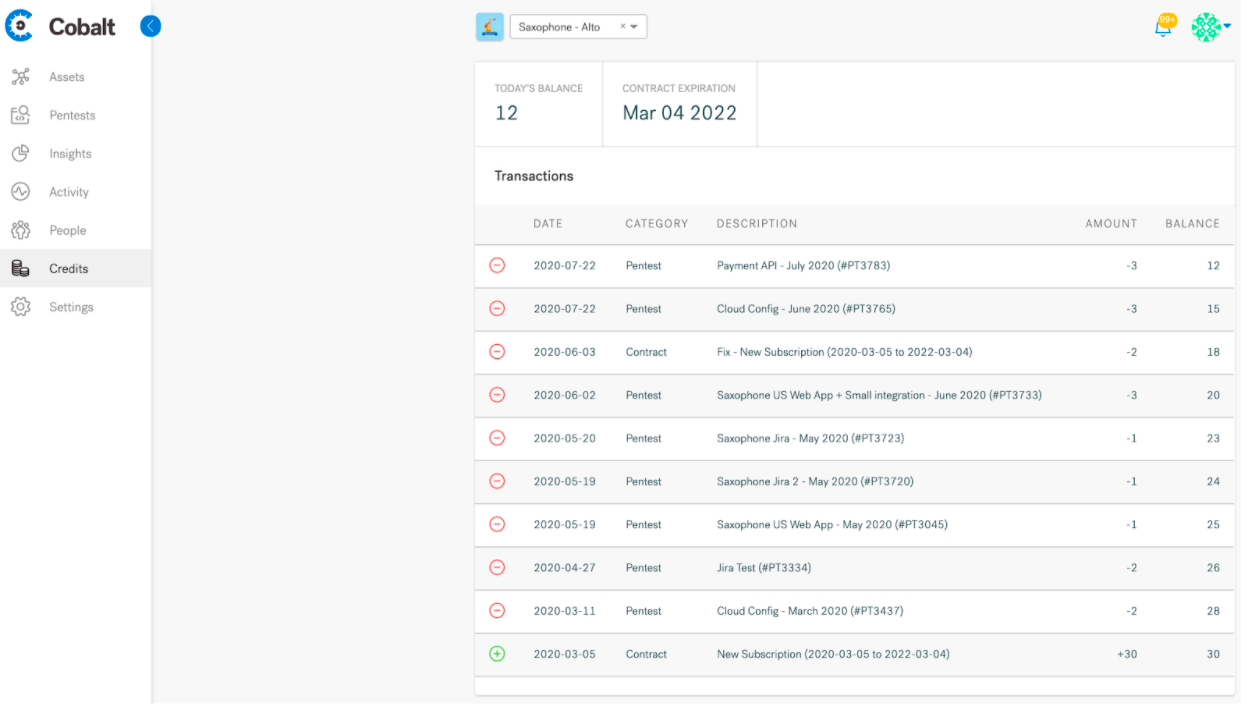
Features:
- Scanner Capacity: Web and mobile applications, APIs, Networks, and Cloud
- Manual pentest: Yes
- Accuracy: False positives possible
- Vulnerability management: Yes
- Compliance: SOC2, PCI-DSS, HIPAA, CREST
- Price: Quote on request
Cobalt is another penetration-testing-as-a-service provider. They connect your organization with the global community of vetted penetration testers whose pentesting skills suit your tech stack.
Its SaaS platform helps you gather real-time insights so that your teams can get on with the remediation quickly. It helps you with web app pentesting, mobile app pentesting, cloud scanning, and API pentesting.
Learn why some teams are shifting to Cobalt alternatives and competitors that deliver unlimited scans, expert validation and audit-ready reporting.
Pros
- Impressive existing clientele, including Nissan and Vodafone.
- 14-day trial period.
- Accelerated find to fix cycles
Limitations
- The retest often takes too much time
- Complex pricing structure
- Reported false positives
Customer Review
“Cobalt provides an excellent balance of flexibility and expertise in penetration testing. I like how their platform makes it easy to track findings, communicate directly with testers, and manage retesting. The talent and professionalism of their pentesters stand out—they deliver actionable results, not just reports. The continuous visibility into progress and remediation guidance is a huge value add.” – Taylor P.
Best For
Best for on-demand, human-led penetration testing through a pentesting-as-a-service (PTaaS) model.
No other pentest product combines automated scanning + expert guidance like we do.
