Penetration testing on an application or network detects all security flaws, hidden vulnerabilities, and misconfiguration errors present in the system. This gives organizations an opportunity to fix these vulnerabilities before hackers can exploit them.
Organizations hire ethical hackers, professional pentesters, a penetration testing company to probe into their networks using real-life hacking techniques and pen-testing tools.
If you are one of those security-conscious organizations planning to get penetration testing done for your websites, web apps, mobile apps, cloud infrastructure, network devices, etc, then you have landed in the right place.
In today’s post, we are taking you on a tour of Astra Security’s Pentest Suite, which recently got updated with new features.
A little about Astra
Astra Security is a cybersecurity company committed to making security simpler for online businesses.
We offer a complete suite of security tools including a firewall, a malware Scanner, an IP & a Country blocker, to fight off coming attacks & malicious requests on a website or app.
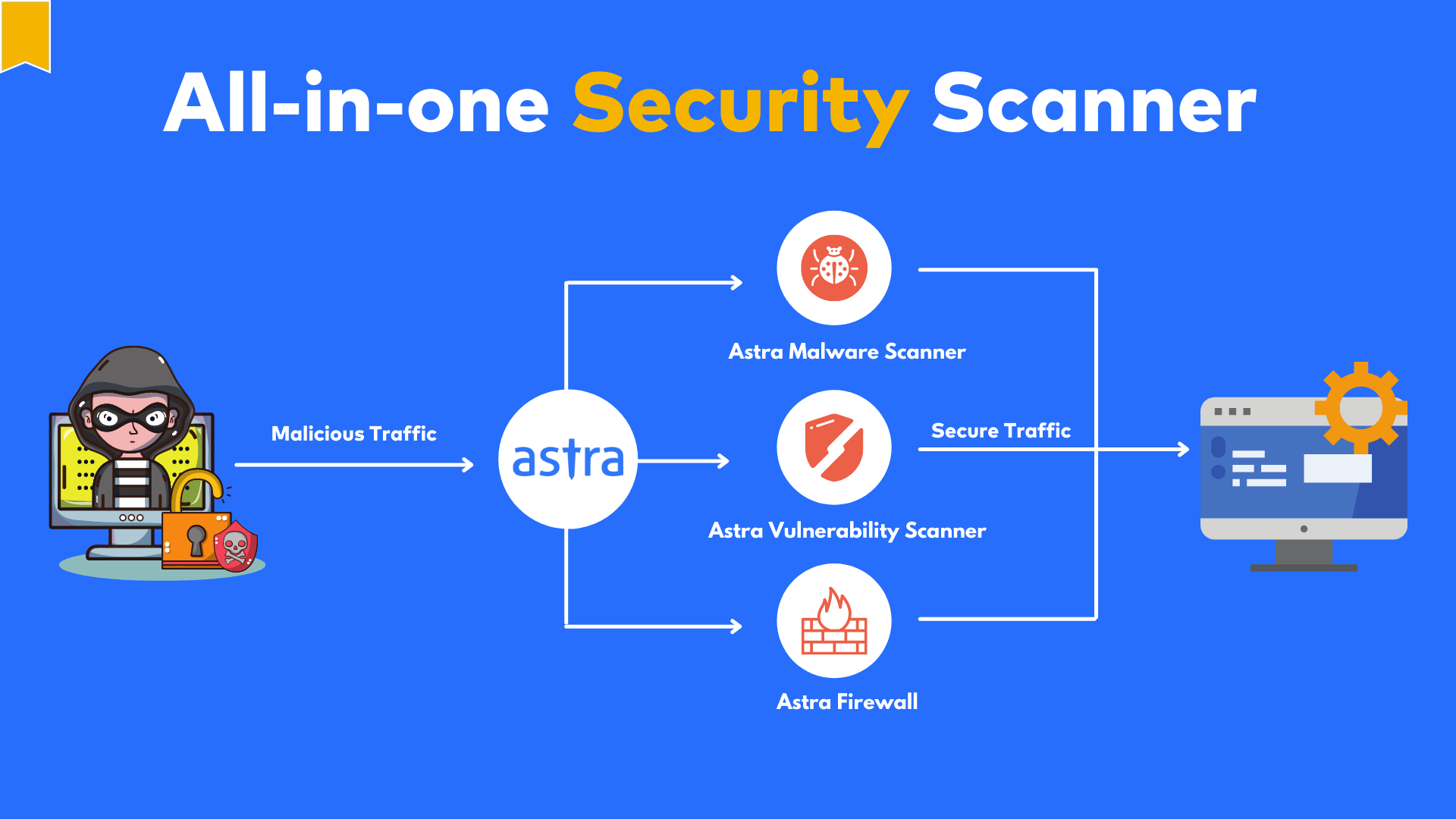
As one of the leading penetration testing companies, we also provide a complete pentest suite that helps companies find potential security flaws, vulnerabilities & loopholes in their system.
Our team of expert security professionals has helped thousands of businesses like Dream 11, Ford, Signalement, OOONA, Kotak Mahindra, and Indian Finance, identify & fix underlying security issues in their internet-facing software.
