Cloud environments have redefined the attack surface and, with them, the role of penetration testing.
80% of organizations have experienced at least one cloud security breach in the past year, with an average of 43 misconfigurations per account.
What used to be a matter of scanning ports and identifying known exploits is now about understanding complex trust relationships, misconfigured identities, and services that rarely behave consistently.
This guide breaks down how to approach cloud penetration testing with the depth and precision modern infrastructure demands.
Standard vs. Cloud Penetration Testing
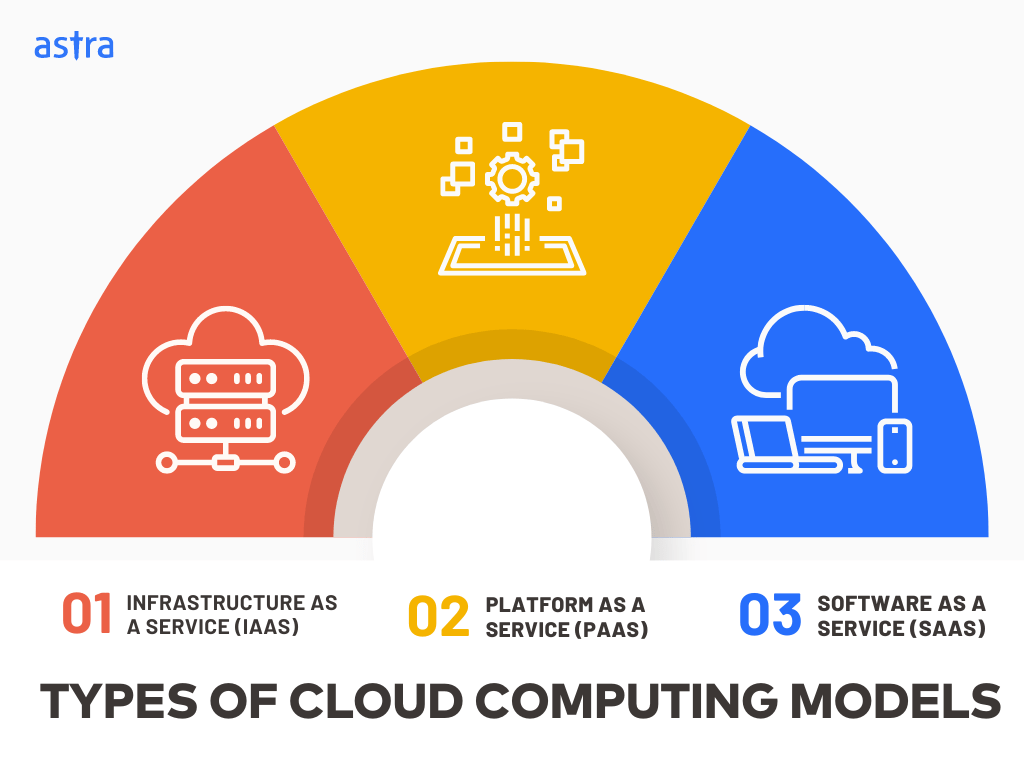
Building on these challenges, cloud penetration testing takes a fundamentally different approach. Unlike traditional pentests that assume a fixed, on-premises infrastructure, cloud pentesting adapts to the cloud’s dynamic, API-driven nature and shared-responsibility model. It focuses specifically on testing what you control within your IaaS, PaaS, or SaaS stacks.
