George Washington once said, “The best defense is a good offense.” With companies conducting one penetration test a year, which typically drags on for a few months, Mr. President’s wise words need to be followed more closely.
Is the traditional annual pentest enough to keep your business safe? This is where penetration testing as a service (PTaaS) steps in! Before we jump in, let’s start by understanding what PTaaS is in detail.
What is Penetration Testing as a Service (PTaaS)?
Penetration testing as a service (PTaaS) is a subscription-based model where organizations outsource their penetration testing needs to a third-party provider. It brings security engineers closer to the development team & makes the entire penetration test process more effective in terms of both time & cost.
PTaaS vs. Traditional vs. In-House
While traditional penetration testing has served organizations well, it often lacks the agility and scalability needed in today’s dynamic threat landscape. Here’s a comparison between PTaaS & Traditional Pentesting on factors that modern engineering teams care about:
| Factor | PTaaS (Astra) | Traditional Pentesting | In-House Pentesting |
|---|---|---|---|
| Cost | Predictable subscription or per-target pricing; scales with usage | High one-off fees per test; expensive for frequent testing | High fixed costs (salaries, benefits, training) regardless of testing frequency |
| Team Expertise | Blend of automation + specialized security engineers; continuously updated attack library | Strong manual expertise, but dependent on individual testers; less automation | Depends on hires; often limited to generalist security engineers |
| Speed | Continuous scanning + results in hours; rescans in <2 days | Engagements scheduled weeks/months in advance; results in 2–6 weeks | On-demand if resources available; bottlenecked by team capacity |
| Risk Ownership | Shared where the platform tracks findings & MTTR; vendor assists in remediation | Vendor reports issues, remediation fully on your team | Fully your responsibility, including detection, prioritization, and fixes |
| Integration Effort | Native CI/CD + dev tool integrations; minimal setup | Minimal integration, results delivered as static reports | Full integration possible but requires internal engineering effort |
| Coverage | Live traffic + incremental scans; supports REST, GraphQL, SOAP, mobile, serverless | Scope-based; only tests defined endpoints during engagement | Scope determined internally; often limited to known endpoints |
| Adaptability | Can scale from small to enterprise; supports fast-changing environments | Inflexible as re-scoping is needed for changes | Flexible if team can keep up with changes |
| Finding Quality | Automation catches broad issues; human testing finds logic flaws | Manual expertise strong for logic flaws; may miss breadth due to time limits | Quality depends on in-house skill depth and tooling investment |
| Testing Frequency | Continuous | Point-in-time | Continuous (if resources allow) |
Designed as a project-based service, the traditional one-time engagement model is characterized by hefty upfront payments, patchy communication from security analysts, and lengthy penetration testing cycles. The wait for the final report – delivered in weeks or months – leaves you vulnerable in between and hinders timely remediation.
In contrast, PTaaS adopts modern engineering methodologies to deliver continuous security testing, real-time reporting, and agile pentesting models integrated seamlessly within your development lifecycle.
This leads to faster identification, enhanced agility, and improved ROIs. It helps you transition from reactive fixes to continuous improvement. PTaaS accelerates your giant leap from DevOps to DevSecOps.
Key Benefits of Penetration Testing as a Service (PTaaS)
Security Teams
- Continuous Testing: Always-on assessments identify vulnerabilities as soon as they appear, not just during quarterly or annual cycles.
- Reduced Noise: High accuracy and fewer false positives free up time for actual remediation work, rather than chasing false alarms.
- Scalable Testing: Run small, targeted tests or broad enterprise-wide assessments without overloading internal staff.
- Expert Insight: Access to seasoned penetration testers for advanced, manual validation and guidance.
IT / Admin Teams
- Real-Time Alerts: Instant notification of critical vulnerabilities so patching can happen before exploitation.
- CI/CD Integration: Automated scans integrated into deployment pipelines to catch security gaps before production release.
- Policy and Compliance Alignment: Easy mapping to security policies and regulatory standards such as PCI DSS, HIPAA, and GDPR.
- Operational Efficiency: Faster remediation cycles reduce downtime and resource drain.
C-Suite and Executives
- Clear ROI: Lower costs compared to building and maintaining an in-house pentest team.
