Securing today’s enterprise attack surface feels a lot like securing the sky. The real problem with an attack surface this size is understanding what is moving underneath it, detecting vulnerabilities as they surface, deciding which ones actually matter, and knowing what to do about them before someone exploits it.
Almost 70% of web application breaches occur simply because vulnerabilities were never fixed in time. When you’re dealing with dozens or hundreds of findings at once, the difference between staying ahead and falling behind comes down to speed and smart prioritization.
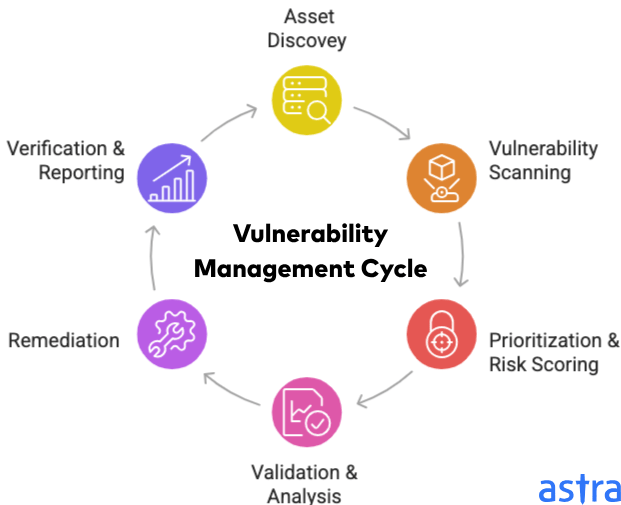
That’s exactly what vulnerability management does. It delivers continuous visibility, risk-based scoring, and fast remediation workflows that cut through the noise and keep MTTR under control while satisfying every compliance requirement.
So if you’re looking to buy a tool or partner with a vulnerability management company, this blog will help you understand exactly what vulnerability management is, the different types available today, and the top 5 vulnerability management companies in 2026.
What are Vulnerability Management companies?
Vulnerability management companies are cybersecurity vendors that provide platforms, tools, and services to security teams to find, assess, and fix vulnerabilities across their IT assets. In simple terms, it’s a manager responsible for your digital asset’s security posture.
Vulnerability scanning, management, assessment, and testing are the four terms often conflated, but each represents different activities with different scopes and outputs.
Vulnerability scanning is the non-invasive automated process of probing systems to detect known weaknesses.
Vulnerability assessment goes a step further. It takes scan results and adds context: business impact, exploitability, and asset criticality.
Vulnerability testing (often called penetration testing) is an active simulation of a cyberattack to confirm whether a vulnerability is genuinely exploitable. It requires human expertise and is typically scoped and scheduled, not continuous.
How we selected the best vulnerability management companies
Every company on this list was evaluated against a consistent set of criteria and real-world capabilities that directly affect security outcomes.
Scalability and deployment model
Does the platform fit organizations at different maturity levels, and can it scale as the asset inventory grows?
Scanning accuracy
Does the tool find what’s there without many false positives?
Risk-based prioritization
Does the platform help teams decide what to fix first, using threat intelligence, exploitability data, and asset criticality?
DevSecOps integration
Does the tool plug into CI/CD pipelines, container registries, and IaC scanning? Modern vulnerability management tools can’t exist outside of the development workflow.
Top Vulnerability Management Companies in 2026
The vulnerability management companies have matured past the point where the core question is “Does this tool find vulnerabilities?” Every major platform on this list does. Differentiation now lives in specific technical dimensions of the product that directly determine security outcomes.
While many solutions exist, these top 5 vulnerability management companies consistently rank highest in analyst reports, ace in our review, and market adoption due to their feature sets, scalability, and integration capabilities.
