SOC 2 compliance software secures your data like safe, secure valuables, but it’s more than just a security tool – it’s your passport to building lasting trust in today’s digital world.
When customers choose your service, they’re not just buying a product but entrusting you with their data. As cyber threats become more complex and data breaches make headlines, SOC 2 compliance has become necessary and a competitive advantage. It shows your commitment to protecting what matters most to your clients.
Compliance automation tools simplify SOC 2, improving the efficiency and cost-effectiveness of the whole testing process, all while upholding stringent privacy considerations and security measures.
9 Best SOC 2 Compliance Software in 2026
- Astra Pentest
- Sprinto
- Vanta
- Drata
- Secureframe
- AuditBoard
- LogicGate
- Qualys
- OneTrust
Comparison of The Best Automated SOC 2 Compliance Software
| Name of SOC 2 software provider | Key standout feature (G2) | DemoAvailability | Customer Rating (G2 –(out of 5 | G2 Recognition |
| Astra Security | Vulnerability Assessment and Malware Detection | 7-day free trial and scheduled demo | 4.9 | APAC Leader Fall 2025 |
| Sprinto | Compliance Auditing | Scheduled demo | 4.8 | Top 50 GRC Products 2025 |
| Vanta | Compliance Monitoring | Scheduled demo | 4.6 | G2 Top 50 GRC Products 2025 |
| Drata | Compliance Monitoring | Scheduled demo | 4.8 | G2 Leader Winter 2025 |
| Secureframe | Risk management policies | Scheduled demo | 4.7 | G2 Leader Summer 2025 |
| AuditBoard | Internal Controls Management | Scheduled demo | 4.7 | G2 Top 50 GRC Products 2025 |
| LogicGate | Audit Management | Scheduled demo | 4.6 | G2 Grid Leader Summer 2025 |
| Qualys | Vunerability Assessment | Scheduled demo | 4.4 | G2 Leader Fall 2023 |
| OneTrust | Privacy and Risk Management | Scheduled demo | 4.3 | G2 Leader Summer 2025 |
1. Astra Pentest (Book a Demo)
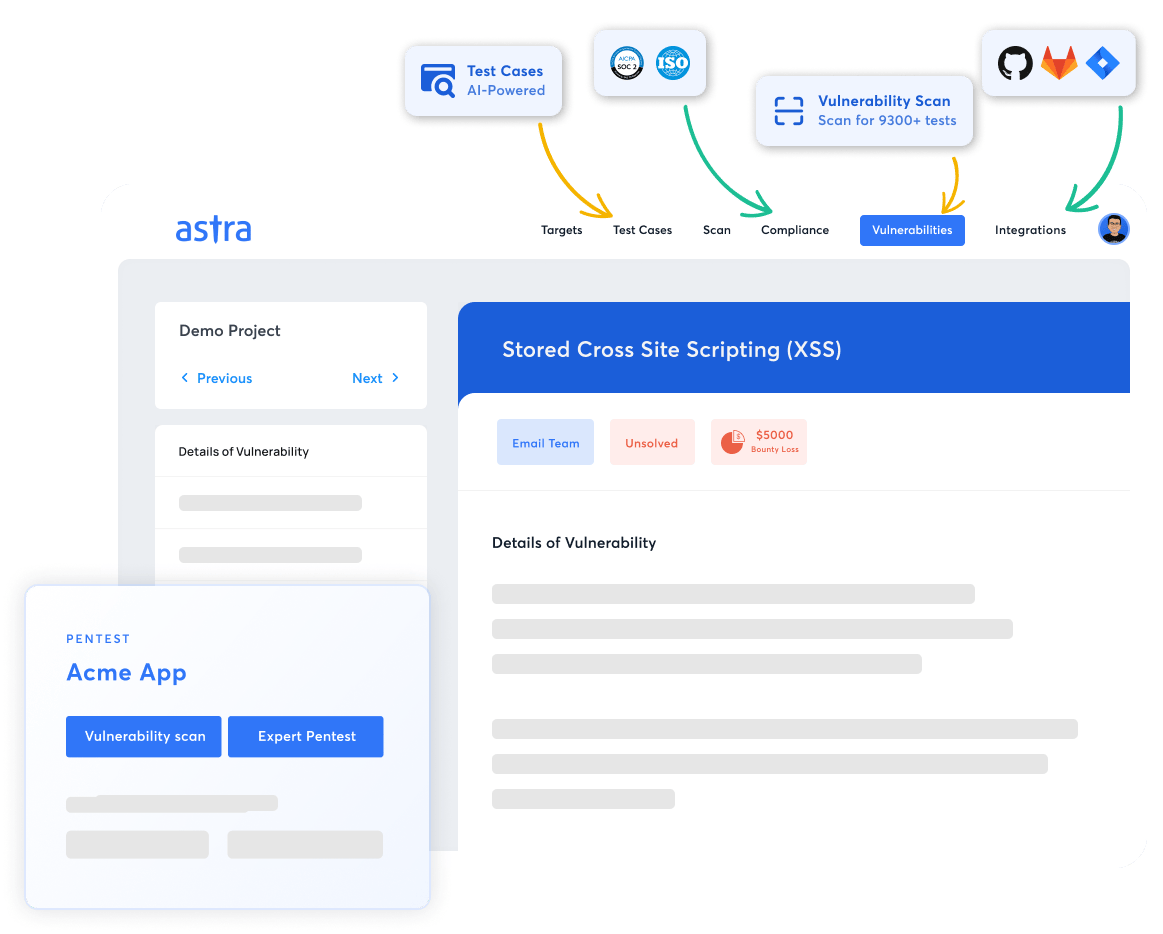
Key Features:
- Platform: SaaS
- Pentest Capabilities: Continuous automated scans with 10,000+ tests and manual pentests
- Accuracy: Zero false positives (with vetted scans)
- Compliance Scanning: OWASP, PCI-DSS, HIPAA, ISO27001, and SOC2
- Publicly Verifiable Pentest Certification: Yes
- Workflow Integration: Slack, JIRA, GitHub, GitLab, Jenkins, and more
