Vulnerability scanners have recently emerged as one of the most critical tools for ensuring proper security posture management for organizations, especially with newer attack vectors and a cyberattack occurring every 39 seconds.
However, with multiple types and vendors offering different features, pricing, timelines, and capabilities, choosing the right one for you can seem impossible. But before we discuss the 11 best vulnerability scanners of 2026, let’s examine the various types of scanners on the market!
Top 11 Vulnerability Scanners of 2026

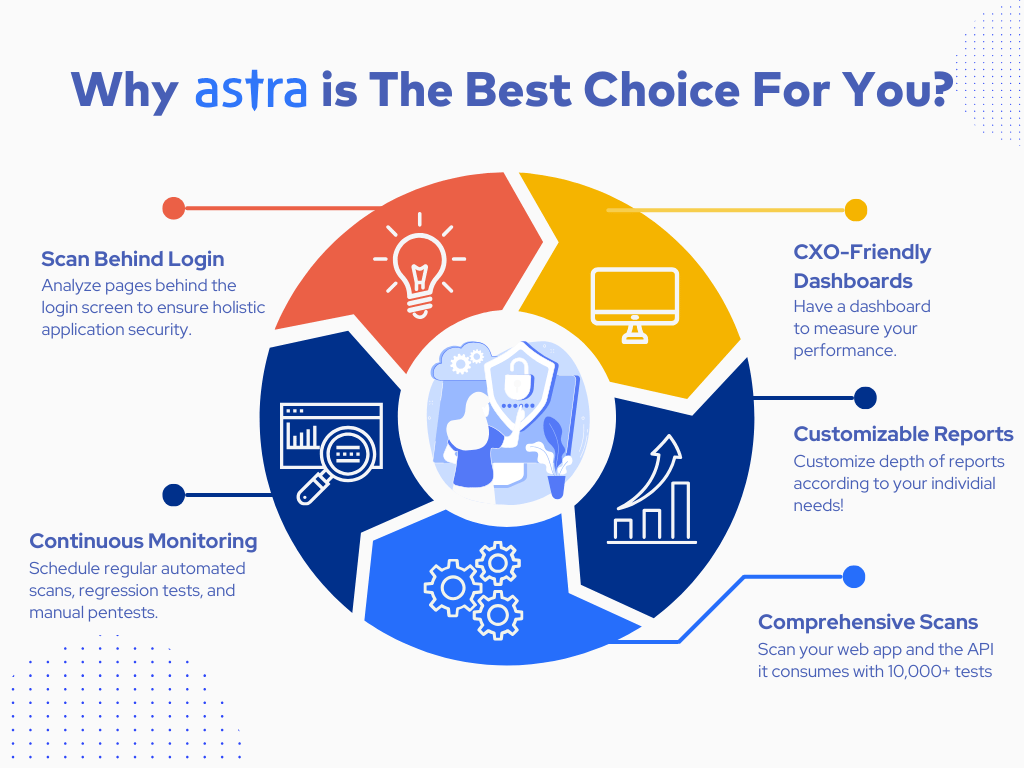
Why is Astra Vulnerability Scanner the Best Scanner?
- We’re the only company that combines automated & manual pentest to create a one-of-a-kind pentest platform.
- Vetted scans ensure zero false positives.
- Our intelligent vulnerability scanner emulates hacker behavior & evolves with every pentest.
- Astra’s scanner helps you shift left by integrating with your CI/CD.
- Our platform helps you uncover, manage & fix vulnerabilities in one place.
- Trusted by the brands you trust like Agora, Spicejet, Muthoot, Dream11, etc.

Top 3 Vulnerability Scanners Compared
Evaluation Criteria
We evaluated the vulnerability scanners based on several criteria. Our assessment included the scope of scanning capabilities and how well each tool covers various application types and vulnerabilities. Ensuring accuracy and reducing false positives are critical for managing vulnerabilities effectively. The tools should seamlessly integrate into current development and security workflows and offer comprehensive reporting features, which were significant factors in our evaluation. Lastly, we aimed to include various open-source and commercial tools to meet diverse budgets and organizational requirements.
