Key Takeaways
- ISO 27001 penetration testing is not explicitly mandated, but auditors universally expect it as evidence for controls A.8.8 and A.8.29
- Pentest at least annually and after every major infrastructure or application change. Complete testing 6–8 weeks before any audit to leave the remediation runway.
- Reports must map findings to specific Annex A controls, include severity ratings, remediation guidance, and retesting proof
- Pentest results feed directly into three critical ISMS documents: the risk register, the risk treatment plan, and the Statement of Applicability
- Aligning your methodology to OWASP, NIST SP 800-115, or PTES gives auditors the framework-backed evidence they expect
Okay, to clear the clutter, ISO 27001 compliance tests not your controls but rather their implementation, and even if it does not mandate penetration testing, their requirements are such that you are bound to conduct pentests across the 14 domains and 6 security areas, which fall under your purview.
Moreover, your pentests should be closely aligned with industry methodologies. For example, if you are into web apps, auditors would at least review the OWASP Top 10 vulnerabilities.
With over 96,700 organizations now certified globally (a 35% jump since 2022, according to Pareon) and vulnerability exploitation accounting for 20% of all breaches, auditors are scrutinizing technical controls more closely than ever. Yet many organizations still walk into audits with incomplete pentest evidence, outdated reports (document, document, document!), or no testing at all.
That is why in this piece, we break down exactly which Annex A controls demand penetration testing evidence, what auditors look for during Stage 2 assessments, and how to scope, schedule, and report pentests so they feed directly into your Statement of Applicability and risk treatment plan.
Moreover, we have included checklists throughout this piece for your apps, cloud infra, etc. to best help you develop your pentesting strategy and stay compliant.
Does ISO 27001 require penetration testing?
The short answer: no, not explicitly, but auditors expect it anyway, and skimming past this is the fastest route to a failed audit.
While ISO 27001 defines what an ISMS (Information Security Management System) must achieve, ISO 27002 offers the how. The standard never uses the phrase “you must conduct a penetration test.” But two controls make it nearly impossible to demonstrate compliance without one.
Control A.8.8 (Management of technical vulnerabilities)
The successor to A.12.6, this control requires you to identify your technical vulnerabilities in a timely fashion, evaluate the exposures, and thus take appropriate measures.
Secondly, the implementation guidance in ISO 27002:2022 explicitly states that organizations should “perform periodic, documented penetration tests, either by internal staff or by an authenticated third party.” That basically means you really can’t work your way around a pentest.
Control A.8.29 (Security testing in development and acceptance)
Formed by merging the old A.14.2.8 and A.14.2.9, this control mandates security testing throughout development and acceptance phases. Its guidance explicitly calls for “performing penetration tests to identify weak coding and design.” If you ship software, this control applies.
Several other controls shout out to penetration testing as a supporting activity. For example, A.8.25 treats pentesting as a prerequisite for secure development, A.8.16 posits it as an extension of your security monitoring, while A.5.36 puts it as a method you use to verify your compliance.
Want your pentest findings to plug directly into your risk register, treatment plan, and SoA? Astra’s compliance-first reporting makes that workflow seamless. Book your pentest now
What auditors actually look for during Stage 2?
Stage 2 is the certification audit, in which auditors verify the real-world implementation of your controls. Firstly, they use your Statement of Applicability as the roadmap and then check whether your controls actually work. For penetration testing, they typically expect:
Second on the list is a signed pentest report no older than 12 months, with clear scope definitions, methodologies used, and tester qualifications (CREST or OSCP certifications carry weight!).
They expect that in your findings, you show severity ratings (preferably using CVSS scores) as these define the core of your risk mitigation and management framework, along with exploitation evidence such as screenshots, reproduction steps, etc., to justify these ratings.
Thirdly, remediation logs show which findings have been closed, when, and by whom. Auditors will flag open critical or high-severity findings whose remediation timelines are not documented and tag them as a nonconformity.
That is why ensure that every vulnerability has a remediation recommendation that’s mapped to the relevant Annex A control. Moreover, they may also ask for any Retesting evidence confirming that the fixes actually work.
Lastly, avoid the obvious but not-so-obvious contradiction auditors catch immediately; make sure you register all identified risks in the risk register and map them to the corresponding control. Identifying one and not mapping or mapping it incorrectly often leads to nonconformities that may jeopardize your certification.
