In our ongoing efforts to secure our digital landscapes, the frequency of cyberattacks continues to rise, emphasizing the need for robust cybersecurity measures. Recent statistics indicate that in 2022 alone, cybercrime has become a big stepping stone for most organizations, namely a $6 trillion one. This alarming figure underscores the urgency of developing innovative defense strategies.
In this context, gray box penetration testing has emerged as a dynamic approach, combining realism and security to strengthen digital defenses. This article aims to provide an in-depth understanding of gray box penetration testing, including its definition, methodology, significance supported by data, and the boundaries it operates within.
What is Gray Box Penetration Testing?
Gray box penetration testing is a type of penetration testing in which the pentesters have partial knowledge of the network and infrastructure of the system they are testing. Then, the pentesters use their own understanding of the system to do a better job of finding and reporting vulnerabilities in it.
In a sense, a gray box test is a combination of a black box test and a white box test. The black box test is a test that is done from the outside in, with the tester not knowing the system before testing it. A white box test is a test that is done from the inside out, with the tester having full knowledge of the system before testing it. In this blog, we will only discuss gray box penetration testing to provide you with enough information on the same.
Why choose Gray Box Penetration Testing?
Gray box penetration testing is a method that marries the strengths of the Black Box and White Box approaches. The success rate of the same is as such dependent on your depth of understanding of the target environment. This unique approach makes gray box testing a preferred choice in controlled settings like military and intelligence agencies.
In fact, gray box pentesting evaluates both network and physical security, making it the perfect fit for breaches involving perimeter devices such as firewalls. This approach blends techniques like network scanning, vulnerability assessment, social engineering, and manual source code review to assess all potential impacts from hackers or attackers.
How does Gray Box Penetration Testing differ from the black box and white box?
Penetration testing is divided into three categories: black box, white box, and gray box. Let’s understand the differences between these three:
| S No. | Black Box Penetration Testing | Gray Box Penetration Testing | White Box Penetration Testing |
|---|---|---|---|
| 1 | Little or No knowledge of network and infrastructure is required. | Somewhat knowledge of the Infrastructure, internal codebase and architecture. | Complete access to organization infrastructure, network and codebase. |
