CVSS or Common Vulnerability Scoring System is a framework that numerically characterizes the severity of software vulnerabilities between the range of 0-10. CVSS scores help infosec organizations with vulnerability management and prioritization of vulnerabilities for efficient remediation.
This article will detail everything about CVSS from CVSS ratings to CVSS examples and metrics.
What is CVSS Score?
CVSS vulnerability score is a rating that indicates the severity of a vulnerability present in software or applications. A CVSS score is calculated based on certain metrics like base metrics, temporal metrics, and environmental metrics which have underlying score components that help calculate the score.
CVSS uses metrics to capture the principal characteristics of a vulnerability and quantify them to produce a numerical value that reflects the severity. This CVSS score range (0-10) can then be qualified into different categories i.e low, medium, high, and critical.
These calculated scores on CVSS scales and their qualifiers help companies assess and prioritize their remediation efforts in vulnerability management.
How Did CVSS Come About?
CVSS was initially established in 2005 by NIAC or National Infrastructure Advisory Council after much research between the years 2003 – 2004. The goal of CVSS was to be able to provide open and universally standardized metrics for software vulnerabilities.
By April 2005 the management and ownership of the framework were passed on to the Forum for Incident Response And Security Teams or FIRST.
CVSS SIG
FIRST sponsors and supports CVSS SIG (Special Interest Group) made up of multiple organizations that promote and refine the framework.
SIG includes representatives from various industries such as banking, finance technology and academia.
Their current initiatives include developing individual improvements to form the next CVSS version which is CVSS v4.0.
CVSS Versions
Common vulnerability scoring system version 1 was released in 2005 and was the initially established version. Later revised version, CVSS v2 was released in 2007. The revised version saw a significant improvement from its predecessor, had fewer inconsistencies, and provided more accuracy that reflected the characteristics of the CVSS vulnerabilities in IT.
A more advanced version CVSS v3 was released in June 2015 and this version came with changes to scoring that accurately pointed out the actuality of vulnerabilities that are detected in the software.
The latest version is CVSS 3.1 which will be discussed below.
FIRST CVSS Severity Levels Explained
According to FIRST, the CVSS database divides its severity levels into the following categories according to CVSS v3.
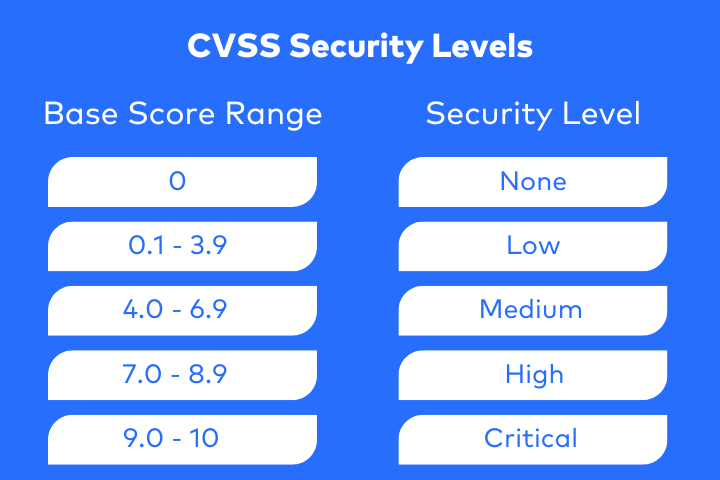
In the earlier versions, i.e. CVSS v2 the base score range was divided into the following:
| Base Score Range | Severity |
| 0 – 3.9 | Low |
| 4.0 – 6.9 | Medium |
| 7.0 – 10 | High |
Severity Levels Explained
CVSS base scores are divided into severity levels critical, high, medium, low, and none.
Critical
- Vulnerabilities in this range are highly compromisable resulting in root-level exposure.
- The attacker does not require any special measures or functions like authentication credentials or social engineering.
