A vulnerability is a weakness or a flaw in an IT, network, cloud, web, or mobile application system arising from coding errors, misconfigurations, design flaws, or human error that can make it susceptible to a successful external attack.
In an environment of accelerating digital transformation, vulnerabilities have grown in sophistication and scale, often outpacing traditional defensive measures. They are no longer isolated technical flaws but represent a dynamic challenge that intersects with strategy, governance, and innovation.
Addressing them requires not just tools but a mindset shift from reactive patching to proactive, continuous risk mitigation. But what is vulnerability, and why should it demand the undivided attention of CTOs and CISOs?
Categories Of Vulnerabilities
Detected by vulnerability scanning services, various vulnerabilities can be divided into different categories based on the systems in which they are present, including:
1. Software Vulnerabilities
These include software or network configuration flaws, such as unpatched software, open ports, or outdated versions, which can manifest as injections, insufficient testing, design flaws, and memory violations, among others.
While technical vulnerabilities are often seen as “fixable” with patches or updates, they reveal a deeper issue: the challenge of balancing rapid innovation with robust security. For instance, many organizations rush to deploy cutting-edge technologies without fully addressing their security implications, creating a cycle of reactive rather than proactive defense.
2. Hardware Vulnerabilities
Weaknesses in securing physical assets – such as server rooms, IoT devices, or even laptops – ranging from humidity to poor security and everything in between, are often overlooked. However, physical breaches can have cascading impacts, especially in industries reliant on operational technology (OT).
Furthermore, with the rise of IoT, safeguarding physical devices against dust, natural disasters, poor encryption, and hardware cyber threats is paramount, alongside robust software security through effective physical access controls and tamper-detection mechanisms.
3. Human Vulnerabilities
No matter how advanced an organization’s technical defenses are, they can be undermined by a single human error—whether it’s a misconfigured server, a weak password, or falling for a phishing email.
As such, exploitation of user behavior through phishing, social engineering, or insider threats remains the weakest link in cybersecurity, underscoring the critical need for a culture of security awareness where every employee understands their role as the first line of defense.
When paired with behavioral analytics, cybersecurity training can significantly reduce these risks.

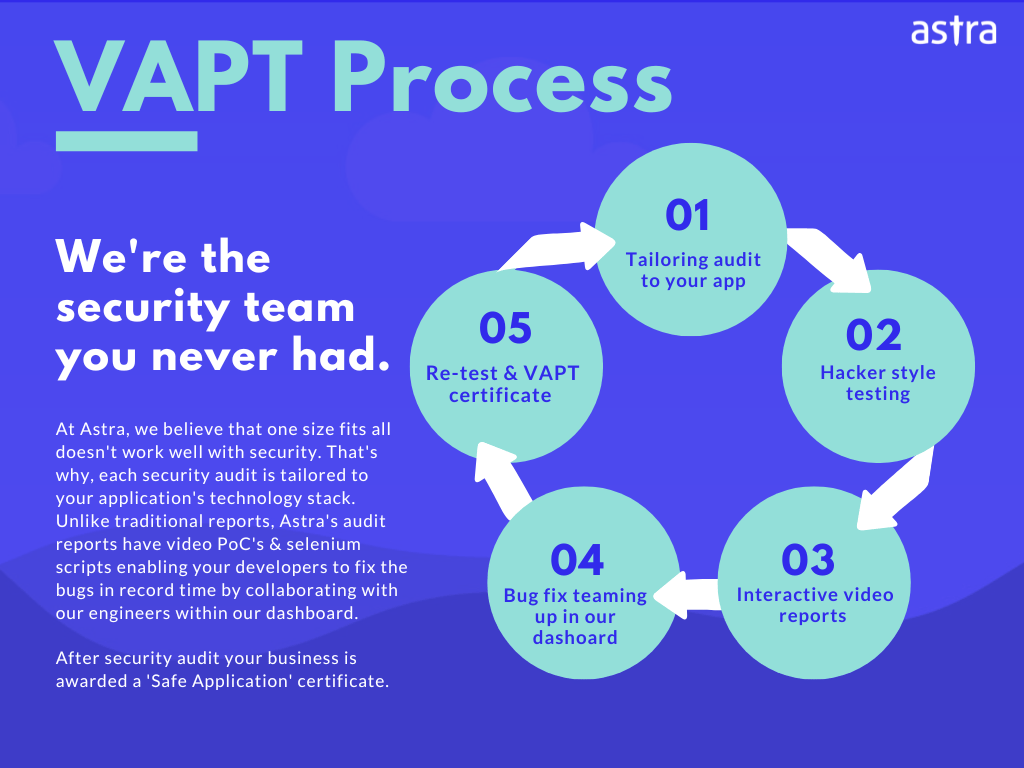
Why is Astra Vulnerability Scanner the Best Scanner?