The distinctions between cloud and traditional penetration testing come down to several key factors:
| Aspect | Cloud Penetration Testing | Standard Penetration Testing |
|---|---|---|
| Scope | Tests ephemeral assets like EC2 instances, Lambda functions, Kubernetes pods, and managed services that spin up/down dynamically | Targets relatively static servers, networks, and physical infra with predictable assets |
| Multi-Environment | Spans multiple accounts, regions, and providers (AWS, Azure, GCP) with cross-cloud attack paths and trust relationships | Typically confined to a single data center or unified network perimeter |
| Identity & Authorization | Focuses heavily on IAM roles, policies, temporary tokens (AWS STS), federated identity (OAuth/OpenID Connect), and role-based access | Primarily tests network access controls, firewalls, and traditional authentication mechanisms |
| Infrastructure Boundaries | Operates within a shared responsibility model. Tests only tenant-owned configs while respecting provider-managed infra | Assumes full control over entire infrastructure stack from hardware to application |
| Elasticity & Ephemerality | Must account for auto-scaling, containers, and serverless functions that exist temporarily; vulnerabilities appear and disappear during testing | Tests persistent infrastructure where assets remain stable throughout engagement |
| Infrastructure-as-Code | Audits Terraform templates, CloudFormation, CI/CD pipelines, and provisioning APIs as part of attack surface | Focuses on running systems and deployed configurations rather than deployment automation |
| Logging & Monitoring | Validates that CloudTrail, CloudWatch, Azure Monitor capture events from ephemeral workloads and serverless triggers | Tests local system logs and traditional SIEM integration on persistent infrastructure |
| Vendor Dependencies | Accounts for shared risk from managed services, container registries, and DBaaS vulnerabilities that affect multiple tenants | Vendor risk limited to software/hardware procurement and full control over implementation |
Top Cloud Security Issues to Watch

Cloud Penetration Testing Methodology
Here is the methodology to assess cloud security, from mapping assets and reviewing configurations to exploiting vulnerabilities, reporting risks, and verifying fixes. This stepwise process ensures cloud environments are tested against real-world attack scenarios across AWS, GCP, and Azure.
Step 1: Inventory Mapping
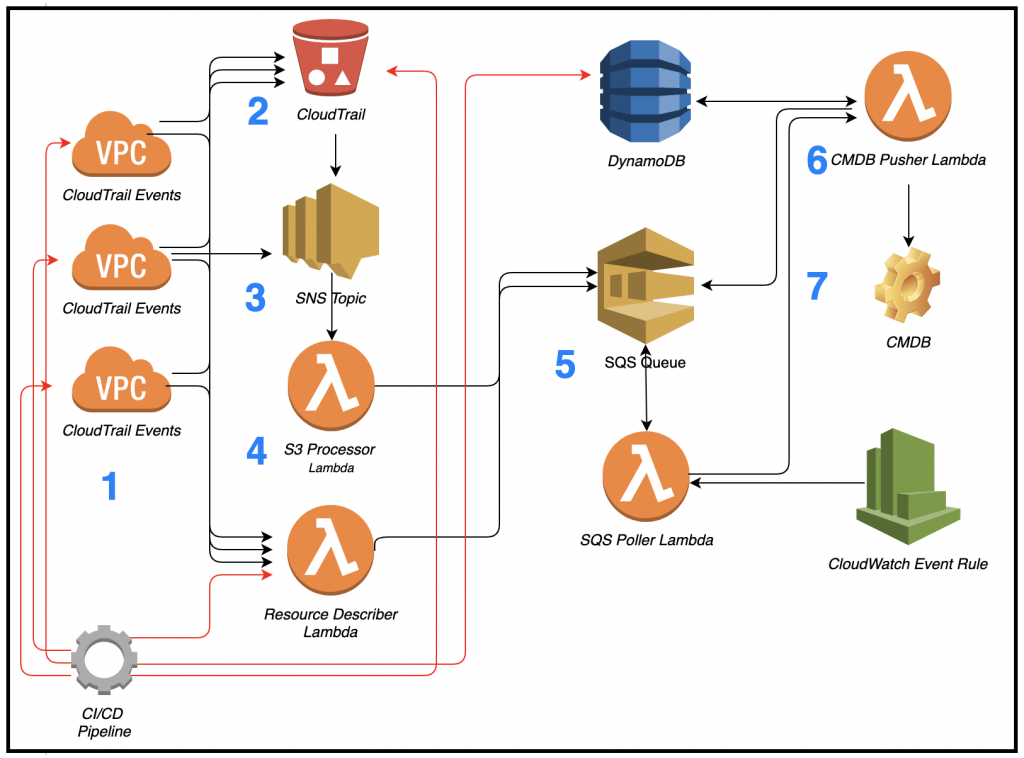
The initial crucial step for a cloud penetration test is Inventory Mapping. It means identifying and inventorying all the cloud-based assets in a target environment. You identify the complete attack surface, ensuring no crucial component is missed during testing.