- Business-Focused Reports: Executive summaries that translate technical findings into risk, financial impact, and strategic priorities.
- Compliance Confidence: Demonstrable adherence to industry regulations improves stakeholder trust.
- Reputation Protection: Reduced breach risk means stronger brand credibility and customer trust.
How to Choose a PTaaS (Penetration Testing as a Service) Platform?
With many local and international PTaaS vendors in the market and diverse offerings, choosing the ideal platform can take time and effort. Here are some essential features to look for in your ideal PTaaS vendor:
1. Comprehensive Vulnerability Detection:
The automated and manual pentest should scan and identify known, unknown, and emerging vulnerabilities, including those listed in OWASP 10 and SANS 25. They should also actively look for attack vectors specific to your industry and the tech stack you use.
2. Advanced Threat Detection:
While individual low-risk vulnerabilities seem harmless, they can create high-criticality attack vectors together. This is especially true for vulnerabilities related to business logic, IAM (Identity and Access Management), and payment manipulation.
Due to their sophisticated nature, most automated tools miss them, necessitating timely manual penetration testing by certified experts.
3. Zero False Positives:
False positives often lead to wasting time and precious resources across the board. The ideal PTaaS platform should offer minimal false positives – through expert vetted results of automated and manual pentests – if not eliminate them altogether.
4. Engineer-Friendly Reports:
Clear and concise reports are essential for long-term security and effective decision-making. Customizable reports, based on user roles with developer versions, including vulnerability details, CVSS score, impact, PoC, and steps to replicate and patch it, go a long way.
5. ‘Platform’ Approach to PTaaS:
Choose a company that offers a centralized dashboard to track real-time updates on penetration tests, key reports, and streamlined communication to avoid bottlenecks. An intuitive interface, customizable views, and easy user management help avoid bottlenecks and delays.
Potential Challenges of PTaaS
1. Rigid and Standardized Methods
Many PTaaS providers follow standardized testing methods to maintain consistency and efficiency. While this approach works for common vulnerabilities, it can miss industry-specific risks. For example, a healthcare provider might face HIPAA-related API vulnerabilities that are not covered in a generic OWASP-based test. Different industries, business models, and threat landscapes require tailored strategies.
Mitigation: Choose a provider that customizes test cases for your sector. Astra adds targeted checks for compliance and industry-specific threats.
2. Limited Data Access and Sharing
In-depth penetration testing often requires access to internal systems and sensitive data. According to the Ponemon Institute, 46% of security teams say internal access restrictions limit the depth of external pentests. Without adequate access, some vulnerabilities remain hidden. Sharing sensitive data can also raise privacy and security concerns.
Mitigation: Use secure, NDA-backed access protocols and encrypted channels. Astra employs these measures to maintain security while enabling full-scope testing.
3. Skill Gaps and Lack of Expertise
The quality of a pentest depends heavily on the tester’s skill and experience. Some providers may assign testers without specific expertise, leading to missed vulnerabilities; for instance, misconfigured S3 buckets remain one of the top exploited misconfigurations in cloud breaches.
Mitigation: Work with providers who assign certified engineers experienced in web, API, and cloud security. Astra keeps its false positive rate below 5% through expert-led testing.
4. False Positives and Efficiency
Automated scans can produce false positives, leading teams to waste time chasing non-existent vulnerabilities. A financial services firm once reported a three-week remediation delay after pursuing false positives from an automated scan.
Mitigation: Opt for a hybrid testing approach that combines automation with manual validation. Astra verifies every reported vulnerability before it reaches your team.
5. Cost and Return on Investment
Determining the optimal PTaaS budget can be challenging. While quality testing is essential, leaders must ensure it delivers measurable value. IBM’s 2024 Cost of a Data Breach report estimates the average breach cost at $4.45M preventing even one high-risk vulnerability can justify the investment.
Mitigation: Map each finding to potential financial impact. Astra provides reports that quantify risk reduction, helping demonstrate ROI.
How Does a PTaaS Platform Work?