- We’re the only company that combines automated & manual pentest to create a one-of-a-kind pentest platform.
- Vetted scans ensure zero false positives.
- Our intelligent vulnerability scanner emulates hacker behavior & evolves with every pentest.
- Astra’s scanner helps you shift left by integrating with your CI/CD.
- Our platform helps you uncover, manage & fix vulnerabilities in one place.
- Trusted by the brands you trust like Agora, Spicejet, Muthoot, Dream11, etc.

What is Vulnerability and its Root Cause?
Most people today believe vulnerabilities are isolated flaws in the system. Infact, they are often symptoms of deeper issues rooted in how technology, organizations, and human behavior intersect in an increasingly complex world.
While the digital landscape has advanced, the root causes of vulnerabilities remain rooted in historical and emergent patterns that continue to shape vulnerabilities today:
1. Complexity and Interconnectedness
Over the last decade, the explosion of interconnected systems, from IoT devices to sprawling SaaS ecosystems, has amplified the potential for vulnerabilities. Complexity is no longer optional—it’s an outcome of innovation.
Yet, it also often conceals misconfigurations, unintended access points, and exploitable blind spots. Even AI-powered systems trained on flawed or incomplete datasets can inadvertently create vulnerabilities. The future of security lies in designing for simplicity — whether through automation or AIML— to proactively identify threats without adding to the operational burden.
2. Increased Attack Surface
Today’s reliance on external vendors, cloud-native apps, and third-party APIs has exponentially increased the attack surface. A single vulnerability in a shared dependency can cascade into widespread breaches—a lesson underscored by incidents like the SolarWinds or MOVEIT attacks.
Adding multiple systems with similarities (code, software, OS, and even hardware) only increases the odds of a successful attack. As such, moving forward, you need to reimagine risk management frameworks to treat supply chains as critical assets, applying Zero Trust principles to internal and external touchpoints.
3. Human Error and Behavior
Despite advances in technology, human error remains the most exploited vulnerability. From phishing and social engineering to fundamental errors, such as weak passwords or misconfigurations, the resilience of the human factor is still a work in progress.
Beyond just training, organizations need to foster a culture of awareness with proactive behavior analysis to detect abnormal activity before it becomes a breach.
4. Legacy Systems and Outdated Practices
While technology continues to advance at breakneck speed, in light of transition costs and human resistance to change, adoption continues to lag. This leaves you lugging unpatched software and dated systems that not only lag in functionality but act as entry points to exploiting well-documented flaws.
This is where DevSecOps steps in. Viewing cybersecurity as an enabler, not an overhead, allows you to embed the same into pipelines from the ground up, creating long-term resilience while retiring outdated systems is built into the process.
5. Shared Vulnerabilities Across Common Platforms
Standardized software, frameworks, and libraries have streamlined development but also made entire ecosystems vulnerable to a single point of failure. Incidents like Log4Shell remind us that shared dependencies can be weaponized at scale.
As organizations increasingly adopt generative AI tools and shared ML models, they face similar risks. Securing these tools and diversifying dependencies will be critical to reducing your systemic exposure.
Vulnerabilities vs Risks
When discussing vulnerability vs. risk, the simplest way to frame it is this:
- Vulnerability is the “what”—the weakness or flaw that an attacker could exploit, whether in a system, process, or behavior.