| Features | Astra Vulnerability Scanner | Qualys | Rapid7 |
|---|---|---|---|
| Scanner Capabilities | Web and Mobile Applications, Cloud Infrastructure, API, and Networks | Cloud and web applications | Network, cloud, and web applications |
| Accuracy | Zero False Positives Assured (Vetted Scans) | False positives possible | False positives possible |
| Scan Behind Logins | Yes | Yes | No |
| Compliance | PCI-DSS, HIPAA, SOC2, GDPR, and ISO 27001 | PCI-DSS | CIS and ISO 27001 |
| Integrations | Slack, Jira, GitHub, GitLab | Cisco, IBM, Splunk | Splunk, AWS, Microsoft |
| Expert Remediation | Yes | Yes | No |
| Deployment | SaaS | SaaS or private cloud-based options | On-premise |
| Pricing | Starts at $199/month | Quote upon request | $175/month |
11 Best Vulnerability Scanners in Detail
1. Astra Vulnerability Scanner (Best for Startups and Enterprise)
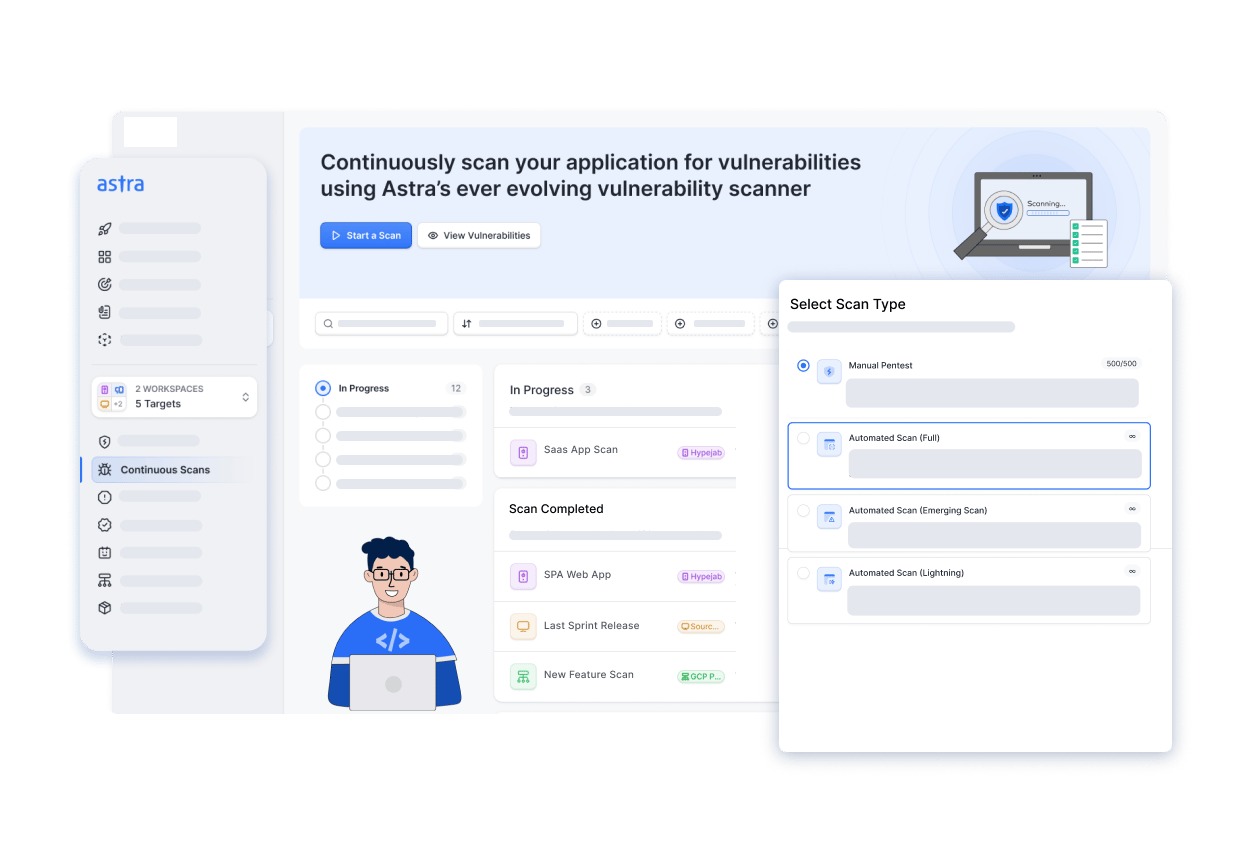
Features:
- Scanner Capabilities: Web and Mobile Applications, Cloud Infrastructure, API, and Networks
- Accuracy: Zero False Positives Assured (Vetted Scans)
- Scan Behind Logins: Yes
- Compliance: PCI-DSS, HIPAA, SOC2, and ISO 27001
- Integrations: Slack, Jira, GitHub, GitLab
- Expert Remediation: Yes
- Deployment: SaaS
- Pricing: Starts at $199/month
- Rating on G2: 4.5 out of 5
Built on standards like OWASP, NIST, and SANS25, Astra vulnerability scanner runs over 10,000+ tests to pinpoint new, emerging, and existing vulnerabilities in various types of assets.