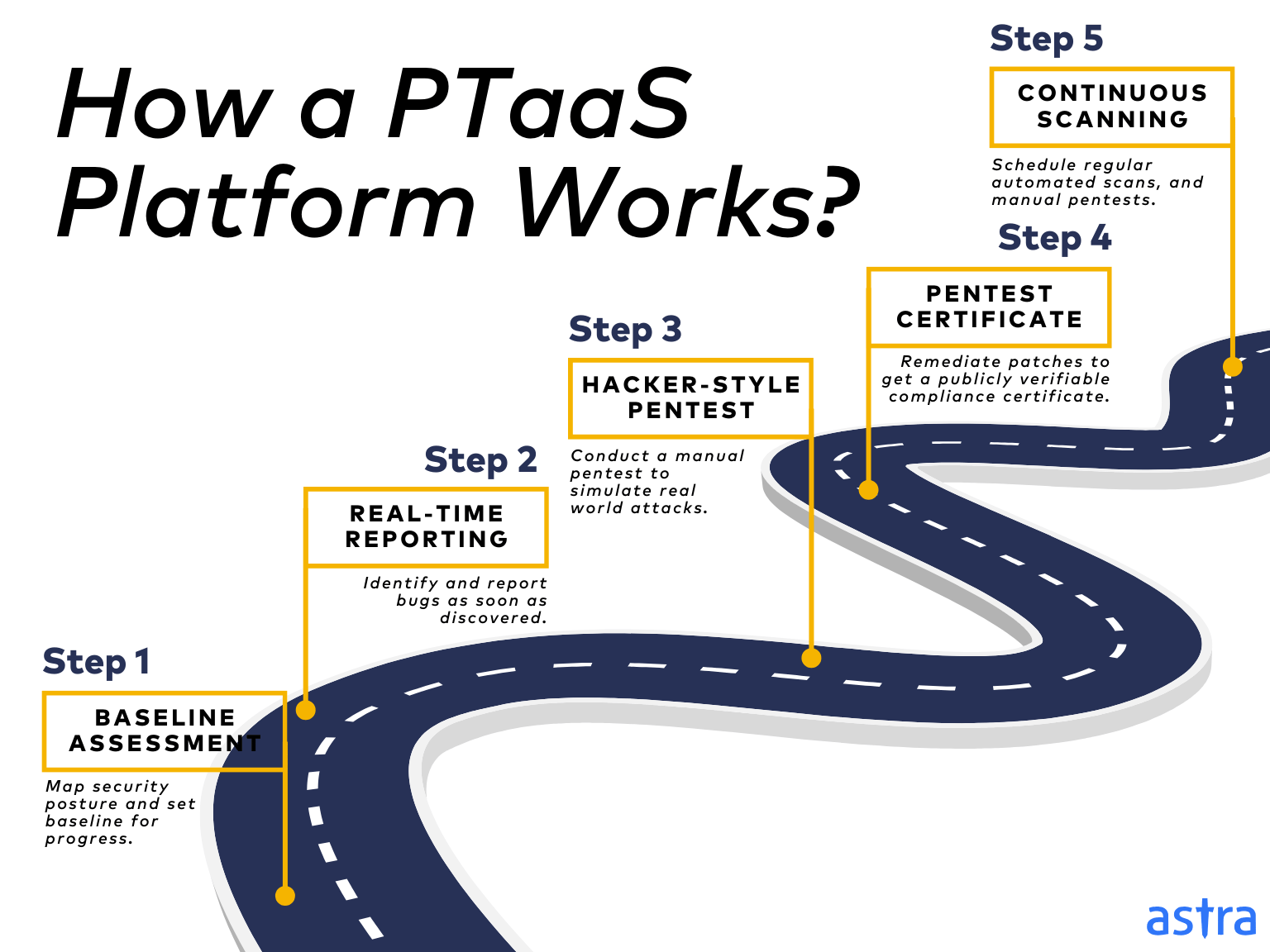
Step 1: Baseline Assessment
The process starts with an automated scanning engine to map your systems, applications, and network to generate an initial report of your current security posture – how the security measures in place would fare in case of an attack.
This report acts as the baseline against which all future progress is measured. As such, it also details proof of findings and recommendations for enhanced security measures.
