Did you know that there’s no non-compliance fee associated with SOC 2?
Then why is everyone running to get one?
While SOC 2 compliance is voluntary, and the AICPA (American Institute of Certified Public Accountants) doesn’t penalize non-compliance, following this framework’s guidelines can significantly improve your security posture.
Getting SOC 2 helps improve brand credibility, win customers, and give you a competitive edge. Moreover, it helps you build a failproof security system, a necessity, especially when a cyberattack occurs every 39 seconds, with the damage to the economy valued at $10.5 trillion USD annually by 2025.
Top 5 SOC 2 Auditors in 2025
- Schellman & Company, LLC
- A-LIGN
- Linford & Company
- Deloitte
- CyberSapiens
Top 5 SOC 2 Audit Companies & Platforms
Who are SOC 2 Auditors?
A SOC 2 auditor evaluates an organization’s systems and controls to ensure they comply with SOC 2 trust service criteria. This includes assessing security, availability, processing integrity, confidentiality, and privacy controls. These SOC 2 experts provide a detailed report to verify compliance, helping organizations demonstrate reliability to stakeholders.
To maintain independence and objectivity, SOC 2 auditors cannot have any pre-existing relationship with the organization they are auditing.
Note: SOC 2 is a voluntary framework developed by the AICPA that assesses the security levels of your internal system and data based on five pillars: data security, confidentiality, privacy, processing integrity, and availability.
During an audit, such auditors evaluate your security posture with comprehensive pentests to ensure it aligns with industry standards. Once you complete the certification process, your organization receives a SOC 2 report, which you can share with stakeholders to demonstrate your commitment to maintaining high data protection standards.
What SOC 2 Auditor Qualifications Should You Look for?
Choosing a SOC 2 auditor means finding a partner who can read your architecture like an engineer, challenge your controls with real-world judgment, and translate complex design choices into defensible evidence. They should keep the entire process efficient enough to support your roadmap rather than drag it down.
AICPA Accreditation and a Commitment to Audit Rigor
At the baseline, the auditor must be a licensed CPA firm approved to perform SOC examinations under AICPA standards. Just as important is their approach to independence, sampling methodology, and testing depth, which determines how defensible your final report will be with customers and regulators.
Real Experience with Security Control Implementation
Good auditors not only know the Trust Services Criteria, but also how those controls actually materialize in production. Look for someone who has seen hardened baselines, threat modeling practices, log routing strategies, and incident response runbooks across multiple orgs to keep your audit grounded in how controls operate under load rather than how they look on paper.
Deep Command of Cloud Native Architectures
Choose an auditor who understands multi-tenant environments, shared responsibility models, managed services, and common patterns like zero trust segmentation, and are comfortable discussing IAM misconfigurations, data-plane/control-plane separation, KMS workflows, as well as your CI/CD pipeline impact of your control objectives.
If they cannot speak your language, they cannot validate your controls with any real nuance.
Strong Understanding of Automation and Evidence Integrity
Modern audits succeed or fail on evidence quality. Your auditor should understand automated evidence harvesting, log immutability, drift detection, and the nuances of ephemeral infrastructure, as well as what clean telemetry looks like, how to evaluate tamper protections, and how to distinguish cosmetic automation from real observability.
What is the SOC 2 Trust Services Criteria?
The Trust Services Criteria define the control areas your SOC 2 audit measures, and each area maps to real engineering decisions such as how you enforce identity boundaries, protect data in motion and at rest, sustain system uptime, and maintain clean telemetry.
Understanding these criteria helps you design controls that survive scale, minimize operational drag, and stand up to customer scrutiny.
| Criterion | What It Covers | Why Should You Care |
|---|---|---|
| Security | Access control, network protections, monitoring, workload hardening | Proves that your core stack can resist common attack paths and that your detection signals are reliable. |
| Availability | Uptime, redundancy, capacity planning, incident handling | Validates that your service can absorb faults, recover fast, and keep SLOs in good shape. |
| Confidentiality | Data isolation, encryption, key management, retention policies | Ensures sensitive data stays contained and that your crypto hygiene meets customer expectations. |
| Processing Integrity | Input validation, workflow accuracy, data flow consistency | Confirms that your system processes data correctly without silent corruption or logic breaks. |
| Privacy | Collection, storage, and handling of personal data | Demonstrates that your product handles personal data responsibly and aligns with regional privacy rules. |
Best SOC 2 Audit Firms [AICPA Accredited]
If you want a SOC 2 report that holds up under customer scrutiny, procurement reviews, and real risk assessments, you need an AICPA-accredited CPA firm, which operates under SSAE 18 and AT-C 205, maintains independence, and undergoes peer reviews that validate its audit quality.
Here are 5 of the most trusted names, each known for different strengths but all fully qualified to issue a defensible SOC 2 report.
1. Schellman & Company, LLC
Schellman is one of the few CPA firms dedicated almost entirely to IT attestation, which is evident in the precision of its SOC 2 work and its methodical approach: tight alignment with AICPA standards, well-defined sampling strategies, and a high-signal audit process supported by the Schellman Secure Portal for structured evidence intake.
If you’re running a complex, cloud-native environment and want auditors who understand technical nuances without slowing the process, Schellman is a strong fit.
2. A-LIGN
A-LIGN blends traditional CPA audit rigor with a tech-forward workflow built around their A-SCEND platform, giving you predictable evidence cycles, easier collaboration, and a transparent view of your control readiness throughout the engagement. They work well for mid-market SaaS companies scaling fast, where continuous compliance indicators matter just as much as the final report.
