A SOC 2 Penetration Testing (pentest) is often highly recommended by the auditors to demonstrate the effectiveness of the controls implemented during the SOC 2 audit.
Developed by the American Institute of CPAs (AICPA), SOC 2 establishes a comprehensive framework based on 5 key pillars for managing data and strengthening relationships with all stakeholders. However, strong security policies alone aren’t enough to achieve or maintain compliance, often challenging those policies just like a hacker would.
That’s where SOC2 pentesting comes into play. But before we delve deeper into why a pentest plays a vital role in SOC 2, let’s learn a bit more about its compliance requirements.
What is SOC 2 Penetration Testing?
SOC 2 penetration testing is a simulated cyberattack conducted within the framework of SOC 2 compliance. It is designed to identify vulnerabilities in your IT systems and assess their potential impact on securing customer data.
It leverages the Trust Service Criteria (TSC) to guide the testing process. This targeted approach exposes vulnerabilities and provides actionable remediation measures to strengthen your overall cybersecurity posture and demonstrate your commitment to data protection.
What is the difference between SOC 2 Type 1 and Type 2?
SOC 2 Type 1 assesses whether your security controls are properly designed at a specific point in time (providing a snapshot of your control design and confirming that policies and procedures exist and are theoretically sound).
Meanwhile, SOC 2 Type 2 evaluates whether those controls operate effectively over a period of 3-12 months and further tests consistent implementation throughout the reporting period, providing stronger assurance about your ongoing data security commitment.
| Feature | SOC 2 Type 1 | SOC 2 Type 2 |
|---|---|---|
| Focus | Design of controls | Operating effectiveness of controls |
| Report Type | Description of documented policies and procedures | Description of controls AND testing results over a period |
| Timeframe | Specific point in time (usually date of report) | Typically 3-12 months |
| Assessment | Evaluates the suitability of the design of controls to meet the TSC | Evaluates the suitability of the design of controls AND their operating effectiveness over time |
| Testing Procedures | Not required (may include interviews) | Testing of controls to validate their effectiveness |
