Key Takeaways
- Vendor chaos kills SOC 2. Fragmented pentest, audit, and scanner teams clash on timelines, scopes, and evidence, burning 20+ hours weekly on translations.
- Trust Service Criteria drive everything. Security, Availability, Processing Integrity, Confidentiality, and Privacy demand aligned controls proven by auditor tests.
- Pentesting powers compliance. It uncovers vulnerabilities in systems, APIs, and cloud, vital for Security criteria and clean audit opinions.
- With zero false positives, SOC 2-tuned scans, Jira/Slack integration, Astra Security smoothens SOC 2 pentesting, starting at $1999/year.
The threat landscape is moving faster than your audit cycle. Vulnerability exploitation as an initial access vector grew 34% year over year, now accounting for 20% of all confirmed breaches [Source: Verizon’s 2025 Data Breach Investigations Report]. Yet your security testing still happens once a year (if budget allows).
You have hired a pentest firm, a compliance auditor, a CPA firm, and a vendor to help with continuous scanning, only to find out in 3 days that none of them share a common language or evidential taxonomy, while continually stumbling over each other’s timelines, scopes, and requirements.
So now you’re stuck burning 20+ hours every week just translating SOC 2 speak into Jira tickets, mapping them to the Trust Service Criteria requirements, and back again, all while trying to make sure you don’t under- or over-optimize the scope, i.e., blow off the budget on the wrong target.
Vendor fragmentation, broken communication, cost and quality pressures, and timeline constraints have just turned your SOC 2 report and certificate (a badge to strengthen consumer trust) into a big headache you are no longer sure about. So how do you fix or altogether avoid this?
Well, the first step is to go back to basics. In this article, we take a deep dive into the world of SOC 2 and cover definitions, importance, benefits, processes, and components, but most importantly, how you can avoid the above trap.
What is SOC 2?
SOC 2, or Service Organization Control 2, is an internationally acknowledged framework that provides comprehensive guidelines for protecting customer data based on the five “trust service principles.” It’s based on five key “trust service principles,” namely Security, Availability, Processing Integrity, Confidentiality, and Privacy, ones that can be adapted to your unique business needs.
Moreover, according to a recent report, 94% of SOC 2 Type II auditors demand pentest evidence, expecting at least 1 full test annually; missing it triggers CC7.1 (vulnerability management) exceptions.
What’s the Difference: SOC 2 Type I vs Type II?
| Aspect | SOC 2 Type I | SOC 2 Type II |
|---|---|---|
| Assessment Scope | Design suitability at a point in time | Operational effectiveness over 6+ months |
| Timeline | Point-in-time snapshot | Continuous monitoring period |
| Pentest Requirement | Often optional | 94% of auditors mandate it |
| Customer Acceptance | Limited; initial onboarding | Industry standard; required for RFPs |
| Cost | $15,000 - $50,000 | $25,000 - $100,000+ |
| Validity | 6-12 months | 12 months from issuance |
What is a SOC 2 Report?
A SOC Type 2 report is produced by an external auditor that proves your company’s adherence to the SOC 2 cybersecurity framework of data security, availability, processing integrity, confidentiality, and privacy standards set by the American Institute of Certified Public Accountants (AICPA).
The report covers data protection and privacy, which is crucial for clients and stakeholders. It ensures the company follows stringent standards to safeguard sensitive information and maintain a secure IT environment.
Who Needs a SOC 2 Report?
Service organizations that handle customer or third-party information, such as SaaS providers, cloud platforms, IT service firms, and payment processors, typically need a SOC 2 report.
“People wouldn’t even talk to us without SOC 2. It’s very difficult to sell without compliance. Our first customer was hesitant. They questioned our resources and data security. SOC 2 compliance turned the deal around.”
Lalit Indoria, Co-Founder and CTO, ClearFeed
1. Service Organizations: Business service providers that access, process, or store sensitive data use SOC 2 reports to ensure client data safety. Examples include cloud providers like Azure and AWS, payment processors, and data hosting companies that access client files.
2. Companies Dealing in Sensitive Data: Companies handling sensitive information, such as personal, financial, and health records, need a SOC 2 audit. Examples include banks, healthcare providers, and e-commerce businesses.
3. Businesses Partnering With Other Enterprises: Businesses engaging in partnerships with other enterprises must present them with a report before beginning negotiations as proof of having adequate controls to secure sensitive data.
4. Companies Required by Regulations: Organizations operating within specific regulated fields may be required by law or industry standards to secure a SOC 2 compliance report. For example, healthcare organizations in the US must abide by HIPAA, which mandates specific controls for protecting health information.
5. Technology Companies: Tech companies, such as software developers, IT service providers, and online platforms, often require a SOC 2 audit report because they manage substantial volumes of client data that must be handled securely.