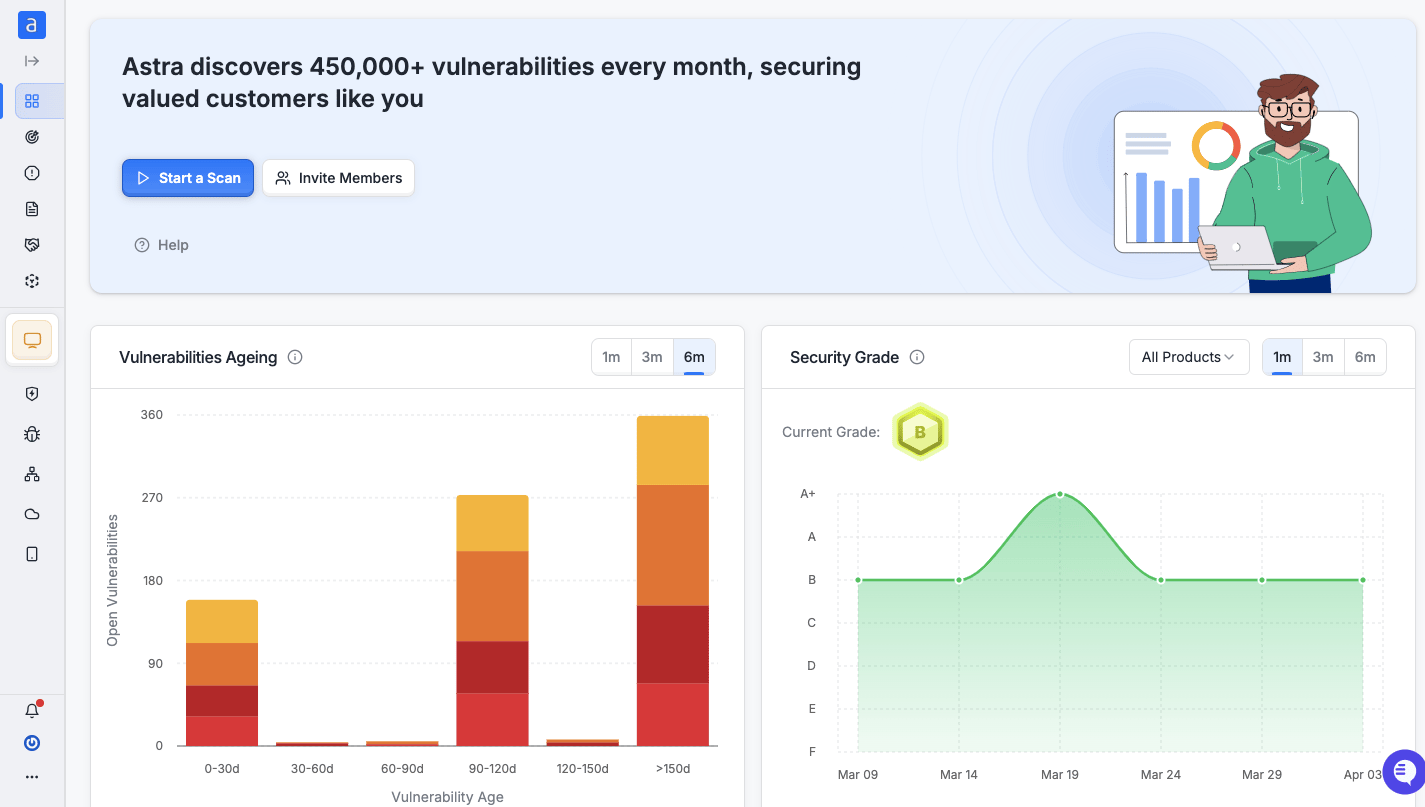
1. Astra security[Get Started]

Astra Security is a continuous pentest and vulnerability management platform that combines 15,000+ automated security tests with expert manual testing across web applications, APIs, cloud infrastructure, mobile apps, and network devices. Trusted by 1,000+ companies, including GoDaddy, TATA, and Dream11.
Key features
- Zero False Positives – Every alert is reviewed by security engineers and confirmed before being reported.
- Once a vulnerability is marked fixed, Astra’s engineers retest the specific finding to confirm the remediation, providing verified closure.
- Issues a publicly verifiable pentest certificate upon completion, backed by the Astra Trust Center, giving sales, procurement, and compliance teams client-facing proof of security posture
- Native integrations with GitHub, GitLab, Jira, Slack, Azure DevOps, Bitbucket, and major CI/CD pipelines
- Compliance reporting pre-mapped to SOC 2 Type II, PCI DSS 4.0, ISO 27001:2022, HIPAA, and GDPR
- AI-assisted business logic testing for vulnerability classes that signature-based scanners structurally cannot detect
- Offers a dynamic dashboard to track vulnerabilities easily.
Best for
Enterprises, SaaS companies, fintech, healthtech, and mid-market organizations that need the accuracy of manual pentesting in a frequency of continuous automated scanning from a single platform rather than a stitched-together toolchain.