3. Linford & Company
Linford & Company brings a more personalized audit model, ideal for teams with unusual architectures, layered compliance needs, or controls that don’t map cleanly to cookie-cutter patterns. Their SOC 2 auditors emphasize clarity in findings, clean documentation, and transparency throughout the engagement, giving you a stronger line of sight into your actual control posture.
If you need a thoughtful SOC 2 audit firm rather than a high-volume machine, Linford is a solid choice.
4. Deloitte
As a Big Four SOC 2 firm and CPA, they combine massive attestation depth with dedicated cybersecurity expertise, making them suitable for enterprises running multi-region infrastructure or multiple trust principles at scale. Their audits are thorough, structured, and built to withstand scrutiny from regulators, strategic partners, and high-scrutiny customers.
5. CyberSapiens
CyberSapiens, as an AICPA-accredited firm, focuses on startups and SMBs that need a clean, credible SOC 2 audit firm without enterprise-level overhead.
They are known for their practical guidance and for helping first-time teams avoid common design and operation pitfalls with prep guidance and a hands-on approach for a strong first-pass success rate, valuable for newcomers who need clear direction with minimal disruption.
How Much Does a SOC 2 Audit Cost?
SOC 2 audit costs vary because the audit mirrors your real environment, and the price moves with your scope, control maturity, and how much cleanup your team needs before testing can begin. Most budgets mix prep work, audit fees, tooling, and yearly upkeep, and the jump from Type I to Type II adds both duration and internal effort.
| Component | Typical Range (USD) | Key Notes |
|---|---|---|
| Readiness Assessment | $5,000 - $20,000 | Finds gaps before the formal audit |
| Risk Assessment | $10,000 - $20,000 | Sometimes packaged into readiness |
| Consultant / Advisory Fees | $150 - $300 per hour | External help for controls, evidence, and remediation |
| Auditor’s Fees (Type I) | $5,000 - $20,000 | Lower for smaller, simpler environments |
| Auditor’s Fees (Type II) | $15,000 - $50,000+ | Scales with audit duration and control surface area |
| Legal / Policy Preparation | $10,000 - $30,000 | Policies, contracts, and documentation updates |
| Compliance Tools (annual) | $5,000 - $30,000+ | Automated evidence and control monitoring platforms |
| Infrastructure / Upgrades | $20,000 - $100,000+ | Security tooling or system changes needed for compliance |
| Penetration Test | $12,000 - $15,000 | Often required for risk validation |
| Internal Team Effort | 100 - 200 hours | Evidence collection, policy work, and audit meetings |
| Annual Maintenance | $10,000 - $60,000/year | Recurring upkeep and yearly audits |
For planning purposes, a Type I audit usually costs $10,000–$25,000, with total first-year spend around $30,000–$50,000 once prep and tooling are included.
A Type II audit is heavier, with audit fees typically in the $15,000–$50,000 range and full program costs reaching $80,000–$150,000 for more complex environments, though teams with broader scope or higher remediation needs should expect to land toward the upper end of each range.
Best SOC 2 Audit Companies & Platforms
Here is a quick side-by-side look at some of the most reputable SOC 2 audit firms, focused on their strengths, typical engagement style, and where they fit best
| Feature | Sprinto | Drata | Secureframe |
|---|---|---|---|
| Platform | Online | Online | Online |
| Remediation Support | Yes | Yes | Yes |
| Compliance | SOC 2, ISO 27001, HIPAA, GDPR | SOC 2, ISO 27001, HIPAA, GDPR | SOC 2, ISO 27001, HIPAA, GDPR |
| Integrations | Slack, GitHub, GitLab, Google, AWS, etc. | GitHub, GitLab, Google, AWS, etc. | Slack, GitHub, GitLab, Google, AWS, etc. |
| Continuous Monitoring | Yes | Yes | Yes |
| Auditor Dashboard | Yes | Yes | Yes |
| Automated Evidence Collection | Yes | Yes | Yes |
| Customizable Controls | Yes | Yes | Yes |
| Vendor Management | Yes | Yes | Yes |
| Anomaly Detection | Yes | Yes | Yes |
| Data Loss Prevention | Yes | No | Yes |
| Cloud Gap Analytics | Yes | Yes | Yes |
1. Sprinto
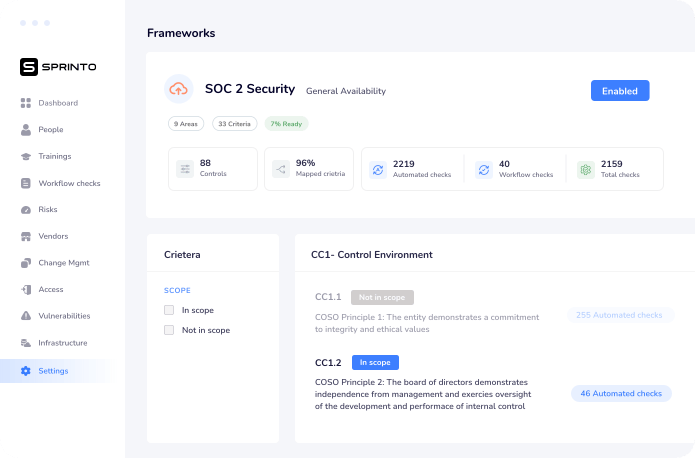
Sprinto offers an automation-driven SOC 2 compliance program that helps cloud-hosted companies become audit-ready in the shortest timeframe possible while eliminating errors to a large extent. It structures your evidence-finding compliance, supports continuous monitoring, and provides a dashboard tailored for SOC 2 service auditors to make the certification process more convenient.