Begin by using reconnaissance tools to discover exposed services and assets. For AWS, leverage the AWS CLI combined with commands like aws ec2 describe-instances to enumerate EC2 instances, or aws s3 ls to list S3 buckets.
Tools like Nmap can scan for open ports (e.g., nmap -sS -p- ), while Shodan helps find internet-facing cloud assets.
CloudMapper generates visual network diagrams of your AWS infrastructure, making it easier to map relationships between services.
As part of this step, catalog all segregated compute resources (EC2 instances, Lambda functions), storage resources (S3 buckets, EBS volumes), databases (RDS, DynamoDB), network components (VPCs, security groups), and IAM entities (users, roles, policies).
Document API endpoints and integrate findings into a centralized asset inventory for continuous visibility.
Step 2: Cloud Configuration Review
One of the most important parts of a cloud pentest methodology is identifying misconfigurations that can be exploited. This phase is called cloud configuration review.
In this phase, you need to have excellent knowledge of all services used in the cloud infrastructure and best practices from each cloud provider. Now, let us dissect this for the three largest cloud providers: AWS, GCP, and Azure.
How to Pentest AWS Cloud

Penetration testing in the AWS Penetration Testing Service means extensive scanning of each service and its configurations. Start by setting up AWS CLI with read-only credentials for reconnaissance. Use aws iam get-account-authorization-details to extract all IAM policies and roles, then analyze them for overly permissive access.
Tools to conduct testing:
S3Scanner: A tool for finding and testing S3 buckets. Execute python3 s3scanner.py --threads 5 buckets.txt to check for public read/write access. In 2024, 1.48% of S3 buckets remained publicly accessible according to industry data, making this crucial.
AWS CLI: Official AWS command-line tool. Install via pip install awscli, configure credentials, then enumerate resources across all regions using commands like aws ec2 describe-security-groups to find open ports (0.0.0.0/0) in security groups.
Scout Suite – Open-source multi-cloud security auditing tool. Run python scout.py aws to generate HTML reports highlighting IAM misconfigurations, S3 bucket permissions, and CloudTrail settings. It checks against 400+ rules and outputs findings by severity.
Pacu: An open-source AWS exploitation framework. After installing, run run iam__enum_permissions to enumerate IAM permissions, then run s3__download_bucket to test data exfiltration. Pacu simulates real attacks like privilege escalation and EC2 impersonation. For example, Capital One’s 2019 breach could have been detected using Pacu to identify the misconfigured Web Application Firewall.
CloudMapper – A tool to generate network diagrams of AWS environments. Use python cloudmapper.py prepare --account myaccount to collect data, then python cloudmapper.py webserver to visualize VPC connections and identify network segmentation issues.
How to Pentest GCP Cloud
GCP penetration testing requires a thorough understanding of Google Cloud Services and their security models. Start by authenticating with service account credentials and use gcloud compute instances list to enumerate resources. The process incorporates GCP-native tools and third-party solutions to find threats in the GCP cloud.
Tools to use:
Forseti Security: Open-source tool for GCP security monitoring. Deploy it to continuously scan for policy violations, unusual IAM changes, and firewall misconfigurations.