We guarantee zero false positives through vetted scans, a CXO-friendly dashboard, and an AI-powered test case generation and chatbot. Moreover, our smart Chrome extension helps record logins for simplified scanning of protected screens and user roles.
Lastly, our scan behind login capabilities surpasses the traditional CVEs, making it the go-to choice for scanning modern infrastructure and one of the most trusted vulnerability scanners.
Experts Review
Pros
- Can detect business logic errors and conduct scans behind logins.
- Provides 3 rescans to ensure successful remediation of vulnerabilities.
- Offers compliance-specific reports.
- Ensures zero false positives through vetted scans.
Limitations
- Only a 1-week free trial for Astra Vulnerability scanner is available.
What our Customers Have to Say
“Astra penetration testing is comprehensive and provides automated vulnerability scanning. Astra also integrates well with CI/CD pipelines and ensures vulnerability assessments in software development lifecycles.” – Source: Gartner
Book a pentest for your Indian Business and stay protected with our 10,000+ AI-powered test cases.
Discuss your security needs & get started today!
2. Qualys (Best for Enterprises)

Features:
- Scanner Capabilities: Cloud, web applications
- Accuracy: False positives possible
- Scan Behind Logins: Yes
- Compliance: PCI-DSS
- Integrations: Cisco, IBM, Splunk
- Expert Remediation: Yes
- Deployment: SaaS or private cloud-based option
- Pricing: Quote upon request
- Rating on G2: 4.4 out of 5
Qualys WAS is a cloud-based website vulnerability scanner platform that assesses cloud assets, vulnerabilities, and compliance status.
Qualys constantly updates its database of over 20,000 vulnerabilities across various asset types and Operations systems. Its scalability, accuracy, and user-friendly interface are some of the reasons that make this tool a popular choice.
As a pentester, Qualys provides you with a good mix of automated and manual testing and comprehensive reports to facilitate understanding the vulnerabilities, especially in enterprises.
Experts Review
Pros
- The highly scalable vulnerability scanning solution
- Provides vulnerability management, detection, and response.
- Accurate reporting that is easy to follow.
Limitations
- Can be slow when scanning.
- Difficult to navigate for beginners.
- Not a cost-effective solution.
Customer Review