Key Features:
- Mode of Interaction: Online platform
- Capabilities: Automated compliance solution that implements SOC with continuous monitoring features
- Remediation Support: Yes
- Compliance: ISO 27001, SOC 2, HIPAA, and GDPR
- Integrations: Slack, GitHub, GitLab, Google, AWS, and more
- Continuous Monitoring: Yes
- Known For: Auditor’s Dashboard, editable security policy templates, and automated evidence collection
- Price: Available on quote
Pros:
- Setting up security policies that help deliver a seamless auditing experience.
- Facilitates employee onboarding and offboarding.
- Helps in mapping your business and creating an auditable catalog of evidence.
- Becoming compliance-ready within weeks, investing only 10-14 hours of your time.
Limitations:
- Since the tool is customized to each company’s specific needs, it could take some time to function efficiently.
Doing SOC 2 manually is extremely tedious. I wouldn’t recommend it. Use a software platform. We use Sprinto. It’s cost-effective and handles all our logs in one place. It simplifies the entire process.
Lalit Indoria, Co-Founder and CTO, ClearFeed
2. Drata
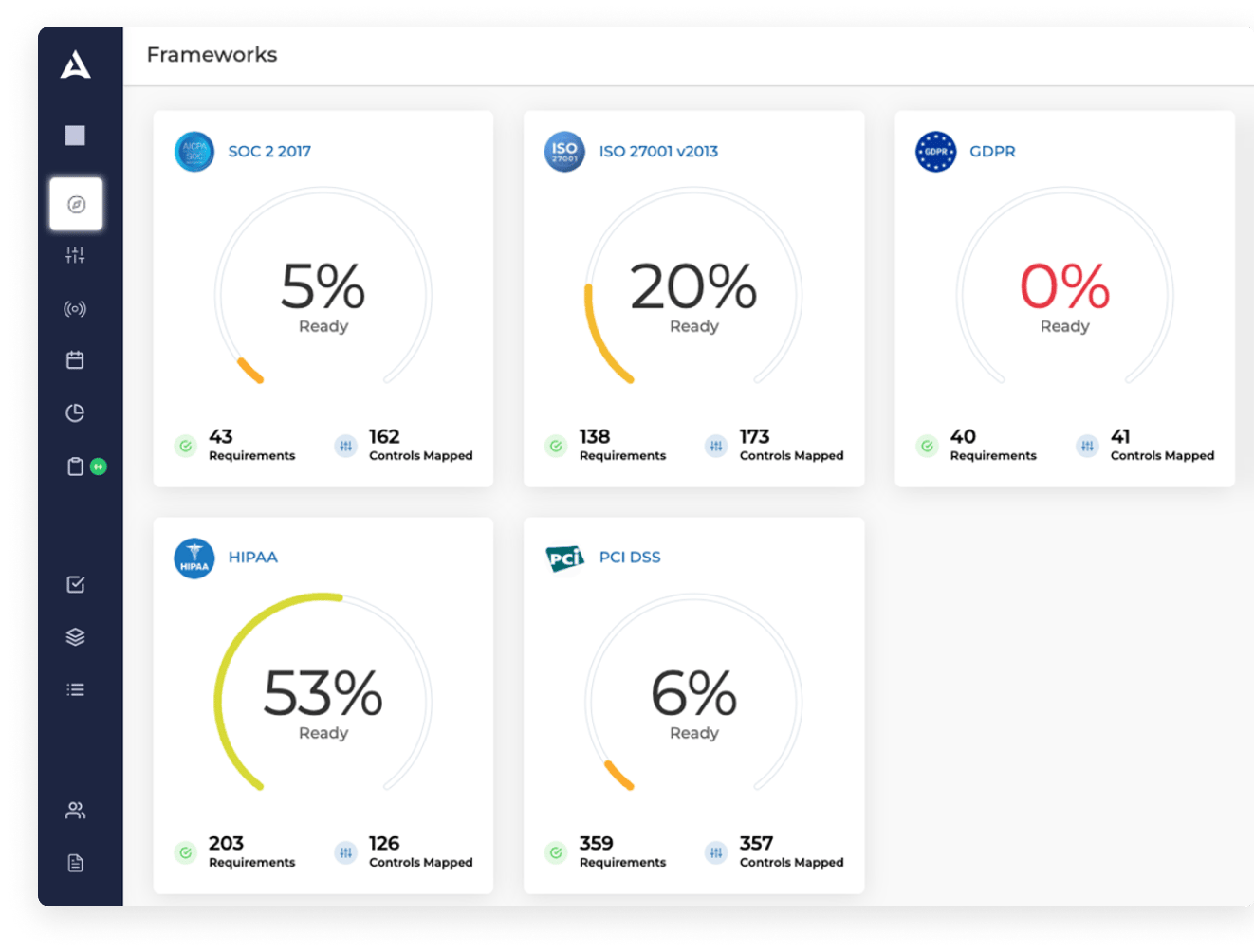
Drata, as a SOC 2 audit firm, focuses on creating an audit-friendly control environment by standardizing evidence, enforcing continuous control checks, and organizing documentation exactly the way auditors need to see it. Its customizable controls and integrations make it easier to shape your audit scope accurately, especially when your environment or trust principles vary.
Simply put, it helps businesses comply with various regulations, including SOC 2, ISO 27001, HIPAA, GDPR, PCI DSS, and more.
Key Features:
- Mode of Interaction: Online platform
- Capabilities: Automated evidence collection and continuous monitoring for SOC 2.