GCP CLI (gcloud): Official command-line tool. Run gcloud projects get-iam-policy [PROJECT_ID] to audit IAM bindings and identify excessive permissions like “Editor” or “Owner” roles assigned broadly.
G-Scout: GCP security scanner that automatically audits configurations. Execute python gscout.py -p [PROJECT_ID] to scan for exposed Cloud Storage buckets and overprivileged service accounts.
GCPBucketBrute: Google Storage bucket enumeration tool. Use it to brute-force common bucket naming patterns and identify publicly accessible storage with python3 gcpbucketbrute.py -k keywords.txt.
How to Pentest Azure Cloud

Azure penetration testing is a security assessment targeting Microsoft Azure cloud services, including VMs, storage accounts, Virtual Networks, and Azure AD. Begin by authenticating with az login and run az account list to enumerate subscriptions and resources.
Tools to use:
Stormspotter – Creates attack graphs within Azure environments. After data collection via stormspotter.py, analyze privilege escalation paths from Azure AD users to subscription-level permissions.
Azure CLI – Command-line tool to manage Azure resources. Use az vm list to list all VMs and az network nsg rule list to check network security group rules for overly permissive access (like allowing SSH from any source).
Azucar – Azure auditing tool that generates configuration reports. Run Get-AzucarReport in PowerShell to analyze Azure AD roles, storage account encryption, and VM configurations.
MicroBurst – PowerShell-based scripts for Azure security assessment. Use Invoke-EnumerateAzureBlobs to discover publicly accessible storage containers and Invoke-AzureRmVMBulkCMD to execute commands across VMs.
Step 3: VAPT ( Vulnerability Assessment and Penetration Testing )
In this stage of the cloud pentesting methodology, you need to find different types of vulnerabilities and attempt to exploit them to help the organization understand real risks. It combines automated scanning (as discussed in the previous step) with manual testing techniques to comprehensively assess the cloud environment’s security posture.
Begin with cloud-native and third-party tools that can perform automated vulnerability scanning. For instance, AWS Inspector automatically discovers EC2 instances and Lambda functions, continuously scanning them for CVE findings and network exposure risks.
Major cloud providers offer their own security assessment services:
- AWS Inspector reports findings directly in AWS Security Hub.
- Azure Security Center provides continuous assessment of Azure resources.
- Google Cloud Security Command Center centralizes security findings across GCP.
With these tools, you can easily find misconfigurations and common vulnerabilities specific to each cloud platform.
For a more in-depth analysis, you can also utilize market-tested vulnerability scanners such as Astra Security, Nessus, Qualys, or Tenable. These VAPT tools are often configured to scan cloud environments with specific modules for cloud services.
For example, Nessus Cloud Edition can orchestrate scans of your cloud VPC or managed instances, producing detailed HTML/JSON reports for compliance teams.
Real-world case: the 2024 Football Australia breach occurred when developers misconfigured AWS S3 buckets, exposing 127 digital storage containers with player data—a vulnerability that automated scanning could have detected.
Step 4: Reporting
The reporting part of a cloud penetration test is essential. It involves taking technical discoveries and putting them in simple language for the client. A good report should graphically display the findings, highlight areas that could be exploited, and outline the necessary fixes.
Structure your findings, detailing every vulnerability (describing the issue and potential impact) with proof of how to reproduce it. Utilize a widely recognized vulnerability scoring system such as CVSS (Common Vulnerability Scoring System) to aid in prioritizing findings.
For example, an S3 bucket with public read access might score 7.5 (High), while an overly permissive IAM role allowing privilege escalation could score 9.1 (Critical).
Don’t miss out on an executive summary and a technical section. The guidance should outline a clear path for developers to remediate each vulnerability.
Include specific commands (e.g., aws s3api put-public-access-block) and infrastructure-as-code examples. Screenshots from tools like Pacu or ScoutSuite showing the misconfiguration add credibility.
Step 5: Remediation
This is where you analyze your penetration test results to enhance the overall security of your environment. This stage should be conducted in close cooperation between the penetration testing team and the client’s development team.
