Vulnerability assessments and penetration testing are often confused, but they serve fundamentally different roles in cybersecurity. A vulnerability assessment scans for and identifies known security weaknesses, offering a broad view of potential risks. Penetration testing, on the other hand, simulates real-world attacks by actively exploiting those weaknesses to reveal how deep an attacker could get.
Despite these differences, both are essential. Many security professionals, from CISOs setting strategy to hands-on testers, rely on them together to build a stronger, more resilient security posture.
What is Vulnerability Assessment?
A vulnerability assessment is a systematic process that identifies and quantifies security weaknesses (vulnerabilities) in an organization’s IT infrastructure. This includes networks, systems, applications, and cloud environments. By proactively uncovering these vulnerabilities, organizations can prioritize remediation efforts and reduce their risk of cyberattacks.
What is Penetration Testing?
Penetration testing is an authorized simulated cyberattack on a computer system, network, or web application to evaluate its security. Ethical hackers, also known as penetration testers, use the same techniques as hackers to identify and exploit vulnerabilities. This process helps organizations understand their security weaknesses and prioritize remediation efforts to strengthen their defenses against real-world attacks.
Recommended Reading: What is Pentest? A Complete Guide for 2025
Vulnerability Assessment vs Penetration Testing
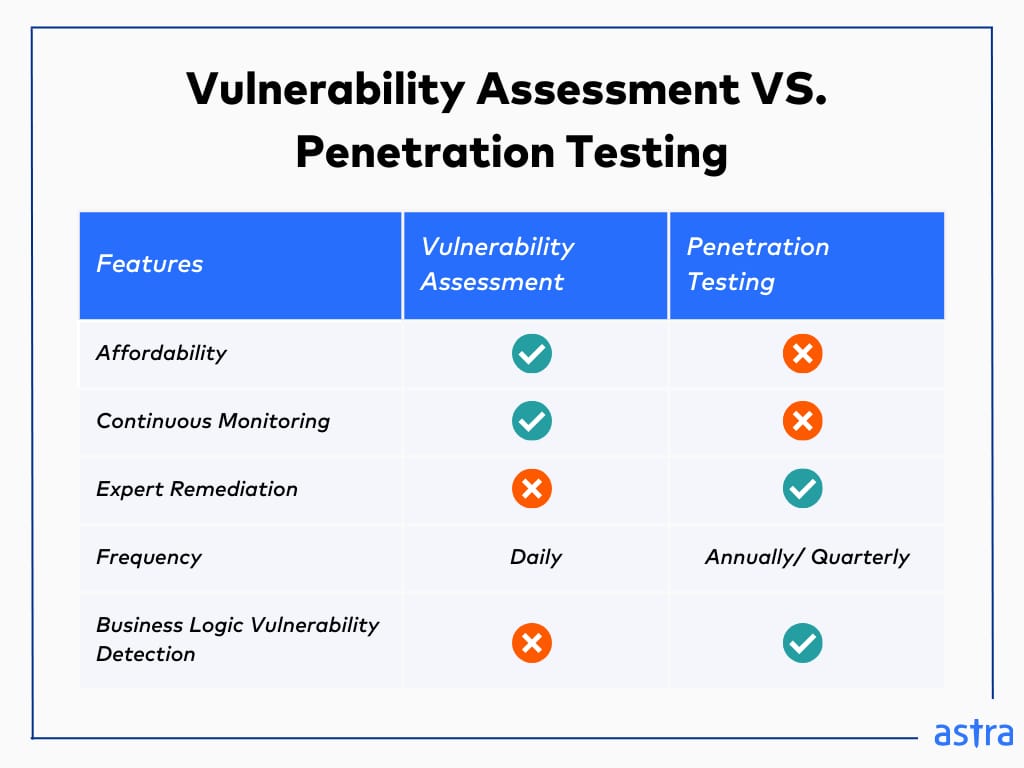
| Feature | Vulnerability Assessment (VA) | Penetration Testing |
|---|---|---|
| Focus | Identifies potential vulnerabilities and prioritizes them based on severity. | Attempts to exploit vulnerabilities to understand their actual impact and potential for compromise. |
| Usage of Tools | Heavily relies on automated vulnerability scanners | Primarily uses skilled security experts. Tools may be used for initial discovery or specific tasks. |
| Performed By | Largely automated by vulnerability scanning tools. | Conducted by experts with deep knowledge of hacking techniques and system security. |
| Depth | Offers a broad overview of potential weaknesses. | Provides a deeper understanding of exploitable vulnerabilities. |
| Automation | Highly automated, allowing for frequent and quick scans. | Limited automation. Requires manual intervention to analyze results, exploit vulnerabilities, and assess impact. |
| Frequency | Can be performed very frequently (daily or weekly) depending on risk tolerance. | Typically performed monthly, quarterly, or annually, depending on security needs. |
| Compliance | Can be used for continuous compliance monitoring | Mandatory for compliance pentests such as GDPR, HIPAA, ISO, CERT-IN, and SOX |
| Certification | Does not directly lead to a penetration testing certification. | Can be used to prepare for and demonstrate skills required for penetration testing certifications. |
| Outcome | Provides a report listing vulnerabilities and their severity levels. | Provides a report detailing exploited vulnerabilities, the attacker's path to compromise, and potential remediation strategies. |
| Cost | Lower cost due to automation. | Higher cost due to skilled personnel required. |
What is the Difference Between Vulnerability Assessment and Penetration Testing?