- Remediation Support: Yes
- Compliance: ISO 27001, SOC2, HIPAA, and GDPR
- Known For: Automated asset creation, customizable security controls, data integration with MDM for endpoint evaluation
- Continuous Monitoring: Yes
- Integrations: GitHub, GitLab, Google, AWS, and more
Pros:
- Automates evidence collection and cataloging, saving businesses time and effort.
- Seamless integration with various tools and platforms, simplifying compliance management.
- Streamlined the SOC 2 audit process with a user-friendly interface.
- Customized policies help cater to your unique needs.
Limitations:
- Lacks risk assessment features.
- Limited reporting capabilities compared to other SOC 2 audit firms.
3. Secureframe
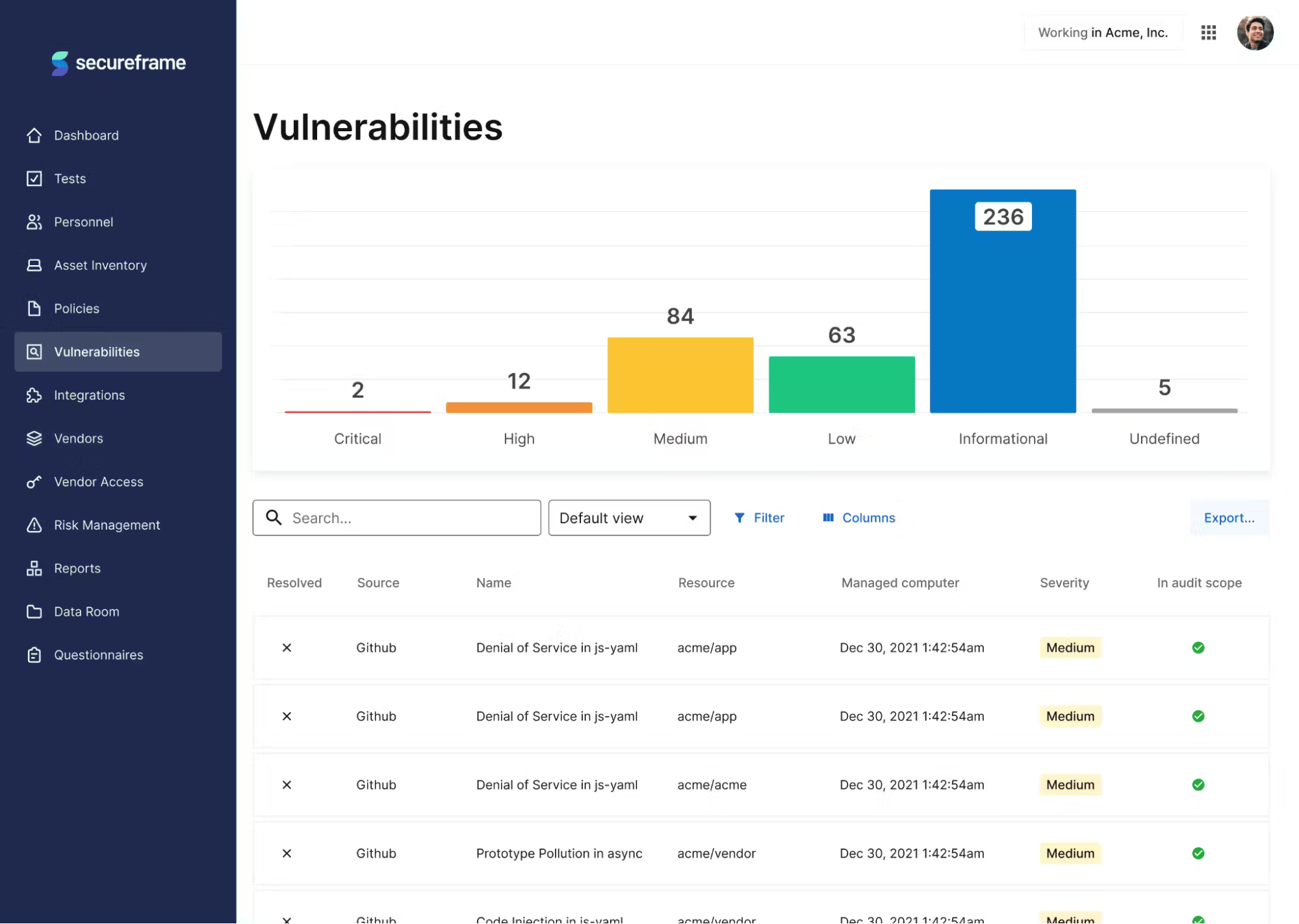
Secureframe centers its workflows around audit preparation and remediation, making it easier to remove blockers before an auditor arrives. Connecting your environment and scanning for issues early helps you resolve gaps that typically turn into exceptions, while its dedicated CSM structure provides guided audit readiness for teams new to SOC 2.
Key Features:
- Mode of Interaction: Online platform
- Capabilities: Streamlined SOC 2 audit preparation with comprehensive support.
- Remediation Support: Yes
- Compliance: ISO 27001, SOC2, HIPAA, and GDPR
- Known For: Automated evidence collection, seamless vendor management, dedicated CSM
- Continuous Monitoring: Yes
- Integrations: Slack, GitHub, GitLab, Google, AWS, and more
Pros:
- The audit interface simplifies access to information for AICPA-approved SOC 2 service providers.
- Easy access to information helps avoid back-and-forth with auditors.
- Saves time and effort.
- Reports facilitate easy analysis and remediation.
Limitations:
- It may involve a potential learning curve.