“The best aspect of Qualys VMDR is its user-friendly interface that allows for easy and intuitive vulnerability scanning. The platform empowers us to select and customize the specific types of scans we need, providing a tailored approach to address our unique security requirements.”
– Priyank B (Source: G2)
3. Rapid7 (Best for Security Assessment)
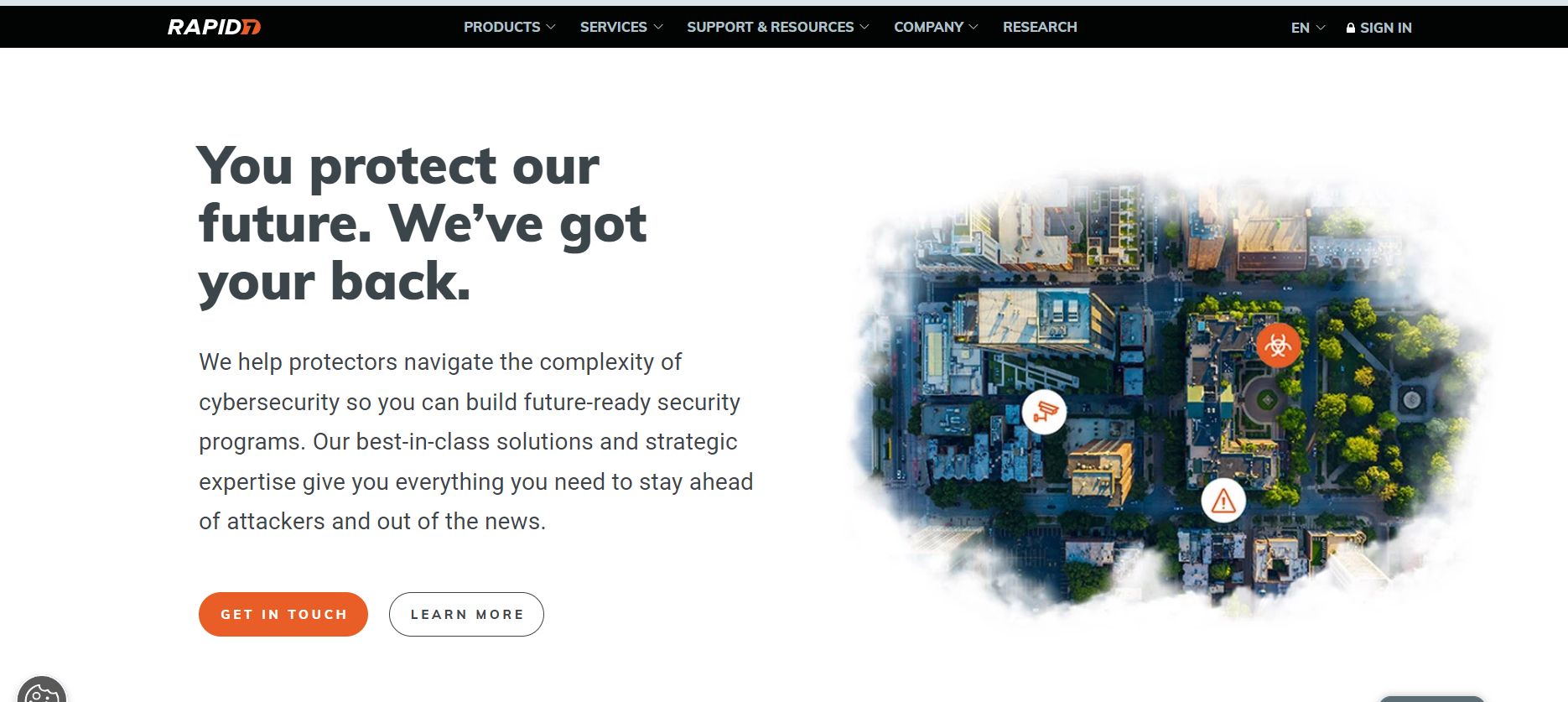
Features:
- Scanner Capabilities: Network, cloud, and web applications
- Accuracy: False positives possible
- Scan Behind Logins: No
- Compliance: CIS, ISO 27001
- Integrations: Splunk, AWS, Microsoft
- Expert Remediation: No
- Deployment: On-premise
- Pricing: $175/month
- Rating on G2: 4.0 out of 5
Rapid7 is also a vulnerability scanning tool that provides vulnerability testing, risk management, and threat intelligence on various assets.
Their self-service vulnerability scanner can detect over 1,80,000 vulnerabilities, from informational to critical level vulnerabilities, and more than 4,000 exploits in their Metasploit framework.
As a security expert, Rapid7 helps organizations with large networks and assets by providing an in-depth view of the network and the corresponding threats and vulnerabilities, making it easier to track and remediate.
Experts Review
Pros
- Great scanning abilities that help meet compliance requirements.
- Their services are easy to use and deploy.
- The services are scalable based on customer requirements.
Limitations
- Scanned devices can only be removed manually.
- Not a cost-effective solution
Customer Review
“Single platform for complete risk management, I appreciate the overall interface, and the support team is also very helpful with providing relevant information for the system.” – Source: G2
4. Veracode (Best for SCA)
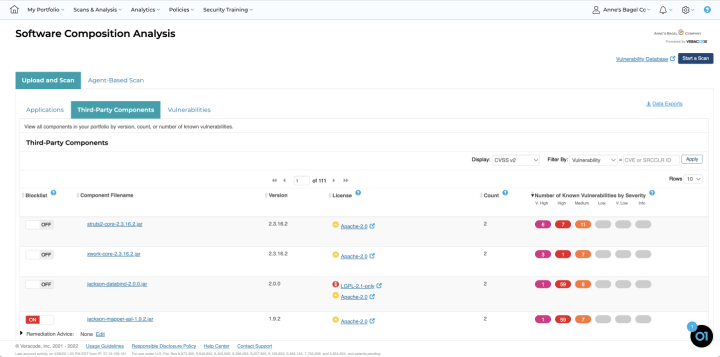
Features:
- Scanner Capacity: Web applications and Source Code Review
- Manual Pentest: Yes
- Accuracy: False positives possible
- Scan Behind Logins: Yes
- Vulnerability Management: Yes
- Compliance: NIST, PCI, OWASP, HIPAA, GDPR
- Deployment: SaaS
- Price: Quote upon request
- Rating on G2: 4.2 out of 5
Veracode is a popular online vulnerability scanner that offers multiple types of security testing: SAST, DAST, software composition analysis (SCA), and penetration testing. This online web application vulnerability scanner is designed to cope with the speed of development that comes with DevOps.