- Risk defines “why it matters”—the potential outcome or consequence of that exploitation, often measured in impact and likelihood.
To put that in context, in the Colonial Pipeline attack of 2021, the vulnerability was a single compromised password—small on its own, but it unleashed a cascade of events: 23 Million stolen passwords, a 5-day operational shutdown of the largest US fuel pipeline, disrupted 45% of supply, and incurred over $4.4 million in ransom payments.
| Feature | Vulnerability | Risk |
|---|---|---|
| Definition | A weakness or flaw in a system or its design that can be exploited to cause harm. | The potential for loss, damage, or negative impact resulting from a threat exploiting a vulnerability. |
| Nature | Technical | Business |
| Focus | System, application, or network | Impact on the organization |
| Example | A SQL injection in a web application | Data breach, financial loss, reputational damage |
| Mitigation | Patching, configuration changes, security controls | Risk assessment, risk management strategies, incident response plans |
| Role | Prerequisite for a risk to materialize | The outcome of a successful exploit |
Common Security Vulnerabilities
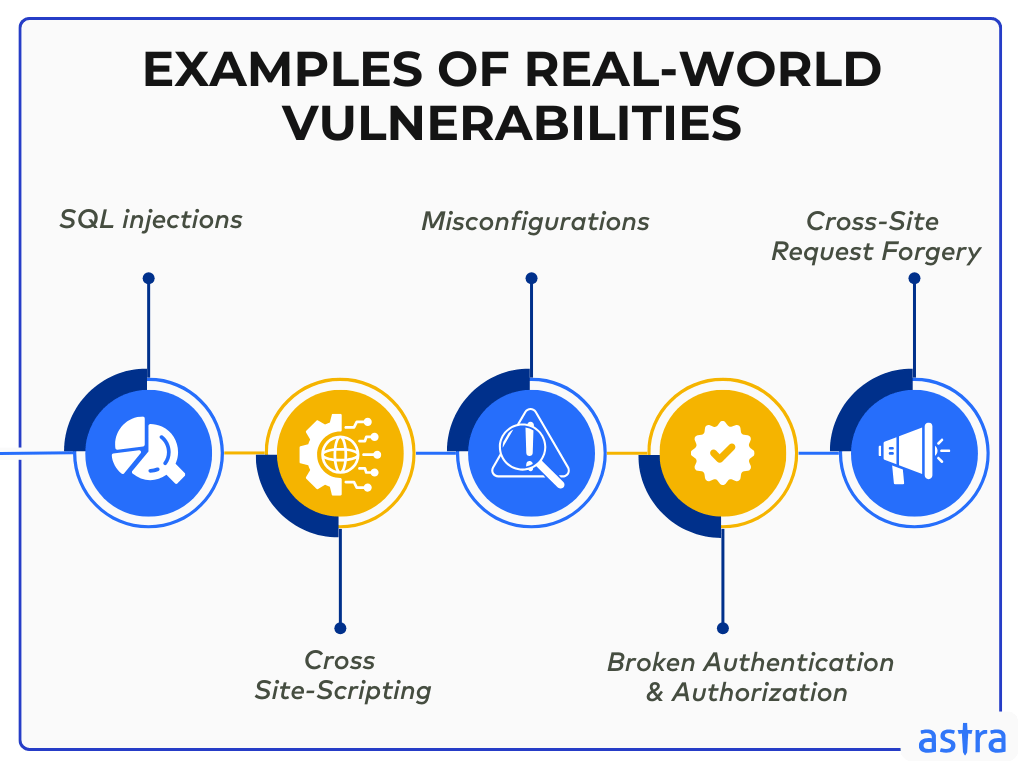
1. SQL Injections
SQL injections underscore a glaring truth: organizations still fail to enforce security basics, like input sanitization and parameterized queries. Modern frameworks and ORM libraries prevent these vulnerabilities almost effortlessly, yet they are frequently sidelined in the rat race to deploy.
With the shift toward microservices architectures and API-based interactions, where multiple services access databases, the attack surface for SQL injections has expanded dramatically. This complexity increases the risk of vulnerabilities going unnoticed in a labyrinth of interconnected systems.