4. Vanta
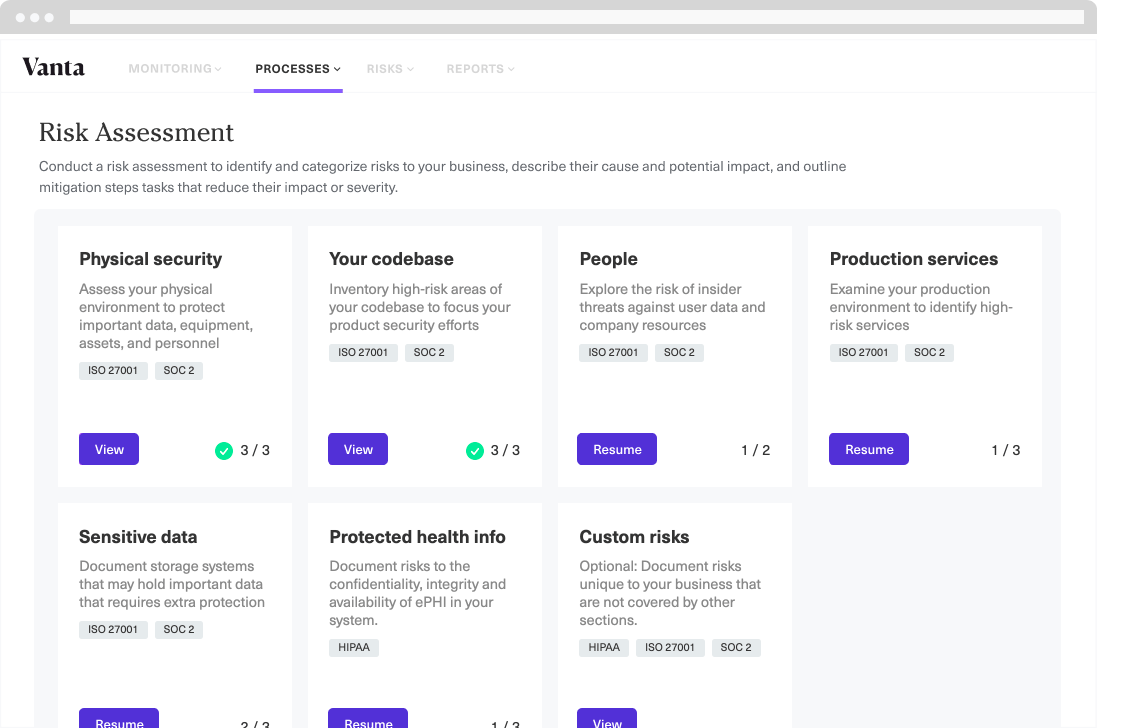
Vanta focuses heavily on keeping your audit period clean and defensible through continuous hourly checks, mapped controls, and strong integrations. Its automated workflows help ensure that configuration drift, onboarding/offboarding gaps, and asset inconsistencies don’t show up as exceptions during SOC 2 audit testing.
It also connects users with vetted auditors familiar with its evidence structure.
Key Features:
- Mode of Interaction: Online platform
- Capabilities: Offers a holistic suite for SOC 2 compliance automation and management.
- Remediation Support: Yes
- Compliance: ISO 27001, SOC2, HIPAA, and GDPR
- Known For: Centralized dashboard, automated RFP management, employee information management, and mapped security controls.
- Continuous Monitoring: Yes
- Integrations: Slack, GitHub, GitLab, Google, AWS, and more
Pros:
- Tailored security controls based on AICPA guidance.
- Continuous testing for security and compliance verification.
- Faster audit report generation.
- Simplified compliance management.
Limitations:
- Limited information on SOC 2 reporting capabilities.
- Involves potential learning curve.
5. LogicGate
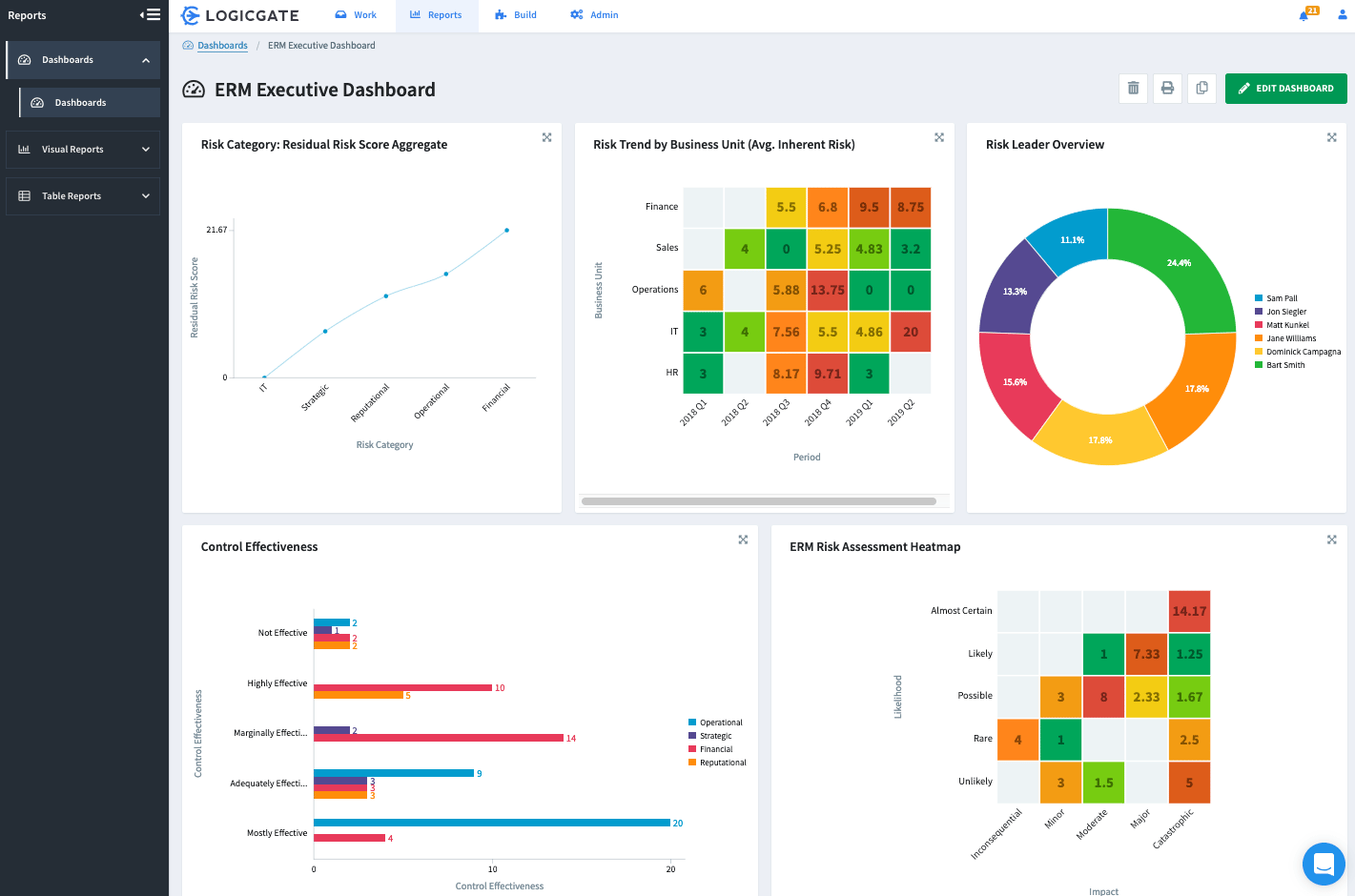