- These patches should be remediated as soon as possible upon discovery, i.e. within 2 weeks or at maximum within 3 months of discovery.
High
- These vulnerabilities are a bit more difficult, but not impossible to exploit.
- Exploiting generally results in escalated privileges and could result in data loss or downtime.
- Such vulnerabilities should be resolved within 4 weeks to 3 months of being identified and verified.
Medium
- Vulnerabilities belonging to this category need additional measures such as social engineering in order for them to be exploitable.
- Exploitation only provided limited access.
- Medium-level vulnerabilities should be resolved within 6 weeks to 3 months upon verification.
Low
- These are vulnerabilities that have little to no impact on the business or its security.
- Most exploitation of such vulnerabilities requires physical access.
- Low-level vulnerabilities have a larger resolution period ranging from 25 weeks to 180 from being verified.
CVE vs CVSS
CVE or Common Vulnerability Enumeration is a classification scheme for each IT vulnerability that is listed in the NIST (National Institute of Standards and Technology) National Vulnerability Database (NVD).
CVSS on the other hand refers is a framework that helps assign severity to each vulnerability based on different metrics.
CVE assigns unique identifiers to each vulnerability that is listed in the NVD. The identifiers are usually in the format:- CVE – (Year) – (Sequential Identifier), for example, CVE-2023-2138 or CVE-2022-42889 (Text4Shell)
CVE uses the CVSS framework for severity levels to provide an indication of severity for each CVE.
How Is The CVSS Score Calculated?
The CVSS score is assigned based on the various CVSS score metrics:
- Base Metric Group
- Temporal Metric Group
- Environmental Metric Group
Out of the three metric groups, Base metrics is calculated by NVD analysts and is the score that is published, whereas CVSS temporal scores and environmental scores are unique to each organization depending on how the vulnerability manifests in their cyber environment.
CVSS Base Metrics
Base metrics refer to the characteristics of the vulnerability itself. They are not dependent on time or on their exploitability level in the real world. These are the scores that are put forth by NIST’s NVD for public severity rankings.
Base metrics for CVSS are subdivided into three categories, exploitability, scope, and impact.
Exploitability
Exploitability refers to the characteristics of the vulnerability that is further divided into
- Attack Vector
This score is assigned based on the level of access required to exploit the vulnerable component. It’s higher for exploits that can be executed remotely and lower for ones that need physical access.
- Complexity of Attack
The attack complexity score is assigned based on factors that aren’t under the control of the attacker. Here higher scores are given to vulnerabilities that require an investment of a measurable amount of time and effort from the attacker’s end in order to execute a successful attack based on the vulnerability.
- Privileges Required
This score varies based on the privileges required by the attacker to successfully exploit the vulnerability. Vulnerabilities that require higher administrative privileges are given higher scores than vulnerabilities that require no authentication.
- User Interaction
The score here is assigned based on whether the attacker requires a willing on unwilling participant in order to complete their task. Scores are higher if the task can be executed alone and lower if it requires participation.
Scope
This CVSS metric captures the effect of a vulnerability in one component affecting other components. The score is higher if such propagation is possible.
A prime example of this is when an attacker can access the backend database after a successful exploit of a vulnerability in a web server.
Essentially, the security scope of a part includes all other parts that provide the functionality to the original part too if the other parts have their own security authority.
Impact
This is the sub-section of base metrics that actually focuses on the outcome of an attack that occurs through the exploiting of the vulnerability to be scored. Three sub-metrics under impact are
- Confidentiality
This score varied based on the availability of data post-exploit. It is higher if data is accessible and lower if not.
- Integrity
Here the score will be high if, upon the exploitation of the vulnerability, consequential and severe modifications are possible.
- Availability
Here vulnerabilities have a higher score if systems are unavailable or unusable to authorized users post-attack.
CVSS Temporal Metrics
Temporal metrics relate to the relationship between vulnerability and time. These metrics measure the changes in vulnerability over time including its current level of exploitability, and availability of remediation measures.
