Article Summary
This article details what cloud vulnerability management is, the common vulnerabilities found by it, the steps in managing cloud vulnerabilities, and the best practices that help it. It also explains the features of the best cloud vulnerability management solution.
Cloud vulnerability management refers to the continuous process of identifying, reporting, and remediating security risks found within the cloud platform. It becomes vital that good cloud security measures with an extensive cloud vulnerability management system be placed to ensure data and application safety.
Introduction
Major and upcoming companies, even small businesses of today have largely migrated to make use of the cloud platforms available. This enables such businesses to worry less about secure physical data storage facilities as it is all in the cloud servers.
However, it is to be noted while the advent of the cloud has revolutionized storage and working efficiency, it too is not without risks. These come in the form of unwanted malicious attacks through which hackers try to breach the cloud and obtain sensitive information.
This article will talk about the further aspects of cloud vulnerability management including cloud-based vulnerabilities, features, steps taken in cloud vulnerability management, and the best cloud vulnerability management practices.
Common Cloud-Based Vulnerabilities
Before checking out the features of a good cloud vulnerability management system and everything associated with it, it is important to understand the type of cloud-based vulnerabilities that need to be identified, addressed, and managed on a regular basis to avoid any serious breaches or other issues that may arise from them.
The most common cloud-based vulnerabilities include:
1. Misconfigurations
Misconfigurations are one of the major reasons that lead to big data breaches in cloud platforms. Misconfigurations refer to any glitches or gaps in the security measures adopted that can lead to leaving valuable information virtually unprotected.
These misconfigurations can generally include a lack of proper access management, and even security group misconfigurations. Not having proper access restrictions in place can lead to individuals gaining access to unauthorized sections of data and applications thus putting the entire system in danger.
Security group misconfigurations refer to the glitches or vulnerabilities in the security system in place for the cloud platform, by the service providers, such misconfigurations can lead to getting direct access to the cloud platform and result in heavy data theft and or loss.
2. Data Loss or Theft
A major attraction and risk of cloud platforms are the effortless storage requirements that attract customers to depend on the cloud rather than physically present servers. Since the transmission and storage of data are off-premises and in a cloud environment, it leaves it open to a whole host of cyberattacks that can jeopardize the data and applications within the cloud servers.
This can even include their IP which is a major share of data stored. Some of the reasons why data loss takes place are data deletion, lack of access, and data altering. Data deletion and alteration can lead to major chunks of important data being lost or changed which can severely impact an organization’s operations.
3. Non-Compliance
Every sector and the companies that work within them have certain industry-specific standards and regulations that they strictly need to have adhered to. This is called compliance. Certain important compliance standards include PCI-DSS, HIPAA, ISO 27001, SOC 2, and more.
They mainly deal with data protection and also assess the steps taken by each company to adhere to and keep up with the regulations listed. Doing so ensures that the organization is rock-solid in terms of maintaining security, all the access controls and restrictions implemented are functional and proper as well as ensure data security.
It is to be noted that maintaining cloud security does not fall on the providers alone. This is known as the shared responsibility model where the cloud security is maintained by the provider but the data security can and should be maintained by the customers.
4. Weak Access Management
This is one of the most common risks to data security posed in the cloud. Improper or weak access restrictions mean that unauthorized personnel can access data that they aren’t authorized to do.
Establishing proper access controls means that only authorized individuals can access certain data, documents, and applications. The process of vetting out the individuals who should be allowed access and who shouldn’t is known as authorization.
Not having role-based access management, disabling access to inactive users or former employees, and having multiple sign-in accounts can all lead to a safety risk in terms of proper access management.
5. Vulnerable APIs
Initially, APIs were given less attention in terms of security. However, with attackers focusing on APIs to gain access to valuable information, security for APIs had to be upgraded accordingly.
In the case of cloud computing, APIs help streamline the data present for both it and the applications within it. Insecure APIs pose a threat by opening channels of communication that can lead to them getting exploited.
Insufficient authentication and authorization measures to restrict access to APIs are seen to be one of the most common causes that make APIs an extremely vulnerable region prone to getting attacked. This leaves the APIs open to the reach of anyone on the web who can then use them to gain access to sensitive information.
Also Read: A Complete Guide to Cloud Penetration Testing
Features That Make Cloud Vulnerability Management Important
Features of cloud vulnerability management make it imperative to have the system in place and on the checklist of cloud security to ensure a well-protected cloud service that maintains its reputation and more importantly, safety.
Here are some of the features that make cloud vulnerability management important:
1. Better Security
The steps are taken through cloud vulnerability management to ensure better security for the cloud platform, the applications that make use of it, and the data that is stored and transmitted by them.
Vulnerability management enables the constant monitoring of your applications and data thereby providing 24*7 protection and identification of vulnerabilities that can then be remediated immediately.
2. Cost-Effective
Having an efficient system in place for cloud vulnerability management means the platform and data stored within it are under constant monitoring to detect any new vulnerabilities in time.
This quick detection and remediation of flaws mean that the amount spent on fixing the vulnerabilities and dealing with the blowout from the exploitation of these vulnerabilities will be significantly reduced.