- Price: Starting at $1999/yr
Astra Security combines automated and manual pentesting expertise to deliver comprehensive SOC 2 compliance pentesting solutions with advanced CI/CD integration and AI support that evolves with each pentest.
While an annual pentest is a solid security practice and firm SOC 2 requirement, in cyber security, SOC 2 penetration testing is a vital process that evaluates an application’s security by exploiting its hacker style to expose and assess security risks based on emerging threats and best practices.
Built by experts who secured Microsoft, Adobe, Facebook, and Buffer, Astra Security’s intelligent automated vulnerability scanner, coupled with in-depth manual pentesting, spots 15,000+ vulnerabilities per month and saves hundreds of hours for developers & CXOs.
Pros
- User-friendly interface
- Rescanning for vulnerabilities
- Detailed compliance scans and reports
- 24/7 AI-enabled and human customer support
- Zero false positives
Cons
- 1-week trial available at $7
Astra Security, along with our manager Aparna, has proven to be an excellent choice for us. We’ve gone through the first extended screening and vetted scanning in 6 months. Astra provided exceptional service, addressing and meeting all our needs, which significantly enhanced the security of our product and helped us obtain a certification proving our compliance with security standards.
Elen K., Product Delivery Manager (Source G2)
Demo Availability: Try a 7-day free trial or schedule a demo with Astra’s expert team by visiting the website.
2. Sprinto
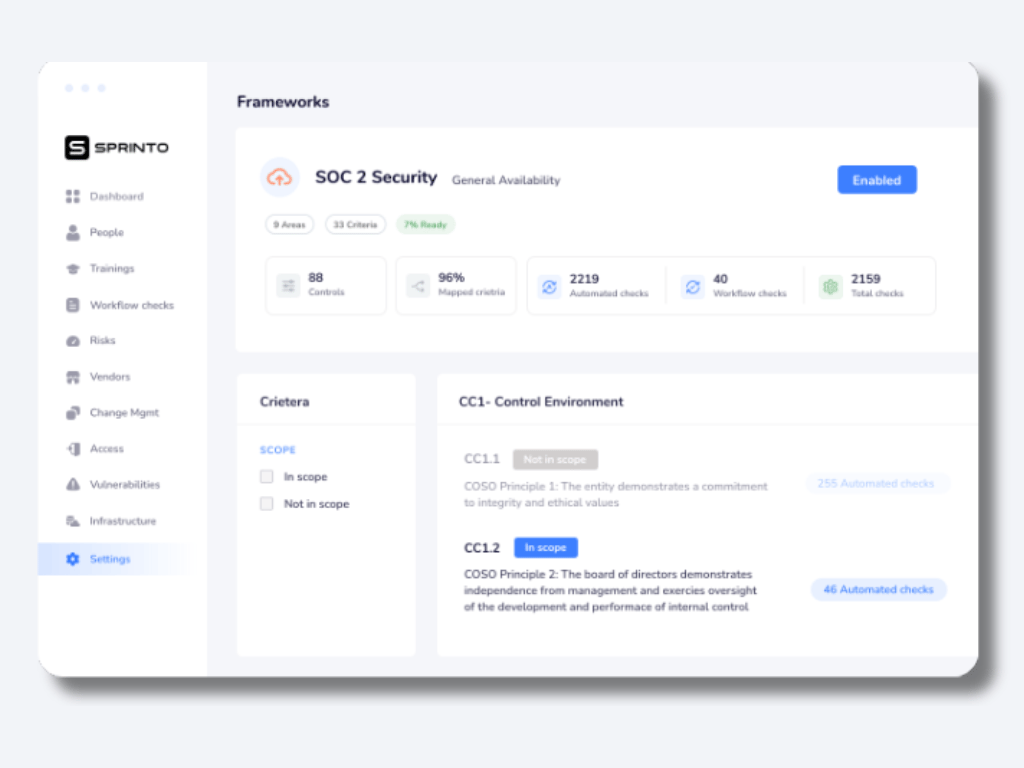
Key Features:
- Platform: Online
- Capabilities: Automated compliance solution that implements SOC with continuous monitoring features
- Remediation Support: Yes
- Compliance: ISO 27001, SOC 2, HIPAA, and GDPR
- Integrations: Slack, GitHub, GitLab, Google, AWS, and more
- Continuous Monitoring: Yes
- Best for: Auditor’s Dashboard, editable security policy templates, and automated evidence collection
- Price: Available on quote
Sprinto helps you map risks to controls and run fully automated checks to ensure continuous compliance and breeze through your audit. With Sprinto’s SOC 2 compliance software, you can ditch tedious spreadsheets for adaptive automation.
