HIPAA Penetration testing refers to the scanning and exploitation of a security system that needs to be HIPAA-compliant to find hidden vulnerabilities and risks. Doing HIPAA penetration testing helps organizations fix the vulnerabilities found, thus maintaining compliance and avoiding hefty fines.
Whether it was the Kaiser Permanente attack in 2024 or Change Healthcare, the growing attacks on the healthcare industry have pushed CIOs into overdrive to achieve HIPAA compliance and secure critical patient data.
According to the Health Insurance Portability and Accountability Act (HIPAA), any company, organization, hospital, or pharmaceutical company that uses and stores confidential health information is required to carry out continued risk analysis through penetration tests or vulnerability assessments.
Ensure your systems meet HIPAA security standards. [Book a HIPAA penetration testing demo] and identify compliance gaps before audits.
HIPAA Penetration Testing Requirements
1. Risk Analysis
Risk analysis is the process of scanning and or analyzing an organization’s security system to identify vulnerabilities that could cause potential damage to the sensitive data stored by that organization. This can range from confidential patient health information (PHI) to various test results.
Due to the sensitive nature of the information, HIPAA mandates continuous risk analysis to protect patient health information (PHI). While the guidelines don’t specify a particular type, auditors often prefer a combination of continuous scans and pentesting due to its comprehensive approach and accuracy.
2. Vulnerability Patches
HIPAA mandates prompt remediation of vulnerabilities identified through risk assessments like penetration testing. Failing to address these weaknesses can expose sensitive patient data to breaches.
Penetration testing reports provide detailed findings, including actionable risk scores, to help your team prioritize and remediate vulnerabilities efficiently, ensuring ongoing HIPAA compliance.
3. Continuous Scanning
To maintain or achieve HIPAA compliance, continuous monitoring, scanning, and conducting HIPAA compliance penetration testing are essential to identify any new vulnerabilities that threaten an organization’s online security.
The tools for HIPAA penetration testing must be fully integrated with the security system to provide automated continuous monitoring. This should also ensure that there will be no false positives or unnecessary resource expenditures.

Why Astra is the best in pentesting?
- We’re the only company that combines automated & manual pentest to create a one-of-a-kind pentest platform.
- Vetted scans ensure zero false positives.
- Our intelligent vulnerability scanner emulates hacker behavior & evolves with every pentest.
- Astra’s scanner helps you shift left by integrating with your CI/CD.
- Our platform helps you uncover, manage & fix vulnerabilities in one place.
- Trusted by the brands you trust like Agora, Spicejet, Muthoot, Dream11, etc.

Steps in HIPAA Penetration Testing
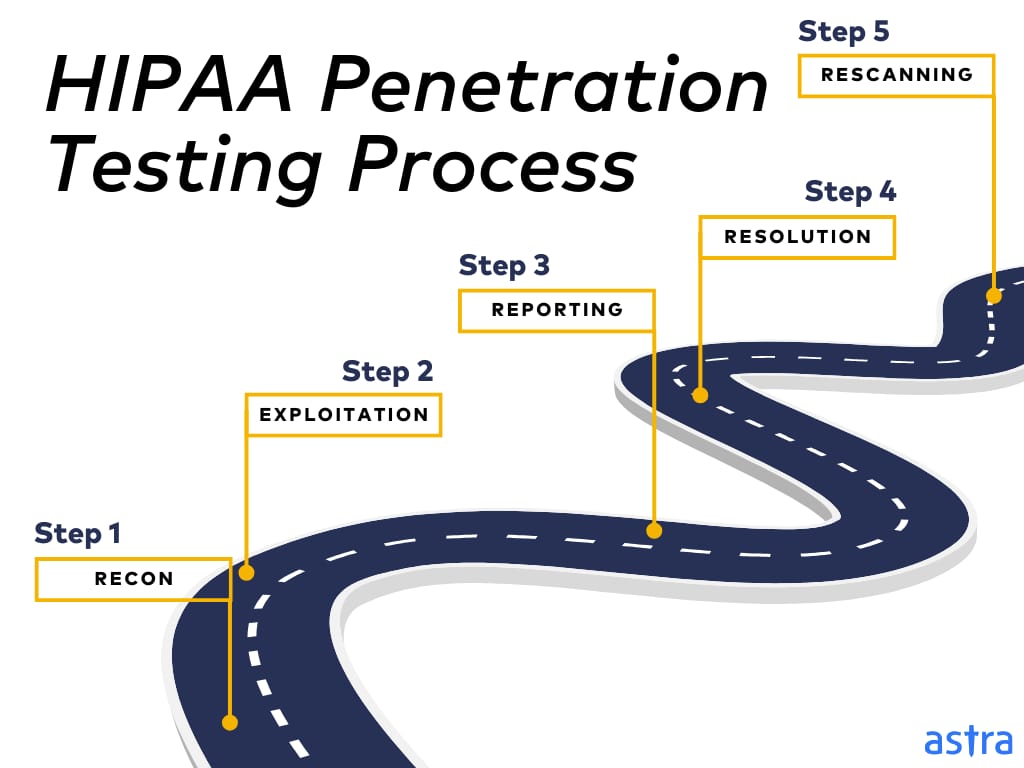
1. Reconnaissance