Step 2: Real-Time Reporting
With the onslaught of emerging CVEs and cyberattacks, real-time reporting is the cornerstone of contemporary digital security. Vulnerabilities are identified and reported as soon as they are discovered.
This near real-time pentest reporting empowers you to address issues swiftly, minimize exposure, and enable proactive remediation.
Step 3: Hacker-Style Pentesting
While automated scans are effective, they can’t replicate the ingenuity of human attackers. PTaaS goes beyond by employing experienced pentesters to conduct “hacker-style” offensive security tests that simulate real-world attacks.
They leverage their years of experience in thinking like a hacker, AI-powered test cases, and industry-standard tools to uncover attack vectors, such as payment manipulation and business logic vulnerabilities — which often go undetected by automated vulnerability scanners.
Step 4: Pentest Reports and Certificates
Instead of simply pinpointing vulnerabilities, the ideal PTaaS platforms offer end-to-end vulnerability management services. This translates to providing detailed reports with Proof of Concepts (PoCs), vulnerability details, CVSS score, and steps to recreate and patch the same.
Moreover, after remediation, they verify the above to help you generate clean reports and publicly verifiable pentest certificates that facilitate compliance audits and strengthen your stakeholders’ trust.
Step 5: Continuous Vulnerability Assessment & Penetration Testing
With new zero days being identified daily, continuous vigilance is crucial. The ideal PTaaS platform helps you schedule regular automated scans and regression tests and run ad-hoc pentests.
Moreover, they help conduct quarterly or half-yearly manual pentests to identify new vulnerabilities that might have surfaced to ensure compliance across standards such as SOC2, ISO27001, CIS, GDPR, and HIPAA.
What Features Should You Expect From a PTaaS Platform?
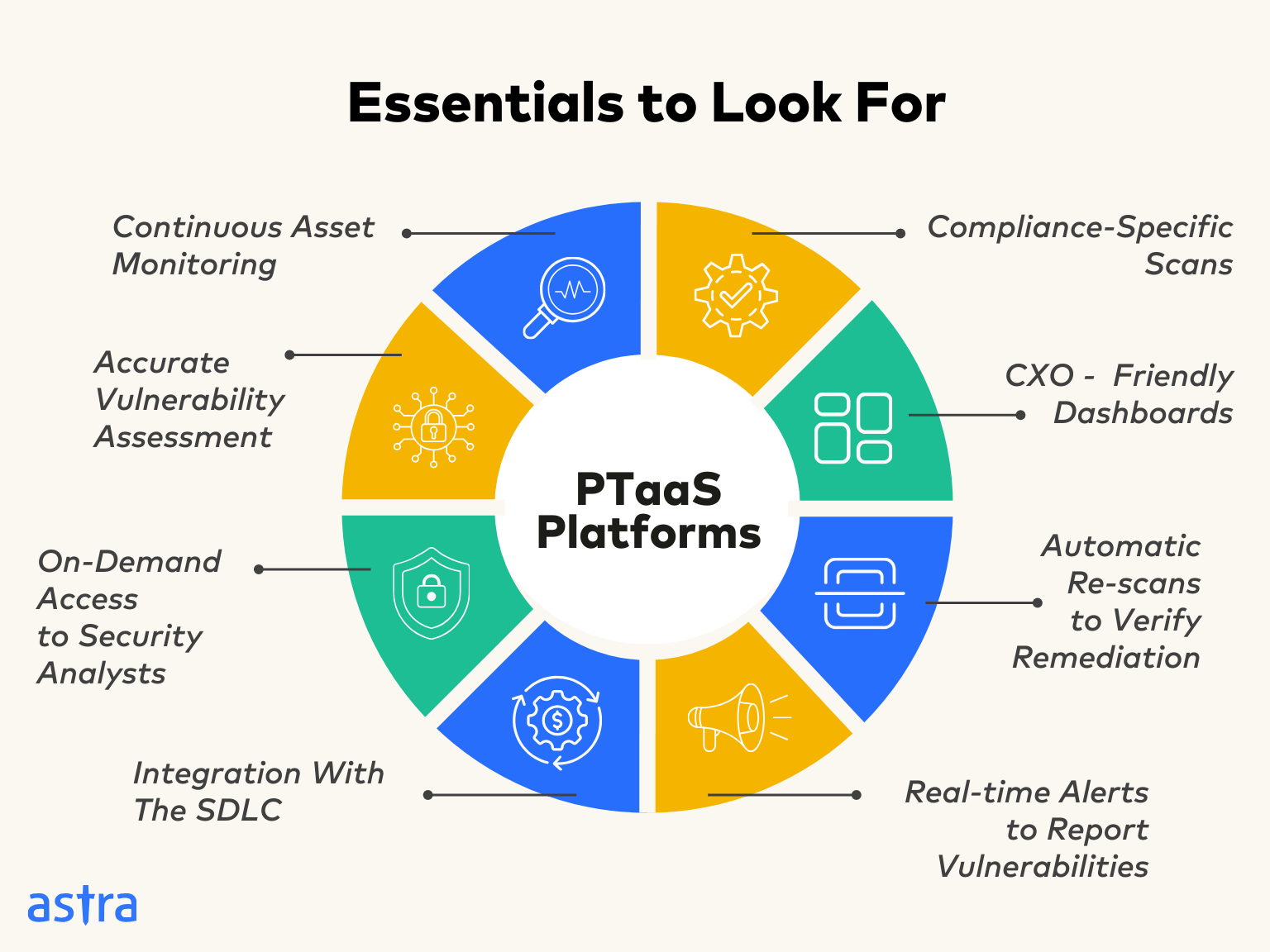
- Continuous monitoring of your assets