What are the Components of a SOC 2 Report?
The components of a SOC 2 report include the Five Trust Service Criteria, documentation, auditor testing, and a compliance opinion, as detailed under.
Control failures are costing organizations their audits. A 2024 analysis of SOC 2 Type II audit failures showed that 67% of organizations without regular vulnerability scanning received management letter comments for inadequate security monitoring.
1. Five Trust Service Criteria
The SOC 2 compliance report is organized around five Trust Service Criteria (TSCs), which form the core principles for safeguarding its systems and the information processed: Security, Availability, Processing Integrity, Confidentiality, and Privacy.
- Security involves protecting system resources against unwarranted access.
- Availability refers to the access to products or services as per the contract/service level agreement.
- Processing integrity is defined as completeness, validity, and accuracy in system processing.
- Confidentiality protects information designated as confidential.
- Finally, privacy refers to safeguarding personal information collected, retained, disclosed by an entity, and eventually discarded.
2. Document Requirements for SOC 2 Audit Prep
Prepping for a SOC 2 audit entails gathering and organizing numerous documents, such as policies and procedures, and supporting evidence, such as system configuration files, access logs, or incident response plans, to demonstrate control implementation.
Document requirements depend upon your operations and the trust services criteria being assessed. For instance, documents related to data encryption, firewalls, and access controls are necessary for accessing security criteria, while backup plans and system monitoring are mandatory for availability criteria.
3. Auditors’ Opinion
This section of a SOC 2 report serves as the independent auditor’s statement regarding the fairness of the system’s presentation, the suitability of the controls’ design, and the operating effectiveness of the system, if applicable (Tier-II reports only).
An auditor may express one or more opinions during an audit: an Unqualified Opinion (clean opinion), a Qualified Opinion, an Adverse Opinion, or a Disclaimer of Opinion. An Unqualified Opinion indicates that controls were designed, implemented, and are operating effectively, while any other opinion indicates issues identified during the audit warrant inclusion in the report.
3. Description of Tests of Controls and Results
This section includes an in-depth explanation of all of the tests carried out by an auditor to test and measure the design and operating effectiveness of controls in place, along with the results of these assessments, especially a SOC 2 Type II report.
Each control tested will be described and its criteria evaluated; procedures performed by the auditor to test it; results from tests; and any recommended corrections that might need to be implemented to maintain the effective operation of those controls in place.
Stay SOC 2 compliant 24/7 with Astra.
What is the Process of Obtaining a SOC 2 Report?
The process spans pre-assessment to identify control gaps, formal audit testing by independent auditors, post-audit remediation of findings, and ongoing annual maintenance to sustain compliance.
1. Pre-Assessment Phase
Before initiating their SOC 2 audits, organizations often undergo a pre-assessment phase—either internally or by third-party consultants—designed to detect any weaknesses in their controls that must be addressed before the official audits.
This requires reviewing policies, procedures, and controls against SOC 2 Trust Service Criteria to pinpoint areas where the organization does not satisfy a threshold.
2. Assessment Phase
This phase involves conducting an actual audit by an independent third-party auditor who will assess your organization and controls against SOC 2 Trust Service Criteria, such as reviewing policies and procedures while interviewing relevant personnel to asses whether these controls meet SOC 2 certification requirements.
An auditor will then prepare a draft report for SOC 2, which includes an in-depth description of your organization’s system, expert opinions from the audit team, and results of control tests. Before the final report is released to the organization for final review by the auditor, any further clarification or additional information must be submitted before it is signed off as the final document.
3. Post-Assessment Phase
Following the assessment phase, organizations receive their final audit report from an auditor, including the auditor’s opinion and the control testing results.
Post-assessment phase activities focus on responding to any recommendations or areas for improvement identified by an auditor, even when an organization receives an unqualified opinion.
4. Maintenance Phase
Generating a SOC 2 report is not a one-off event for organizations. To meet the SOC 2 Trust Service Criteria, organizations need to evaluate and update their controls regularly. This may involve reviewing policies and procedures regularly, performing internal audits, and responding to new risks or threats.
Organizations should also consider periodically obtaining a compliance pentest report—at least once annually—to assure stakeholders of the effectiveness of their controls and demonstrate their commitment to maintaining an efficient control environment.
What are the Benefits of SOC 2 Reports?
The above report can help you boost customer trust, avoid non-compliance fines, and improve leads and conversions while mitigating genuine cybersecurity risks.

1. Enhanced Data Security
A SOC 2 audit is a rigorous process of testing your systems and controls where you find any vulnerabilities that pose a threat and mitigate them immediately to achieve compliance. This significantly improves the strength of your data security and prevents data breaches.