The main difference is that a vulnerability assessment is a broader security checkup in which automated tools scan your systems for known weaknesses, whereas penetration testing simulates an actual cyberattack. Both methods help you identify potential risks.
In pentesting, ethical hackers try to exploit those weaknesses, like a security expert testing your defenses. This shows you the real-world impact of those risks and helps you prioritize fixes accordingly. Essentially, vulnerability assessment finds the weaknesses, while penetration testing tests how those weaknesses could be exploited.
1. Speed of Execution
Automated vulnerability assessments streamline security by methodically scanning your systems, networks, or applications daily or weekly, depending on your needs. The scanner quickly checks your systems and code against known vulnerabilities, generating a report in as little as 10 minutes, though complex scans may take up to 72 hours.
Penetration testing, on the other hand, prioritizes depth over speed. With analysts manually exploring your systems, mimicking the tactics of real attackers, a pentest can take 15-20 days on average, depending on the scope and complexity of the target system.
Winner: Vulnerability Assessment
2. Intensity of Testing
Vulnerability scans offer a swift, high-level assessment, leveraging databases of known issues (CVEs) to identify common threats like outdated software or misconfigurations. However, they may overlook unique vulnerabilities in your system’s logic and generate false alarms.
Penetration testing goes a step ahead by exploring vulnerabilities and their potential impact, followed by remediation guidance. Thus, while it is more time-consuming and resource-intensive, it provides a clearer picture of your system’s accurate security testing.
Winner: Penetration Testing
3. Risk Analysis
In vulnerability assessment vs penetration testing, the former efficiently scans for vulnerabilities, categorizing them based on severity, ease of exploitation, prevalence (how common they are), and CVSS score (a standardized risk rating). This helps prioritize the most critical weaknesses by assigning a risk score.
The latter, i.e., pentesting, takes risk analysis a step further. It considers the same vulnerability factors from a vulnerability assessment but adds real-world context, such as likelihood and impact. Its human element helps identify CVEs that might be easily exploitable in your specific environment, even if they seem less severe on paper.
Winner: Penetration Testing
4. Reporting
Vulnerability assessments provide a technical inventory detailing assets analyzed and discovered CVEs, a technical breakdown of each bug for risk analysis with compliance implications, and step-by-step guidance for patching it.
Penetration testing reports, on the other hand, go beyond just listing vulnerabilities to paint a more narrative picture, including proof of concept, attack methodology, exploitation chain, impact assessment, and tailored remediation guidance.
Winner: Penetration Testing
Astra Pentest is built by the team of experts that helped secure Microsoft, Adobe, Facebook, and Buffer

5. Impact on Compliance
Regulations like PCI DSS and HIPAA require regular vulnerability scanning and fixing of critical issues. A documented process for assessing vulnerabilities and a plan to address them demonstrate your commitment to data safety and compliance.
While many compliances also mandate an annual pentest, successful pentests help you assess the effectiveness of your existing controls and strengthen your overall compliance posture.
Winner: A combination of vulnerability assessment and pentesting, depending on the compliance regulations.
6. Remediation Support
While reports show the problem and its impact, specific solutions under a vulnerability assessment vs. pentesting might require consulting vendors and security experts or exploiting databases for actions like patches, upgrades, or configuration changes.
On the other hand, in VA vs. PT, thanks to a human touch, a pentest delivers actionable reports with concrete fixes, such as software patching, system hardening, or implementing additional controls. A code as proof further simplifies the remediation process.
Winner: Penetration Testing
7. Pricing
Vulnerability assessments tend to be the more budget-friendly option. Depending on the scope, targets, frequency, and features, they range from $1,000 to $4,500 per year on average.
As you can imagine, the latter is a more in-depth and manual process in the vulnerability assessment vs penetration testing debate, leading to a higher price tag. The average cost can vary significantly, ranging from $5,000 to over $70,000 depending on the complexity of your systems, the depth of testing, and the experience of pentesters.