We’ll talk more about Astra’s Pentest Suite later on in the post.
Let’s understand what is penetration testing with this next segment.
What is Penetration Testing?
A penetration test or a pen-test is the process of simulating an attack on the targeted network or application to identify and exploit its weaknesses.
There are different approaches to these attacks, about which you can read in this guide – What, Why, and How of Penetration Testing.
After the test, the penetration testing provider prepares a detailed report of the vulnerabilities present in the target system along with recommendations for fixes.
There are four key steps involved in penetration testing. These are:
- Gathering information about the target website and scanning for vulnerabilities
- Exploiting discovered vulnerabilities
- Making a comprehensive report of the test
- Patching vulnerabilities and conducting a re-scan
In nutshell, penetration testing looks into your system and network from an attacker’s point of view and tries to break in via simulating near real-life hack scenarios. It also provides insights into the amount of damage your company can face if the security controls are breached.
Also Read: Continuous Penetration Testing: The Best Tool You’ll Find in 2022 | API Penetration Testing: What You Need To Know
Stay Secure With Astra Security’s Pentest Suite
As we discussed above, Astra’s pentest simplifies network and application protection for online organizations. We offer thorough VAPT (Vulnerability Assessment & Penetration Testing) with an efficient and time-saving reporting and fixing process. It is a one-stop penetration testing tool for all your needs.
Our security suite is easy to set up, and quite intuitive to use, which saves you time in little ways. You will not have to spend your valuable time scrolling, navigating & or comprehending yet another jargon-clad software.
You can, instead, immerse yourself in taking important business decisions and leave the security of your organization in good and trusted hands.
Also Read: Why Firewall Penetration Testing is Essential to Your Security Strategy
Whether you’re looking to pentest your web app, mobile app, APIs, network, or cloud, Astra Security is one place for you. Our offerings include but are not limited to:
- Web App Pentesting
- Mobile App Pentesting
- APIs Pentesting
- SaaS Platform Pentesting
- Blockchain Pentesting
- Cloud Infrastructure (AWS/Azure/GCP) Pentesting
- Network Infrastructure & Devices Pentesting
Our collaborative cloud dashboard can be used to receive reports about any discovered vulnerabilities. These reports include an assessment of the vulnerability’s impact along with a proposal for a technical solution.

Also Read: Top 5 Software Security Testing Tools in 2022 [Reviewed]
Best Penetration Testing Company – Why Choose Astra?
1. Standardized Security Testing by Experts
Unlike most penetration testing firms Astra Security provides you with a security solution tailored to your needs. Each penetration test follows OWASP, CREST, and NIST testing methodologies, tests for SANS 25 vulnerabilities, tests for PCI, GDPR & ISO compliance, business logic errors, and much more.
With over 8000+ tests you can rest assured that no vulnerabilities will remain hidden in your system.
Learn more about NIST Security Audit | Penetration Testing Quote
2. Transparent Process With Intuitive Dashboard
Stay in the loop with detailed vulnerability reports, and video proof of concept (POCs) through the dashboard. You can also add developers to collaborate with our security team. With live reporting of issues and easy communication, your developers will be able to fix the issues in no time.
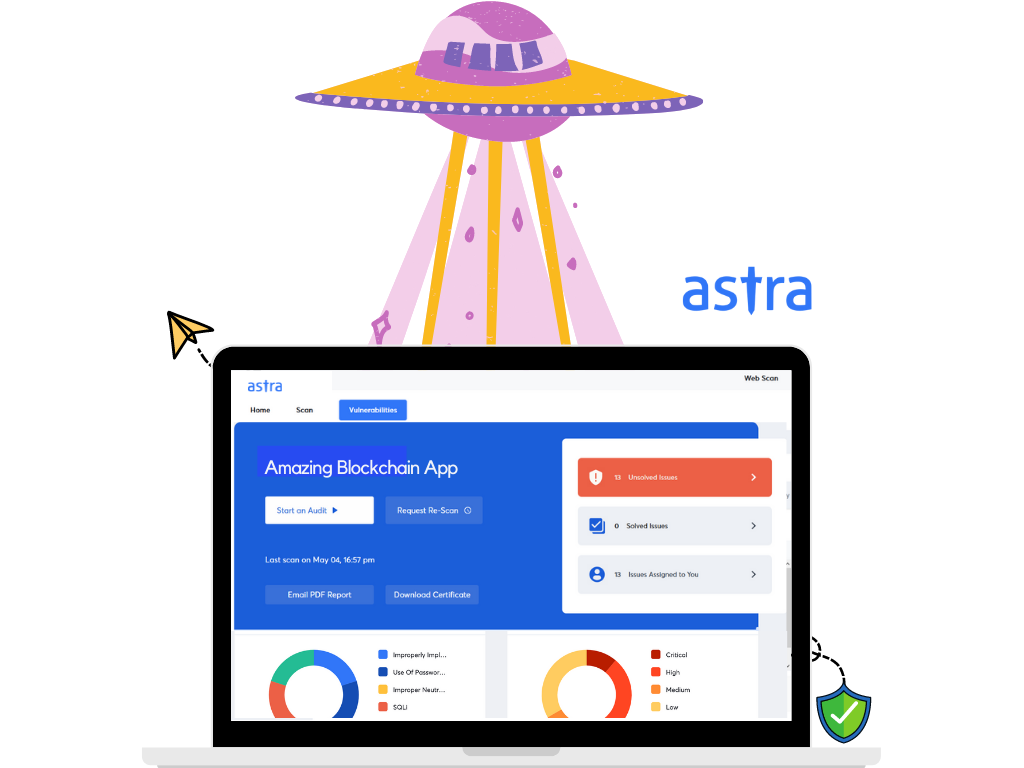
The new dashboard provides additional options:
Astra’s Pentest dashboard makes it an easy choice over other penetration testing services.