Pricing
Vulnerability scans start at $69; comprehensive pentest plans start at $5,999 annually.
Want Better pricing, tailored to you.
Pros
- Authenticated scanning covers the post-login application attack surface.
- Zero false positives through vetted scans.
- Provides a client-facing pentest certificate as proof of security posture with public verifiability.
- Detects business logic vulnerabilities that automated platforms miss by design
Cons
- Only a 1-week free trial is available.
2. Qualys VMDR
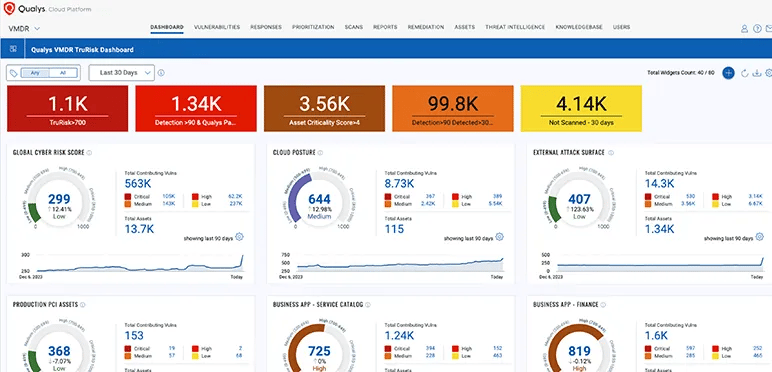
Qualys VMDR (Vulnerability Management, Detection, and Response) is a cloud-native, multi-tenant SaaS platform that unifies asset discovery, risk prioritization, and remediation workflow in a single platform.
Key Features:
- Continuous asset discovery across cloud, containers, OT, and endpoints
- TruRisk scoring that combines CVSS with real-world threat intelligence
- Automated patch deployment via integrated patch management
- Built-in policy compliance and configuration assessment
- Audit-ready compliance reporting for PCI DSS, HIPAA, and more
Best for
Enterprises managing large, distributed asset inventories across hybrid environments
Pricing
Costs approximately $199–$250 per asset per year.
Pros
- Provides automated remediation for SOAR.
- Uses threat intelligence for prioritization.
Limitations