2. Increased Customer Trust
Displaying a pentest report and certificate increases consumers’ trust that you prioritize data protection. Considering the testing process is done by a renowned independent third-party regulatory body, it acts as a solid differentiating factor in a customer’s decision.
“SOC 2 answers a lot of questions about security team size, data handling, and processes. It builds trust.”
Lalit Indoria, Co-Founder and CTO, ClearFeed
3. Compliance with Industry Standards
In most cases, organizations are not legally required to get a SOC 2 report, but obtaining SOC 2 compliance often meets or exceeds HIPAA, GDPR, and ISO 27001 requirements. It helps organizations manage compliance requirements by decreasing standard compliance times and reducing associated expenses.
4. Attracts Clients
By conducting a SOC 2 audit, your security commitment increases your appeal to business partners and clients, prioritizing data protection and enterprise-level demanding clients. In many RFPs and due diligence processes, a SOC 2 report is becoming a de facto requirement. Hence, SOC 2 allows businesses to access new opportunities while gaining a market advantage.
5. Risk Mitigation
Through SOC 2 audit processes, organizations can detect and solve security threats before they are exploited. Proactively removing these vulnerabilities can reduce your risk profile and prevent reputational damage, financial losses, and operational halts.
How is SOC 2 Linked to Penetration Testing?
SOC 2 and penetration testing are complementary processes essential to an organization’s cybersecurity. While SOC 2 primarily examines an organization’s controls against the Trust Service Criteria, penetration testing simulates cyberattacks against systems to discover vulnerabilities that attackers might exploit.
The remediation window is narrowing. According to Verizon’s 2025 DBIR, only 54% of vulnerabilities are fully remediated during the year, with a median remediation time of 32 days.
Penetration testing could be used to find and resolve vulnerabilities during a SOC 2 audit. While SOC 2 certification reassures organizations that they have implemented suitable controls for managing customer data, penetration testing further assures that these safeguards effectively block unauthorized entry to systems owned by their organization.
Did you know? Per a recent study, 73% of breaches hit web apps (pentest sweet spot), yet control failures like unclear ownership and manual processes tank 40%+ of audits.
It is one small security loophole v/s your entire website or web application.
Get your web app audited with
Astra’s Continuous Pentest Solution.

What is the Role of Penetration Testing in SOC 2 Compliance?
Penetration testing identifies vulnerabilities and is one of the best ways to measure the effectiveness of security controls in protecting system resources against unwanted access. It is essential for achieving SOC 2 compliance.
It can also be vital in other Trust Service Criteria, such as Availability and Processing Integrity. For example, a pentest can identify vulnerabilities allowing an attacker to conduct denial-of-service attacks against a system, impacting availability.
How can Astra Security help with SOC 2 Compliance?