| Level of Assurance | Lower | Higher |
What are SOC 2 Compliance Requirements?
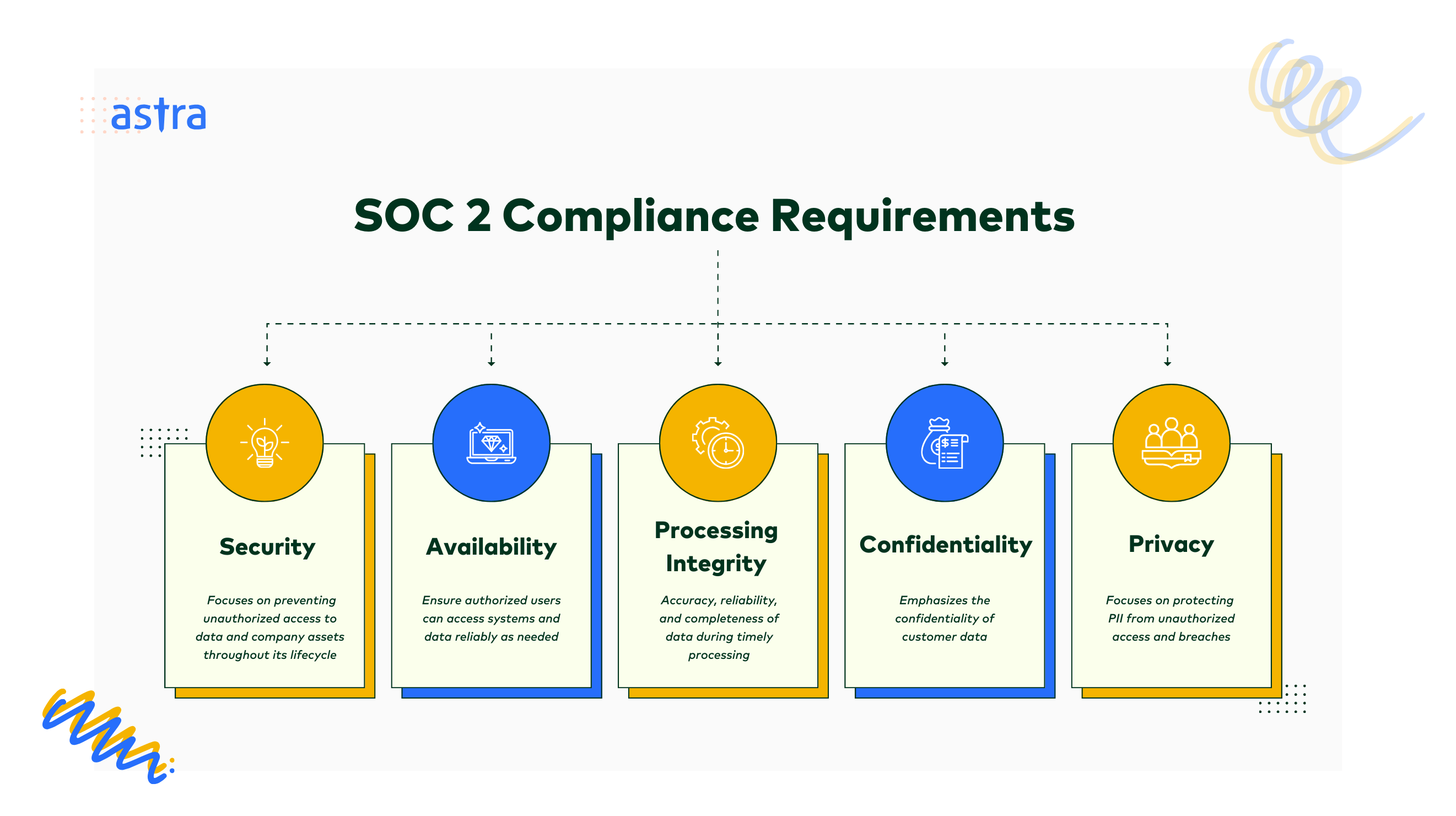
In line with AICPA policies, the SOC 2 framework outlines comprehensive criteria for how organizations should handle customer data based on five Trust Service Criteria (TSC): Security, Availability, Processing Integrity, Confidentiality, and Privacy, as explained below.
1. Security
This is the most crucial principle of SOC 2. It focuses on preventing unauthorized access to data and company assets throughout their lifecycle. It mandates controls to safeguard against malicious attacks, data deletion, misuse, or unauthorized disclosure, among other things.
Some key controls include access controls, intrusion detection systems (IDS), anti-virus, and firewalls.
2. Availability
This criterion aims to ensure authorized users can access systems and data reliably as needed. As such, SOC 2 compliance requires organizations to maintain uptime and minimize downtime through redundancy and disaster recovery plans.
Some common focus areas include network performance monitoring, security incident response procedures, backup and data recovery as well as disaster recovery procedures.
3. Processing Integrity
This principle emphasizes the accuracy, reliability, and completeness of data during timely processing. Controls such as quality assurance procedures and monitoring tools to prevent unauthorized data modification, errors, or omissions fall under this category.
4. Confidentiality
As the name suggests, it emphasizes the confidentiality of customer data. To comply, organizations must limit data collection to what’s necessary, obtain user consent, and practice proper access restrictions, user activity monitoring, and appropriate disposal procedures.
Pro Tip: Data classification and NDAs also help ensure contractual obligations are met and compliance with external factors.
5. Privacy
Unlike Confidentiality, which applies to a broader range of sensitive information, Privacy focuses on protecting Personally Identifiable Information (PII) from unauthorized access and breaches. SOC 2 mandates clear communication of data privacy practices to anyone whose information is stored.
Some key controls include clear privacy policies, rigorous access controls, encryption, and 2FA.