- High licensing costs and an asset-based pricing model increase the total cost of ownership.
- Steeper learning curve and requires a dedicated SecOps team for tuning.
3. Rapid7 InsightVM
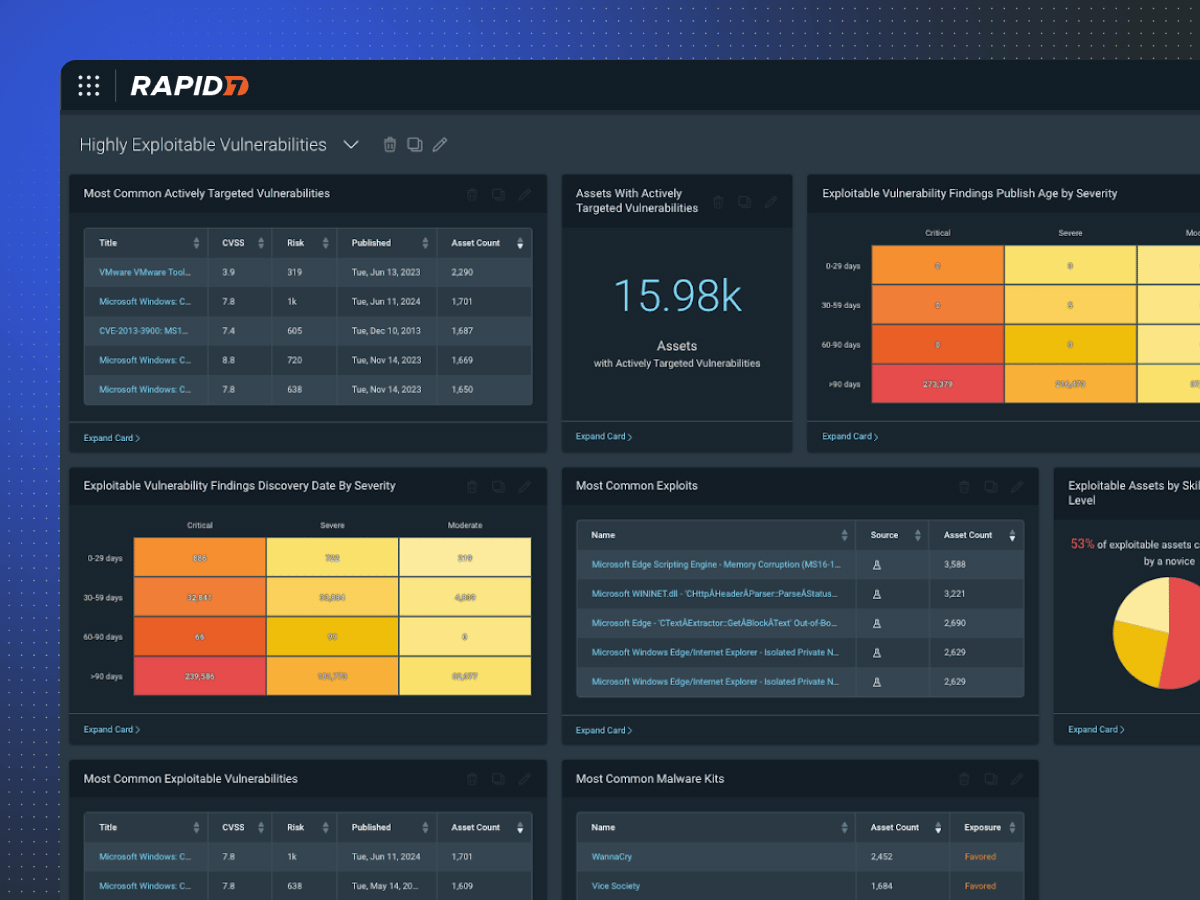
InsightVM is Rapid7’s live vulnerability management solution, built on the Nexpose scanning engine and the Insight Cloud platform. Its technical differentiators are Metasploit-correlated prioritization and a Remediation Projects workflow that closes the gap between security detection and engineering action.
Key Features
- Real-time agent and agentless scanning for continuous assessment.
- Active Risk Score combining CVSS, exploit availability, and asset criticality.
- Live dashboards with customizable risk reduction tracking
- Integration with over 40 business and security applications.
- Asset tagging and grouping for prioritized remediation by business unit
Best for
Security operations teams that already use Metasploit for red team or validation workflows.
Pricing: InsightVM pricing is per-asset with volume discounts for larger deployments.
- 250 assets: ~$2.19/month per asset ($26.25/year)
- 500 assets: ~$1.93/month per asset ($23.18/year)
Annual cost for 500 assets: Roughly $11,000–$15,000, depending on exact configuration.
Pros
- Excellent hybrid infrastructure coverage.
- Excellent integration with workflow tools.