- On-demand access to pentesters and security analysts
- Fast results from human-led & automation-powered Pentests
- Accurate vulnerability assessment
- Integration with your SDLC
- Real-time alerts to report vulnerabilities
- Minimal gap between discovery and remediation of vulnerabilities
- Automatic rescans to verify the remediation
The Best PTaaS (Penetration Testing as a Service) Platform: Astra Pentest
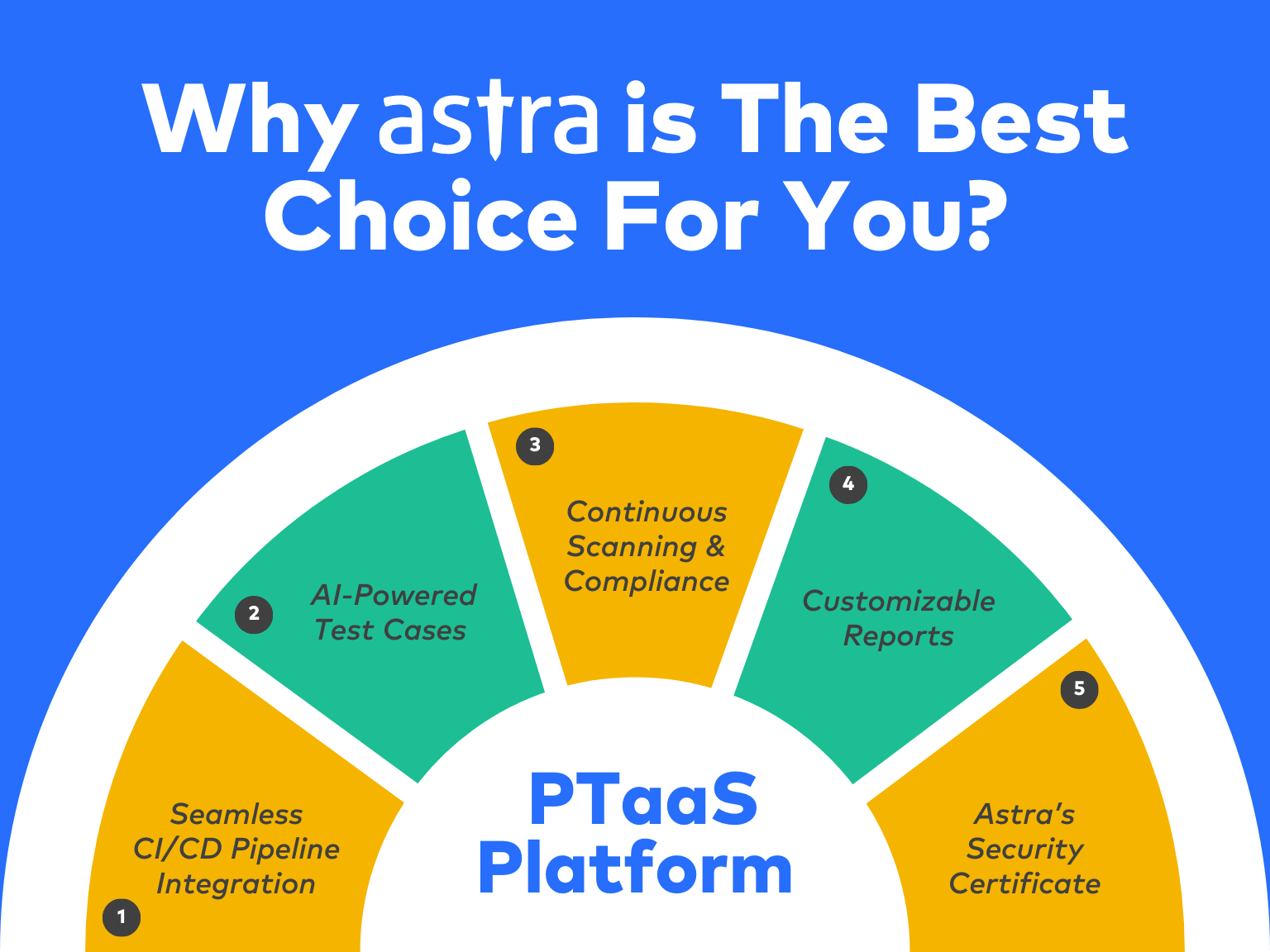
Astra is a one-of-a-kind PTaaS Platform that makes otherwise chaotic penetration tests a breeze. Astra’s continuous vulnerability scanner emulates hacker behavior to scan applications for 9300+ security tests. CTOs & CISOs love Astra because it helps them fix vulnerabilities in record time and move from DevOps to DevSecOps with Astra’s CI/CD integrations.
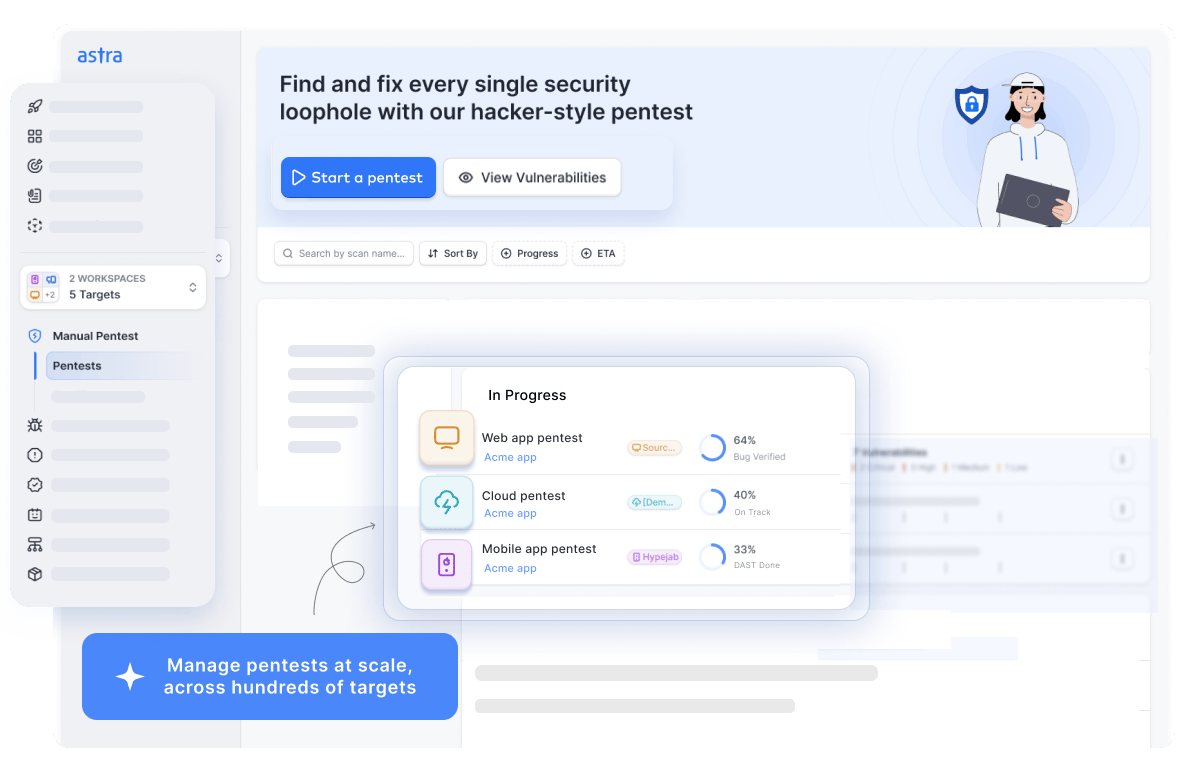
Astra is loved by companies across the globe. Last year, Astra uncovered 2,000,000+ vulnerabilities for its customers, saving customers $69M+ in potential losses due to security vulnerabilities.