Discuss your security
needs & get started today!

8. Probely
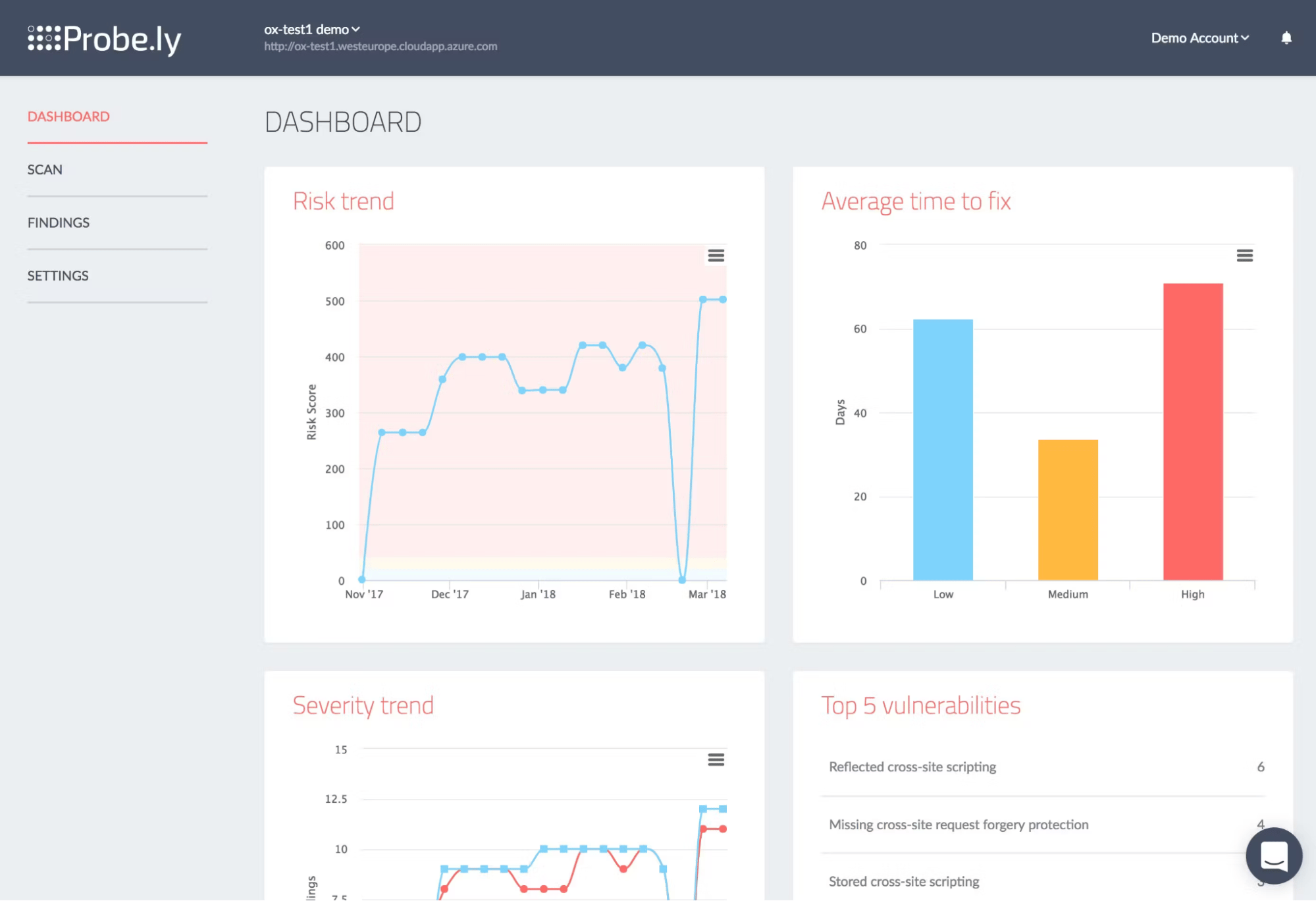
Features:
- Scanner Capacity: Web applications, APIs
- Manual pentest: No
- Accuracy: False positives possible
- Vulnerability management: Yes
- Compliance: HIPAA, PCI-DSS, GDPR, & OWASP TOP10
- Price: Starts at $98/month – Pro Plan
Probely is designed for web application scanning and API scanning. They say, using Probely is like adding a virtual specialist to your team. We will let you be the judge after you look at the features.