- Provides customizable continuous visibility and reporting.
Limitations
- Asset discovery is not good for external-facing or shadow assets.
- Initial deployment and console configuration can be time-consuming.
4. Wiz
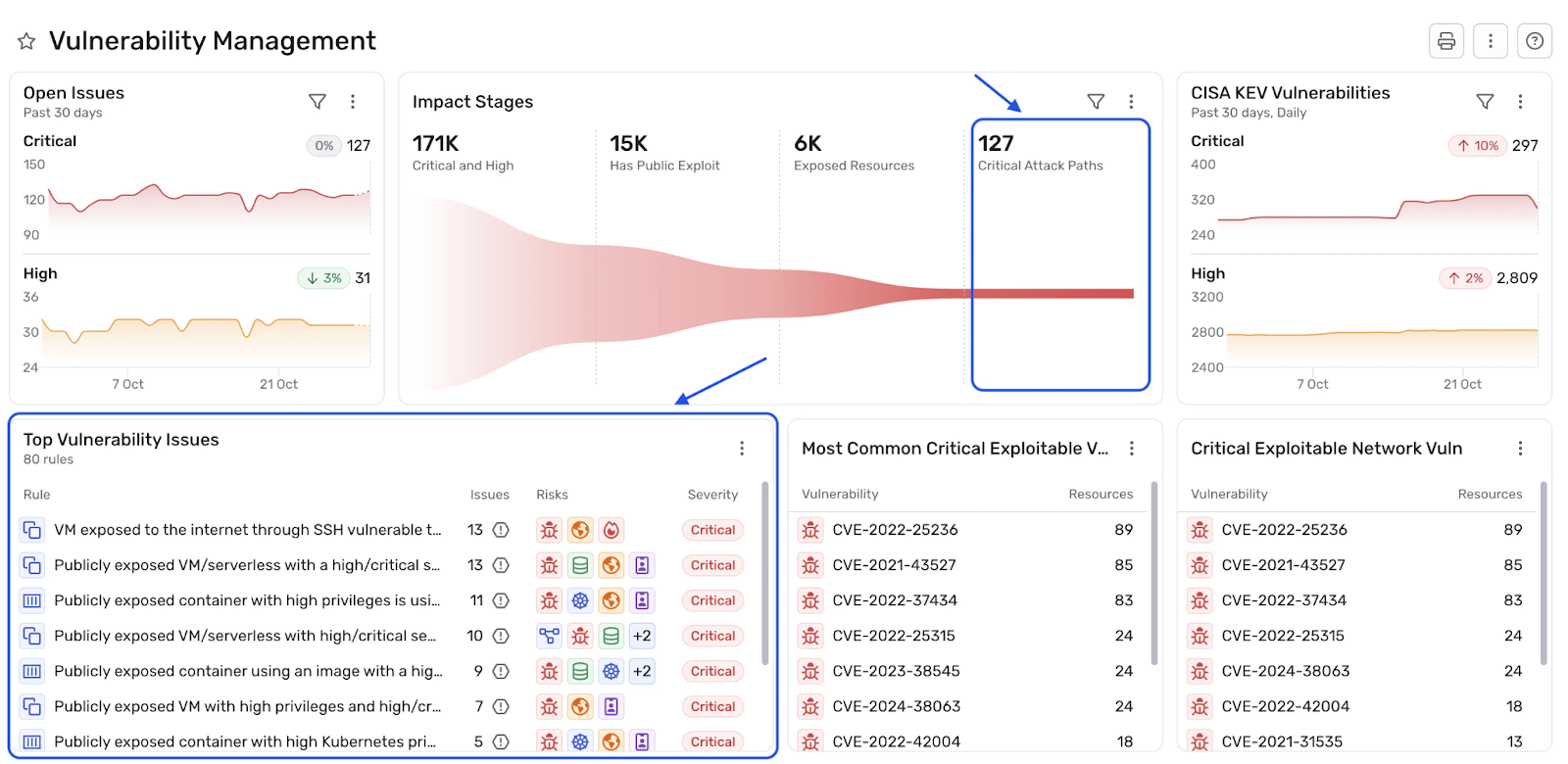
Wiz is a cloud-native application protection platform (CNAPP) with vulnerability management as a core capability. Its agentless, API-based architecture achieves full cloud environment visibility in minutes without installing software on workloads.
Key features
- Agentless scanning across various cloud providers (e.g., AWS, Azure, GCP, and OCI) with no deployment overhead.
- Security Graph that correlates vulnerability findings with cloud context (exposure, IAM, data sensitivity).
- Supports integration with CI/CD pipelines for shift-left vulnerability detection.
- Risk prioritization based on actual exploitability within cloud topology.
Best for
Cloud-native organizations running complex multi-cloud or Kubernetes-heavy workloads, where infrastructure scanning depth or on-premises coverage is required.
Pricing
Wiz pricing is based on workload and starts at $24,000/year.
Pros
- Agentless, API-driven Security Graph delivers real-time contextual prioritization of internal misconfigurations.
- Modern and intuitive UI.
Limitations
- Limited coverage for on-premises, OT/IoT, or legacy infrastructure.
- Need heavy workflow tuning.