| 2 | Black box testing is also known as closed box testing. | Gray box testing is also known as translucent testing. | White box testing is known as clear box testing. |
| 3 | No syntactic knowledge of the programming language is required. | Requires partial understanding of the programming language. | Requires high understanding of programming language. |
| 4 | Black box testing techniques are executed by developers, user groups and testers. | Performed by third party services or by testers and developers. | The internal Development team of the organization can perform white box testing. |
| 5 | Some standard black box testing techniques are: Boundary value analysis, Equivalence partitioning, Graph-Based testing etc. | Some standard gray box testing techniques are Matrix testing, Regression testing, Orthogonal array testing, Pattern testing. | Some standard white box testing techniques are Branch testing, Decision coverage, Path testing, Statement coverage. |
5 steps to Perform Gray Box Penetration Testing
Gray box penetration testing is usually performed in 5 different steps mentioned below:
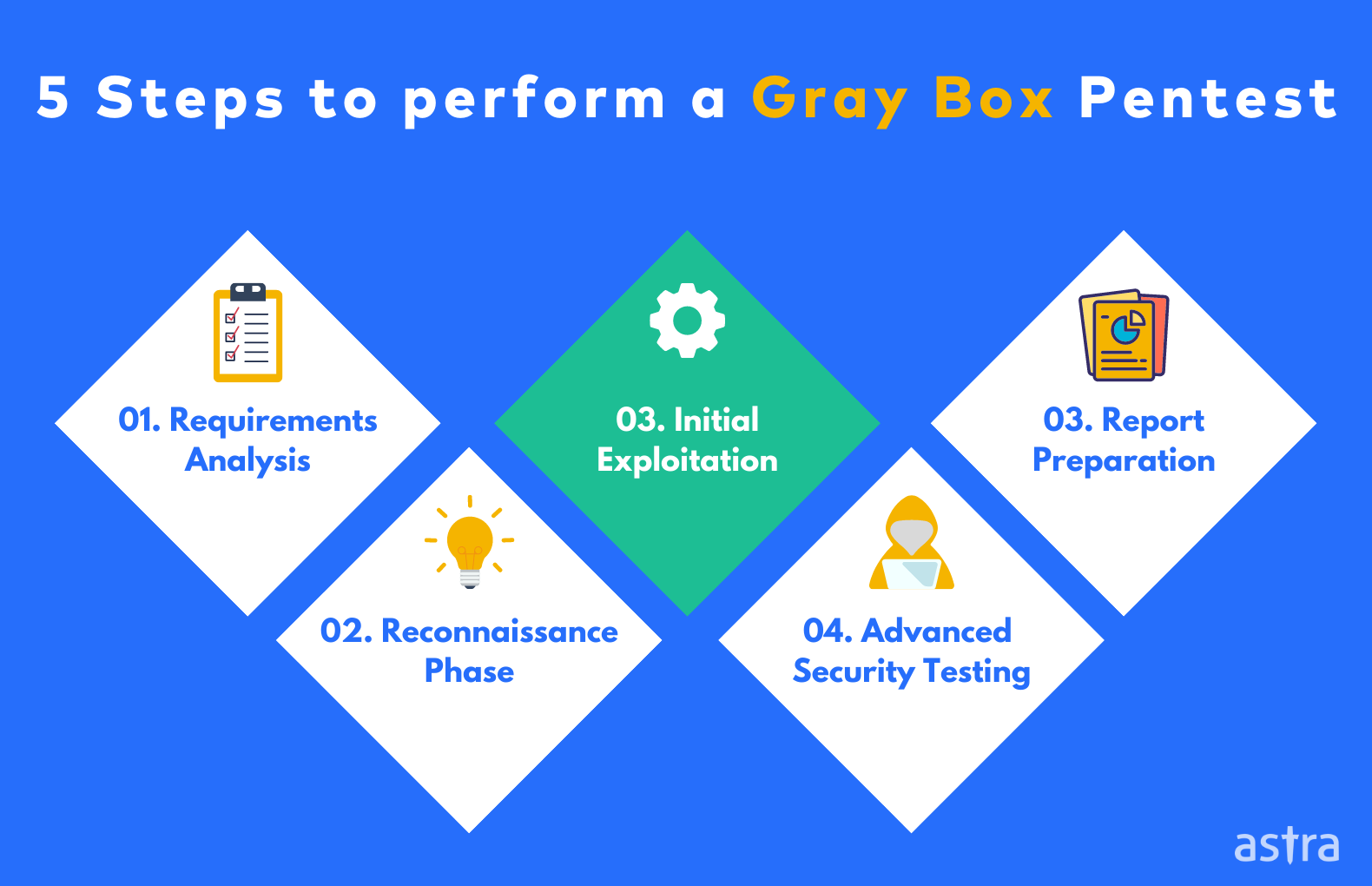
1. Planning and Requirements Analysis:
This phase includes understanding the scope of the application and the tech stack being used. The security team also requests some application-related information, such as dummy credentials, access roles, etc. This phase includes understanding the scope of the application and the tech stack being used. Furthermore, preparing a documentation map is also part of this phase.
2. Discovery Phase:
This phase is also known as Reconnaissance, which includes discovering the IP addresses being used, hidden endpoints, and API endpoints. The Discovery phase is not limited to networks but includes gathering information about the employees and their data, also known as Social Engineering.
3. Initial Exploitation:
Initial exploitation includes planning what kind of attacks will be launched in the later steps. This phase also includes finding misconfigurations in the servers and cloud-based infrastructure. The requested information helps the security team in creating various attack scenarios like privilege escalation etc. Further, behind the login, scanning would also be possible. Further, behind the login, scanning also goes on.
4. Advanced Penetration Testing:
This phase includes launching all planned attacks on the discovered endpoints—execution of Social Engineering attacks based on the collected information of employees. Furthermore, various vulnerabilities found are combined to create real-life attack situations.