Probely automatically prioritizes vulnerabilities based on the risk of the vulnerabilities and provides proof of legitimacy for each issue.
Pros
- Simple to use with continuous scanning.
- Wide range of tests.
- Good customer support.
Limitations
- Could have better integrations.
- Custom vulnerability scoring does not align with general scoring.
Customer Review
“Helps the development team in building secure apps through scanning for vulnerabilities before going live.
Provides reports and insights that help future app development.
Secure web applications and API’s access.” – Odbor K.
Best For
Best for continuous automated web and API scanning with developer-friendly reporting.
9. Rapid7
Features:
- Scanner Capacity: Cloud and Web Applications
- Manual pentest: Yes
- Accuracy: False positives possible
- Vulnerability management: Yes
- Compliance: CIS, ISO 27001
- Price: Starts at $175/app/month
As a vulnerability assessment service provider, Rapid7 is another web pentesting tool with a range of services dedicated to web application security. They configure the scans, schedule them, validate the findings, and remove false positives.
They optimize the vulnerability scans based on your compliance requirements. Apart from these things, Rapid7 also provides business logic testing that is otherwise impossible with a vulnerability scanner.
Pros
- Simple and easy-to-navigate interface.
- Capable of finding hidden vulnerabilities
- Great and easy-to-understand reports.
Limitations
- Customer support can be improved.
- Removal of scanned devices must be done manually.
Customer Review
“Their CRC Essentials license is absolutely value for money as it includes three of their products – InsightVM, InsightCloudSec and InsightConnect, giving us a nice package for all our needs including vulnerability management, cloud security and compliance and to some extent security orchestration and automation capabilities.
Whilst the package is great for a business like ours, considering we are a small security team, we got a wide variety of various services from Rapid7 in a single license, However, it has made our work significantly more which is pretty annoying.” – Himanshu K.
Best For