Winner: Vulnerability Assessment
8. Who is it Ideal for?
Automated and affordable vulnerability assessments are ideal for resource-conscious SMEs, evolving startups with frequent deployments, and continuous compliance environments.
Penetration testing, however, caters to more specific needs, including industries handling sensitive data, such as finance or healthcare, government PSUs, or firms with complex IT infrastructure and a security-first culture.
Winner: Penetration Testing (for being more customizable)

What Makes Astra the Best VAPT Solution?
- We’re the only company that combines automated & manual pentest to create a one-of-a-kind pentest platform.
- The Astra Vulnerability Scanner runs 10,000+ tests to uncover every single vulnerability
- Vetted scans ensure zero false positives.
- Our intelligent vulnerability scanner emulates hacker behavior & evolves with every pentest.
- Astra’s scanner helps you shift left by integrating with your CI/CD.
- Our platform helps you uncover, manage & fix vulnerabilities in one place.
- Trusted by the brands you trust like Agora, Spicejet, Muthoot, Dream11, etc.

How to Choose Between Vulnerability Scanning and Penetration Testing?
| Security Testing Method | Businesses It's Ideal For | Examples |
|---|---|---|
| Vulnerability Assessment (VA) | Resource-constrained SMEs and continuous compliance environments | Evolving startups with frequent deployments, |
| Penetration Testing (PT) | Organizations with sensitive data or firms with complex IT infrastructure and a security-first culture | Finance or Healthcare industries, Government PSUs |
| Vulnerability Assessment and Penetration Testing (VAPT) | Organizations seeking a comprehensive security posture; combines the benefits of VA and PT | Energy, E-commerce, SaaS and Tech companies |
Vulnerability assessments are like automated digital watchdogs. They’re cost-effective and can be performed frequently throughout the year, providing a continuous pulse on your security posture, especially for industries like finance, healthcare, E-commerce, and government agencies. This allows for early detection of potential weaknesses before attackers can exploit them.
However, vulnerability assessments have limitations, including false positives, missed business logic vulnerabilities, and zero days. Pentesting, on the other hand, simulates real-world attacks, attempting to exploit vulnerabilities and gain access to your systems.
Thus, it provides a much deeper understanding of your compliance posture, especially in critical infrastructure industries, power grids, communication networks, and other vital systems. The downside? Penetration testing requires skilled professionals and can potentially disrupt ongoing operations. As a result, it’s typically done less frequently than vulnerability assessments.
Hence, the final choice between vulnerability scanning vs penetration testing depends on your specific needs and resources. Ideally, a strong strategy utilizes both methods for a well-rounded defense.
What is VAPT?
This is where Vulnerability Assessment and Penetration Testing (VAPT) platforms step in. Instead of VA vs PT, it combines the strengths of both to deliver a more holistic evaluation. The process typically starts with a vulnerability assessment to identify potential weaknesses in your systems, followed by a pentest to exploit the above and assess their severity.
Such a comprehensive approach provides a better picture of your controls, the exploitability of CVEs, and the potential consequences of a breach. While VAPTs come at a higher cost than vulnerability assessments alone, they offer a more efficient use of resources than running separate assessments.
How Can Astra Help?