2. Cross Site-Scripting
The rise of single-page applications (SPAs) and client-side rendering has made XSS attacks more prevalent and harder to detect. Traditional server-side input validation falls short when so much of the logic resides on the client side. Attackers inject malicious scripts into web pages, compromising user data and enabling malicious actions.
XSS vulnerabilities thrive because organizations prioritize speed over security. Often, developers overlook secure coding practices or use quick fixes, like simple regex, failing to address the complexity of modern attacks, especially when working with JavaScript-heavy frameworks. The solution isn’t just technical—it’s cultural. Teams must prioritize security reviews and adopt robust Content Security Policies (CSP) to protect users.
3. Misconfigurations
With the proliferation of cloud services and distributed systems, misconfigurations have become the Achilles’ heel of modern infrastructure. From exposed S3 buckets to improperly configured firewalls, these vulnerabilities arise from human error and the complexity of managing sprawling environments, highlighting gaps in DevOps workflow.
Automation tools like Infrastructure, such as Code (IaC), offer a partial solution but are not panaceas. Misconfigurations often occur because organizations lack centralized visibility and robust processes for verifying settings. The focus should shift from firefighting to prevention, automating configuration checks, and embedding security into every stage of the lifecycle.
4. Broken Authentication and Authorization Measures
Weak passwords, poor session management, and lack of multi-factor authentication (MFA) continue to expose organizations to unauthorized access. Often, these vulnerabilities stem from a false sense of security. Default credentials like “admin/admin,” session tokens that don’t expire or are reused, and, worst of all, tokens that users can tamper with to escalate privileges are glaring examples.
Implementing strong identity and access management (IAM) systems, including OAuth, SSO, and MFA, is no longer optional—it’s foundational. Specialized libraries can handle much of this complexity, but organizations must remain vigilant and always triple-check authentication mechanisms.
5. Cross-Site Request Forgery
Unlike flashier vulnerabilities, CSRF is a silent threat, relying on subtle browser manipulation – causing authenticated users to unknowingly perform actions on malicious sites, such as transferring funds or changing settings. The problem lies in the implicit trust websites place in browsers to authenticate requests without further validation.
CSRF attacks highlight the need for developers to think beyond functionality and consider user behavior. Anti-CSRF tokens are a start, but security must evolve to include behavioral analytics, which can detect and block requests that deviate from standard patterns. Security isn’t static—it must adapt to changing attacker tactics and user expectations.
Four Types of Vulnerabilities & Why They Matter
Vulnerabilities don’t exist in silos—they often overlap and amplify each other. A misconfiguration can enable the exploitation of a software flaw, while human error can deepen systemic risks in shared ecosystems. The “worst” vulnerability depends on the context—a zero-day exploit might cause instant devastation, but persistent human-driven issues can erode defenses over time.
But to understand the nuances of such a chain, we need to break down each type into more than a sterile list of definitions but contexted actionable insights.
1. Flaws
A flaw can be defined as functionality placed unintentionally within the system. It results from poor design or mistakes made during development that can go undetected for quite an extended period (even years!), and most of the CVEs discovered nowadays belong to this category.
If discovered by the wrong side of people, such flaws can be sold and bring in hundreds of thousands of pounds. As such, their persistence demands continuous code reviews, automated testing, and security audits throughout the SDLC. Regular assessments and a culture of security-first design can reduce the likelihood of these flaws being undetected.
2. Zero-day Vulnerabilities
In cybersecurity, a zero-day vulnerability is any vulnerability that has recently been discovered and is not publicly known. Once they are publicly known, they immediately become a valuable commodity for carrying out repeated attacks.
While the importance of threat detection and response is often debated, we advocate for a balanced approach. In addition to behavior-based security systems and continuous monitoring, a proactive patch management strategy and collaboration with threat intelligence platforms can significantly reduce the window of vulnerability when zero days are discovered.
What Are Zero-Day Exploits?
These are exploits that make use of a relatively unknown vulnerability in cybersecurity. Until such a vulnerability is patched, people with malicious intent can use it to exploit the system affected by it.