Astra Security offers a comprehensive SOC 2 pentest designed to help you comply with the industry standards. We combine automated vulnerability scanning with pentesting to identify over 15,000 vulnerabilities across web apps, mobile apps, cloud infrastructures, APIs, and networks.
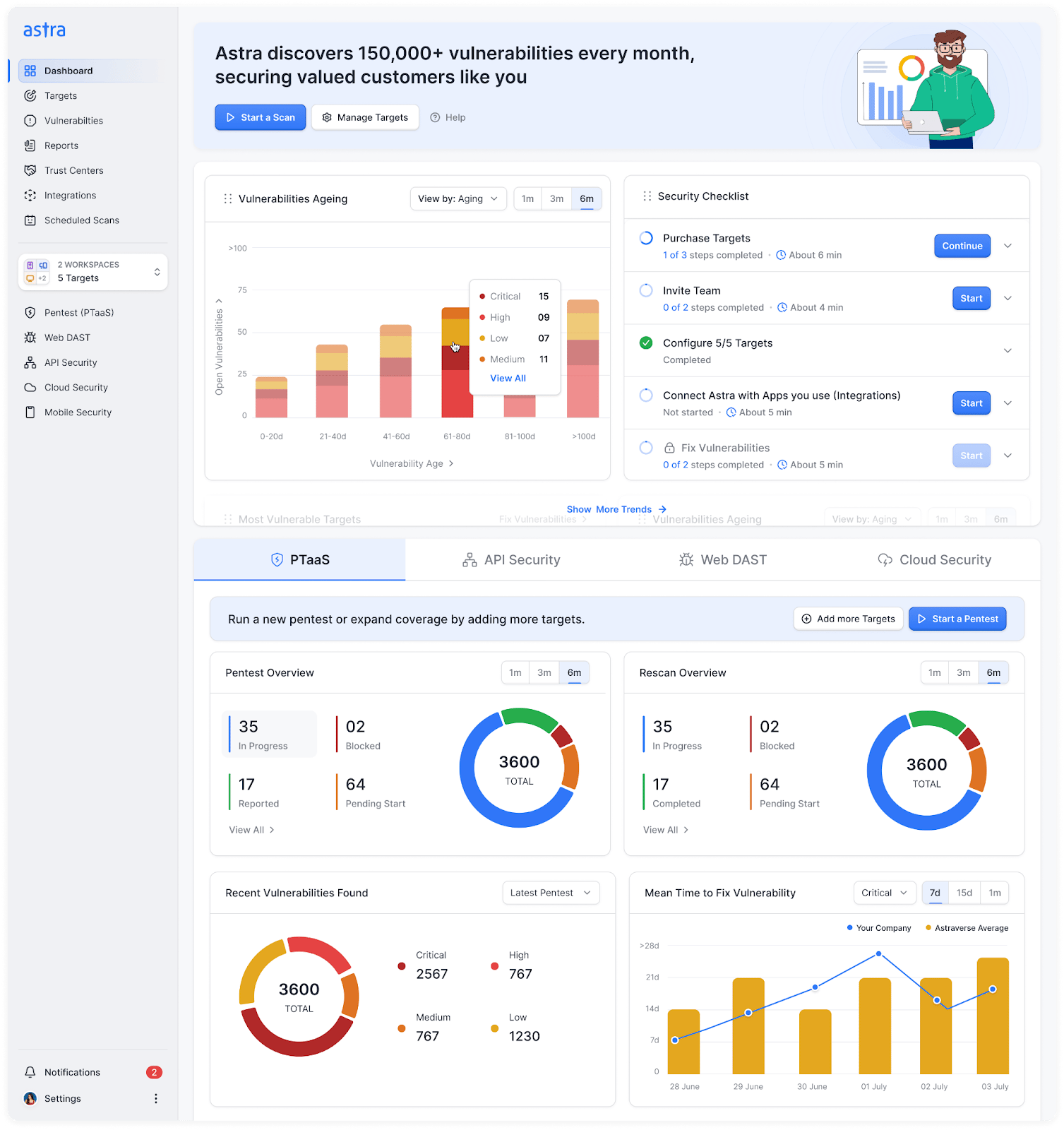
Key Features
- Platform: SaaS
- Pentest Capabilities: Continuous automated scans with 10,000+ tests and manual pentests
- Accuracy: Zero false positives (with vetted scans)
- Compliance Scanning: OWASP, PCI-DSS, HIPAA, ISO27001, and SOC2
- Publicly Verifiable Pentest Certification: Yes
- Workflow Integration: Slack, JIRA, GitHub, GitLab, Jenkins, and more
- Price: Starting at $1999/yr
This ensures that all your systems are aligned with SOC 2 controls for secure configuration, enabling you to address CVEs relevant to the SOC 2 framework. We also find business logic vulnerabilities critical for compliance with SOC 2’s Security, Availability, Processing Integrity, and Confidentiality (SAAIC) principles.
Experience how Astra’s SOC 2 pentesting continuously validates your security controls and generates audit-ready evidence.

Final Thoughts
Data breaches and cyberattacks have become frequent, making it imperative that organizations demonstrate their dedication to cybersecurity. A SOC 2 audit assures stakeholders that an organization has implemented appropriate controls for managing customer data.
At the same time, penetration testing ensures that these controls effectively prevent unauthorized access—both essential components of a holistic cybersecurity approach.
Simply stated, any organization handling sensitive data that wishes to demonstrate a commitment to data security should consider obtaining a SOC 2 report and regularly conducting penetration testing. This will safeguard their information and build trust among their stakeholders.
FAQs
What are SOC 1 and SOC 2 reports?
SOC 1 and SOC 2 reports assess an organization’s controls over financial reporting and data security, respectively. SOC 1 focuses on internal controls relevant to financial statements, often for outsourced services. SOC 2 evaluates technology services’ security, availability, processing integrity, confidentiality, and privacy controls.
How long is a SOC 2 report valid for?
While a SOC 2 report technically doesn’t expire, its validity is recognized for 12 months from the issuance date. Beyond this, the report is deemed “stale” and may not be accepted by potential customers, highlighting the importance of regular assessments to maintain currency and trust in cybersecurity practices.
What are the types of SOC 2 reports?
SOC 2 reports come in two types: Type I assesses design suitability at a specific point, while Type II evaluates operational effectiveness over time. Both assure a company’s control environment, with Type II offering insights into long-term adherence.
What is the purpose of SOC 2 reports?
SOC 2 reports help assess and communicate the effectiveness of a service organization’s information security controls. It is vital to demonstrating their commitment to safeguarding sensitive data and building trust with clients.
Explore Our SOC 2 Series
This post is part of a series on SOC 2. You can
also check out other articles below.