Sprinto has evolved beyond basic compliance automation, introducing an intelligent control framework that adapts to your business needs. Their platform now features continuous evidence collection and a sophisticated vendor assessment system that integrates seamlessly with major cloud providers.
Pros
- Fast set-up and deployment
- Centralized visibility and progress tracking
- No loss of engineering bandwidth
- Tailored for unique business cases
Cons
- The system might consume resources extensively for intensive tasks
- Any service data transmitted through trial services will be lost unless you purchase a subscription to the same service
“We use Sprinto. It’s cost-effective and handles all our logs in one place. It simplifies the entire process.”
Lalit Indoria, Co-Founder and CTO, ClearFeed
Demo Availability: You can book a personal demo by visiting their website.
3. Vanta
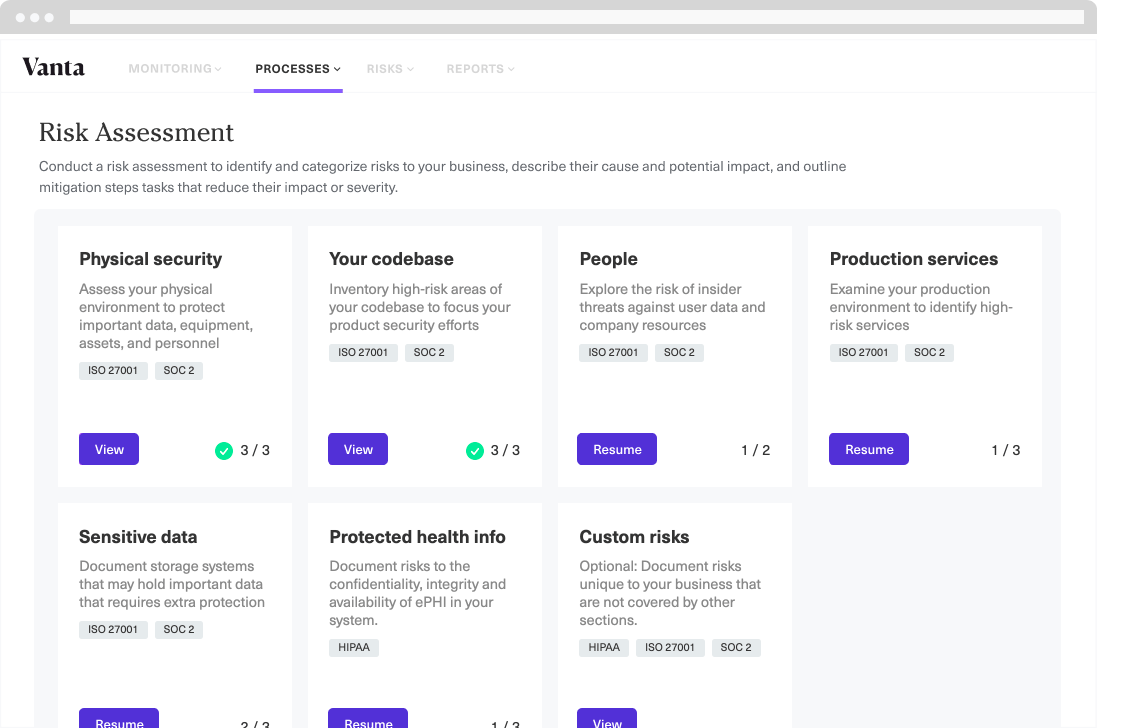
Key Features:
- Platform: Online
- Capabilities: Offers a holistic suite for SOC 2 compliance automation and management.