The tool lets you scan hundreds of apps and APIs simultaneously, making it the perfect web application analysis tool for large enterprises. It can detect vulnerabilities in over 10 languages and popular libraries, such as RPM, Maven, PyPi, and NPM.
For developers or pentesters, Veracode’s feature, which allows multiple sandboxes of different code to be scanned individually, makes it one of the fastest static code scanners with accurate results, allowing it to manage vulnerabilities correctly.
Experts Review
Pros
- Less than 5% rate of false positives with Veracode
- Provides automated remediation assistance.
- Flexible scan parameters
Limitations
- Zero false positives are not assured.
- Not easy to use or navigate.
- Can be difficult for beginners.
Customer Review
“A step-by-step process for SAST and DAST scans.Excellent Customer Support and a great, responsive technical assistance team.” – Hamzad K (Source: G2)
5. Nessus (Best for IT assets)
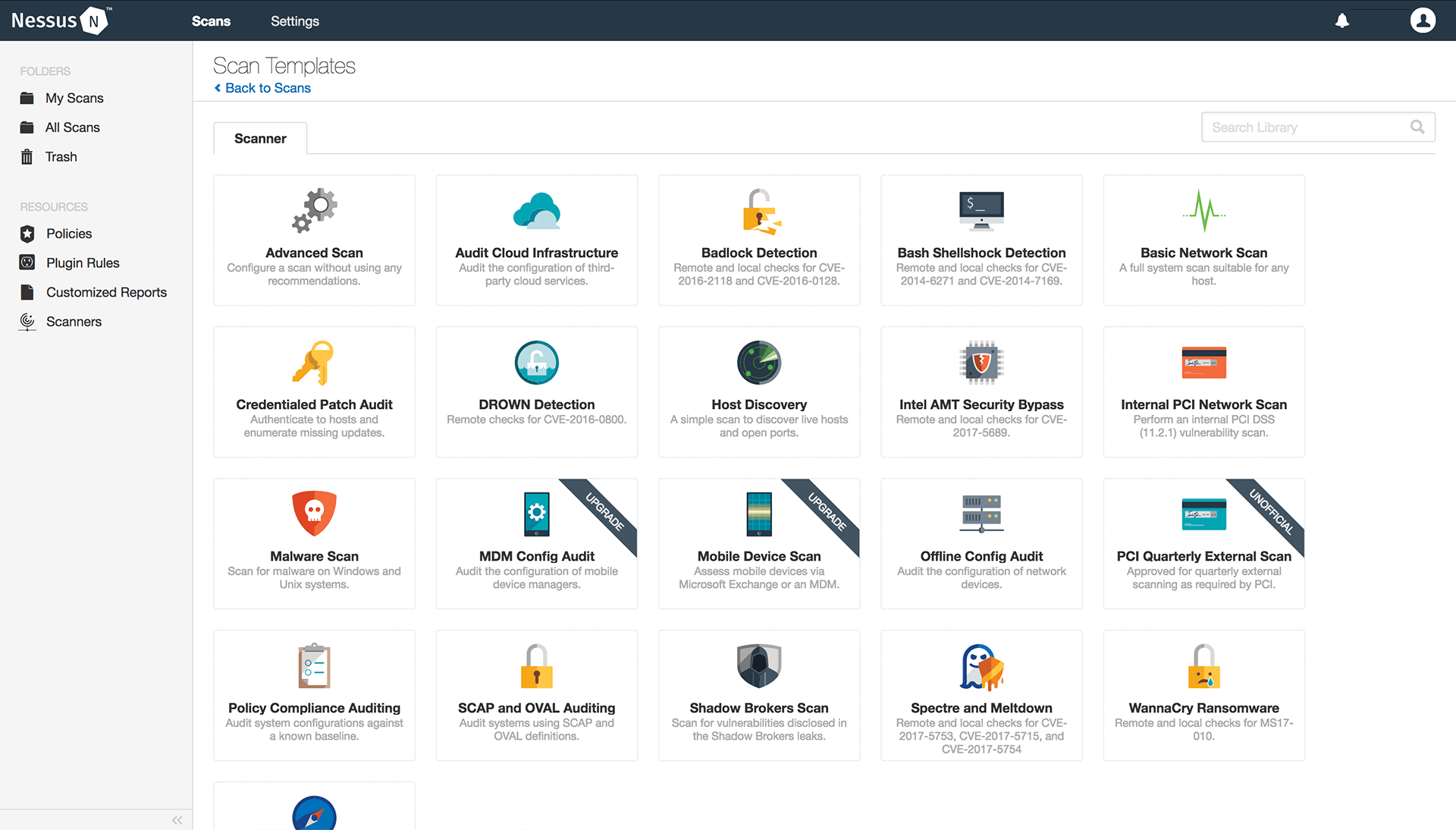
Features:
- Scanner Capabilities: web applications, network
- Accuracy: False positives possible
- Scan Behind Logins: No
- Compliance: HIPAA, ISO, NIST, PCI-DSS
- Integrations: AWS, Microsoft, Splunk
- Expert Remediation: Yes (Additional Cost)
- Deployment: Local
- Pricing: $5,880.20/ year
- Rating on G2: 4.5 out of 5
Nessus is one of the best web vulnerability scanning tools Tenable has released. It helps with point-in-time analysis of security systems to find vulnerabilities that may be plaguing them.
They also provide a detailed reporting feature that details the vulnerabilities found and the appropriate patches for them.