5. Tenable
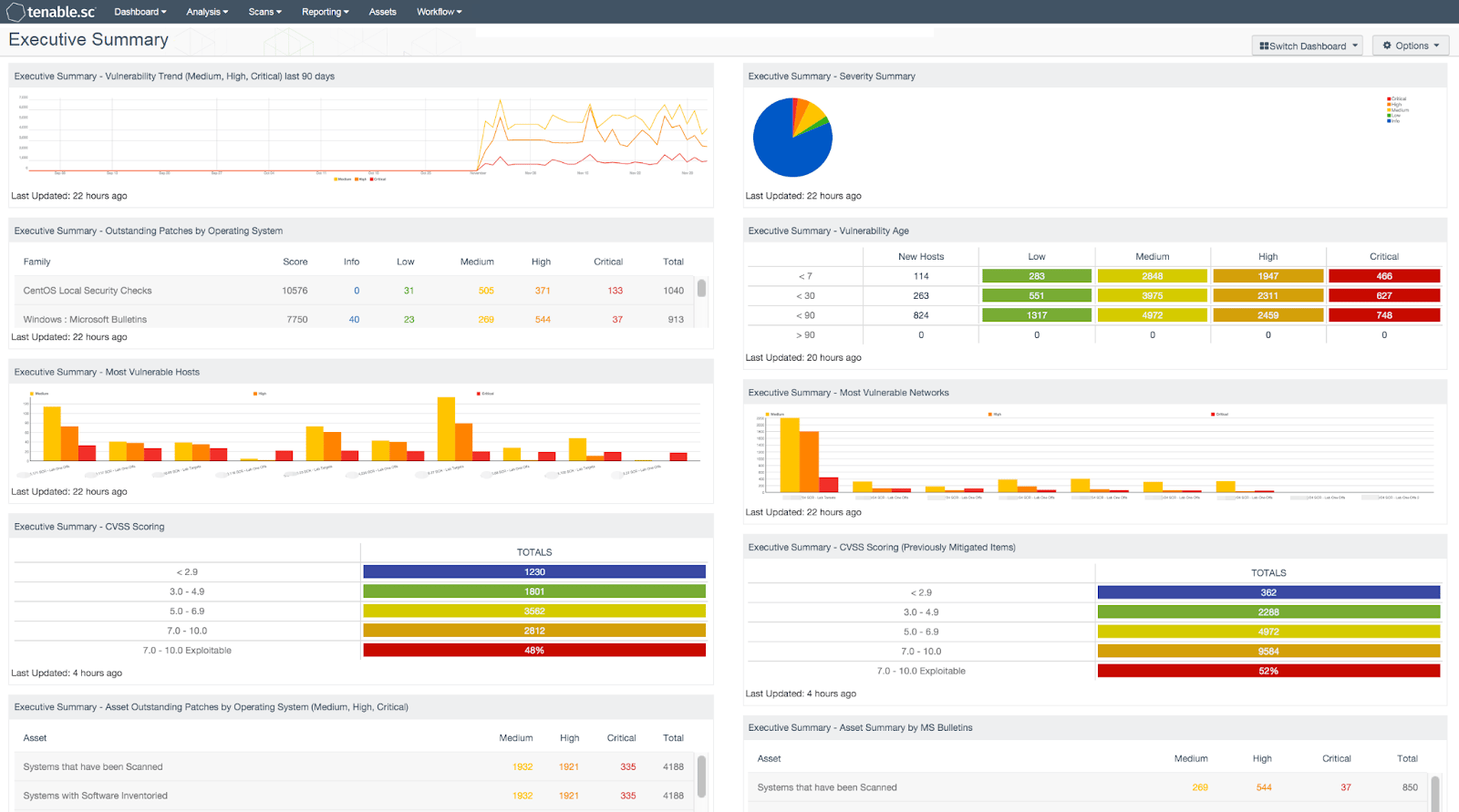
Tenable Vulnerability Management, powered by the Nessus engine, delivers continuous internal misconfiguration detection across hybrid, cloud, container, and OT estates. It provides predictive prioritization beyond CVSS, automated asset discovery with real-time drift detection for various serious security flaws.
Key features
- Agentless and agent-based scanning for on-prem, cloud, and OT environments
- Lumin Exposure View for executive-level risk reporting.
- Native integration with ServiceNow, Jira, Splunk, and major SIEMs.
- Attack Path Analysis that models lateral movement risks across infrastructure.
- Web application scanning and container security.
Best for
Large enterprises with hybrid infrastructure (on-premises, cloud, OT/ICS).
Pricing model
Tenable uses asset-based licensing with options for standalone or full exposure management. For 100 assets, it would cost around $3,500–$5,800/year.
Pros
- Deepest plugin library in the market.
- Mature OT/ICS coverage for industrial environments where other VM platforms lack protocol support.
Limitations
- Tenable One’s full capability requires significant licensing.
What are the types of Vulnerability Management Providers?
Vulnerability management companies offer solutions across various categories, each with a different deployment model and use cases. Understanding which type of vulnerability management companies match your operational model is as important as comparing individual feature sets.
For example, an external vulnerability scanner is the wrong solution for manufacturing organizations with significant OT exposure.