- Remediation Support: Yes
- Compliance: ISO 27001, SOC2, HIPAA, and GDPR
- Best for: Centralized dashboard, automated RFP management, employee information management, and mapped security controls.
- Continuous Monitoring: Yes
- Integrations: Slack, GitHub, GitLab, Google, AWS, and more
Vanta’s SOC 2 compliance software helps businesses get and stay compliant by continuously monitoring people, systems, and tools to improve security posture. It supports you across the entire compliance journey by pairing the automated platform with the most seamless audit experience.
Vanta’s approach to SOC 2 compliance now incorporates machine learning for enhanced threat detection. Their platform has expanded its integration ecosystem while simplifying the compliance journey through simplified workflows and customizable control frameworks.
Pros
- Intuitive user interface
- Responsive customer support
- API-driven capabilities
Cons
- Lack of customization options
- Better tutorials needed
4. Drata
Key Features:
- Platform: Online
- Capabilities: Automated evidence collection and continuous monitoring for SOC 2.
- Remediation Support: Yes
- Compliance: ISO 27001, SOC2, HIPAA, and GDPR
- Best for: Automated asset creation, customizable security controls, data integration with MDM for endpoint evaluation
- Continuous Monitoring: Yes
- Integrations: GitHub, GitLab, Google, AWS, and more
Drata offers you fast and frictionless SOC 2 compliance software. Built for powerful automation and designed by auditors and security experts for ease of use, Drata accelerates your compliance process.
Drata’s platform now combines AI-driven automation with expert guidance, making SOC 2 compliance accessible for organizations of all sizes. Its enhanced real-time monitoring system provides continuous visibility into compliance status, while its new risk intelligence feature helps prioritize security efforts based on your specific business context.
Pros
- Automation & integration
- User-friendly interface
- Get audit-ready faster
- Compliance expert help
Cons
- UX and power user-focused aspects
- Add-ons with additional costs
5. Secureframe
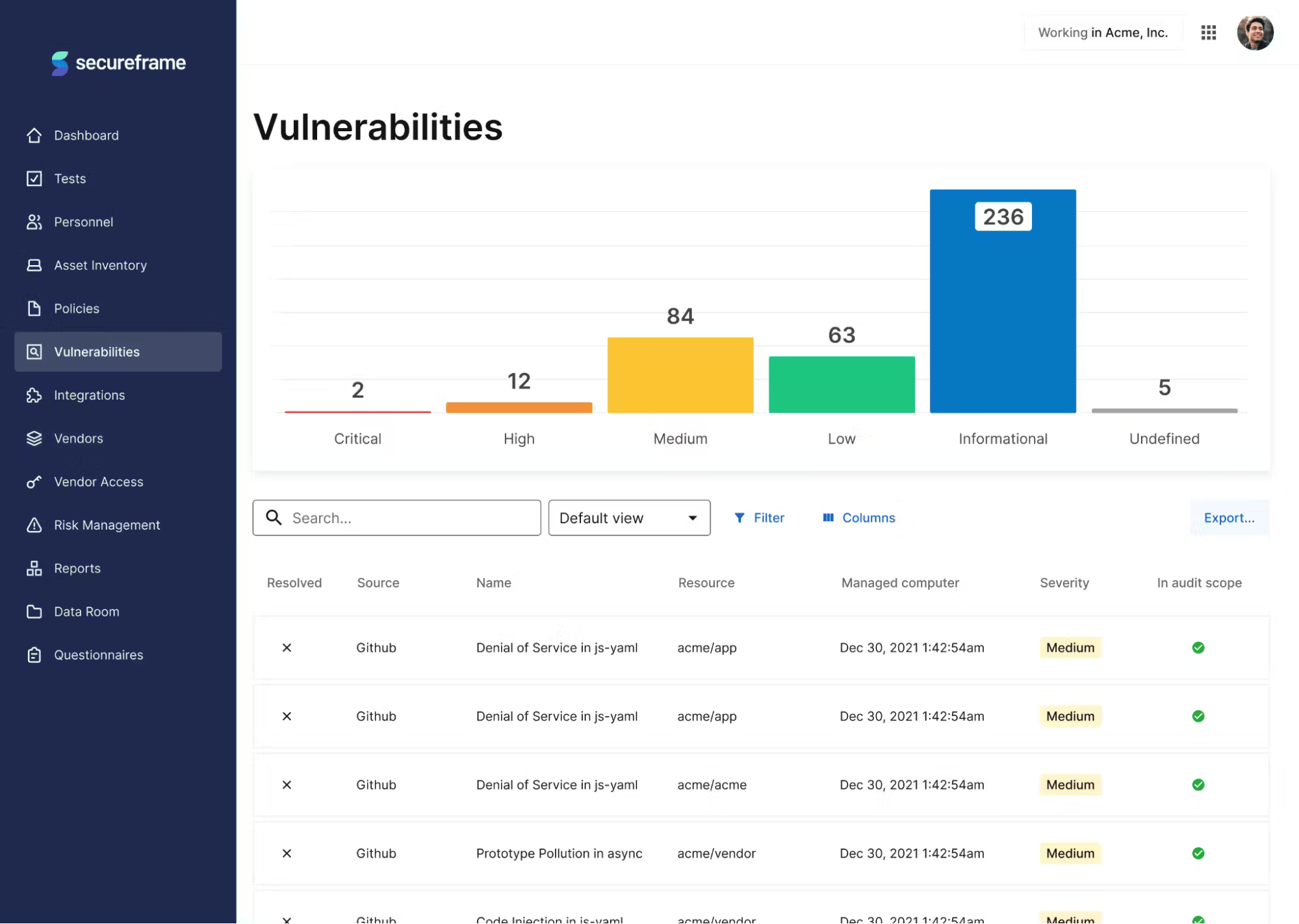
Key Features:
- Platform: Online
- Capabilities: Streamlined SOC 2 audit preparation with comprehensive support.