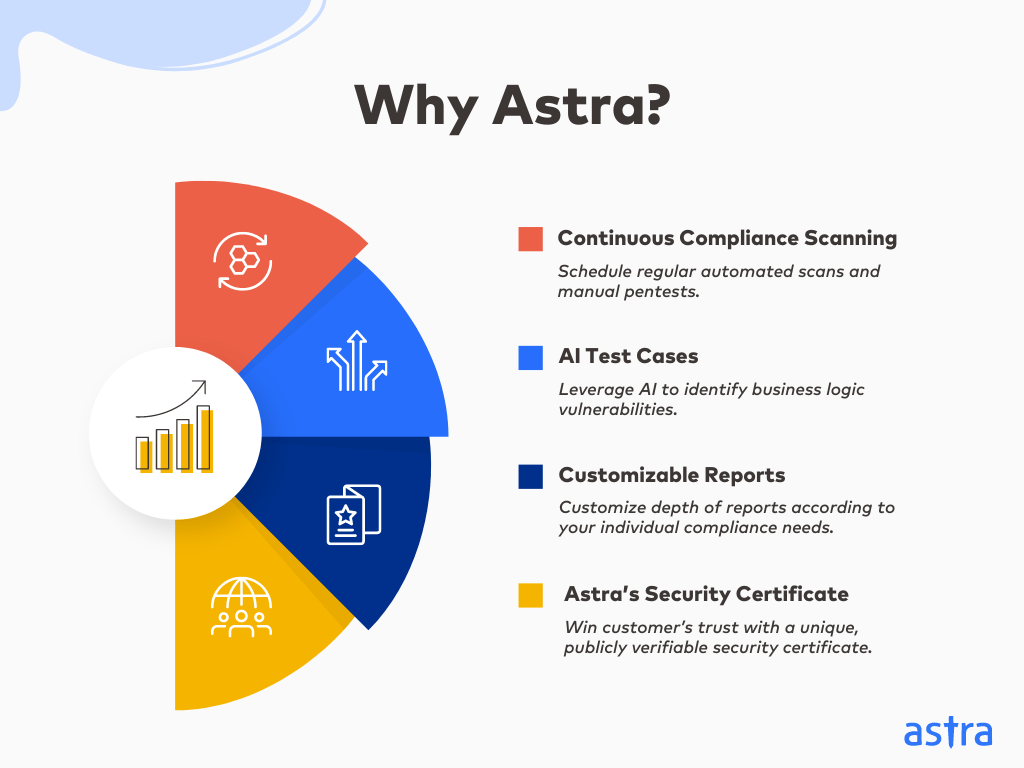
Why Astra is the best in
SOC 2 Pentesting?
- We’re the only company that combines automated & manual pentest to create a one-of-a-kind PTaaS platform with SOC 2 vulnerability tags.
- Vetted scans ensure zero false positives to avoid delays
- Our intelligent vulnerability scanner emulates hacker behavior with 10,000+ tests to help achieve continuous compliance
- Astra’s scanner helps you simplify remediation by integrating with your CI/CD
- Our platform helps you uncover, manage & fix vulnerabilities in one place
- We offer 2 rescans to help you verify ptaches and generate a clean report
- Trusted by the brands you trust like Agora, Spicejet, Muthoot, Dream11, etc.

What are SOC 2 Penetration Testing Requirements per Compliance in 2026?
While SOC 2 frameworks don’t explicitly list penetration testing as a mandatory requirement, auditors consistently view it as an essential component for demonstrating compliance with Trust Services Criteria (TSC), particularly around vulnerability management and risk mitigation.
In practice, annual third-party security assessments and SOC 2 penetration testing have become the industry standard for proving that your protective measures can withstand sophisticated attack scenarios. Organizations that skip this step—or fail to document their remediation efforts—typically face significant challenges during Type II audits and may struggle to receive unqualified reports.
The rationale is straightforward: TSC controls like CC4.1, A1.2, and C1.1 require tangible proof that your defenses work as intended. While alternative evidence methods exist, they’re often more resource-intensive and less convincing to auditors than penetration test results that demonstrate real-world resilience, as explained below.
1. Validating Security Controls (Security Principle):
“CC4.1: The entity selects, develops, and performs ongoing and/or separate evaluations to ascertain whether the components of internal control are present and functioning.”
Simply put, a SOC 2 penetration testing goes beyond static reviews of policies and procedures to actively attempt to exploit vulnerabilities. This provides a more realistic overview of how well your security controls (firewalls, access controls, etc.) would fare in the real world while addressing the Security principle.
2. Identifying Unknown Weaknesses (Availability Principle):
A1.2: “The entity authorizes, designs, develops, or acquires, implements, operates, approves, maintains, and monitors environmental protections, software, data backup processes, and recovery infrastructure to meet its objectives.”
Penetration testers employ various techniques to uncover and address weaknesses that traditional vulnerability scans might miss. Such vulnerabilities could disrupt system availability if exploited by a real attacker. Addressing these weaknesses strengthens your compliance with the Availability principle of SOC 2.
3. Assessing Data Breach Risk (Confidentiality Principle):
C1.1: “The entity identifies and maintains confidential information to meet the entity’s objectives related to confidentiality.”
A pentest for SOC 2 compliance can simulate how an attacker might gain access to sensitive data. This allows your company and auditors to assess the risk and impact of a successful attack with respect to sensitive customer data covered under the Confidentiality principle.