Table 1: Summary Table for What Auditors Look For
| Evidence element | What does it contain? | Maps to |
|---|---|---|
| Pentest report | Executive summary, scope definition aligned to ISMS, methodology reference (OWASP/NIST SP 800-115/PTES), detailed findings with CVSS scores and proof-of-concept, remediation recommendations, tester qualifications, testing dates and duration | A.8.8, A.8.29 |
| Remediation tracking log | Each finding linked to assigned owner, target date per SLA (Critical: 48hrs, High: 7 days, Medium: 30 days, Low: 90 days), actual completion date, Jira/ServiceNow ticket reference, deployment evidence | A.8.8, A.8.29 |
| Retest report | Separate validation confirming critical/high findings were resolved; may be a focused follow-up engagement or targeted scans | A.8.8 |
| Risk acceptance records | For unresolved findings: formal risk acceptance in risk register, management sign-off, compensating controls documented, scheduled review date | A.8.8, A.5.7 |
| Scope and methodology documentation | Pentest policy/procedure, rules of engagement, asset inventory showing tested systems mapped to ISMS scope, justification for any exclusions, tester selection criteria | A.8.8, A.8.29, A.5.9 |
| Testing schedule and compliance record | Documented annual testing plan, actual test dates vs. planned, trigger event log showing when ad hoc tests were conducted and why | A.8.8, A.8.29 |
Scope, frequency, and when to trigger a new test
Frequency that satisfies auditors
ISO 27001 prescribes no fixed cadence, but practicing, annual penetration testing aligned with the certification cycle is their baseline expectation.
For high-risk firms such as SaaS platforms, fintech, and healthcare, from a purely time-period POV, undergoing pentesting biannually or quarterly is most beneficial. Supplement this with quarterly vulnerability scans so as to maintain continuous visibility between tests.
Moreover, time your pentests. Make sure you finish 6-8 weeks before any scheduled audit. This offers enough leeway for remediation and retesting, so you walk into the audit with clear evidence and not open findings, sporting an awkward grin, relying on the auditor’s mercy.
Trigger events that demand additional testing
Beyond the annual cycle, these events should be followed by a pentest:
- Major infrastructure changes: cloud migrations, new vendors, network redesigns, or server decommissions
- Significant application releases: new features, architectural changes, API updates
- Post-incident: after any security breach or serious attempted compromise
- Mergers and acquisitions: new systems entering your ISMS scope
- Pre-audit preparation: before certification, surveillance, or recertification audits
Scoping your test to match your ISMS
Try to best align your pentest scope with your ISMS boundaries. Excluding in-scope assets creates blind spots that auditors will flag and frown upon. Make sure to include:
- External attack surface:internet-facing servers, web applications, APIs, and cloud infrastructure
- Internal networks: Active Directory, internal services, lateral movement paths
- Cloud environments: IAM configurations, storage permissions, container security across AWS, Azure, or GCP.
- Applications: all customer-facing and data-processing applications within ISMS scope, including mobile apps.
- Third-party integrations: this includes supplier systems and APIs that process or store data covered by your ISMS.
Moreover, ISO 27001 certification holds affinity towards Gray-box testing as it gives testers enough context (credentials, architecture documentation) to simulate realistic threat scenarios besides identifying vulnerabilities. The ideal strategy would be to plan at least 40 hours of testing for small-to-medium scope and ~5-30 person-days for complex and volatile environments.
Table 2: Your Crisp Web App ISO 270001 Penetration Testing Checklist
| Test area | Annex A controls | Frequency | Dev-friendly approach | Auditor evidence |
|---|---|---|---|---|
| Authentication | A.8.5, A.8.29 | Annual + per major auth change | SAST rules for hardcoded creds on every PR; DAST auth tests on staging | Pentest report section on auth findings; remediation tickets with closure dates |
| Authorization | A.8.5, A.8.3, A.8.29 | Annual + per RBAC change | Automated DAST role-matrix tests on staging; manual testing at release milestones | Findings mapped to user roles tested; evidence of multi-role testing coverage |
| Session management | A.8.5, A.8.29 | Annual + per session architecture change | DAST session tests in CI staging pipeline | Session configuration review; cookie attribute audit log |
| Input validation / injection | A.8.28, A.8.8, A.8.29 | Annual manual + continuous DAST | SAST on every commit; DAST on staging deployments; WAF rule validation | SAST/DAST scan reports; manual pentest findings with PoC; WAF logs |
| Business logic | A.8.29, A.8.26 | Annual (manual only) | Threat modeling during sprint planning; manual tests at major release gates | Documented business logic test cases; findings with exploitation narrative |
| Cryptography | A.8.24, A.8.29 | Annual + after cert/TLS changes | Automated TLS scanning (testssl.sh) in CI; SAST for hardcoded keys | TLS configuration report; cryptographic implementation findings |
| Configuration | A.8.9, A.8.29 | Annual + after infrastructure changes | IaC scanning (Checkov, tfsec) on every deployment; automated config baseline checks | Configuration audit results; hardening benchmark compliance report |
| Error handling | A.8.28, A.8.29 | Annual + continuous DAST | SAST rules for exception handling; DAST error response checks | Error handling findings; evidence of custom error pages |
| Client-side | A.8.28, A.8.29 | Annual + per frontend release | Browser security header scanning in CI; CSP validation | Client-side vulnerability findings; security header audit |
Methodologies that map to audit expectations
Auditors don’t really care for the methodology, but they do care for the structured, repeatable approaches backed by recognized frameworks. Here, citing OWASP, NIST, or PTES in your report signals rigor.