- Remediation Support: Yes
- Compliance: ISO 27001, SOC2, HIPAA, and GDPR
- Best for: Automated evidence collection, seamless vendor management, dedicated CSM
- Continuous Monitoring: Yes
- Integrations: Slack, GitHub, GitLab, Google, AWS, and more
Secureframe helps you quickly achieve and maintain compliance with key frameworks. Architected by compliance experts and former auditors, it offers an information hub for the fundamentals of SOC compliance software, curated best practices, and resources for security beginners, all in one place.
Secureframe has strengthened its position by introducing an integrated GRC platform that unifies compliance, risk management, and security operations. Their enhanced policy automation engine and vendor risk assessment provide a more comprehensive approach while reducing manual overhead.
Pros
- Customizable policies and automated tests
- Efficient vendor relationship lifecycle management
- SOC 2 Resources and Tools
Cons
- Integrations are clunky and can be hard to find
- No auto-reminder feature for integrated services
6. AuditBoard
Key Features:
- Pricing: Available on quote
- Platform: Cloud-based audit, risk, and compliance management
- Capabilities: Audit management, compliance monitoring, GRC
- Remediation Support: Yes
- Known For: Risk and compliance solutions for SOC 2
- Continuous Monitoring: Yes
- Compliance Scanning: SOC 2, ISO 27001, GDPR, HIPAA, PCI DSS
- Integrations: ERP systems, GRC tools, Jira, AWS, Azure
AuditBoard is a cloud-based audit, risk, and compliance management platform that helps organizations of all sizes streamline their compliance processes for SOC 2 audits.