LogicGate strengthens the audit experience by centralizing risk, controls, and remediation into one system that aligns directly with SOC 2 audit requirements. Its Risk Cloud brings regulatory controls, assessments, and evidence into an organized structure, helping you present a coherent audit story without piecing data together manually.
Key Features:
- Mode of Interaction: Online platform
- Capabilities: Cloud-based risk management platform focusing on regulatory compliance, including SOC 2.
- Remediation Support: Yes
- Compliance: ISO 27001, SOC2, HIPAA, and GDPR
- Known For: Inventory of regulatory controls, risk assessment, and corrective action plans.
- Continuous Monitoring: Yes
- Integrations: Slack, Jira, GitHub, GitLab, Google, AWS, and more
Pros:
- Helps businesses fix security gaps and remain compliant.
- Keeps you updated on your security posture and makes compliance with industry-specific changes easy.
- Explains and mitigates potential security consequences.
Limitations:
- It may not cover all the relevant controls for SOC 2.
How Can Astra Help You Achieve SOC 2 Compliance?
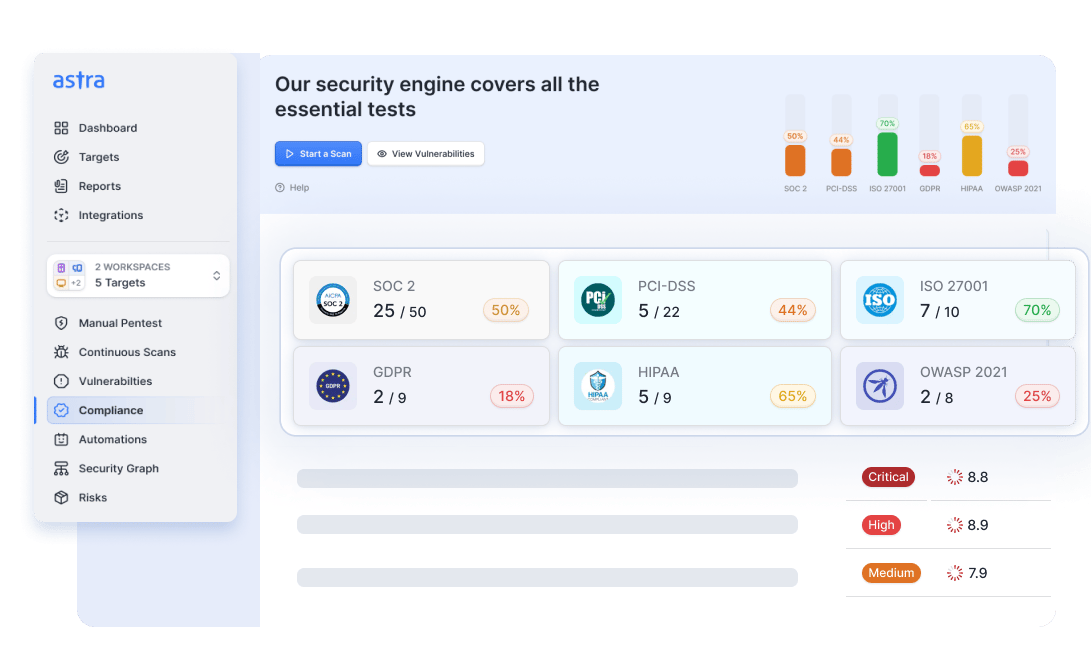
Astra Security‘s Vulnerability Assessment and Penetration Testing (VAPT) services can help you track vulnerabilities that prevent you from achieving SOC 2 compliance and provide detailed remediation steps to tackle them.