In this scenario, day zero refers to the day the invested party learns of the vulnerability and works to patch it.
3. Features
What’s meant to enhance user experience can often be weaponized by attackers. Features are intended functionalities within the system that are exploited for unauthorized access or control. They’re not flaws; instead, features designed for convenience and usability, when left unchecked or improperly secured, can create vulnerabilities.
Security and product teams must collaborate closely to ensure all features are thoroughly tested for vulnerabilities, especially those that introduce new access points. Secure by design should be the paramount principle, prioritizing functionality and resilience to exploitation.
4. User Error
User errors are introduced through the user’s practices, such as setting weak passwords, enabling vulnerable features, failing to fix flaws, and more. They compromise the integrity of a well-designed system intended to reduce cybersecurity vulnerability.
Ironically, even cybersecurity-aware individuals aren’t immune—human behavior is unpredictable, and lapses can occur in the most “secure” environments.
Thus, addressing the above requires more than just awareness training—it’s about building systems that are resilient to human mistakes. Automated patch management, multifactor authentication, and behavior-driven access controls can mitigate the risks of human error.
Why Vulnerabilities Matter to CTOs and CISOs
Vulnerabilities in cybersecurity are often framed in terms of financial losses, reputational damage, legal consequences, and compliance failures. While these are critical, the true impact of vulnerabilities extends far beyond a single breach.
Simply put, they are responsible for shaping an organization’s long-term agility, innovation, and resilience in a rapidly shifting digital ecosystem.
Evolving Nature of Risk
Vulnerabilities are no longer isolated incidents but reflect the dynamic interplay between infrastructure, people, and processes. As cyber threats become more sophisticated, the ability to respond quickly to emerging vulnerabilities is as critical as preventing them in the first place.
In our experience, organizations that are slow to identify and address vulnerabilities will fall behind not just in security but in their overall capacity to innovate and scale securely.
The Competitive Edge
In today’s market, customers and partners value security more than ever, and an organization’s ability to demonstrate robust vulnerability management can set it apart from competitors.
Thus, the narrative is no longer just about avoiding breaches; it’s about positioning your organization as a security leader who proactively protects its digital assets, people, and stakeholders.
Beyond Compliance and Cost
While compliance (GDPR, PCI DSS, SOC 2, etc.) and financial consequences remain significant motivators, focusing solely on these factors can narrow an organization’s perspective.
Viewing vulnerability management as a compliance-driven task or cost-saving mechanism limits its potential, while a more strategic approach places it as an enabler for broader business goals, including:
- Fostering Innovation: By embedding vulnerability management into the development lifecycle, organizations can ship faster and with greater confidence.
- Building Resilience: By identifying weaknesses early, organizations can strengthen their defenses, ensure they remain adaptable, and create long-term resilience.
- Elevating Strategic Decision-Making: Proactively managing vulnerabilities allows CXOs to make informed, data-driven decisions to balance risk with innovation.
What is Vulnerability Management?
Vulnerability management is more than just a technical process—it’s a strategic pillar supporting the business’s overall health and growth. It systematically identifies, assesses, prioritizes, and mitigates vulnerabilities within an organization’s infrastructure, applications, and networks.
But before diving into specific practices, it’s essential to understand the vulnerability lifecycle from discovery to learning. Optimizing each stage enables better allocation and helps anticipate potential threats, positioning organizations to not just defend against attacks but stay ahead of them.
What is the Lifecycle of a Vulnerability?