With enhanced workflow automation and real-time monitoring capabilities, their updated internal controls management system includes AI-assisted risk assessment and automated data collection, making it easier for you to maintain continuous compliance while reducing manual workload.
Pros
- Comprehensive suite of features for audit
- User-friendly interface
Cons
- Large data sets can lead to performance difficulties
- Integration with other tools can be difficult
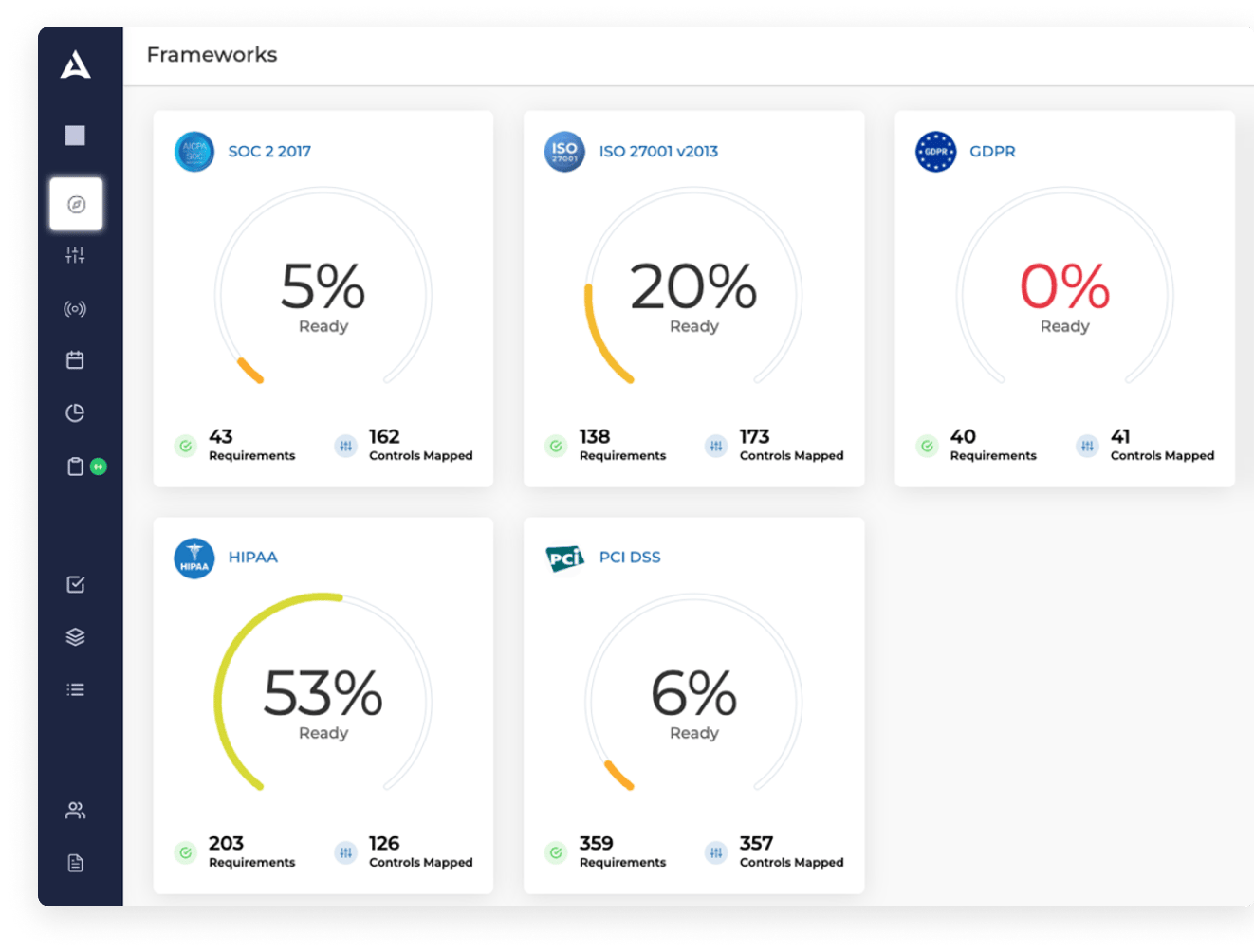
7. LogicGate
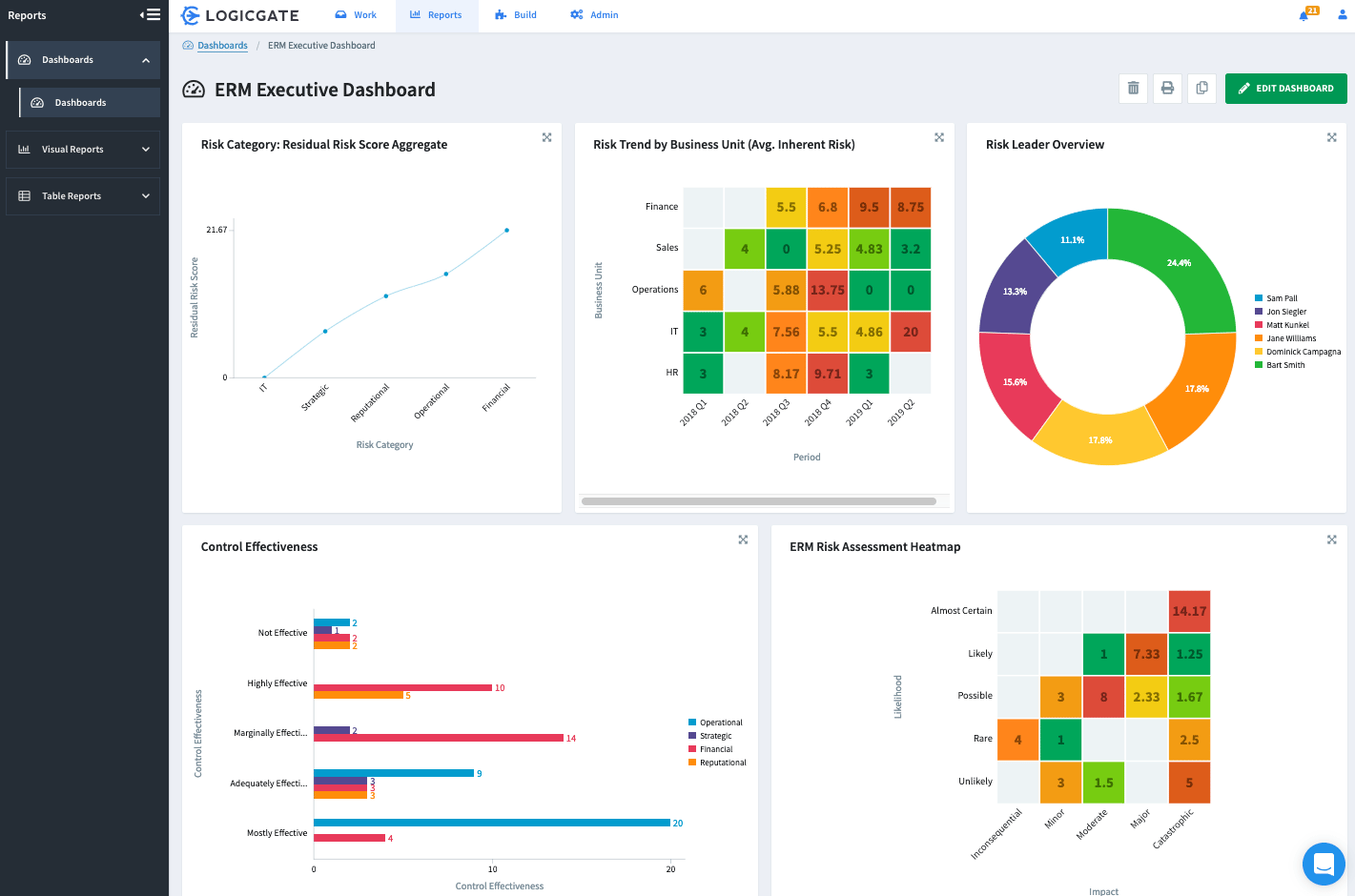
Key Features:
- Platform: Online
- Capabilities: Cloud-based risk management platform focusing on regulatory compliance, including SOC 2.
- Remediation Support: Yes
- Compliance: ISO 27001, SOC2, HIPAA, and GDPR
- Best for: Inventory of regulatory controls, risk assessment, and corrective action plans.
- Continuous Monitoring: Yes
- Integrations: Slack, Jira, GitHub, GitLab, Google, AWS, and more
LogicGate is a popular risk and compliance management platform that helps you identify, assess, and mitigate risks and manage compliance with SOC 2 requirements and other standards.
LogicGate has revamped its risk and compliance platform, emphasizing operational resilience. Their enhanced vendor risk management module now includes continuous monitoring capabilities, as well.
Pros
- Comprehensive coverage of SOC 2 requirements
- Strong focus on vendor risk management
Cons
- Limited customization options
- The interface can be more user-friendly
Stay SOC 2 compliant 24/7 with Astra.
8. Qualys
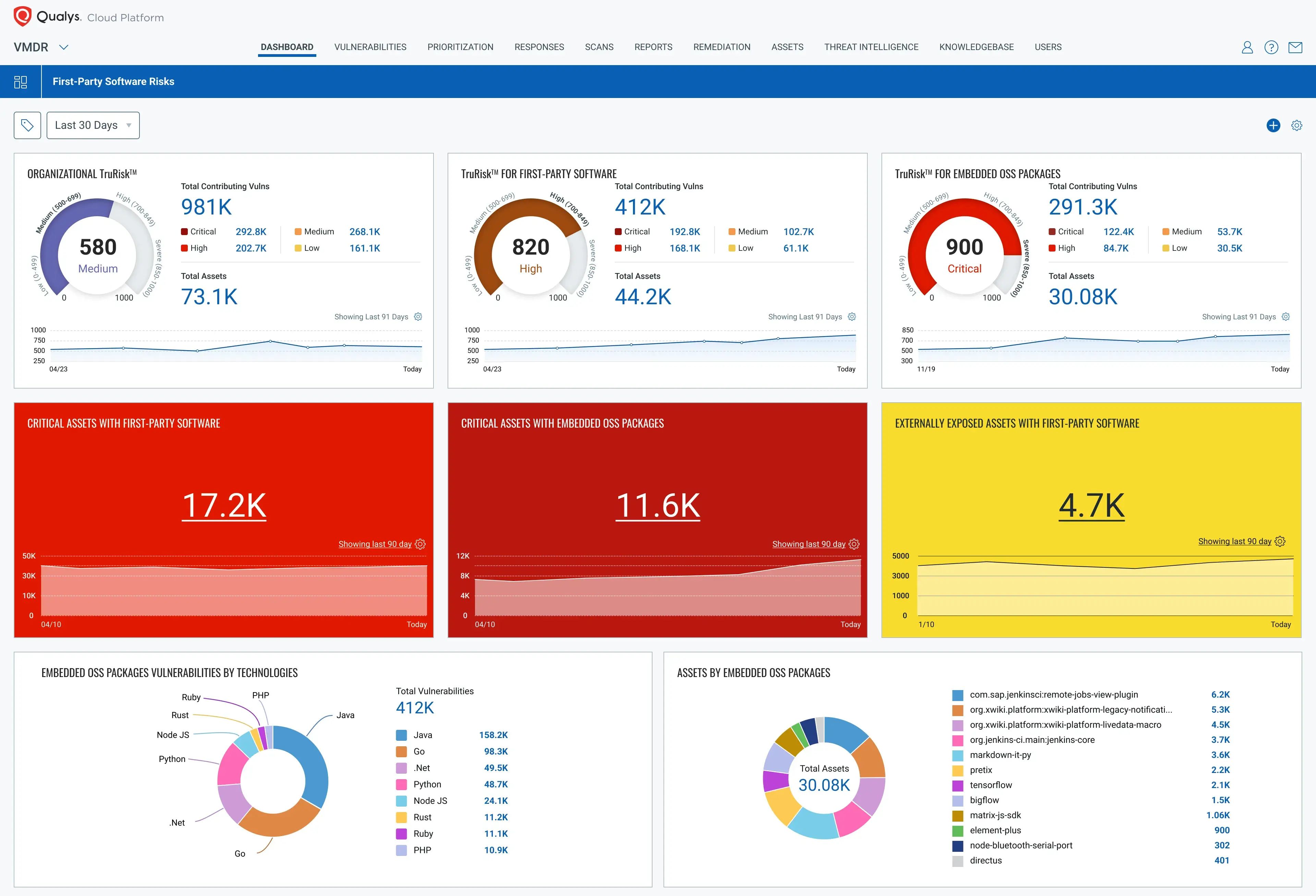
Key Features:
- Platform: Cloud-based security and compliance platform
- Capabilities: Vulnerability management, detection, and response
- Remediation Support: Yes
- Best for: Cloud security, vulnerability management
- Continuous Monitoring: Yes
- Compliance Scanning: PCI DSS 4.0, GDPR, HIPAA, and more