We combine automated vulnerability scanning with pentesting to identify over 10,000+ vulnerabilities across web apps, mobile apps, cloud infrastructures, APIs, and networks.
This ensures that all your systems are aligned with SOC 2 controls for secure configuration, allowing you to address CVEs relevant to the SOC 2 framework.
Our security experts manually vet the scan results once vulnerability scanning is complete to ensure zero false positives. Then, for our manual pentest, they mimic real-world attacker tactics. We place emphasis on finding business logic vulnerabilities, which are critical for achieving compliance with SOC 2’s Security, Availability, Processing Integrity, and Confidentiality (SAAIC) principles.
We adhere to industry standards like OWASP and SANS25, and our VAPT reports can be customized to provide dedicated SOC 2 auditor reporting and highlight vulnerabilities that map directly to relevant SOC 2 controls.
What are Common SOC 2 Audit Exceptions (And How to Avoid Them)?
An exception is any point where your stated control and your real operation fall out of sync, and most of them come from drift, inconsistency, or processes that lean too heavily on people instead of guardrails.
The patterns repeat across most audits: manual tasks that slip, logging that isn’t uniform, pipelines with soft edges, policies that age out, and incidents that move faster than the documentation meant to capture them. Here are some of teh most common ones:
Stale or Inconsistent Access Reviews
These show up when reviews depend on manual effort, scattered ownership, or outdated role mappings inside IAM, which means, over time, accounts go stale, offboarding leaves gaps, and permissions drift in ways that are easy for an auditor to surface through basic sampling. The underlying issue is usually a lifecycle that relies on reminders rather than automation.
Pro Tip: Automate reviews, sync HR events to IAM, and keep the lifecycle tight.
Missing or Incomplete Logging
Logging breaks when different services follow different standards, when retention windows aren’t monitored, or when high-volume components shed events under load. Even a minor gap can create an incomplete evidence trail that fails audit testing because the auditor cannot link activity across systems, stemming from inconsistent configurations rather than a significant outage.
Pro Tip: Set one logging standard and check completeness routinely.
Unapproved or Unticketed Changes
Change control exceptions occur when pipelines allow bypasses, teams push emergency fixes straight to prod, or approvals get skipped without guardrails, i.e., the record of who changed what disappears, and the auditor treats it as a direct control failure, widespread in fast-moving teams that rely on trust instead of enforcement.
Pro Tip: Block direct-to-prod changes and require everything to flow through a reviewed path.
Outdated or Unaligned Policies
Policies age out when teams evolve their workflow, but the documentation never follows, leaving an obvious mismatch for the auditor to discover while comparing written policy to the way your engineers actually operate. Even if the practice is solid, the gap between intent and execution is treated as an exception.
Pro Tip: Review and update policies whenever the process shifts.
Weak Incident Response Evidence
These exceptions arise when incidents move fast, get fixed quickly, and leave no structured record of decisions, timestamps, or actions, meaning that without a trail, auditors cannot confirm the control ran as claimed, even if the response was handled well. The root cause is usually reliance on memory or scattered chat logs instead of a repeatable playbook.
Pro Tip: Use a simple playbook and record steps during the event, not after.
Why Do You Need SOC 2 Compliance?
SOC 2 helps you unlock trust at scale by showing customers, partners, and regulators that your security practices hold up under real scrutiny.

1. Builds Trust with Customers
While voluntary, SOC 2 certification greatly emphasizes a business’s commitment to safeguarding customer data through an objective audit and increasing brand credibility. Your company’s transparency reduces customers’ perceived risk, establishing you as a trustworthy partner in their minds.
“People wouldn’t even talk to us without SOC 2. It’s very difficult to sell without compliance. Our first customer was hesitant. They questioned our resources and data security. SOC 2 compliance turned the deal around.”
Lalit Indoria, Co-Founder and CTO, ClearFeed
2. Competitive Edge
Achieving SOC 2 compliance can improve your positioning with vendors and customers, simplify approval procedures, and lead to new business prospects in a competitive market. Many organizations now require a SOC 2 certification from their vendors and partners, so achieving it can open doors to new business opportunities.
3. Building a Culture of Security
Achieving SOC 2 certification fosters a culture of security within your organization. Preparing for an audit requires a company to critically examine its security controls and identify areas for improvement by conducting vulnerability assessment and penetration testing.
These proactive security procedures help you understand your company’s security posture. You can use the insights to identify gaps and build a more secure organization.
Learn SOC 2 Penetration Testing
4. Compliance Foundation for Other Regulations
SOC 2 compliance aligns with many other data security regulations, such as GDPR and HIPAA. The rigorous security controls implemented for SOC 2 often serve as a strong foundation for meeting the requirements of these other regulations, saving significant time and resources in achieving other compliance certifications.
5. Expanding to New Geographies
The specific Trust Service Criteria (TSCs) addressed in a SOC 2 report can be tailored to address the requirements of different geographic regions. For example, a company looking to expand into the European market may want to focus on controls that align with GDPR.
Similarly, a healthcare company expanding in the USA would benefit from a SOC 2 report demonstrating compliance with HIPAA requirements. By complying with relevant regional regulations, a company can simplify its entry into new markets and establish itself as a trusted partner to local businesses and customers.

Astra Pentest gave us the ability to provide the evidence necessary to satisfy the pentest and vulnerability scanning requirements for our SOC2 certification, which gives our clients confidence that they can trust Validatar with their data as Validatar helps them gain trust in their data.