Cloud vulnerability management platforms
Cloud vulnerability management platforms are SaaS-delivered specialized security solutions built for cloud-native infrastructure. They identify, assess, prioritize, and remediate vulnerabilities across cloud environments. These platforms are mostly agentless and rely on cloud providers’ APIs, metadata streams, and control-plane integrations to provide real-time visibility with minimal performance overhead. Ideal for organizations running predominantly cloud or containerized workloads.
External vulnerability scanning companies
External vulnerability scanning companies are specialized security providers that focus exclusively on mapping and monitoring an organization’s internet-facing attack surface, i.e., what attackers see before they get inside your perimeter.
This tool will be particularly valuable for organizations that have grown their web presence rapidly and need to know what’s exposed externally.
Managed vulnerability management services (VMaaS)
Managed vulnerability management services are delivered by MSSPS that operate or provide the vulnerability management platform on behalf of the customer. Security teams at MSSPs or specialized providers handle scanning configuration, triage, reporting, and remediation guidance on your behalf.
This model suits organizations without dedicated security engineering teams. In simple terms, VMaaS provides a staffed operation and tooling rather than just tooling.
Exposure management platforms
Exposure management platforms represent the latest evolution of vulnerability management platforms towards a broader CTEM (Continuous threat exposure management model).
These platforms can go beyond CVE scanning to provide a holistic view of all exploitable attack paths with identity exposures, misconfigurations, and third-party risks. This gives security teams a true picture of their exploitable attack surface. Exposure management platforms are complex in design and expensive, but they answer “What is vulnerable?” and “How can threat actors chain the vulnerabilities?”
Why Businesses Need Vulnerability Management Services
The threat landscape in 2026 is a complete mess and more hostile than ever. NIST NVD published more than 49,000 CVEs in 2025 alone, and with an increase in AI adoption, it could easily cross 60,000 or 70,000 in 2026.
Partnering with effective vulnerability management companies can shift security operations from a reactive patching cycle to a proactive, risk-driven program that significantly reduces the organization’s MTTR. Some other benefits of having vulnerability management companies as partners are
For example, Log4Shell (CVE-2021-44228) was exploited within 72 hours of its disclosure, even in 2021. Now it’ll be much shorter, and a vulnerability management program is a must to identify assets quickly in scenarios like this, to perform a workaround or understand the blast radius.
- Continuous asset inventory with deep context (cloud workloads, containers, serverless, APIs)
- Integration with CI/CD pipelines for pre-production scanning
- Continuous compliance mapping against frameworks like NIST CSF, HIPAA, and PCI-DSS
- Significant reduction in MTTD and MTTR
Beyond threat reduction, embedding a vulnerability management tool into a security program also plays a critical role in compliance and operational efficiency.
Almost all EU, UK, and US-based cybersecurity-related or tech-related standards and regulatory frameworks now directly or indirectly mandate continuous vulnerability scanning and risk management.
A strong VM program helps organizations meet these requirements with minimal manual effort while maintaining audit-ready evidence and reports.
How to Choose the Right Vulnerability Management Provider
Most vendor evaluations start with feature lists. The more useful starting point is understanding what your current VM program structurally cannot detect and building the selection criteria from that gap.
Questions to ask every vendor before shortlisting:
- When a vulnerability is marked remediated, does the platform automatically re-test to confirm the fix, or does verification require a manual trigger?
- Does the platform offer multi-surface coverage from a single data model (cloud, web app, API) in a unified view?
- Can the platform trigger a scan on every PR merge?
- Does your platform offer scanning behind the login?
- What is your false positive rate on authenticated web application scans, and how is false positive management handled in the remediation workflow?
- How do you detect IDOR, broken object-level authorization, and business logic vulnerabilities
- Are vulnerabilities mapped to known international compliance standards?
The platform that answers all 7 of those questions cleanly with technical specificity is the one that has actually built the capability rather than checked a roadmap box.
Most platforms answer 2 or 3 questions well. The ones that cover scan behind login, automated + manual detection, and CI/CD integration are worth buying.
Every vulnerability management company offers trials or limited evaluations. Run two or three platforms against your actual environment, compare the findings quality, prioritization accuracy, and integration experience, and based on that, make a final call.
What are the Benefits of Using a Vulnerability Management Tool?
A good vulnerability management tool changes how quickly your security teams move from exposure to remediation. The operational and security benefits compound the longer the program runs, and they’re measurable in ways that most other security investments aren’t.