3. Highly Preventative
Vulnerability management can help organizations successfully prevent a multitude of attacks directed at their sensitive data and applications owing to the 24*7 detection, assessment, and remediation of flaws.
4. Time-Saving
If an application and the data stored in the cloud aren’t continuously monitored it can lead to disastrous attempts to gain access to said data. This can cost the organization to spend valuable time fixing the after-effects of the exploitation of such vulnerabilities rather than the vulnerabilities themselves. This is where having the best cloud security companies with vulnerability management help save time and a lot of manpower.
Steps In Cloud Vulnerability Management

Cloud vulnerability management refers to the constant vigilance provided to the cloud environment for the timely detection and remediation of any vulnerabilities.
This is done through the following steps:
1. Identification Of Flaws
This is the initial step taken in well-implemented cloud-based vulnerability management. It involves the identification of vulnerabilities within the system using comprehensive vulnerability scanners capable of detecting a wide range of vulnerabilities.
In general, it should be able to detect the known CVEs, and vulnerabilities mentioned in standard frameworks like the OWASP Top 10 and SANS 25 as well as based on the current trends in malicious exploitation.
The process results in mapping out your assets in detail and scouring them for any possible vulnerabilities that could construe a threat to the cloud platform. It is vital to schedule such scans during slower traffic times as it can cause disruptions in regular operational conditions.
Also Read: Top 5 Cloud Vulnerability Scanners
2. Risk Assessment
Once the vulnerabilities identified are matched to the vulnerability database at hand, they are assessed further to understand the extent of their threat levels. Another reason for this evaluation of identified threats is to prioritize them according to the mentioned risk levels posed by each vulnerability.
This allows a team to understand which of the vulnerabilities need to be fixed immediately and make a diligent plan in lieu of it.
The most common system used to identify the extent of threats posed and prioritize them is the CVSS system. CVSS stands for Common Vulnerability Scoring System, it assesses the vulnerabilities according to a few set characteristics like their traits and specific effects on the cloud. Based on the scores, the vulnerabilities are patched.
Also Read: 10-Point Vulnerability Assessment Checklist
3. Remediation of Vulnerabilities
Once the vulnerabilities are assessed according to the risk they pose, it is now time to respond and fix each flaw found. This is done based on the data from the risk assessment.
Based on the threat level there are three general measures that can be opted for to create a viable and healthy security solution for the cloud. This includes:
- Patching: This refers to fixing the highest risk posing vulnerabilities immediately based on their risk severity. The vulnerabilities are patched or fixed and the issue is completely eradicated.
- Mitigation: If fixing the problem at hand isn’t a feasible solution at the time, then the next step is to try and reduce the risk or problem posed by them to the security of the cloud. This in turn reduces the chances of them being found and exploited.
- No Action: This refers to taking no action against some found vulnerabilities. Such flaws always have an extremely low CVSS score and the pros of exploiting them are vastly outweighed by the cons. Therefore leaving these vulnerabilities alone and focusing on the more attention-demanding flaws is recommended.
4. Vulnerability Assessment Report
Once the risk assessment is carried out and the flaws are patched, mitigated, or left as such, a detailed vulnerability assessment report is generated by the cloud-based vulnerability scanner employed.
This report details the details of the scan, the methods employed to detect vulnerabilities, and the vulnerability database used as a standard reference. Along with this, the vulnerabilities found are listed and extensively explained with their CVSS scores as well as possible remediation measures.
Also Read: 10 Best Cyber Security Audit Companies [Features and Services Explained]
5. Re-Scanning
Once the major steps of identification, assessment, and remediation are carried out followed by the report generation. The final step would be to avail a re-scan to ensure the cloud platform is safe from all the initially found flaws and they have been appropriately managed or fixed.
Doing so is akin to going the extra mile in the name of safety and truly ensures the safety of your cloud service. It also increases your reputation as a safety-conscious provider and increases trustworthiness.
Best Cloud Vulnerability Management Practices
Cloud vulnerability management can be made perfect by opting for practices that give maximum security to the sensitive information stored within it. These cloud vulnerability best practices include:
- Comprehensive Vulnerability Scanning
Making use of a comprehensive vulnerability scanner help greatly with cloud-based vulnerability management. Such a scanner should be able to continuously scan and detect even the most minute of vulnerabilities.
It should also have an extensive vulnerability database so that all vulnerabilities are rightly assessed. A good scanner should also be able to carry out behind-the-login scans, detect logic errors, weed out any false positives as well as ensure that are no false negatives.
- Ensure Integration
Integrating vulnerability scanning into the development allows for continuous scanning for vulnerabilities throughout the progress of the application.
Such integration also allows for cloud service providers to be continuously compliant with the important regulatory standards they need to abide by like GDPR, ISO 27001, HIPAA, and PCI-DSS.
- Regular Pentests
Conducting regular pentests is an excellent practice for the best cloud vulnerability management. They go a step further from vulnerability scanning by exploiting the found vulnerabilities to properly assess the extent of damage that could occur from such an attack in real-life.
Regular pentests and scans are often considered mandatory during compliance audits since they help organizations identify and fix loopholes that need to be resolved.