“Many think SOC 2 slows them down. That’s a myth. Automation is key to maintaining agility. If you’re selling SaaS in the US, SOC 2 is essential. It’s a precursor, not an option.”
Lalit Indoria, Co-Founder and CTO, ClearFeed
Does SOC 2 Compliance Mandate Vulnerability Scanning?
The criteria CC7.1 of SOC 2 listed below suggests (if not mandates) regular vulnerability scanning.
CC7.1: “To meet its objectives, the entity uses detection and monitoring procedures to identify (1) changes to configurations that result in the introduction of new vulnerabilities, and (2) susceptibilities to newly discovered vulnerabilities”
In addition to complimenting pentesting, vulnerability scanners help achieve a more comprehensive assessment of the above.
1. Continuous Monitoring
Unlike SOC 2 penetration testing, which is typically conducted periodically, vulnerability scanning can be automated for continuous monitoring. This ongoing assessment helps ensure your security posture remains strong and vulnerabilities are addressed promptly.
2. Early Detection
Vulnerability scans proactively identify weaknesses in systems and applications, allowing your organization to minimize the risk of security incidents that could impact SOC 2 criteria like Security, Availability, or Confidentiality.
3. Control Effectiveness
Vulnerability scanning helps assess the effectiveness of existing security controls, which can be particularly helpful in demonstrating compliance with the Security and Processing Integrity criteria. Auditors often look for evidence of ongoing vulnerability management processes.
What Are The Various Types of Pentests for SOC 2 Compliance?
SOC 2 penetration tests fall into three buckets broadly based on the information provided to testers: Black Box (zero knowledge), White Box (complete access), and Grey Box (partial information). Each approach offers distinct advantages for validating different aspects of your security controls and TSC compliance.
Black Box Pentest
A Black Box Pentest, in the context of SOC 2 pentest requirements, simulates an external attacker with absolutely no prior knowledge of your system, network, or applications. This testing methodology aims to identify vulnerabilities and assess the effectiveness of your security controls.
While the external approach has multiple benefits, the lack of assessment of internal controls, such as IAMs, can hamper efficiency.
White Box Pentest
A White Box Pentest approach to SOC 2 testing provides analysts with complete knowledge of your system’s architecture, configuration details, and potentially even source code. This in-depth access allows for a highly targeted and efficient evaluation of your security posture.
While advantageous, it is crucial to remember, in this case, that the effectiveness of the SOC 2 pentest hinges on the accuracy and completeness of the information provided about the system.
Grey Box Pentest
A Grey Box Pentest provides testers with limited knowledge about your system and environment. This middle ground offers a more efficient and targeted approach than a purely external or internal perspective, making it ideal for SOC 2 compliance.
Simply put, by skipping the time-consuming discovery phase of a black box pentest and yet providing a more targeted control assessment than a white box, a grey box allows for efficient evaluation of security posture against SOC 2 criteria.

Astra Pentest gave us the ability to provide the evidence necessary to satisfy the pentest and vulnerability scanning requirements for our SOC2 certification, which gives our clients confidence that they can trust Validatar with their data as Validatar helps them gain trust in their data.

Darrell Zook
Director of Development & Technology,
Validatar

How Can Astra Security Help?