Reconnaissance refers to the research phase of the pentest, where the pentesting teams aim to find all the information they can about the publicly available target. This is done after scoping, where all the assets are to be tested, and the reasons and the limits are discussed to avoid any legal troubles and scope creep.
There are two types of reconnaissance, active and passive surveillance:
- Active reconnaissance refers to finding information about the target through thorough interaction. This type of surveillance requires prior permission from the target.
- Passive reconnaissance refers to finding information without any interaction from the actual target through publicly available online resources, such as websites.
2. Exploitation
This is the phase where the information from the reconnaissance is scanned and tested to find different vulnerabilities. These vulnerabilities are identified based on a vulnerability database of known CVEs, the OWASP Top 10, and SANS 25.
Vulnerabilities can also be found using an automated, comprehensive vulnerability scanner, which can be vetted with a manual pentest to avoid false positives.
3. Reporting
Once the exploitation phase of the penetration testing process has been completed, a detailed report is issued with an executive summary and information on the scope of the test, rules of engagement, methods employed, and, lastly, a list of the CVEs identified.
Each vulnerability is described in detail, along with its CVSS scores, impact, and actionable remediation guidance for prioritization through POC videos and customer assistance.
Don’t risk non-compliance penalties. [Request a HIPAA pentest demo] to validate your safeguards and fix vulnerabilities early.
4. Resolution
Once an organization receives the penetration testing report, the identified vulnerabilities must be promptly addressed to mitigate risks. This helps avoid any breaches or threats to security, maintain compliance, and enhance trust of patients.
5. Rescanning
This is the last step in the pentesting procedure to safeguard the fixes made to the security of an organization’s assets. A quick rescan or pentest is conducted to verify the patches rolled out by the organization.
Once this step is complete and zero vulnerabilities have been detected, the organization’s online security can be said to be completely safe, and a security certificate is also issued by some select vendors.
Recommended Reading: What is Pentest? A Complete Guide for 2026
How to Choose The Right HIPAA Pentesting Partner?
1. Reputation
Ensure that the company you opt for to meet your HIPAA penetration testing requirements has a good reputation and experience within the field. You can vet this through reviews and comparisons available online, as well as through interaction with existing or previous customers to learn their thoughts.
2. Certifications
Ensure that the compliance penetration testing provider you opt for is compliant with all the standard regulations and rules that they need to follow. Also, ensure that pentesters within the company have the right experience and certifications to make your pentesting and compliance journey a breeze.