- The OWASP Testing Guide maps directly to A.8.29, providing granularity in test cases for web applications and APIs. With web-facing products part of every tech-stack, OWASP coverage basically becomes table stakes
- NIST SP 800-115 is a governance-oriented framework that weaves testing into the broader risk management cycle. It emphasises formal planning, execution, analysis, and post-testing documentation
- PTES (Penetration Testing Execution Standard) covers the full testing lifecycle across seven phases (from pre-engagement through to exploitation and reporting). It’s especially strong for network and infrastructure testing
The best approach is to layer these: use NIST for governance and planning, OWASP for web and API depth, and PTES for infrastructure coverage.
Table 3: Your Crisp API ISO 270001 Penetration Testing Checklist
| Test area | Annex A controls | Frequency | Dev-friendly approach | Auditor evidence |
|---|---|---|---|---|
| Broken Object Level Authorization (BOLA) | A.8.5, A.8.3, A.8.29 | Annual + per new endpoint | Automated BOLA tests using OpenAPI spec diffs in CI; manual validation at release gates | API-specific findings showing tested endpoints and user role combinations |
| Authentication | A.8.5, A.8.24, A.8.29 | Annual + per auth mechanism change | SAST for hardcoded API keys; automated token validation tests in staging | Auth bypass findings with exploitation evidence; token security review |
| Object Property Level Authorization | A.8.5, A.8.11, A.8.12, A.8.29 | Annual + per data model change | Schema validation in CI comparing response payloads to expected fields; DAST property fuzzing | Findings showing excessive data returned or writable fields exploited |
| Resource consumption | A.8.8, A.8.20, A.8.29 | Annual + per API gateway change | Rate-limit testing in staging; load testing with security focus | Rate-limiting configuration evidence; DoS resilience findings |
| Function Level Authorization (BFLA) | A.8.5, A.8.3, A.8.29 | Annual + per RBAC change | Automated role-based access matrix tests from OpenAPI spec | Authorization matrix document; BFLA test results per role |
| Business flow abuse | A.8.29, A.8.26 | Annual (manual only) | Threat modeling of API business flows during design; rate-limit rules | Business logic test scenarios and results; abuse-case documentation |
| SSRF | A.8.28, A.8.8, A.8.29 | Annual + per integration change | SAST for URL construction patterns; DAST SSRF probes on staging | SSRF findings with internal access evidence |
| Security misconfiguration | A.8.9, A.8.29 | Annual + after config changes | Automated configuration scanning in CI; API gateway policy validation | Configuration audit findings; API gateway hardening report |
| Inventory management | A.8.8, A.8.9, A.8.29 | Quarterly automated + annual manual | API discovery scanning in CI/CD; OpenAPI spec completeness checks | API inventory document; shadow API discovery results |
| Unsafe consumption | A.5.22, A.5.23, A.8.29 | Annual + per new integration | SCA for API client libraries; input validation SAST rules for external data | Third-party API security review; integration risk assessment |
How to Structure Your Report for Auditors?
Your pentest report serves two audiences simultaneously: engineers who fix vulnerabilities and auditors who verify controls. Structure it accordingly:
- Executive summary: Presenting key findings, overall risk posture, and business impact; this is what auditors and leadership read first.
- Scope and Methodology: Document what was tested, how, which frameworks were followed, and test dates.
- Detailed technical findings: with severity ratings, CVSS scores, exploitation evidence, and step-by-step reproduction instructions.
- Annex A control mapping: linking each finding to the specific control it affects (for example, an SQL injection finding maps to both A.8.8 and A.8.29).