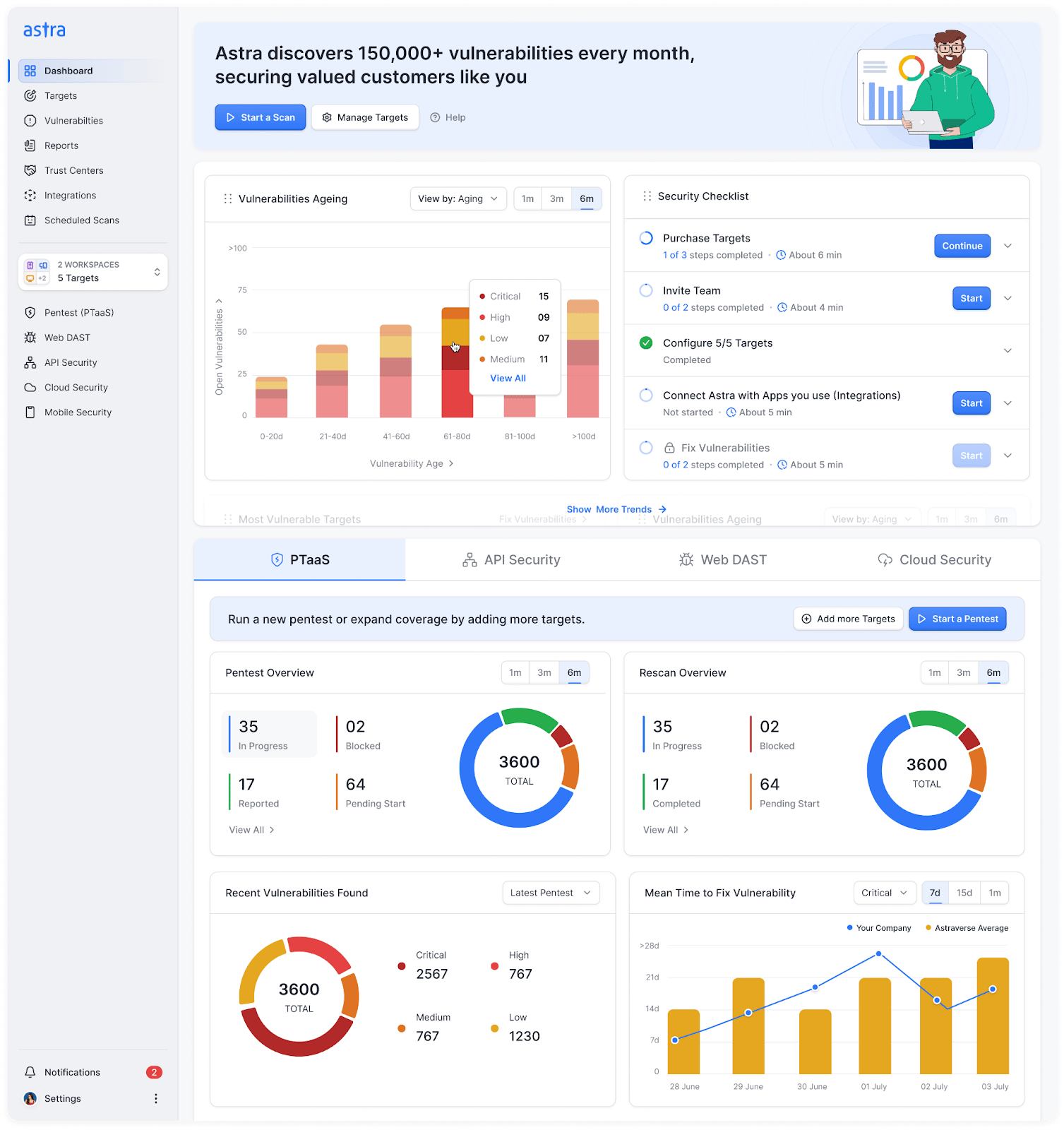
Astra’s unique PTaaS platform combines automated and manual SOC 2 penetration testing to help you stay compliant throughout the year. Our state-of-the-art vulnerability scanner mimics real-world hacker tactics to run 10,000+ security tests on your applications.
Meanwhile, with zero false positives and unique AI test cases, our engineers conduct in-depth pentests to deliver exhaustive SOC 2 reports with remediation steps customized to provide actionable insights at every level, from engineers to executives.
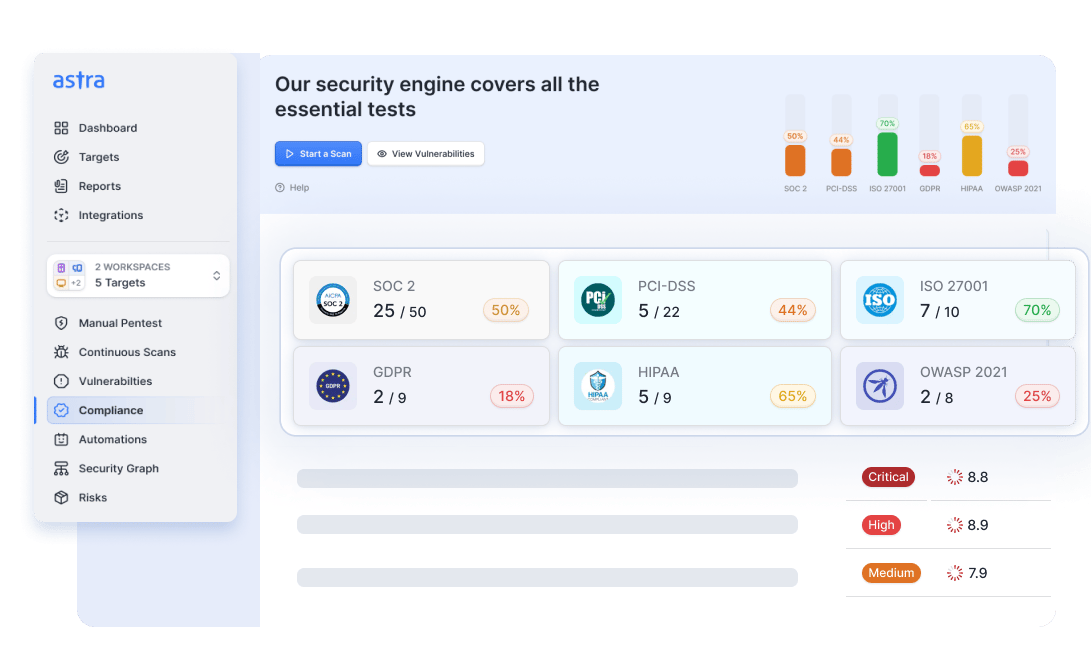
Once vulnerabilities are patched, we conduct a comprehensive rescan to verify effectiveness and provide a clean report for your auditors. Lastly, our seamless tech stack integrations, easy scheduling, regression test capabilities, and real-time expert support help make all pentests simple, effective, and hassle-free.