3. Detailed Reporting
Ensure that the reports provided by the pentesting company are detailed and have easy-to-follow steps, as well as POC videos to help ease the remediation process. A bonus is that they provide a collaboration feature between the pentesters and the development team.
4. Budget
Choose a pentest services provider that is within your budget and offers options to customize and tailor the penetration test to your specific requirements.
Astra Pentest is built by the team of experts that helped secure Microsoft, Adobe, Facebook, and Buffer

The Healthy Solution – Astra Pentest
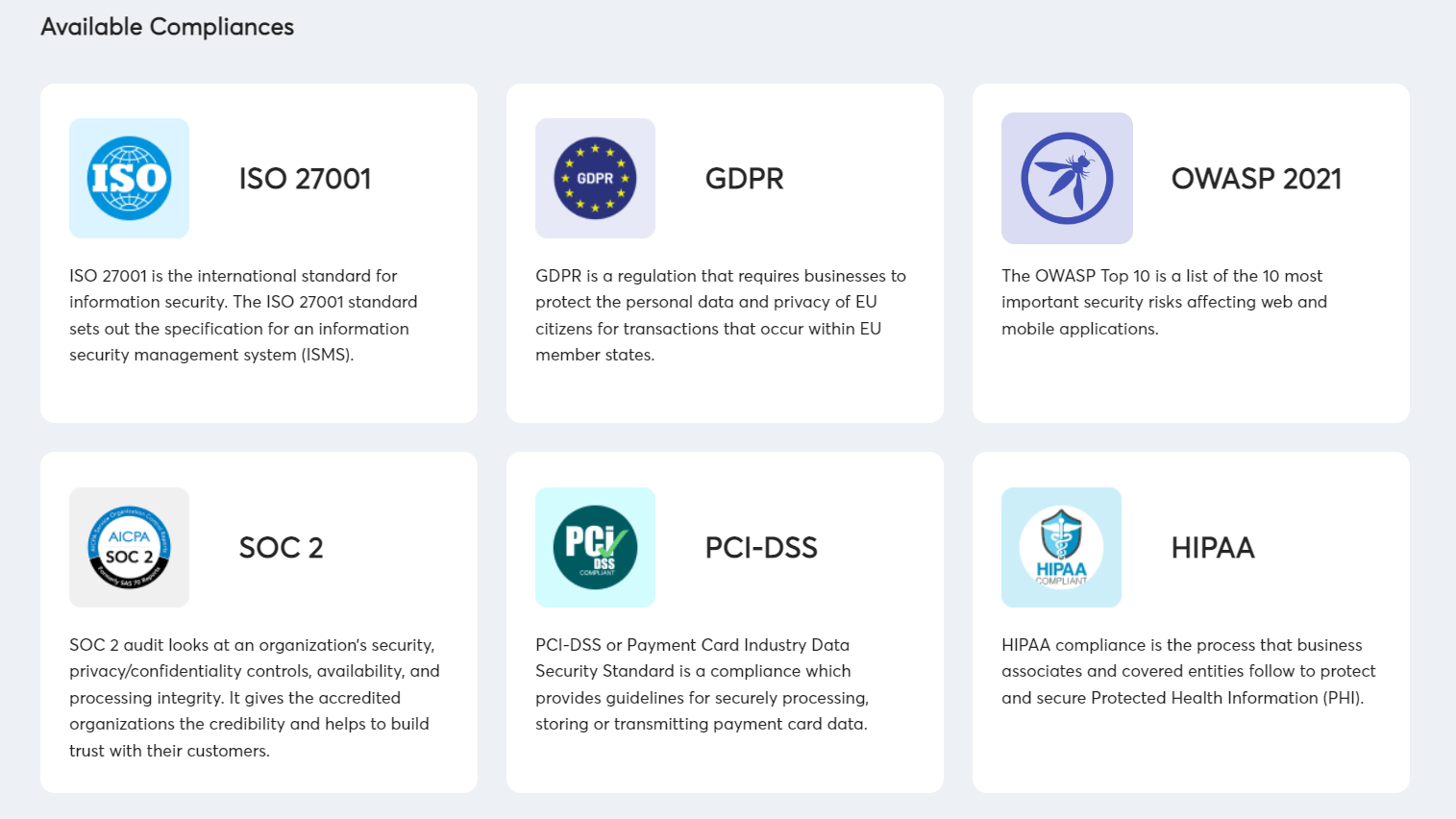
1. Compliance-Specific Scans
Astra provides compliance-specific scans with its own dashboard and personalized compliance reports. These are available for various regulatory standards, such as HIPAA, GDPR, PCI-DSS, SOC 2, and ISO 27001, and can scan for vulnerabilities such as Google OAuth Patient ID disclosed, XSS vulnerabilities, and more.