With zero false positives, seamless tech stack integrations, and real-time expert support, Astra makes pentests simple, effective, and hassle-free.
Still don’t believe us? Take a look at what some of our 650+ customers have to say!
Compliance Mapping with PTaaS
| Compliance Framework | Pentest Requirements | How Astra Helps |
|---|---|---|
| PCI DSS (Payment Card Industry Data Security Standard) | Requires annual penetration testing and after any significant changes. Must cover internal and external systems that handle cardholder data. | Provides on-demand and scheduled pentests for web apps, APIs, and infrastructure. Generates PCI-ready reports with clear remediation steps for auditors. |
| HIPAA (Health Insurance Portability and Accountability Act) | Requires regular security assessments to identify vulnerabilities in systems handling Protected Health Information (PHI). | Runs continuous vulnerability scans and targeted pentests. Produces detailed reports that map directly to HIPAA security rule requirements. |
| ISO 27001 | Requires regular security testing as part of the Information Security Management System (ISMS). | Integrates testing into your ISMS process. Maintains historical test records and provides risk-based remediation tracking for audit readiness. |
| SOC 2 | Security principle requires periodic testing of controls to prevent data breaches. | Offers recurring pentests with evidence-based reporting that aligns with SOC 2 trust service criteria. |
| GDPR (General Data Protection Regulation) | Requires data controllers and processors to ensure ongoing confidentiality, integrity, and availability of systems. | Continuous scanning and pentests identify and help remediate vulnerabilities that could lead to data exposure. |
What to Look For in a PTaaS Solution?
1. Depth and Breadth of Pentest Capabilities:
A PTaaS solution is only as good as the skillset of its security analysts and engineers. Look for platforms equipped with scanners to run event-triggered, continuous, and ad-hoc scans across various types of assets designed by qualified security engineers with hands-on experience.
2. Quality of Pentesting Experience:
Security engineers should also hold industry-standard certifications, such as OSCP, CEH, CISSP, etc. It would be fair to mention that the security industry has enough talented security engineers who do not pursue certification but are still at the top of their game. Experience in pentesting specific types of applications, such as those used in tourism, contributes significantly to the quality of pentests, especially with complex applications.
3. Remediation Support:
Look for platforms that offer customizable executive reports for CXOs and exhaustive reports for developers, catering to both automated and manual penetration tests. Some basics include vulnerability details, CVSS score, compliance impact, and steps to replicate and patch it.
Pro Tip: An active customer support team also helps solve planning and execution bottlenecks by providing better insights into vulnerabilities to speed up the remediation processes
4. Seamless Workflow Integrations:
Validate the availability and viability of integrations with your CI/CD pipeline, such as Jira, GitHub, GitLab, and Slack, to facilitate the transition from DevOps to DevSecOps, prioritizing security.
5. Compliance-Specific Scans:
Although most compliance guidelines with industry-specific regulations (e.g., HIPAA, PCI-DSS, SOC2, ISO 27001) typically require only one annual penetration test, PTaaS platforms offer a unique real-time monitoring capability.
Pro-Tip: With in-built compliance-focused scans and reporting algorithms, they help you avoid fines associated with data breaches.