- Remediation recommendations: prioritized by risk, with specific implementation guidance.
- The tester qualifications section lists certifications and firm credentials
Astra’s pentest reports include control mapping, CVSS-scored findings, and remediation guidance—structured exactly the way auditors expect to see them.

How Pentest Results Strengthen Your ISMS
Penetration testing feeds three of the most scrutinized documents in your ISMS: the risk register, the risk treatment plan, and the Statement of Applicability. And thus it is almost inevitable.
Feeding the risk register with real data
Clause 6.1.2 requires systematic risk assessment. Pentest findings replace risks that you envisage on paper with concrete evidence of exploitability. A vulnerability scanner might flag an outdated library as “medium risk,” but a penetration test that chains that library flaw to a privilege escalation that could access production data proves it’s critical. That evidence transforms your risk register from an artifact into an operational tool.
Driving the risk treatment plan
ISO 27001 requires organizations to choose one of four treatment options for each risk: mitigate, accept, avoid, or transfer. Pentest findings inform that decision with hard data. The risk treatment plan documents specific remediation actions, responsible parties, and deadlines for each finding. Auditors examine this plan in detail during certification and surveillance audits to ensure that your treatment decisions are evidence-based rather than hypothetical.
Validating the Statement of Applicability
The SoA is arguably the most important document in your ISMS. It lists all 93 Annex A controls, indicates which are implemented, which are excluded, and justifies every decision.
Pentest results feed it direct evidence that selected controls function as intended. They also expose gaps that testing reveals, such as weak network segmentation. For example, your SoA must reflect that A.8.22 (Segregation of Networks) needs improvement and not mark it as fully implemented.
This creates a continuous improvement loop that maps to ISO 27001’s Plan-Do-Check-Act cycle; pentest findings update the risk assessment (Check), drive control improvements (Act), which are documented in updated SoA and treatment plans (Plan), and then implemented and verified through retesting (Do).
Why Organizations Fail the Pentest Portion of ISO 27001 Audits?
Before diving into asset-specific checklists, understanding failure modes is essential. Auditors follow a predictable chain: show me your report → show me your remediation → show me your risk acceptance for anything left open. Organizations break this chain in six recurring ways:
Stale or missing reports top the list. Auditors stamp your tech stack as non-compliant if it hasn’t undergone a formal security test within 12 months or since any major architectural change. Well, the latter also depends on how their day went, but are you feeling that lucky? Also, reports that predate a cloud migration or major release are rendered irrelevant.
Second, remediation gaps. Auditors ask for the Jira ticket or change request that proves a critical vulnerability was patched within your stated SLA. Your failure to provide so renders the finding a nonconformity.
Third, scope misalignment between the pentest and the ISMS is surprisingly common, for example, testing only the web UI while many undocumented API endpoints remain untouched and undiscovered, or omitting cloud infrastructure listed in the Statement of Applicability.
Other, less obvious failures include:
- Absence of a risk-based testing that connects the pentest scope to the risk register
- Missing retest evidence that confirms whether high-severity findings were actually fixed
- Documentation decay, where organizations test rigorously for initial certification but let programs lapse before surveillance audits
Need more clarity? Check our detailed piece on becoming ISO 27001 compliant and talk to our experts right away!
Table 4: Your Crisp Cloud ISO 27001 Penetration Testing Checklist
| Test area | Annex A controls | Frequency | Dev-friendly approach | Auditor evidence |
|---|---|---|---|---|
| IAM and access control | A.8.5, A.8.3, A.5.23, A.8.9 | Quarterly automated + annual manual | CSPM tools (Prowler, ScoutSuite) in CI; IAM policy validation in IaC pipeline | IAM audit report; privilege escalation test results; access key rotation evidence |
| Network security | A.8.20, A.8.22, A.8.9, A.5.23 | Quarterly automated + annual manual | IaC scanning for network rules (Checkov, tfsec); automated NSG/SG drift detection | Network configuration findings; segmentation test results; firewall rule audit |
| Storage security | A.8.24, A.8.10, A.8.12, A.5.23 | Quarterly automated + annual manual | CSPM continuous monitoring; IaC policy enforcement for storage defaults | Storage access audit; public exposure scan results; encryption status report |
| Encryption | A.8.24, A.5.23, A.8.29 | Annual + after encryption policy changes | IaC enforcement of encryption defaults; automated TLS/cert scanning | Encryption status report across all services; key management audit |
| Logging and monitoring | A.8.16, A.5.25, A.5.23, A.8.9 | Quarterly + annual | CSPM continuous posture checks; IaC enforcement of logging requirements | Logging configuration audit; alert coverage map; detection validation results |
| Container security | A.8.8, A.8.28, A.8.9, A.5.23 | Per deployment + quarterly | Image scanning in CI (Trivy, Snyk Container); admission controllers for policy enforcement | Container scan reports; RBAC audit; runtime security findings |
| Serverless security | A.8.8, A.8.28, A.8.9, A.5.23 | Per deployment + annual manual | IaC role scoping; automated function permission audits; secrets management integration | Serverless permission audit; function exposure findings |
| IaC review | A.8.9, A.8.28, A.8.25 | Every commit (automated) + annual manual | IaC scanning tools (Checkov, tfsec, KICS) as CI gate; policy-as-code with OPA/Sentinel | IaC scan reports; drift detection results; policy enforcement evidence |
| Cloud configuration baseline | A.8.9, A.5.23, A.8.8 | Quarterly automated + annual manual | CSPM continuous benchmarking (Prowler for AWS CIS, Microsoft Defender for Azure CIS) | CIS Benchmark compliance report; remediation tracking log |
How does Astra Security help you pass your ISO 27001 audit?