Darrell Zook
Director of Development & Technology,
Validatar

Who Does SOC 2 Audits?
The SOC 2 audit itself isn’t done by software, so it’s worth knowing exactly which type of organization is trusted to validate your controls.
1. Independent Auditors
Since SOC 2 focuses on trust and transparency, the audits must be performed by a completely independent third party. This independence ensures an objective assessment of your controls, free from any internal bias.
2. Certified Public Accountants
These independent SOC 2 auditors are typically licensed Certified Public Accountants (CPAs) or belong to an auditing firm accredited by the AICPA (American Institute of Certified Public Accountants). They possess the expertise and qualifications necessary to evaluate your internal controls against the SOC 2 Trust Service Criteria.
3. Streamlining Using Tools
Platforms designed to streamline the steps needed before SOC 2 can be used in the pre-audit stage to conduct VAPT, specifically designed to assess controls relevant to SOC 2 guidelines. A qualified and independent CPA or CPA firm will then conduct the final assessment and issue the SOC 2 report.
What to Consider When Choosing a SOC 2 Auditing Platform
Picking the right SOC 2 platform is easier when you know which capabilities actually move the needle and which ones only look good on a feature list.
1. Evidence Management
Managing evidence for a SOC 2 audit can be daunting. Look for a platform that automates evidence collection across your entire digital landscape, from cloud providers like AWS to collaboration tools like Microsoft 365.
This ensures auditors have easy access to all the necessary information while reducing their workload by eliminating manual collection processes.
2. Risk Management
A good SOC 2 auditing platform goes beyond simply collecting evidence and integrating risk management features to improve your security posture proactively. This might include pre-formulated security policies that align with SOC 2 controls, automated assessments to identify and address vulnerabilities, and security awareness training for your employees.
By focusing on prevention, you can minimize the risk of non-compliance issues arising during the audit.
3. Acceptance by SOC 2 Compliance Auditors
While a compliance auditing platform makes the process much easier, and some platforms may even recommend auditors, it’s important to remember that a separate, independent CPA firm conducts the final audit.
Therefore, focus on platforms with a proven track record of successful audits across various auditors. Popularity among auditors often indicates a platform’s alignment with best practices and AICPA guidelines, giving you greater confidence in its ability to prepare you for a successful audit.
4. Continuous Monitoring Support
Real-time monitoring is critical for maintaining SOC 2 compliance. Choose a platform with integrations to your cloud environments and other essential tools, which should enable continuous monitoring of your security controls and configurations.
Ideally, the platform should trigger alerts for deviations from compliance standards, allowing you to take immediate corrective action and minimize risk.
5. Compliances Supported
Many SOC 2 controls overlap with security regulations like ISO 27001, HIPAA, and GDPR. Opt for a platform that supports multiple compliance frameworks, which can significantly reduce your workload and simplify the process when pursuing additional certifications.
A multi-compliance platform ensures your security practices align with a broader range of industry standards.
6. Support for Custom Compliance Frameworks
“Change management is crucial. Document everything, have approvals, test thoroughly, and monitor deployments.”
Lalit Indoria, Co-Founder and CTO, ClearFeed
While pre-built compliance frameworks are valuable, some organizations may have additional security requirements unique to their industry or business model. The ideal platform should offer flexibility to incorporate custom security controls and frameworks alongside existing standardized frameworks.
This ensures a comprehensive compliance approach that addresses your specific needs while adhering to broader SOC 2 standards.
Final Thoughts
SOC 2 compliance demonstrates your commitment to adopting the best data security practices, fostering trust and confidence with clients and stakeholders.
Some of the benefits of a SOC 2 certification include building trust with customers, gaining a competitive edge, and establishing a culture of security in your company. While many SOC 2 auditing platforms are available, our top three choices are Sprinto, Drata, and Secureframe.
By strengthening your security posture using VAPT, leveraging the right supporting tools and resources like Astra, and fostering a culture of security awareness within your organization, you can achieve compliance and build a strong foundation for long-term success.
FAQ
1. Are SOC 2 auditors and SOC 2 vendors the same?
SOC 2 service auditors and vendors aren’t the same. The primary objective of SOC 2 vendors is to help you prepare for a compliance audit by completing the required tests, training, and remediation to achieve compliance. Sometimes, the SOC 2 vendor also helps you find an auditor.
2. How much time does a SOC 2 audit take?
The timeline for a SOC 2 audit is largely variable. After you have prepared for the audit, the auditing process can take up to a couple of months. The preparation leading up to the audit is where you can save a lot of time by choosing the right vendor.
3. How much does a SOC 2 audit cost?
The cost of a SOC 2 audit can vary depending on factors such as the company’s size and scope. On average, small to midsize companies spend between $12,000 and $20,000 on an audit, but the total cost can go up to $100,000 for larger companies.
4. What is the difference between SOC 2 Type I and SOC 2 Type II?
Type I checks whether your controls are designed correctly at a specific moment, while Type II tests whether those same controls operate reliably over a period. Type II offers stronger assurance because it reflects real, continuous performance instead of a snapshot.
5. How do SOC 1, SOC 2, and SOC 3 differ?
SOC 1 focuses on controls that impact financial reporting, SOC 2 evaluates security and operational controls for technology providers, and SOC 3 delivers a simplified, public version of a SOC 2 report. Each serves a different audience and assurance need.
Explore Our SOC 2 Series
This post is part of a series on SOC 2. You can
also check out other articles below.