The lifecycle of a vulnerability is more than just a sequence of events; it is a roadmap that determines the efficacy of an organization’s security posture. Some key stages include:
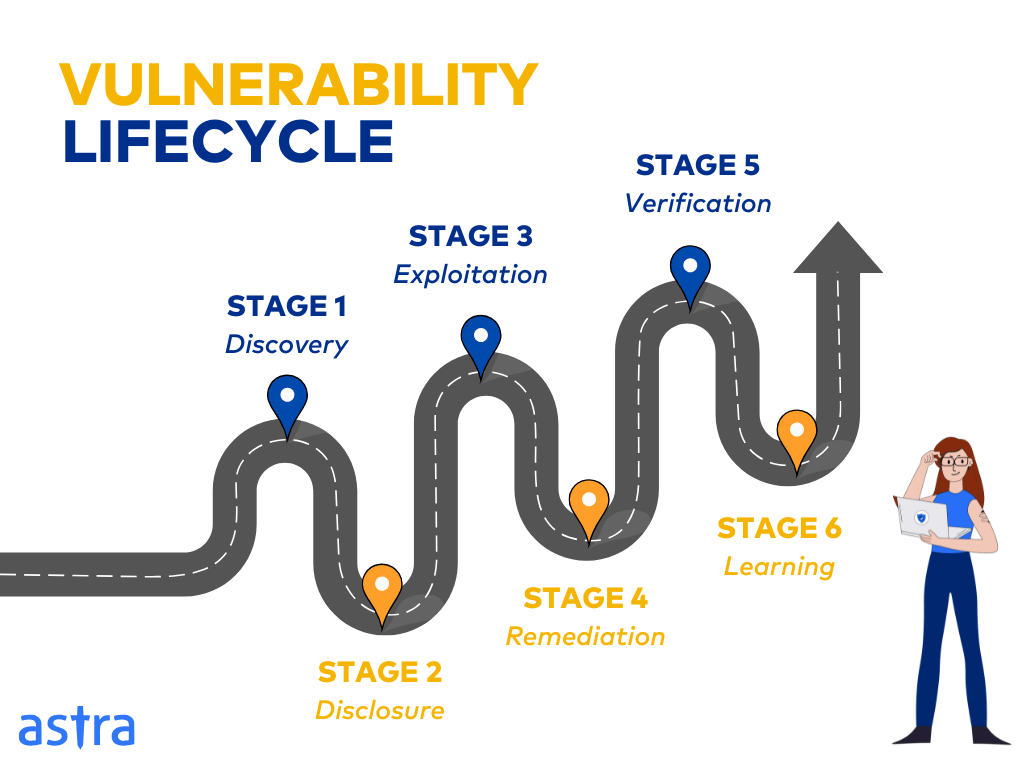
Stage 1: Discovery
The discovery phase marks the starting point, where vulnerabilities are identified through scans, bug bounty programs, or external reports.
Even with the sheer volume of vulnerabilities discovered daily, surprisingly, many organizations still rely on outdated methods, failing to integrate advanced tools like machine learning-based anomaly detection and continuous monitoring frameworks.
Stage 2: Disclosure
Once identified, vulnerabilities must be disclosed responsibly after assessing their scope and potential impact and determining the urgency of remediation. This stage is not just about transparency—it’s a delicate play that requires strategic thinking.
This stage is all about balance (and experience); disclose too early, and you risk exploitation but delay too long, and the threat grows. Coordinated Vulnerability Disclosure (CVD) frameworks can help, but many still mishandle this phase, leading to premature public exposure and potential breaches.
Stage 3: Exploitation
Unaddressed vulnerabilities inevitably enter the exploitation phase, where attackers leverage them for malicious gain.
The rise of automated exploit kits and AI-driven attacks has escalated the speed and sophistication of exploitation, forcing organizations to recognize that the exploitation stage is not just a technical failure but also a failure of governance and strategy.
Stage 4: Remediation
The remediation phase, which focuses on patches, reconfigurations, and/or mitigation deployment, often faces challenges due to varying timeframes. These challenges are further compounded by company-specific constraints, such as considering the coexistence of different technologies, internal policies, and external compliance mandates.
With cloud-native and distributed systems, the remediation process must account for scalability and minimal disruption to operations. If not well-planned, you risk causing more problems than you solve.
Stage 5: Verification
Verification ensures the effectiveness of remediation efforts. However, in real life, this stage is often overlooked or rushed, leading to incomplete fixes and residual vulnerabilities.
Continuous monitoring and regression testing are crucial, especially in dynamic environments like CI/CD pipelines. Verification is not just a technical step but a validation of the organization’s commitment to security.
Stage 6: Learning
The final and most transformative stage is a hallmark of mature cybersecurity programs that separate leaders from laggards.