Best for enterprise-grade vulnerability management with validated findings and business-logic testing support.
10. IndusfaceWAS
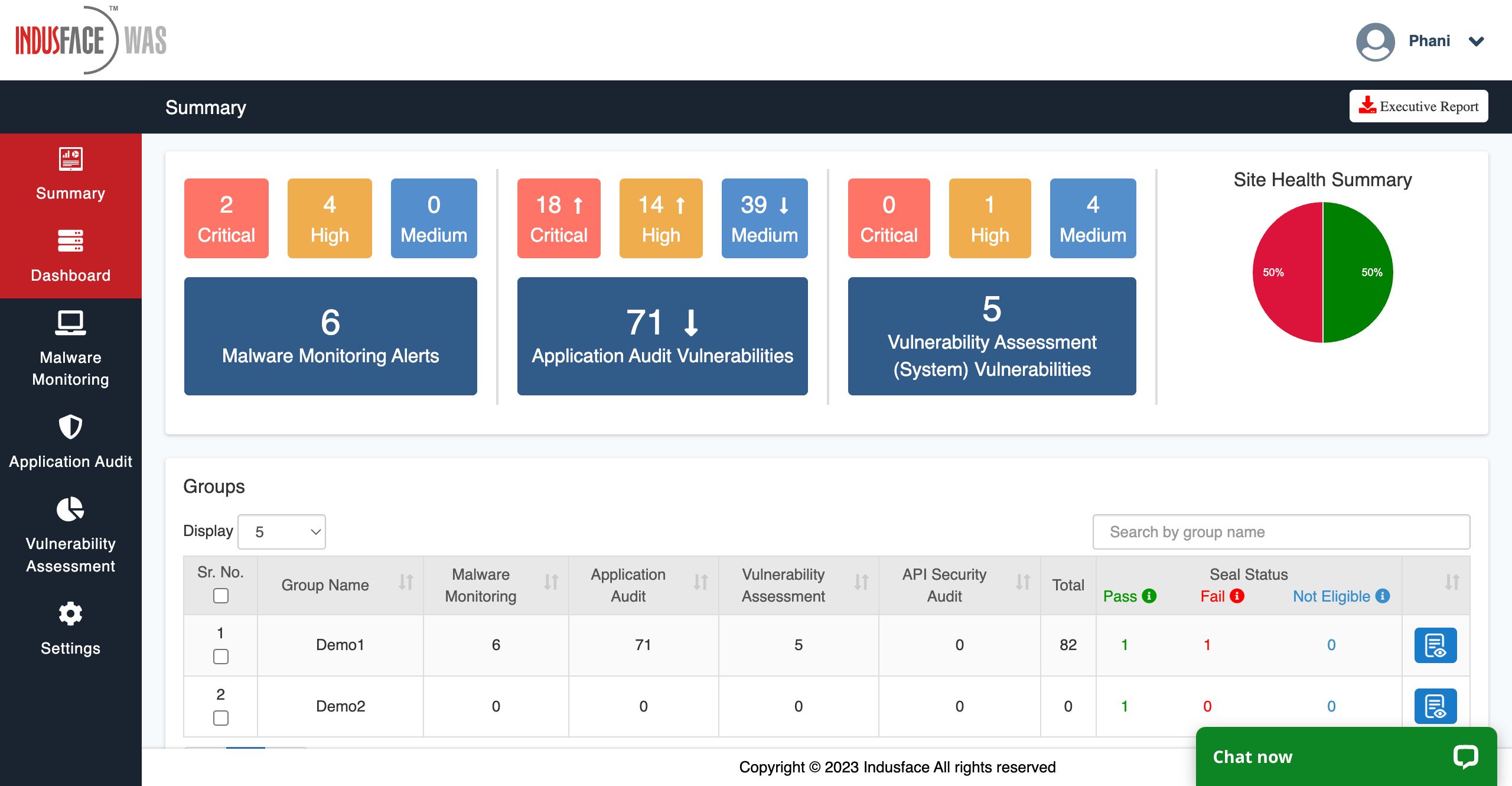
Features:
- Scanner Capacity: Web and mobile applications, APIs
- Manual pentest: Yes
- Accuracy: Zero false positives
- Vulnerability management: Yes
- Compliance: PCI-DSS, ISO 27001
- Price: Starts at $ 59/app/month – Advance plan
IndusfaceWAS combines automated scanning and manual pentesting to help you detect all OWASP top 10 vulnerabilities and business logic errors. Indusface also promises zero false positives and provides remediation assistance.
The scanner built by Indusface is focused on scanning single-page applications and intelligent crawling. It offers unlimited scans and detects application vulnerabilities validated by OWASP and WASC.
Pros
- Assured zero false positives through zero-day protection.
- Helps achieve compliance with regulations like PCI-DSS and ISO 27001.
- Vulnerability detection is not limited to OWASP Top 10.
- It has an executive dashboard that provides necessary information.
Limitations
- Not available for mobile applications.
- Reports are difficult to understand.
Customer Review
“What I like about the WAS platform is that it combines EASM + PTaaS and provides Risk based Vulnerability scoring for all the vulnerabilities.” – Mazhar S.
Best For
Best for automated web and API scanning with zero false positives and compliance-focused dashboards.
11. Veracode
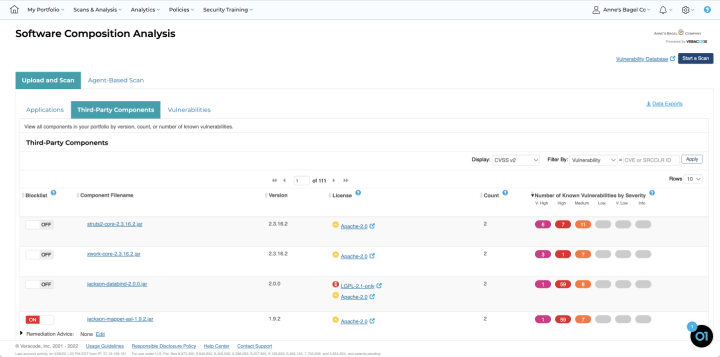
Features:
- Scanner Capacity: Web applications
- Manual Pentest: Yes
- Accuracy: False positives possible
- Vulnerability Management: Yes
- Compliance: NIST, PCI, OWASP, HIPAA, GDPR
- Price: Quote upon request
Veracode is a dynamic solution and one of the best tools for web application pentesting that helps analyze web apps to find vulnerabilities. It can run thousands of tests with a less than 1% false positive assurance rate.
While it offers great utility for web app pentesting, the user interface can have a steep learning curve for beginners.
Pros
- Offers quick penetration testing services.
- Extremely comprehensive reports.
- Remediation assistance is provided.
Limitations
- Zero false positives are not assured.