Prioritize fixes based on CVSS scores and business impact; remediate critical IAM misconfigurations before addressing low-severity logging gaps.
Step 6: Verifying Fixes
The last phase of penetration testing of cloud infrastructures is verifying that the provided solutions have fixed the identified vulnerabilities. For complex vulnerabilities or significant modifications of the cloud infrastructure, these targeted retests may range from focused to more comprehensive assessments.
Of course, pay special attention to critical vulnerabilities. A more rigorous test than usual will likely be required to confirm that they have been completely mitigated. Re-run the same tools (Scout Suite, Pacu) with identical credentials to verify that the issues no longer appear.
For example, if significantly misconfigured IAM permissions are detected, verify that the new structure adheres to the principle of least privilege and doesn’t allow unauthorized access.
Test this by attempting the same privilege escalation path (e.g., using Pacu’s iam__privesc_scan module) and confirming it now fails. According to 2024-2025 data, 82% of cloud misconfigurations stem from human error, making verification essential to prevent recurrence.
Types of Cloud Computing Models
Knowledge of various cloud computing models is mandatory when performing cloud penetration tests, as each model has security implications.
Types of Cloud Penetration Testing
Different testing approaches give you different views of risk. Pick the model that matches your threat profile and the questions you need answers to.
A) Black Box Pentesting:
Testers receive no internal information or credentials. They act like an external hacker using OSINT, DNS enumeration, and public API probing to find visible weaknesses. This shows how exposed your perimeter and public services really are.
B) Grey Box Pentesting:
In this method, testers get limited access or partial documentation, like a user account or topology notes. This simulates a compromised employee or contractor and helps reveal privilege escalation and lateral movement paths. It balances realism with the ability to dig deeper.
C) White Box Pentesting:
In white-box pentesting, testers have full access to code, configurations, IaC templates, and credentials. This is a comprehensive audit that uncovers subtle misconfigurations in IAM, Terraform, CloudFormation, and CI/CD pipelines. It finds issues that surface scans often miss.
D) Other Testing Variations:
Red teaming or adversary emulation, cloud native threat simulation, and continuous pentesting are often used as complementary approaches. Red teams validate detection and response. Adversary emulation follows frameworks such as MITRE ATT&CK for Cloud. Automated emulators and continuous checks validate controls across deployments and catch drift.
Key Areas of Focus in Cloud Pentesting
While the term’ cloud penetration testing’ itself is broad and encompasses various disciplines, several core aspects require a definite focus due to their adverse impact on the overall security posture. It can be broken down into the following broad categories:
Identity and Access Management Testing
Identity has become the primary security perimeter in cloud environments, making IAM testing critical:
- Testing identity boundaries in multi-cloud environments and hybrid architectures
- Testing for excessive permissions and privilege escalation paths across roles and service accounts
- Identifying weaknesses in federation configurations and cross-account trust relationships
- Simulating credential theft scenarios and session hijacking attempts using stolen tokens
- Evaluating multi-factor authentication implementation and testing bypass techniques
- Assessing identity governance processes and detecting orphaned access rights from former employees
Infrastructure-as-Code and CI/CD Security
Modern cloud pentesting “shifts left” to evaluate security before deployment:
- Analyzing Terraform, CloudFormation, and ARM templates for embedded security weaknesses
- Testing CI/CD pipelines for privilege escalation and injection vulnerabilities in build processes
- Evaluating GitOps workflows for unauthorized access opportunities and secret exposure
- Validating security guardrails within infrastructure automation processes
- Identifying policy-as-code weaknesses that could allow the deployment of vulnerable resources
- Testing artifact repositories and container registries for supply chain vulnerabilities
Container and Serverless Security
Cloud-native architectures require specialized testing approaches:
- Evaluating serverless execution environment manipulation techniques and Lambda function abuse