- Integrations: AWS, Microsoft Azure, Jira, Jenkins, GitHub
- Pricing: Available on quote
Qualys is a comprehensive security platform that helps you identify and remediate vulnerabilities, track assets, and report on compliance, including SOC 2 compliance.
With comprehensive vulnerability management and compliance monitoring, its enhanced asset discovery system now uses machine learning to provide more accurate inventory tracking, and its compliance reporting has been streamlined to support multiple frameworks simultaneously.
Pros
- Competitive pricing
- Strong customer support
Cons
- Limited customization options
9. OneTrust
Key Features:
- Platform: Cloud-based integrated risk management platform
- Capabilities: Risk management, data privacy management, compliance management
- Remediation Support: Yes
- Best for: Integrated Risk Management (IRM) and Data Privacy Management
- Continuous Monitoring: Yes
- Compliance Scanning: GDPR, CCPA, ISO 27001, SOC 2, HIPAA, PCI DSS
- Integrations: Okta, Amazon S3, Jira, etc.
- Pricing: Available on quote
OneTrust is an integrated risk management platform that helps you manage all types of risks, including third-party risk management, compliance reporting and audit support, and incident management and response.
It also offers compliance training and certification, incident management, and reporting for SOC 2 Compliance. Their enhanced privacy and security controls along with the updated data mapping capabilities, now provide better visibility into data flows and potential risks.
Pros
- Strong focus on data protection
- Scalable to meet the needs of businesses of all sizes
Cons
- Can be expensive for SMEs,
- Some users have reported difficulty navigating the platform
Final Thoughts