5. Document & Report preparation:
The last step is preparing a detailed report of every endpoint tested along with a list of launched attacks.
Top 3 Gray Box Penetration Testing Techniques
Gray box pentest uses various types of techniques to generate test cases. Let’s understand some of them in detail:
1. Matrix testing
Matrix testing is a technique of software testing that helps to test the software thoroughly. It is the technique of identifying and removing all the unnecessary variables. Programmers use variables to store information while writing applications. Several variables should be as per requirement. Otherwise, it will reduce the efficiency of the program.
2. Regression testing
Regression testing is retesting the software components to find defects introduced by the changes made previously or in first the testing iteration. Regression testing is also known as retesting. It is performed to ensure that weaknesses are not introduced or reintroduced into a software system by modifications after the initial development. Regression Testing is an essential part of software testing because it helps to ensure that newly introduced software features continue to work as intended.
3. Orthogonal Array Testing
Orthogonal array testing is a software testing technique used to reduce test cases without reducing the test coverage. Orthogonal array testing is also known as the Orthogonal array method (OAM), Orthogonal array testing method (OATM), and Orthogonal test set.
What are the Benefits of Gray Box Penetration Testing?
1. Insider Information: Gray box testing is a perfect blend of black-box testing with knowledge of specific internal structures (or “inside knowledge”) of the item being tested. This inside knowledge could be available to the tester in the form of design documentation or code.
2. Less time-consuming: With insider knowledge, testers can plan and prioritize the testing, which will take less than planning test cases with no understanding of the network or codebase.
3. Non-intrusive and unbiased: Gray box test, which is also called non-intrusive and fair. It is said to be the best way to analyze the system without the source code. The gray box test treats the application as a black box. The tester will know how program components interact with each other but not about the detailed program functions and operations.
How Does Gray Box Testing Help Secure Your System?
While black-box tests mimic user experience without application knowledge, gray-box testing uses some information for more accurate user-like interactions.
In the face of determined outsiders despite standard security measures, gray box pentesting excels by focusing on post-breach behavior.
By using the above, you don’t only bolster system security against external threats but also insider risks. Testers’ partial application understanding allows realistic user experience simulations, uncovering errors, vulnerabilities, and exploits before cyber criminals do.
Why Astra’s Pentest Suite is a perfect fit for you?
All 3 types of penetration testing techniques have their own pros and cons but which one is perfect for you? Astra’s pentest suite is equipped with real-life hacking intelligence gathered from 1000+ vulnerability assessments and penetration tests (VAPT) done by our security experts on varied applications.
Say NO to the old boring way to test your organization’s security. Astra’s Vulnerability Scanner is ever learning from new CVEs, bug bounty data & intelligence gathered from pentest we do for companies in varied industries. Your CXOs get a birds-eye view of the security posture of your organization with data-backed insights that help them make the right decisions.
In addition, to ensure utmost security We here at Astra believe in ‘proactive security’ measures where we anticipate the infiltration techniques used by hackers and recommend additional security countermeasures to keep your and your customer’s data secure.
Features of Astra’s pentest suite:
- Self-served, on-the-cloud continuous scanner that runs 2500+ test cases covering OWASP, SANS, ISO, SOC, etc.
- Rich and easy-to-understand dashboard with a graphical representation that helps with vulnerability & patch management.
- Developer & CXO level reporting.
- Team collaboration options for assigning vulnerabilities for fixing.
- Multiple asset management under the same scan project.
- A dedicated ‘Vulnerabilities’ section that offers insights on vulnerability impact, severity, CVSS score, and potential loss (in $).
- A comprehensive scanner that includes all the mandatory local and global compliance requirement checks.
FAQs
1. What are the 5 stages of penetration testing?
Penetration testing comprises 1) reconnaissance, where information about the target is gathered; 2) scanning, identifying potential vulnerabilities; 3) gaining access through exploits; 4) maintaining access, testing for persistence; and 5) analysis, evaluating findings, and producing a comprehensive report for remediation. Find out more on the penetration testing guide.
