- Testing container runtime security and escape vulnerabilities to underlying hosts
- Evaluating serverless function permission boundaries and event-trigger security mechanisms
- Identifying vulnerable dependencies in container images and function libraries
- Assessing isolation weaknesses in multi-tenant container orchestration platforms like Kubernetes
- Testing for lateral movement between containerized and traditional workloads
Multi-Cloud Attack Path Analysis
Modern environments span multiple providers requiring comprehensive testing:
- Identifying orphaned resources and shadow IT across multiple cloud providers
- Identifying identity weaknesses between AWS, Azure, and GCP
- Testing for inconsistent security controls that create exploitable gaps across cloud providers
- Evaluating cross-cloud privilege escalation scenarios and trust relationship abuse
- Assessing data transfer security between different cloud environments and regions
- Testing disaster recovery mechanisms for security weaknesses during failover scenarios
Post-Exploitation & Compliance Validation
Testing results in clear documentation and actionable remediation guidance:
- Supporting PCI DSS, HIPAA, SOC 2, and ISO 27001 compliance with audit-ready documentation
- Demonstrating potential data access capabilities and quantifying business impact
- Evaluating persistence mechanisms and detection evasion in cloud environments
- Documenting full attack chains from initial access to objective completion
- Providing detailed findings with a clear risk context and PocC evidence
- Delivering specific remediation recommendations mapped to cloud provider capabilities
Considerations in Pentesting for Cloud
The dynamic and complex nature of cloud environments makes penetration testing more challenging. Some of the challenges during this phase require pentesters to modify their approach to pentesting and focus on key points. Let’s take a look at some of them.
Necessitates Clearly Scoped Tests
The shared responsibility model approach requires carefully scoped tests that target areas under client control and clearly define boundaries with the cloud provider’s offerings. This requires clear communication and a deep understanding of cloud architectures.
Navigating Jurisdictional Claims
Distributed cloud environments also present complicated issues surrounding legality and ethics. In some instances, cloud penetration testers must also navigate jurisdictional claims and data protection laws (for example, the Service Agreement), particularly in multi-tenant scenarios.
These activities require proper authorization and data-handling practices.
Need For Auto-Scalability
The characteristics of cloud resources are dynamic, including fast provisioning and auto-scalability, which necessitate agile testing. Static, point-in-time assessments can rapidly become outdated, and a process is needed to monitor and adjust them.
Eliminate misconfigurations and hidden risks in your cloud setup with Astra’s pentest platform.

How Astra Security Helps You Secure Your Cloud Environment?
Astra Security’s cloud penetration testing services blend automated scanning and expert-driven manual testing to uncover deep, actionable vulnerabilities in AWS, Azure, and GCP environments. From misconfigurations and exposed services to logic flaws and privilege escalations, our Offensive Security Engine runs 400+ cloud-specific test cases while our security team layers on custom tests tailored to your infrastructure.
Covering critical vectors across cloud storage, networking, and IAM, we evaluate configurations against CIS benchmarks, analyze access controls in line with the PoLP, and flag gaps using industry frameworks like the CSA Cloud Controls Matrix (CCM).
The built-in business logic testing helps expose hidden issues like privilege escalation, insecure workflows, and data access bypasses often missed by automated tools.
Inside Astra’s platform, all vulnerabilities (manual or automated) are delivered with clear impact, reproduction steps, and remediation guidance. With configuration reviews, gap analysis, real-time fix validation, and audit-ready reporting, you can review authentication setups, security groups, firewall rules, and encryption policies through a dedicated dashboard.
Final Thoughts
Modern cybersecurity plans require multi-cloud pentesting (a must-have), a solution that enables organizations to identify and remediate security vulnerabilities, typically in a tightly integrated cloud environment. This keeps the infrastructure and applications safe from threats and enables compliance across the multi-cloud area.