Best PTaaS Platforms 2025
| Company | Core Offering | Strengths | Limitations |
|---|---|---|---|
| Astra Pentest | Pentest as a Service (PTaaS) with continuous vulnerability scanning and manual testing. | Zero false positives, CI/CD integration, compliance-ready reports, expert-led testing. | Primarily focused on web, API, and cloud; not a full SOC provider. |
| CrowdStrike | Threat detection and endpoint security with some offensive testing services. | Strong in incident response and endpoint protection. | Pentesting is not the primary focus. |
| HackerOne | Bug bounty platform connecting companies with ethical hackers. | Crowdsourced vulnerability discovery at scale. | Findings can vary in quality, limited structured remediation guidance. |
| Rapid7 | Security platform with scanning, analytics, and pentesting services. | Strong automation, broad vulnerability coverage. | Manual pentesting depth may be less than specialist providers. |
| Secureworks | Managed security services with some offensive testing. | End-to-end security program support. | Pentesting services are packaged with broader MSSP offerings. |
| Intruder | Automated vulnerability scanning with basic pentest capabilities. | Simple setup, cost-effective for smaller businesses. | Limited manual testing and deeper exploitation checks. |
| Cobalt | Pentest platform connecting clients with vetted testers. | Flexible scheduling, global tester pool. | Coordination can take longer, depends on freelancer availability. |
| ScienceSoft | IT consulting with security testing capabilities. | Offers a range of IT services beyond security. | Security may not be the sole area of specialization. |
| Indusface | Web application security testing and WAF solutions. | Integrated testing and protection. | Primarily focused on web apps, limited infrastructure coverage. |
| Cyberhunter | Penetration testing and cyber defense training. | Good for awareness and preparedness programs. | Less automation and integration into CI/CD workflows. |
2025 Trends in Penetration Testing
Penetration testing is shifting from isolated, annual exercises to continuous, integrated security practices. In 2025, several trends are shaping how companies approach testing:
- Continuous Pentesting: Businesses are embedding pentests into CI/CD pipelines to catch vulnerabilities before release.
- AI-Augmented Testing: Testers are utilizing AI to expedite reconnaissance, payload generation, and exploit detection, thereby reducing manual effort for repetitive tasks.
- API and Cloud Focus: With APIs and cloud workloads becoming top attack surfaces, more tests target these environments specifically.
- Compliance-Driven Testing: Frameworks like PCI DSS 4.0 and evolving privacy laws are pushing companies toward more frequent and documented tests.
- Hybrid Testing Models: Combining automated scanning with expert-led manual verification is becoming the norm to ensure depth and accuracy.
Final Thoughts
While vulnerability assessments and traditional pentests served their purpose, today’s dynamic threat landscape demands a more proactive approach: penetration testing as a service (PTaaS).
In the coming years, the PTaaS model will continue to evolve to become a natural extension of both, the engineering and security teams of an organization. According to Gartner, PTaaS appeals to organizations that aren’t looking to merely achieve but ‘beat compliance’, and we couldn’t agree more!
Building on traditional pentesting functionality, PTaaS equips you with real-time vulnerability detection, reporting, zero false positives, seamless CI/CD pipeline integration into your development process, and faster remediation.
Choose a platform with comprehensive testing, advanced threat detection, and user-friendly features. Embrace a proactive approach to security with Astra’s PTaaS Platform.
FAQs
1. What does PTaaS mean?
PTaaS (Penetration Testing as a Service) platforms offer an all-in-one experience by combining human, AI-augmented, and automated Pentesting services to deliver a holistic security approach. It is crucial to help your business make the leap from DevOps to DevSecOps.
2. What is the cost of Penetration Testing (PTaaS)?
The cost of Penetration Testing depends upon the scope of the test, the size of your organization, and the number of scans. It ranges between $400 and $1000 per scan for websites and between $700 and $5999 for applications.
3. What is the timeline for Pentesting (PTaaS)?
A typical automated pentest can take anywhere from a few minutes to 36 hours. Manual pentest can take a bit longer and usually range between 7-10 business days. However the same may vary based on the scope of the pentest and complexity of the digital asset being scanned.