It is further categorized into three:
- Remediation Level
Upon the initial discovery of a vulnerability, it may not have any remediation measures such as patches available. Over time, however, shields, temporary fixes, and more are developed thus reducing the score.
- Exploit Code Maturity
A vulnerability is considered benign until a code is developed to exploit it. Over time the exploit becomes more stable and widely available increasing the severity score.
- Report Confidence
This measures the level of validation a vulnerability requires to prove its existence and exploitability.
CVSS Environmental Metrics
These are metrics that are calculated by organizations and are unique to each company’s IT space. It modifies the base metrics and security requirements to be more applicable to their cyber environment.
- Security Requirements
This metric essentially assesses the criticality of the asset in question. Critical data gets a higher score than other less important assets.
- Modified Base Metrics
Base CVSS metrics can be modified based on the mitigatory measures already put in place by the organization, this in turn would reduce the score.
How Does CVSS Help in Security Strategy?
CVSS score guide provides accurate information on the characteristics of vulnerability numerically and categorically. This aids organizations all across the globe to prioritize the vulnerabilities found in their IT environments based on the base metrics which gives a general idea of the severity of the vulnerabilities.
Companies can also calculate other CVSS scores using the free CVSS calculators, such as the temporal and environmental scores that are specific to their IT environment and how the vulnerability is affecting it. These measures together help make vulnerability management an easy and hassle-free process.
The CVSS framework can also help potential targets to take an active step to secure their assets by employing vulnerability scanning or assessment.
Latest CVSS Version 3.1
In June 2019, a minor update was made to the pre-existing version CVSS v3.0 and was released as CVSS v3.1. The aim of CVSS version 3.1 was to clarify and improve the previous version by allowing frictionless adoption of the new standard by both scoring analysts and users alike.
Some of the concepts introduced in version 3.0 were also clarified to improve the overall ease of using the standard. Updates to version 3.0 include clarifications of definitions to existing base metrics and security requirements.
A new standard, an extension of CVSS, CVSS Extensions Framework was defined to include additional metrics while retaining the official metrics. The additional metrics allow various industries like healthcare, finance, privacy, and automotive, to score for factors outside of CVSS.
National Vulnerability Database Information On CVSS Rating
NVD put out specific information about vulnerabilities that are being assessed for their CVSS ratings.
Incomplete Data
Not all vulnerabilities have all the required information to create CVSS scores. This happens when a vulnerability is announced by a vendor but vulnerability details are withheld. When such information is unavailable NVD analysts assign a score of 10 (critical) considering it a worst-case scenario.
Industry Collaboration
NVD is open to working together with the security community with regard to CVSS impact scoring. Additional information or corrections can be put forth about CVSS impact scores can be put across via mail.
Legacy CVSS Information
Since 2022, NVD does not provide severity ratings or scores for CVSS v2 while keeping the existing CVSS database intact. This database is no longer actively updated for new CVEs.
All new and reviewed CVEs are assessed based on the current CVSS version, i.e. CVSS v3.1.
Limitation of CVSS
CVSS only publishes base scores, i.e. it indicates the threat posed by a vulnerability in general. However, it does not provide any information on how the vulnerability could pose a risk to one’s organization in specific.
A CVSS calculator is required to assess the temporal and environmental scores for a vulnerability according to an organization’s specific IT environment. FIRST and NIST provide free CVSS calculators for the same.
Conclusion
CVSS is a framework that aids in providing quantifiers and qualifiers to a particular CVE that indicates its severity level. This helps organizations to effectively patch vulnerabilities and have a steady vulnerability management system in place.
This article has discussed all aspects of the CVSS scoring system, from its history, to how the base score values are calculated and the latest version of CVSS, i.e. CVSS v3.1.
FAQs
Difference between CVSS v2 and CVSS v3?
CVSS v3 was released in June 2015 and this version came with changes to scoring that accurately pointed out the actuality of vulnerabilities that are detected in the software.