The process requires a deep theoretical understanding of cloud architectures, as well as a comprehension of specific challenges, such as the shared responsibility model and dynamic environments.
Routine penetration testing keeps organizations informed of rapidly changing threats and maintains compliance with industry regulations. By embracing cloud penetration testing as a continuous process, businesses can utilize the latest technology while efficiently managing security risks.
This zero-trust approach secures assets and builds a reputation with stakeholders, further aiding business objectives in increasing cloud reliance.
FAQs
Does AWS conduct penetration testing?
No, AWS doesn’t pentest your environment directly, but allows you to host pentesting tools on it. It also allows you to perform penetration testing, including activities like vulnerability scanning, exploitation attempts, and code injection, but it excludes DoS attacks without prior approval.
How do I become a cloud pentester?
Cloud pen testing blends IT security and hacking skills. Start with general IT or cybersecurity roles to build a foundation. Then focus on cloud platforms like AWS or Azure through courses and certifications (Security+ or CCSP). Practice with CTFs and labs to hone your hands-on skills in finding and exploiting cloud vulnerabilities.
What is cloud security testing?
Cloud security testing safeguards your confidential information in the cloud and checks your cloud provider’s security measures and your cloud-based applications for weaknesses that hackers could exploit.
Who is cloud penetration testing for?
Cloud penetration testing is essential for organizations that use cloud services such as AWS, Azure, or GCP. It benefits C-level executives, security managers, and IT professionals responsible for infrastructure and data security. Essentially, any business that needs to validate its cloud security controls should consider it.
When do I need a cloud penetration test?
You need a cloud penetration test after major infrastructure changes, new application deployments, or during regulatory compliance audits. It is also critical if you suspect a security incident or need to meet standards like PCI DSS, SOC 2, or ISO 27001. Regular testing ensures your defenses evolve with the threat landscape.
How do I get a cloud penetration testing certification?
Your organization can get a cloud pentesting certification by partnering with a certified penetration testing provider. Look for vendors whose experts hold certifications like GCPN, OSCP, or CCSP. Verify their team’s credentials and request proof of certification in your vendor assessment to ensure qualified experts are performing your tests.
What is the typical cost or scope of a cloud pentest?
A cloud pentest typically costs between $8,000 and $50,000, with an average of around $15,000. The final price depends on the scope, including the number of cloud services, application complexity, and compliance requirements. Testing focuses on misconfigurations, access controls, and cloud-specific services.
How often should cloud penetration testing be done?
Conduct cloud penetration tests at least annually, or biannually if you are in a highly regulated industry. It is also wise to test after any major system change, update, or security incident. For dynamic environments, consider continuous PTaaS models for ongoing assurance.
Can cloud penetration testing disrupt production systems?
Yes, testing in a production environment can potentially cause disruption or unintended data changes. To eliminate risk, testers often proceed with caution, which can limit coverage. Using a dedicated staging environment that mirrors production is usually a safer alternative for comprehensive testing.










What are the Benefits of Cloud Penetration Testing?
Doing a cloud penetration test provides a lot of benefits, mainly through-
1. Finding vulnerabilities to be fixed thereby ensuring the safety of the customer data stored.
2. Helping improve the cloud security system currently in place.
3. Allowing organizations to be compliant with various standards and regulations like ISO 27001, HIPAA, and more.
4. Building trust between cloud providers and customers by establishing the security of data at rest and in transit.
5. Helping maintain reputation and preventing any monetary losses for organizations using it.
Hope this clarifies your doubt.
What is shared responsibility model in cloud?
Hey Daniel, shared responsibility model in cloud refers to following a precise set of rules with a clear understanding between both parties i.e. the cloud provider and customers regarding their obligations and areas of accountability.
This really helped clarify where responsibility lies between the cloud provider and the customer, which is often confusing in practice. Thanks!
How easily cloud misconfigurations can create unintended attack paths, even when infrastructure is “managed”?