Nessus is a scalable vulnerability scanner ideal for achieving compliance with around 213431 plugins, covering 86938 CVE IDs and 30943 Bugtraq IDs. As a security analyst, Nessus is always up-to-date on the latest vulnerabilities and provides comprehensive coverage of all types of assets.
Experts Review
Pros
- Helps find missing patches that are critical to maintaining security.
- Point-in-time analysis of security systems.
- Helps achieve compliance with the scans.
Limitations
- Advanced support is only available upon additional payment.
- Takes time to complete scans.
- Not a cost-effective solution
Customer Review
“Nessus was very easy to install, and we were up and running in very little time. There are lots of various scan-type options to choose from. Our third-party auditors also use Nessus for internal vulnerability scans, and we were able to import their scanning template to do accurate post-remediation scans. We were able to easily set up a weekly scan schedule.” – Source: G2
6. Probely (Best for API Scanning)
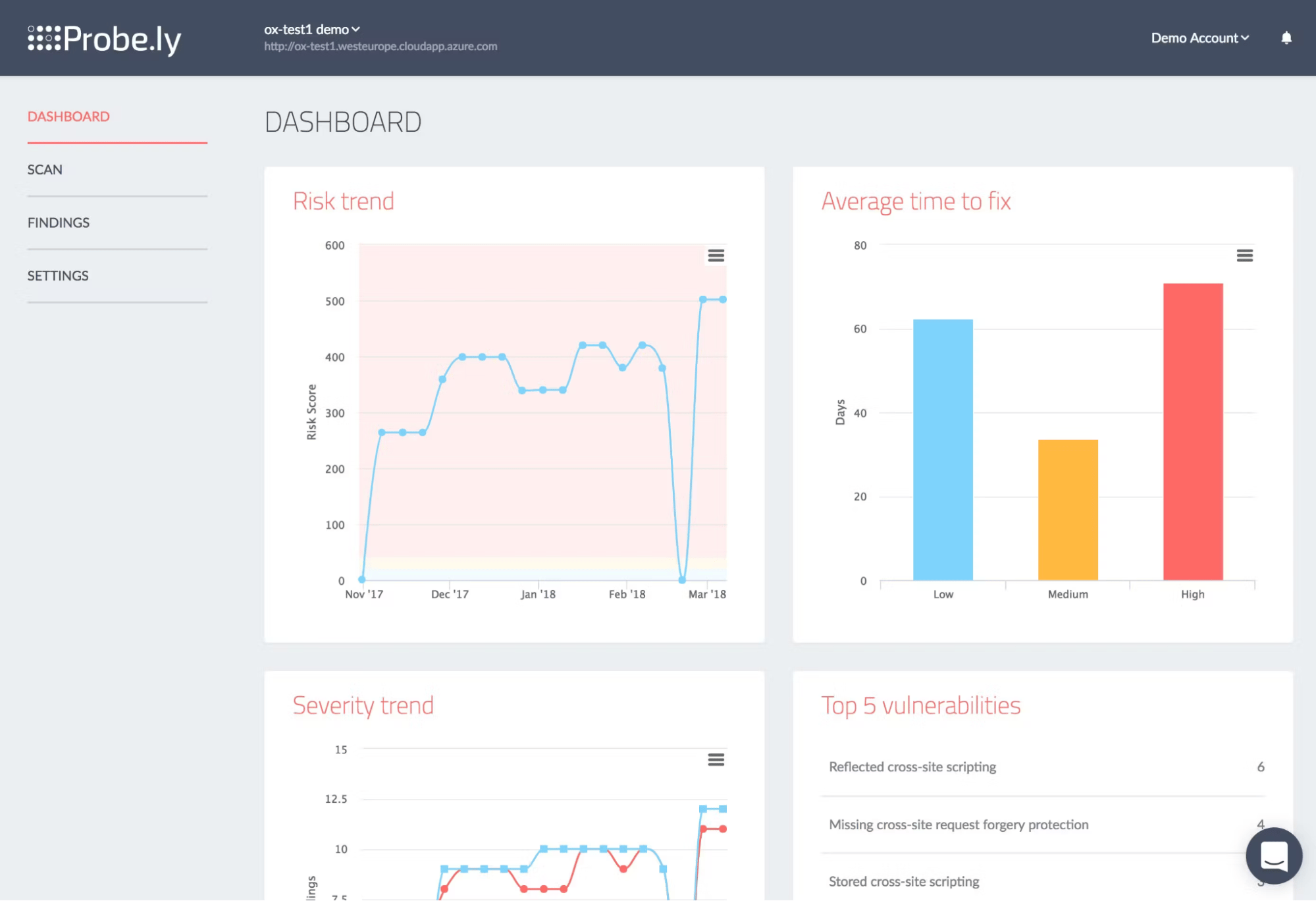
Features:
- Scanner Capabilities: Web application and API scanning
- Accuracy: False positives possible
- Scan Behind Logins: Yes
- Compliance: PCI-DSS, GDPR, ISO-27001, HIPAA
- Integrations: Microsoft Azure, Jira, Slack
- Expert Remediation: Yes
- Deployment: Saas
- Pricing: $4788/year
- Rating on G2: 4.7 out of 5
Probely’sone one of the most popular vulnerability scanners that allows easy security testing for web applications and APIs. It provides thorough reports that are easy to follow.