- Vulnerability Prioritization
Vulnerability prioritizations are a good practice to follow since it helps you narrow down the vulnerabilities that pose the maximum threat and need immediate fixing from others which can only be mitigated or left as such due to their low risk.
CVSS (Common Vulnerability Scoring System) is one such popular system that allows vulnerability prioritization.
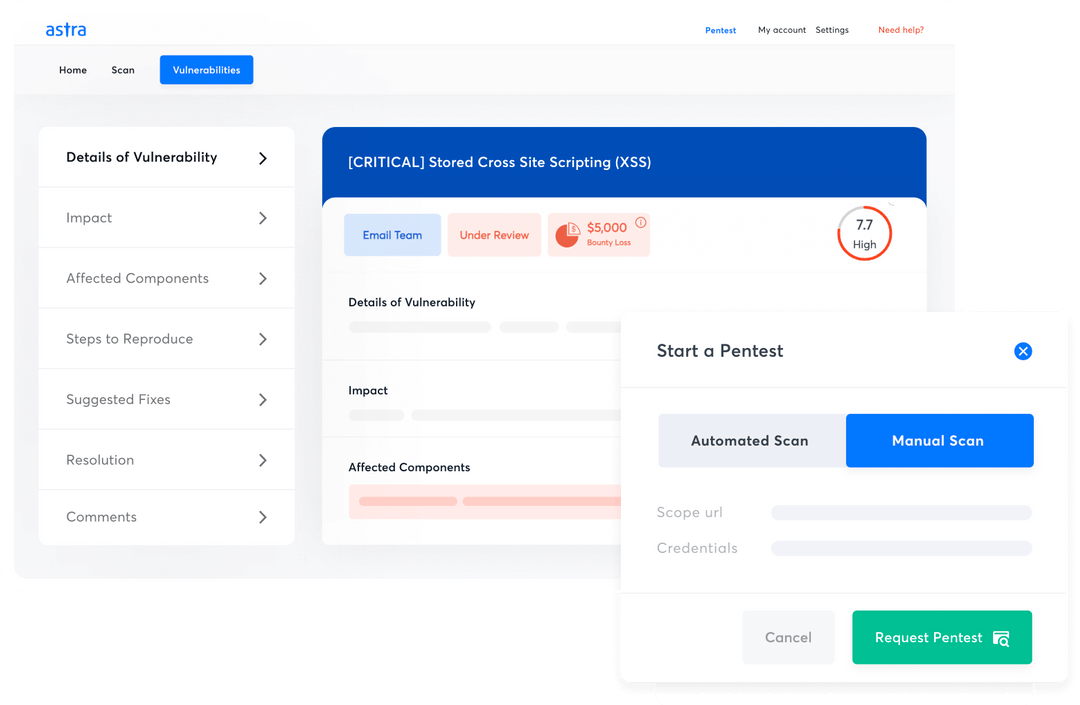
Astra Security: The Perfect Solution
Astra Security’s constantly evolving comprehensive vulnerability scanner is perfect to meet one’s cloud vulnerability management requirements. Its features include:
- Carries out more than 3000 tests to detect vulnerabilities.
- Benchmark your cloud security against NIST, OWASP, and CIS standards.
- Aids with vulnerability management and are CXO-friendly.
- Achieve and maintain compliance with all the major security regulations and laws like SOC 2, ISO 27001, GDPR, HIPAA, and PCI-DSS.
- Gap Analysis to find gaps in areas of security and performance.
- Rescans are provided upon patching of vulnerabilities to ensure safety.
- Prioritization of vulnerability fixing based on CVSS and ROI.
- Seamless collaboration with development team members and CXO to discuss and fix issues.
- Detailed report with actionable recommendations and POC videos to help with patching.
- Checks for business logic errors and gaps in security.
- Zero false positive assurance through thorough vetting of vulnerabilities listed.
- Customers are provided with a publicly verifiable certificate upon completion of vulnerability remediation and rescanning.
Bottom Line
This article detailed what exactly cloud vulnerability management is, the risks associated with not having a good vulnerability management system in place, and the attributes that make it a valuable asset to one’s security practices. All the problems of today and tomorrow can be faced and found by a good cloud-based vulnerability scanner when it is deployed.
Astra Security’s vulnerability scanner is one such tool that can meet all your needs and requirements. It employs the best features of a good vulnerability management system thus ensuring the safety of your cloud service, the applications, and the data within.
FAQs
How do you mitigate vulnerabilities in the cloud?
Vulnerabilities within the cloud can be mitigated by practicing the best cloud vulnerability management practices like employing continuous comprehensive scanning and pentesting, and through the integration of VAPT in the CI/CD pipelines.
What are cloud vulnerabilities?
The most common vulnerabilities that plague cloud services are misconfiguration, data loss or theft, non-compliance, vulnerable access management, and APIs.
What are the 4 types of vulnerabilities seen in cybersecurity?
The 4 types of vulnerabilities commonly seen in cybersecurity are:
1. Human Error Vulnerabilities
2. Network Vulnerabilities
3. Procedural Vulnerabilities
4. Operating System Vulnerabilities
