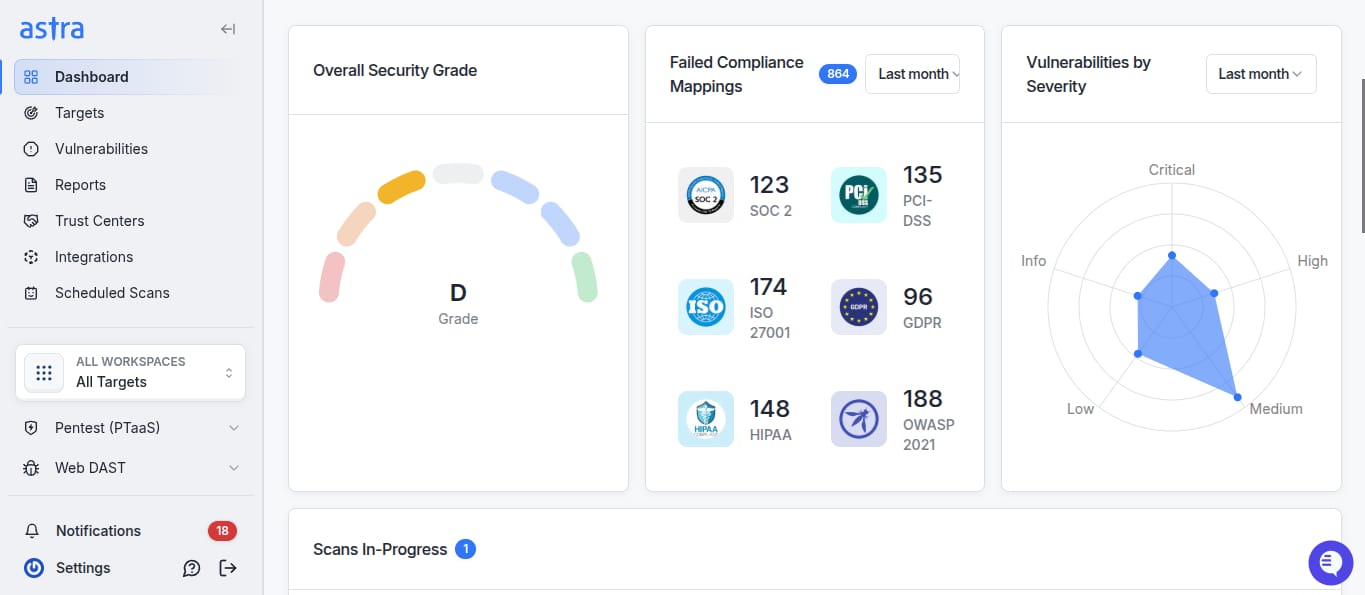
Most pentest vendors hand you a PDF, and when your auditor asks for remediation evidence, control mappings, or retest proof three months later, they cease to respond to your calls. Astra Security combines automated scanning with expert-led manual pentesting across your entire attack surface: web applications, APIs, cloud infrastructure, and networks.
With over 15,000 security tests and compliance checks that receive fortnightly updates, we catch both known CVEs and the business-logic flaws that scanners miss entirely, such as payment-escalation and workflow-bypass vulnerabilities.