- Could improve its user interface
Customer Review
“I find the Veracode Application Security Platform incredibly useful for identifying social injections and providing static code analysis, which helps in addressing all security vulnerabilities effectively. The ease of integrating with GitHub and cloud-based repositories streamlines our development process. The platform’s PR static analysis feature is invaluable for maintaining best code practices, especially in preventing SQL injections and cross-site scripting attacks. I also appreciate the comprehensive code analysis capabilities that ensure our applications maintain high security standards.” – Bhanu Prakash M.
Best For
Best for enterprise DevSecOps teams needing CI/CD-integrated web application security testing and remediation guidance.
12. OpenVAS

Features
- Scanner Capacity: Web applications, network protocols
- Manual Pentest: No
- Accuracy: False positives possible
- Vulnerability Management: No
- Compliance: No
- Price: Free
OpenVAS is an open-source penetration testing software that is comprehensive and powerful. It is supported and updated constantly with the help of expert pentesters all around the world, thus making it up to date.
Most importantly, it has been observed to miss basic vulnerabilities and may result in false positives.
Pros
- Automated vulnerability scanning is quick and efficient
- Freely available network vulnerability scanning tool.
- Scans for improper file access, XSS injections.
Limitations
- Could be difficult for beginners to make use of.
- Automated causes false positives to appear.
Customer Review
“OpenVAS is a great free software for vulnerability scans, offering good performance compared to other free tools. Easy to deploy and well configurable.
The UI of OpenVAS can be confusing for new users. The options are hidden and not very intuitive. The lack of a more well-developed and organized inventory can also be a point of improvement.” – Victor Hugo M.
Best For
Best for free, open-source network and web vulnerability scanning for baseline security assessments.
13. Acunetix

Features:
- Scanner Capacity: Web applications
- Manual Pentest: No
- Accuracy: False positives possible
- Vulnerability Management: Yes
- Compliance: OWASP, ISO 27001, PCI-DSS, NIST
- Price: Quote on Request
This web pentesting software provides vulnerability assessments and automated penetration tests provided by Invicti. Acunetix helps reduce vulnerabilities across various kinds of web applications.
It also allows the scanning of multiple environments as well as the prioritization of vulnerabilities.
Pros
- Time release of updates
- Can find a wide array of vulnerabilities.
- Agile testing with detailed reports
Limitations
- Does not provide expert remediation assistance with professionals.
- Does not ensure zero false positives.
- Dated user interface with scope for improvement.
Customer Review
“What I like best about Acunetix by Invicti is how seamlessly it combines powerful vulnerability detection with ease of use. It’s not just another security scanner — it’s an intelligent, automated tool that feels built for both developers and security professionals. The way it quickly identifies and prioritizes critical vulnerabilities like SQL injection, XSS, and misconfigurations across websites and APIs saves a huge amount of manual effort. ” – Ranit D.
Best For
Best for automated web vulnerability scanning with broad vulnerability coverage and prioritization.
Make your Web Application the safest place on the Internet.
With our detailed and specially curated Web security checklist.
14. SQLMap
Features:
- Scanner Capacity: SQL injection testing for web applications
- Manual pentest: Semi-automated exploitation tool
- Accuracy: High accuracy for SQL injection detection
- Vulnerability management: No
- Compliance: OWASP Top 10 (Injection category – indirect)
- Price: Free (open source)
SQLMap is a specialized open-source penetration testing tool designed exclusively for detecting and exploiting SQL injection vulnerabilities. It automates the process of identifying injectable parameters, fingerprinting database systems, extracting data, and even taking over database servers under certain conditions.
The tool supports a wide range of databases including MySQL, PostgreSQL, Oracle, MSSQL, and SQLite. While extremely powerful, SQLMap assumes the user has a strong understanding of SQL injection concepts and database internals.
Customer Review:
Widely regarded in the security community as the “gold standard” for SQL injection exploitation.
Pros:
- Extremely effective at detecting and exploiting SQL injection
- Supports nearly all major database engines
- Highly customizable via command-line options
- Actively maintained by the security community
Limitations:
- Not beginner-friendly
- Limited strictly to SQL injection vulnerabilities
- No reporting or vulnerability management features
Best For: Experienced penetration testers performing deep SQL injection testing and database exploitation.
15. John the Ripper
Features:
- Scanner Capacity: Password hash cracking
- Manual pentest: Yes (password auditing tool)
- Accuracy: High for weak or reused passwords
- Vulnerability management: No
- Compliance: Supports ISO 27001 password policy validation (indirect)
- Price: Free (open source); Pro version available
John the Ripper is a powerful password security auditing and recovery tool used to test the strength of passwords. It supports brute-force attacks, dictionary attacks, and hybrid approaches against password hashes obtained during penetration tests.