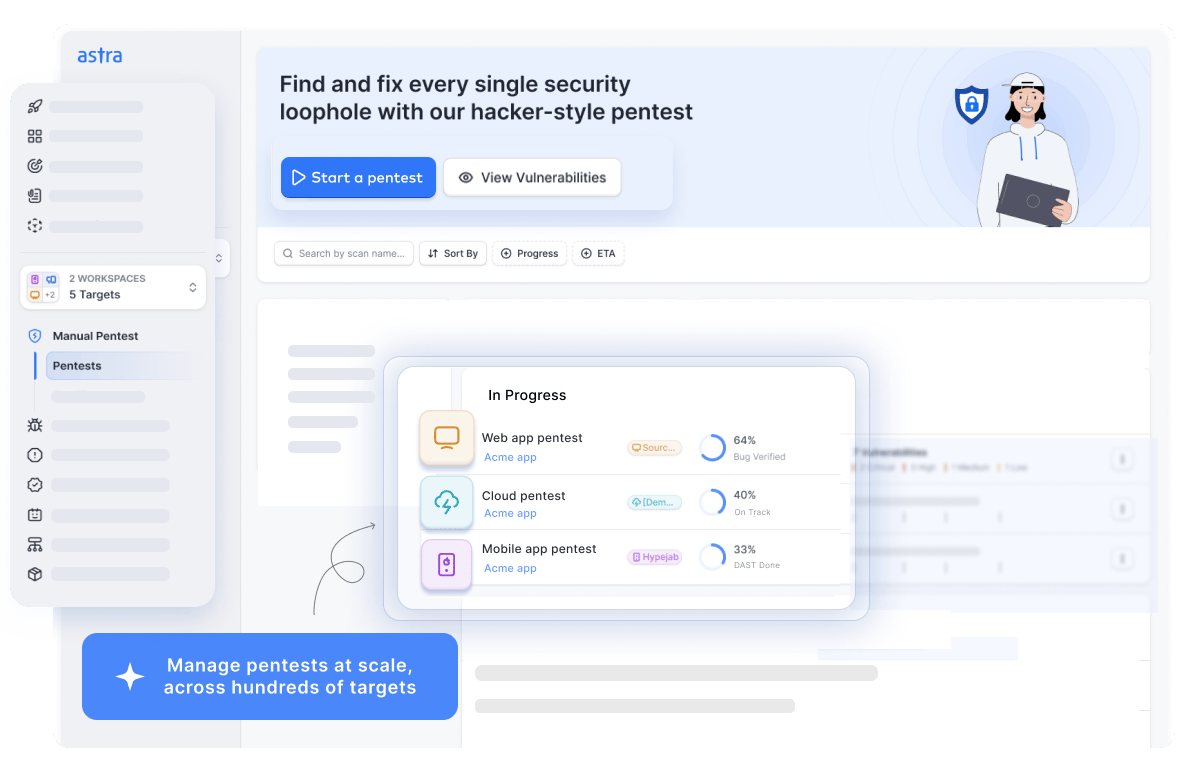
Astra is a comprehensive PTaaS platform that blends automation, AI, and manual penetration testing to offer an intelligent scanner with 9300+ test cases and holistic penetration testing service for your web apps, cloud infrastructure, mobile apps, APIs, and network devices.
Astra’s user-friendly dashboard provides seamless navigation and integrates with your existing CI/CD pipeline for effortless monitoring and compliance. Vetted scans ensure minimal false positives, giving you confidence in the results.
Moreover, our AI-powered test cases help generate unique attack vectors specific to your asset and industry, while the AI chatbot with 24/7 human support helps avoid bottlenecks. Still not convinced? Take a look at what our customers have to say!
Final Thoughts
Simply put, the choice between vulnerability testing and penetration testing boils down to the level of detail you need versus the resources you can dedicate. Automated VA scans offer a cost-effective way to continuously identify potential weaknesses across your systems, enabling early detection and prioritization based on severity.
Pentesting, on the other hand, involves skilled professionals who manually exploit discovered vulnerabilities, giving an exhaustive outlook of their true impact and potential for compromise. As such, it offers a superior understanding, and it’s naturally more expensive.
Thus, for a well-rounded security strategy, consider a VAPT approach like Astra’s. This approach empowers you to make informed decisions about where to prioritize security resources and ultimately strengthens your overall defensive posture.
FAQs
What is the difference between a risk assessment, a vulnerability assessment, and a penetration test?
Risk assessment prioritizes threats to your business. Vulnerability assessments find weaknesses in systems. Penetration tests exploit those weaknesses like real attackers to determine the impact and provide remediation guidance.
What are the three types of vulnerability assessments?
Although there are many types, the three primary types of vulnerability assessments include – Web scans that check websites for weaknesses, app scans that focus on software security, and network scans that identify security holes in your computer systems.
What is a penetration and vulnerability tester?
A pentester is a cybersecurity expert who acts like a hacker, ethically attacking systems to find weaknesses. They expose vulnerabilities and attack vectors before real attackers do.
Is vulnerability assessment also known as pentesting?
No, the vulnerability assessment and penetration testing differ. Whereas a vulnerability assessment gives an outline of the weaknesses within a system, penetration testing simulates actual attacks to exploit those vulnerabilities
Explore Our VAPT Series
This post is part of a series on VAPT. You can also check out other articles below.

- Chapter 1: What is VAPT?
- Chapter 2: A Complete Guide on Vulnerability Assessment Methodology
- Chapter 3: Vulnerability Assessment vs Penetration Testing: Difference?
- Chapter 4: Top 10 VAPT Companies In India for 2026
- Chapter 5: Top 10 VAPT Tools in 2026
- Chapter 6: Detailed Guide on VAPT Report
- Chapter 7: VAPT Pricing – How Much Does a Website VAPT Cost?
- Chapter 8: Vulnerability Assessment and Penetration Testing Services









What are the similarities between VA & PT?