Here’s what a mature VM program actually delivers:
Confirmed fixes
Platforms supporting targeted re-scans of individual findings (rather than requiring full environment rescans to confirm a single patch) reduce validation cycle time and generate the audit evidence record that shows a vulnerability was confirmed resolved, rather than simply marked closed in a ticket.
Reduced Attack Surface
Every confirmed, remediated vulnerability is a potential entry point for a threat actor. Upon maturing, a consistent vulnerability management program measurably shrinks the number of viable entry points available to attackers. Mean time to remediate (MTTR) by severity, open critical finding count week over week, and re-introduction rate (how often fixed vulnerabilities resurface) are the metrics that prove this.
The less visible benefit is what gets caught upstream. Platforms integrated into CI/CD pipelines catch vulnerable dependencies and misconfigurations before they ever reach production. This upstream interception at the PR stage is where mature vulnerability tools provide their ROI.
Improved Security Posture
Security posture improvement is the good ripple effect of the 2 above. Organizations that run consistent vulnerability management programs for more than 12 months develop institutional knowledge of where vulnerabilities keep coming, which development patterns introduce risk, and which asset classes carry disproportionate exposure.
This Pattern recognition enables management-level fixes (e.g., security training, development standards changes, architectural decisions) that reduce the rate at which vulnerabilities are introduced in the first place.
Vulnerability Management vs Vulnerability Assessment vs Vulnerability Testing
Understanding these distinctions helps organizations build the right security program and choose the right mix of vulnerability management services.
Engaging a specialized Vulnerability Management Company brings significant advantages to organizations seeking to strengthen their cybersecurity defenses.
| Aspect | Vulnerability Scanning | Vulnerability Assessment | Vulnerability Testing |
|---|---|---|---|
| Nature | Entirely automated process | Automated scanning + manual/AI-assisted analysis | Manual simulation of a cyberattack in a controlled way |
| Method | Signature-based (CVE matching, benchmark checks) | Risk scoring (CVSS + environmental/contextual factors) | Exploit chaining, TTPs emulation |
| Scope | Broad network/asset discovery | Targeted contextual risk evaluation | Scoped attack simulation |
| Frequency | High-frequency/ recurring | Continous | Scheduled |
| Output | Raw vulnerability list with basic severity | Prioritized findings with business impact & remediation guidance | Exploit proof-of-concept, attack paths & post-exploitation results |
| Human Involvement | None | Limited | Full (active exploitation & chaining) |
| Vulnerability Validation | None, only theoretical | Contextual | In-depth vetting and validation |
| False Positives | Very high | Moderate | Nill |
Final Thoughts
As vulnerability volumes are expected to increase in 2026, relying on traditional scanning is walking blindfolded.
The most effective security programs combine broad automated discovery with intelligent prioritization and real-world validation. While Tenable, Qualys, and Rapid7 Vulnerability Management each bring strong automation and scalability to the table, Astra Security stands out by bridging the critical gap between theoretical findings and confirmed exploitability.
Organizations that are ready to invest in a meaningful partnership with vulnerability management companies will be far better positioned to defend against modern cyber threats.
The global vulnerability management market is projected to reach USD 24.08 billion by 2030, growing at a CAGR of approximately 8% from 2025 to 2030, a clear signal that investment in this space is accelerating due to heavy needs.
FAQ
1. What do vulnerability management companies do?
Vulnerability management companies provide platforms, tools, and services that help organizations continuously identify, assess, prioritize, and remediate security weaknesses across their IT infrastructure.
2. What is the difference between vulnerability scanning and vulnerability management?
Vulnerability scanning is a single technical activity, running an automated tool to detect known CVEs and misconfigurations. Vulnerability management is the full program that includes asset discovery, risk prioritization, remediation tracking, compliance reporting, and continuous monitoring.
Scanning is a component of vulnerability management, not a substitute for it.
3. Are vulnerability management services suitable for small businesses?
Absolutely. Many vulnerability management companies offer SMB-friendly tiers with simplified interfaces, managed service options, and affordable pricing. For small businesses without dedicated security staff, Astra security suits them best and caters all thier in budge
4. How often should vulnerability scans be performed?
The answer depends on your environment and risk tolerance. For internet-facing assets and critical infrastructure, continuous or daily scanning is the standard. For internal networks and lower-risk assets, weekly to monthly cycles are common