The tool works with hundreds of hash formats including Unix, Windows, macOS, database hashes, and application-level password storage. It is commonly used post-exploitation to assess password hygiene and credential reuse risks.
Customer Review:
One of the most trusted password auditing tools in the security community.
Pros:
- Extremely fast password cracking engine
- Supports a wide range of hash formats
- Open-source with strong community support
- Highly customizable attack modes
Limitations:
- Command-line only
- Requires pre-obtained password hashes
- Not suitable for web app scanning on its own
Best For: Password strength testing, credential auditing, and post-exploitation assessments.
Free & Open-Source Web Application Penetration Testing Tools
Open-source tools remain the foundation of modern web application security testing. They offer deep flexibility, strong community support, and the ability to customize scans to match your environment. Below are some of the most widely used OSS tools for web app and API pentesting: each with a crisp overview of what it does well and where it falls short.
16. OWASP ZAP (Zed Attack Proxy)
OWASP ZAP is one of the most popular open-source DAST tools for web apps and APIs. It offers automated scanning, a powerful intercepting proxy, fuzzing capabilities, and support for authenticated testing. ZAP is especially useful for teams that need a free, extensible baseline scanner.
Best For: Small teams, beginners, or CI-driven baseline scans.
Limitations: Slower updates compared to commercial scanners; produces false positives that require manual validation.
17. Burp Suite Community Edition
Burp CE provides the core intercepting proxy and manual testing tools that make Burp Suite so widely adopted. While it lacks automated scanning and many Pro features, it’s still excellent for manual recon, API testing, and understanding how requests and responses flow.
Best For: Learning web hacking fundamentals; manual testing of small apps.
Limitations: No automated scanner; slower performance; limited extensions.
18. Nikto
Nikto is a long-standing open-source web server scanner that checks for outdated versions, known misconfigurations, and dangerous files. It’s lightweight, easy to run, and useful for quick reconnaissance around web assets before deeper penetration testing.
Best For: Fast server misconfiguration checks.
Limitations: Not API-focused; lacks depth for modern frameworks.
19. Nmap + NSE (Nmap Scripting Engine)
Nmap is widely used for network discovery, but with NSE scripts, it becomes a powerful reconnaissance tool for APIs and web services. It helps detect open ports, API gateways, TLS issues, and known vulnerabilities using community-maintained scripts.
Best For: Attack-surface mapping and initial recon.
Limitations: Not a dedicated web vulnerability scanner; requires scripting for advanced testing.
20. OWASP Amass
Amass is one of the best tools for external attack-surface mapping. It uses OSINT, DNS enumeration, certificate transparency logs, and passive/active data sources to uncover domains, shadow APIs, dev endpoints, and forgotten assets.
Best For: Discovering external assets and mapping API exposure.
Limitations: Generates huge volumes of data that require triaging.
21. Arachni
Arachni is a high-performance, modular scanning framework for web apps. It supports both REST and GraphQL, fuzzes endpoints, and detects common issues like SQLi, XSS, and auth flaws.
Best For: Lightweight automated scans with decent API support.
Limitations: Project development slowed in recent years; not updated for newer frameworks.
22. Metasploit Framework
Metasploit allows security engineers to simulate real-world exploits. For web apps and APIs, it helps validate vulnerabilities like RCE, insecure authentication, and injection through controlled exploit modules.
Best For: Advanced exploit testing and chaining vulnerabilities.
Limitations: Requires strong pentesting expertise; not suitable for beginners.
Astra Pentest is built by the team of experts that helped secure Microsoft, Adobe, Facebook, and Buffer

Top Features That Every Web Pentest Tool Should Have
Here are the top features offered by good web application penetration testing tools that you would need to eliminate any security vulnerabilities.
1. Vulnerability Scanning
The web app pentesting tool should have a comprehensive vulnerability scanner capable of scanning for a wide range of vulnerabilities from OWASP Top 10 and SANS 25 to any new vulnerabilities based on CVEs, bug bounty reports, and other trusty sources.
2. Detailed Reporting
A good pentesting tool is accompanied by better reporting, without which it would be incomplete. Reports should have executive summaries, risk scores based on CVSS scores, and contextual data for easy prioritization and steps for remediation.