Your pentest evidence stays current, not stale. Astra runs unlimited automated scans alongside manual assessments, which helps you maintain continuous visibility. So that when a surveillance auditor asks what has changed since your last certification cycle, you have real-time data rather than a 10-month-old report.
Remediation happens inside your existing workflow, not outside it. We offer direct integration with Slack, Jira, GitHub, GitLab, and Jenkins, and generate a ticket for each finding as a prioritized item, so your developers can fix vulnerabilities without compromising their normal sprint cycle or opening separate workstreams just for compliance. This enables shift-left security while you scale, the one that sticks and doesn’t stink
Two free rescans with a publicly verifiable certificate. Once your team remediates findings, Astra retests at no extra cost and issues a certificate that your auditor can independently verify.
Reports are built for two audiences at once. Astra generates custom reports for management and developers separately. Our CXO-friendly dashboard provides an audit-friendly executive summary, risk posture, and control-level mapping for compliance managers and CISOs like yourself. Secondly, our developer report provides all the technical details, reproduction steps, and how-to-fix guidance they need to best patch their systems and stay compliant. So, no longer formatting the 60-page PDFs to make them look consumable.
Testing conducted by certified professionals with real-world credentials. Astra’s security engineers hold OSCP, CEH, eJPT, eWPTXv2, and CCSP (AWS) certifications, which auditors expect to see in your pentest report. We’re also active contributors to OWASP and other open-source security projects, which helps us stay ahead of emerging attack techniques.
Full compliance coverage beyond ISO 27001. In addition to your ISO 27001 Annex A requirements, we also cover you for SOC 2, HIPAA, GDPR, etc. If you work across multiple certifications, we help you consolidate your testing efforts and eliminate duplication of effort and documentation.
Also, when it comes to network infrastructure, Astra Security:
- Maps your full topology
- Classifies assets by criticality, and tests against CIS Benchmarks, NIST, and MITRE ATT&CK frameworks.
- Assesses router configurations, firewall policies, remote access setups, authentication controls, etc., and generates infrastructure-layer evidence that satisfies controls A.8.20 and A.8.22.
- Makes sure every engagement ends with a prioritized, risk-based remediation roadmap and not just a no-good bulletin of findings
To sum up, we help turn ISO 27001 penetration testing from an annual compliance headache into a continuous program that keeps your ISMS audit-ready year-round… without slowing down your development team, of course!
Final Thoughts
Overall, you need to understand that auditors don’t just want to see that you ran a penetration test; for them, this is a means to an end, the end being the proof that you acted on the results.
Their expectation thus becomes fairly straightforward:
- A recent, properly scoped pentest report mapped to Annex A controls
- A remediation log showing that critical findings were closed as per documented SLAs
- Retest evidence that confirms whether your fixes actually work
- Formally accepting the risk for anything left open
You thus need to treat penetration testing as a continuous cycle of testing, remediation, retesting, and documentation. This keeps your ISMS resilient between certification cycles, smoothening your ISO 27001 compliance journey.
IS0 27001 Pentesting FAQs
What documentation do ISO 27001 auditors expect from a penetration test?
Auditors expect:
1. A signed pentest report (dated within 12 months) that includes scope, methodology, tester qualifications, and findings with severity ratings.
2. A remediation log that shows closure of high-risk findings along with retesting evidence that confirms that the fixes work
3. A documented testing plan with rules of engagement.
4. You to map all findings to specific Annex A controls
Can automated vulnerability scans replace penetration testing for ISO 27001?
No. Automated scans identify known vulnerabilities but cannot test business logic flaws, chain exploits, or simulate real attacker behavior. Moreover, ISO 27002:2022’s implementation guidance for A.8.8 calls for “penetration tests” alongside vulnerability scanning tools.
How do I map penetration test results to Annex A controls?
Create a mapping table linking each finding category to the relevant control.
– Unpatched software and known CVEs map to A.8.8.
– Web application flaws like SQL injection and XSS map to A.8.29 and A.8.8.
– Network misconfigurations map to A.8.20 and A.8.22.
– Cloud IAM issues map to A.5.23.
– Weak authentication maps to A.8.5 and A.5.15.
– Failed detection of simulated attacks maps to A.8.16 and A.5.25.
Your pentest provider should include this mapping in their report; if they don’t, you’d better be on the lookout!
How far in advance of an audit should I complete penetration testing?
Complete your penetration test 6–8 weeks before the scheduled audit date. This provides 2–4 weeks for remediation of critical and high-severity findings, plus 1–2 weeks for retesting and documentation.