- Managing subscriptions is easier with the improved subscription page.
- A new “Issues Types” graphical representation.
- Easier to add new team members with the option in the main dashboard.
- Industry-standard PDF reports.
- More secure payment gateway – Paddle.
- A new “Help” option to talk directly to your assigned security engineer.
- One-click actions provide easier collaboration with the security team.
- Send vulnerability details directly by email to your team.
3. Patching Recommendations
In order to make your networks and applications fully secure, Astra as a reliable penetration testing company helps developers with the detailed steps for patching vulnerabilities.
Additionally, Astra Security gives round-the-clock technical assistance, best practices for the development stages of your application, and selenium scripts & video POCs of discovered security vulnerabilities.
We want to ensure that no single issue goes unchecked. Thus, after the patching of vulnerabilities, you can request a re-scan.
After a successful pentest, a certificate will be issued that will assure and acknowledge that your apps & networks are completely secured against any kind of vulnerability exploitation.
Additionally, our expert security engineers implement proactive security measures by anticipating attacks and recommending countermeasures.
4. Publicly Verifiable Certificates
You can download your security certificate from within the dashboard and make them publicly verifiable for your customers & clients to see.
Also Read: Choosing The Right Security Audit Company Made Easy | 10 Best Cyber Security Audit Companies [Features and Services Explained]

A VAPT certificate helps showcase to your clients and partners that your business is up to date with security compliances. Your customers will be at ease knowing that their data is secure. The fact that your pentest certificate comes from one of the top penetration testing companies adds a great value.
5. Friendly Team and 24×7 Human Support
Astra’s team is composed of highly skilled and qualified individuals. They have a wide educational background and hold the experience of conducting thousands of security audits over the years.
Moreover, the auditors are equipped with communication skills that aid them in collaborating with your team and helping them patch issues.
Communication is made easy within the dashboard. The developers from your team can comment under each vulnerability if they have any questions. Our engineers can also talk over chat if any issue demands so.
Our security auditors also hold industry-specific certifications such as:
- Bachelors in Information Security from Northumbria University, Singapore
- CEH – Certified Ethical Hacker
- Advanced Diploma in Information Security, MDI, Singapore
- Cyber Security Fundamentals from Kaspersky
- Policy Compliance Certification, Qualys
As you may see, not only is the Astra team developer-friendly but also provides the best professional security experience you could imagine.
Also Read: Top Penetration Testing Software & Tools in 2022
Customer Testimonials
“I am very satisfied with the result and the recommendations of the audit report. It was an eye-opener. We were able to optimize the security of the app to meet the expectations of our customers.”
Olivier Trupiano, Founder, and CEO of Signalement.
Signalement is a Paris-based whistleblowing platform that offers a multifunctional reporting platform. Olivier, Founder of Signalement, has been working with Astra security’s platform for over three years to keep his platform free from vulnerabilities.
Our other customers share their stories as well:
“There was a 100% reduction of hacked client sites since Astra has been integrated with Themecloud. Actually, the only hacked sites that we are facing now are because they were already hacked before we migrated to Astra or because they did not have Astra installed 🙂”
Laurent Vergnaud Founder, Themecloud.io
“We have felt so much safer since Astra has been integrated with Envent Technologies.”
Siddharth Sharma Co-Founder, Envent Tech.
FAQs
1. What questions should I ask my pentest service provider?
How quickly are the vulnerabilities reported? Does the Pentest report include a detailed remediation plan? What is the scope of collaboration between the security team and the developers? How many rescans are available? These are some questions you should ask. Find what an ideal Pentest report looks like here.
2. How much does penetration testing cost?
The cost for penetration testing ranges between $349 and $1499 per scan for websites. For SAAS or web applications it ranges between $700 and $4999 per scan, depending on your requirements.
3. Why choose Astra Pentesting service?
1250+ tests, adherence to global security standards, an intuitive dashboard with dynamic visualization of vulnerabilities and their severity, security audit with simultaneous remediation assistance, and multiple rescans, are the features that give Astra an edge over all competitors.
4. Do I also get rescans after a vulnerability is fixed?
Yes, you get 1-3 rescans based on the type of Pentesting and the plan you opt for. You can avail of these rescans within 30 days from the initial scan completion even after the vulnerabilities are fixed.
