Customers can choose the compliance they want to scan for. Once the scans begin, vulnerabilities and areas of non-compliance are detected on the dashboard in real-time, with all the information regarding them and the steps to achieve that area of compliance.
2. Comprehensive Vulnerability Scanner
Astra’s automated scanner can conduct over 10,000 tests to find hidden vulnerabilities. It can also carry out scans behind logins and detect any business logic errors that may be affecting an organization’s revenue.
Such continuous pentesting capabilities can help detect vulnerabilities based on known CVEs, OWASP Top 10, and SANs 25, and are constantly updated to find newer vulnerabilities. It follows frameworks like NIST and OWASP to ensure smooth customer scans.
3. Penetration Testing Certificate
Astra goes a step further than all other pentesting providers by providing the customers with a pentest certificate upon completing a successful pentest, followed by the resolution of found vulnerabilities and a rescan to ensure no new vulnerabilities.
This publicly verifiable certificate can be put on one’s website to boost sales and promote a security-conscious approach.
Astra goes a step further compared to all other pentesting providers by providing the customers with a pentest certificate upon the completion of a successful pentest, followed by the resolution of found vulnerabilities, and lastly, a rescan to ensure that there are no new vulnerabilities.
This certificate is publicly verifiable and can be put on one’s website to boost sales and promote a security-conscious approach.
4. Detailed Report
Detailed reports given out by Astra are beneficial for organizations regarding remediation and documentation. It gives a detailed account of the scope, engagement rules, and methodologies.
Most importantly, it lists the vulnerabilities found, with a dedicated section explaining each vulnerability’s CVSS scores, actionable risk values to indicate which vulnerabilities are critical, information found through exploitation, its impact on the security system, and remediation measures to patch it.
5. 24*7 Customer Support
Astra boasts 24*7 customer support through email, chats, and even calls, if necessary, with the help of the expert pentesters on the team. The dashboard provides a comment option for each vulnerability for immediate doubt clearance.
It is one small security loophole v/s your entire website or web application.
Get your web app audited with
Astra’s Continuous Pentest Solution.

Final Thoughts
With compliance becoming a norm to adhere with drastic effects of non-compliance ranging from hefty fines to penalties and even criminal charges, it is no wonder compliance-based pentesting is gaining popularity.
HIPAA penetration testing is set to address and find areas of non-compliance within any healthcare organization, safeguarding it from threats and risks associated with vulnerabilities and non-compliance.
Astra’s Pentest is the one-stop destination for all your HIPAA penetration testing requirements with its compliance-specific scans, dashboard, and compliance reporting. Ensure the health of your organization today by teaming up with Astra!
FAQs
Is pentesting compulsory for HIPAA compliance?
According to HIPAA, organizations need to do risk analyses regularly to avoid and or identify and rectify any areas of non-compliance. This can be done with either penetration tests or vulnerability assessments.
What is the purpose of HIPAA?
The Health Insurance Portability and Accountability Act is designed to protect people covered by health insurance and also to secure their protected health information from any breaches and or theft.