Organizations that analyze incidents and integrate findings into their security strategies create a feedback loop that strengthens defenses. Yet, many fail to institutionalize this phase, treating vulnerabilities as isolated events rather than systemic risks.
Methods to Find Flaws
Commonly used methods for flaws or data vulnerabilities include scans and penetration tests. Each has its merits and demerits, as well as different types that can be carried out.
1. Vulnerability Scans
Vulnerability scans are often seen as the first line of defense, offering quick and regular assessments of a system’s security. While they’re efficient in flagging potential weaknesses, the reality is that they rarely capture the complete picture. Scanners can miss critical vulnerabilities, provide false positives, or fail to identify the more profound risks hiding within the system.
Some common types of vulnerability scans include:
- Scan Behind Logins
Scanning behind logins uses credentials to access the internal system. While more comprehensive, it indicates CVEs present in operating systems, installed software, and even missing security patches.
- Unauthenticated Scans
These scans mimic hacker behavior and analyze exterior vulnerabilities. They can highlight potential attack vectors but often produce a higher volume of false positives, requiring expert validation to separate the noise from actual risk.
2. Pentests
Penetration tests are far more exhaustive, simulating real-world attacks by ethical hackers attempting to breach your systems. They offer deep insight into how vulnerabilities might be exploited and the potential damage an attacker could cause. But there’s a catch—pen tests are expensive, time-consuming, and require significant manual effort.
They can be carried out manually or using automated tools. However, the question arises: are we willing to pay for the depth they provide? Sometimes, businesses rush for this “gold standard” without considering its suitability or frequency—making it crucial to align your testing strategy with your organization’s risk profile.
- Manual Pentests
Penetration tests that qualified expert ethical hackers carry out are known as manual pentests. These are more comprehensive regarding vulnerabilities discovered, and there is a lesser chance of false positives.
- Automated Pentest
Automated pentest is carried out using penetration testing tools. Such software is capable of detecting vulnerabilities and attempting to exploit them using known pre-programmed techniques.
In our opinion, a blend of vulnerability scans and pentests—both manual and automated — provides a more balanced, comprehensive security approach. Ultimately, it’s about finding the right balance that aligns with your organization’s security goals and budget.
Final Thoughts
In today’s hyper-connected digital landscape, what is vulnerability is a complex question. Whether stemming from coding flaws, misconfigurations, or user errors, CVEs create exploit opportunities for systems, networks, and applications, leading to data breaches, financial losses, and reputational damage. Understanding types and root causes is the first step in building a solid security foundation.
More importantly, vulnerabilities represent more than just weaknesses—they mirror an organization’s broader health and agility. As the threat landscapes evolve, so must our approaches.
Today, vulnerability management transcends simple identification, requiring continuous scanning, prioritized remediation, and leveraging tools like scanners, pentests, and databases like CVE and NVD. Fostering a culture of security awareness within the organization is equally crucial.
Ultimately, effective management of CVEs is not merely a technical necessity but a critical business imperative that demands continuous adaptation, the integration of security into every facet of organizational operations, and an unwavering commitment to building resilience into the core of strategic decision-making.
FAQs
Are all vulnerabilities exploitable?
Not all vulnerabilities are exploitable; their exploitability depends on required access, attack complexity, and security controls. Some are theoretical or impractical to exploit. Assessing each vulnerability’s risk and prioritizing remediation based on impact and likelihood of exploitation is crucial for effective security management.
What are common vulnerability databases?
1. Common Vulnerabilities and Exposures (CVE): A standardized, globally recognized database of information security threats and exposures.
2. National Vulnerability Database (NVD): A comprehensive collection of security vulnerabilities provided by the National Institute of Standards and Technology (NIST).
3. Microsoft Security Updates: Microsoft maintains a database of security vulnerabilities and product updates.
4. OWASP Top 10: A list of the top 10 most critical web application security risks maintained by the Open Web Application Security Project (OWASP).
5. Common Vulnerabilities Scoring System (CVSS): A framework for scoring and rating the severity of bugs based on their impact and ease of exploitation.