Many fast-growing companies are turning to SOC 2 compliance software to help them get (and stay) compliant with automated platforms. Automation will help you eliminate the headaches of manual monitoring, such as evidence collection and compliance audits, saving your team significant time and money.
Prioritizing compliance results in a decisive competitive advantage, positioning your company to earn customer trust and avoiding customer data breaches. The best tools are built by companies that practice what they preach. Look for companies with in-depth security and compliance experience and their own solid SOC 2 compliance.
Astra Security is your safe and trusted choice with a 4.9/5 satisfied user rating. Save time, enhance security, and achieve compliance effortlessly with Astra.
FAQs
Why is SOC 2 compliance software important?
SOC 2 compliance software is vital because it safeguards sensitive data, fosters client trust, and minimizes security vulnerabilities. Thus, it ensures a business’s integrity and data protection in the modern, interconnected digital landscape.
Is SOC 2 compliance necessary for every type of business?
SOC 2 compliance is necessary for any business handling sensitive customer information. It’s useful for cloud computing vendors, managed IT services providers, software-as-a-service (SaaS) providers, and data centers.
Is SOC 2 the same as ISO 27001?
SOC 2 and ISO 27001 are distinct but related standards. SOC 2 focuses on service providers’ controls for data security, while ISO 27001 is a broader information security management system (ISMS) standard applicable to any organization. Both address security but have different scopes and purposes.
Explore Our SOC 2 Series
This post is part of a series on SOC 2. You can
also check out other articles below.