3. Vetted Scan Results
Automated vulnerability scans often generate false positives. The tool should have the support of expert pentesters who can vet and weed out any false positives from the scan results for a more effortless remediation experience for you.
4. Scan Behind Logins
The tool should be capable of scanning behind logins and have an extension for recording login information to do the same. This enables the tool to carry out authenticated scans based on different roles.
5. Deep Integrations
Modern web pentest tools should be capable of integrating with other CI/CD tools, such as code repositories like Jenkins, GitHub, & GitLab, or management and communication tools such as Jira & Slack, among others.
6. Good Remediation Support
Another component of a good web pentest tool is good remediation support that helps customers mitigate the detected and identified vulnerabilities with ease. Remediation support entails contacting expert pen-testers and providing step-by-step remediation measures.
7. Easy To Use Dashboard
The dashboard should be easy to use and navigate without presenting the customer with an overload of information. It should have options to download the report and view the scan results in real-time.
Real-World Benefits of Web Application Penetration Testing Tools
Modern web applications are a mesh of frontends, microservices, APIs, serverless functions, and third-party integrations. That complexity creates attack paths that traditional testing methods (QA, unit tests, or CI checks) simply cannot see. Web application penetration testing tools close this gap by continuously mapping your attack surface and surfacing vulnerabilities that have real exploitability.
Here are the practical, measurable benefits security and engineering leaders see when using the right mix of tools.
1. Catch Vulnerabilities Before They Become Production Incidents
Automated DAST scanners uncover issues like XSS, SQL injection, misconfigurations, exposed endpoints, and broken authentication at runtime: the same conditions attackers exploit. Combined with SAST and manual validation, you reduce the risk of a high-severity vulnerability escaping into production unnoticed.
This directly improves MTTR (mean time to remediation) and reduces the probability of CVSS 8.0+ issues making it into customer-facing environments.
2. Validate What’s Actually Exploitable (Reduce False Positives)
Most scanners generate noise. False positives waste engineering time and create friction between AppSec and Dev teams.
Tools that support safe exploit testing, replayable PoCs, and manual validation confirm what’s actually exploitable, so teams focus on vulnerabilities that truly matter.
This is especially important for complex business logic flaws, authentication bypasses, and chained vulnerabilities that automated scanners miss.
3. Strengthen Compliance and Audit Readiness
Frameworks like PCI-DSS, ISO 27001, SOC 2, HIPAA, GDPR require periodic or continuous security testing. Pentest tools provide:
- Audit-ready reports
- CVSS scoring
- Evidence of exploitability
- Gap analysis against the OWASP Top 10
- Documentation for remediation timelines
This reduces compliance effort and strengthens security posture across audits, vendor assessments, and enterprise customer reviews.
4. Integrate Security Early Into DevSecOps & CI/CD
Modern tools integrate with CI/CD platforms (GitHub Actions, GitLab, Jenkins, and Bitbucket) to run automated scans on every pull request or pre-deployment stage. Teams can:
- Block deployments on critical vulnerabilities
- Auto-create Jira or Linear tickets
- Track remediation SLAs
- Enforce security gates without slowing release velocity
This shifts security left without overwhelming developers.
5. Provide Continuous Monitoring of Rapidly Changing Environments
In cloud-native environments, assets change constantly: new endpoints, updated APIs, modified WAF rules, and new IAM roles. Continuous scanning ensures:
- Newly added endpoints are tested
- Configuration drift is caught early
- Shadow APIs and forgotten dev endpoints are flagged
- Exposed cloud services are discovered before attackers find them
This is especially critical in microservices and multi-cloud setups where teams often lose visibility.
6. Improve Developer Awareness and Secure Coding Practices
Good tools come with:
- Clear explanations of root cause
- Impact demonstrations
- Framework-specific guidance (React, Django, Node, Spring)
- Code snippets for fixing vulnerabilities
Developers understand not just what broke, but why: which helps them write more secure code in future sprints.
7. Reduce Breach Costs and Risk Exposure
A single exploited vulnerability can lead to customer data loss, regulatory exposure, and reputational damage. Early detection and continuous scanning directly lowers:
- Probability of breach
- Average dwell time
- Average cost per incident
- Operational and legal fallout
This is why the most mature security teams treat web app pentesting tools as part of their core security infrastructure.
Different Types of Tools Used by Pentesters
The process of pentesting is generally divided into five steps. The Pentest starts with planning, followed by scan, infiltration, escalation, and analysis. Each of these steps requires certain kinds of tools. We will look into different types of tools a Pentester needs to be equipped with.