Final Thoughts
In today’s data-driven world, earning and maintaining SOC 2 compliance is necessary. While not mandatory, VAPT plays a crucial role in achieving continuous compliance with the five SOC 2 Trust Service Criteria.
By pinpointing vulnerabilities and validating the effectiveness of your security controls, SOC 2 pentests help ensure proactive security, demonstrate your commitment to data protection, and build trust with customers.
Lastly, while any manual pentest can meet SOC 2 requirements, continuous pentesting and scans with a platform like Astra help address vulnerabilities throughout the SDLC, thus saving time, energy, and worry that comes with the traditional pentest and remediation cycle.
Key Takeaways
- SOC 2 penetration testing is a simulated attack methodology used to identify security gaps, test control resilience, and demonstrate an organization’s ability to protect customer data in accordance with TSC requirements.
- Annual third-party penetration tests are the de facto standard for proving security controls work against real-world threats.
- Pentests validate three core TSC principles: Security (CC4.1), Availability (A1.2), and Confidentiality (C1.1).
- Grey box testing offers the most efficient approach, balancing targeted assessments with comprehensive control validation.
- Without recent pentest results and documented remediation, achieving a clean SOC 2 Type II report becomes significantly harder.
FAQs
1. What evidence do auditors look for in a SOC 2 penetration testing report?
Auditors expect comprehensive penetration test reports that include executive summaries, detailed vulnerability findings with CVSS scores, evidence of exploitation, and prioritized remediation recommendations. They look for proof that tests covered in-scope systems, documentation of remediation efforts for critical and high-risk findings, and evidence of retesting to confirm fixes were effective before audit completion.
2. Can vulnerability scans replace penetration testing for SOC 2?
While scans identify known weaknesses automatically, they lack the manual exploitation and validation that pentests provide. Auditors view them as complementary; scans offer continuous monitoring between periodic pentests, but only penetration testing demonstrates how an attacker could actually exploit vulnerabilities to compromise your systems and data.
3. What systems should be included in a SOC 2 penetration testing scope?
Include all systems handling customer data: production applications, APIs, databases, authentication systems, network infrastructure, and cloud environments. Your scope must align with your SOC 2 system description and cover components relevant to applicable Trust Services Criteria.
4. What happens if a penetration test finds critical vulnerabilities during a SOC 2 audit?
Critical vulnerabilities identified during SOC 2 audits don’t automatically disqualify you; they require immediate remediation and documentation. You must create corrective action plans, implement fixes promptly, conduct retesting to verify remediation, and provide evidence to auditors. Unresolved critical findings may result in qualified opinions or exceptions noted in your SOC 2 report, potentially impacting customer trust and business opportunities.
5. What is the difference between a SOC 2 pentest and penetration testing?
SOC 2 pentests are a specific type of penetration test designed to assess security controls relevant to the SOC 2 audit. Regular penetration testing might target broader areas, while SOC 2 pentests focus on areas like data security and access controls.
6. How much does SOC 2 penetration testing cost?
A SOC 2 penetration test typically costs between $2,000 and $25,000 depending on the size and complexity of your organization’s systems and controls, as well as the depth of analysis.
Explore Our SOC 2 Series
This post is part of a series on SOC 2. You can
also check out other articles below.