1. Port Scanners
You can use a port scanner to send a packet to specific ports to uncover security vulnerabilities. Ports are virtual points where network connections start or end and each port is associated with a different process. Port scanners are used to identify open ports in a network that are treated as vulnerabilities.
2. Vulnerability Scanners
A vulnerability scanner is an automated tool that you use to create an inventory of all IT assets and then test them for known vulnerabilities. A security professional can use the report generated by a vulnerability scanner to identify security loopholes and categorize them by severity.
3. Network Sniffers
Network sniffers can monitor network traffic and information. It can be used by blackhats to ‘sniff’ traffic to steal passwords or other information. Network administrators can use it to find vulnerabilities and ensure a secure environment.
4. Intercept Proxy
An intercepting proxy sits between the client-side browser and the internet. It allows you to monitor and alter responses and requests by intercepting the connection. It is a very important tool for web application vulnerability assessment.
5. Password Cracker
As the name suggests, a password cracker is used to crack passwords. Several different password-cracking techniques include brute force, dictionary attacks, combined dictionary attacks, Rainbow table attacks, etc. Both attackers and pen-testers use these techniques.
Top Web App Penetration Testing Techniques
1. Black Box Pentesting
Black-box penetration testing is a technique where the pentester does not have any prior information about the target to be exploited.
Since the testers don’t have any information about the target, it is the closest simulation to a real attack. The tester has no information regarding the source codes or internal software information, such as structure and application design.
2. White Box Pentesting
White Box Penetration Testing is a technique in which a system or network’s internal structure and function are known to the penetration tester, including aspects of the application’s architecture and implementation that may not be known to the software’s developers. It is often used to pentest a company’s internal networks and systems.
3. Gray Box Pentesting
Gray box penetration testing is a type in which the pentesters have partial knowledge of the network and infrastructure of the system they are testing. It is a combination of black-box and white-box pentesting where a solid understanding of the system is required, and it is often used in more controlled environments.
Final Thoughts
By understanding the importance of web penetration testing and leveraging the right tools, you can significantly enhance your security posture. Choosing a tool that aligns with your specific needs is imperative, whether it’s a comprehensive platform like Astra Pentest or specialized tools for network scanning (Nmap) or protocol analysis (Wireshark).
Remember, penetration testing is an ongoing process. Regular assessments, coupled with effective vulnerability management, are essential to staying ahead of cyber threats.
FAQs
1. What are Web Application Penetration Testing Tools?
Web application penetration testing tools are software solutions that help identify security vulnerabilities in web apps by simulating real-world attacks. These tools analyze application logic, authentication flows, APIs, and server interactions to uncover issues such as SQL injection, XSS, insecure authentication, and misconfigurations.
2. How do Web Application Pentesting Tools work?
Web pentesting tools work by crawling the application, mapping endpoints, and sending crafted requests to detect vulnerabilities. Some tools rely on automated scanning, while others support manual testing through intercepting proxies, fuzzing, or exploit frameworks. Advanced tools combine automation with expert validation to reduce false positives.
3. What is the difference between Web Application Pentesting Tools and Vulnerability Scanners?
Vulnerability scanners primarily rely on automated checks to flag potential weaknesses, often resulting in false positives. Web application pentesting tools go further by supporting manual testing, business logic validation, and exploit verification, helping teams understand whether vulnerabilities are actually exploitable in real-world scenarios.
4. Are open-source Web Application Pentesting Tools sufficient?
Open-source tools like OWASP ZAP, Nmap, and Metasploit are excellent for learning, reconnaissance, and baseline security testing. However, they often require skilled operators and manual validation. For production environments and compliance needs, many teams complement open-source tools with commercial platforms that offer better coverage, reporting, and support.
Explore Our Penetration Testing Series
This post is part of a series on penetration testing.
You can also check out other articles below.

Chapter 1: What is Penetration Testing?
Chapter 2: Different Types of Pentest Testing
Chapter 3: Top 5 Pentest Methodology
Chapter 4: Top Pentest Companies to Consider in 2026
Chapter 5: Best Pentest Online Tools – Top List
Chapter 6: A Super Easy Guide on WordPress Pentest
Chapter 7: Average Penetration Testing Cost in 2026
Chapter 8: Pentest Reporting (Sample Report)
Chapter 9: Web App Pentest Guide
Chapter 10: Pentest Website Guide