The tool allows unlimited vulnerability scans and provides detailed reports with risk scores, making it ideal for developers, security teams, and DevOps.
As a user, Probely easily integrates into the CI/CD pipelines and helps automate both Web Application and API security testing.
Experts Review
Pros
- Simple to use with continuous scanning.
- Wide range of tests.
- Good customer support.
Limitations
- Limited Customization in scanning and reporting
- Not easy to change targets.
- Not Cost-Effective.
Customer Review
“The implementation was fast and it was easy to configure. It can take a subnet or a range for scanning in one go and gives a full report including the URL when scanning a web application.”
– Farhan A. (Source: G2)
7. Nmap (Best Network Scanner)
Features:
- Scanner Capabilities: Network scanning
- Accuracy: False positives possible
- Scan Behind Logins: No
- Compliance: No
- Integrations: No
- Expert Remediation: No
- Deployment: Local/Command Line Tool
- Pricing: Open Source
- Rating on G2: 3.8 out of 5
Nmap is an open-source network vulnerability scanner that helps with cloud network discovery, management, and monitoring. It is designed to scan large cloud networks. However, it also works fine against singlet networks.
The tool can be used for port scanning, network mapping, service detection, and firewall evasions. For an analyst, the results from NMAP can be quite helpful during the reconnaissance phase of a pentest.
Experts Review
Pros
- Shows open ports, running serves, and other critical facets of a network
- Freely available.
- Usable for large and small networks alike
Limitations
- Complex to use for beginners.
- Might show different results each time.
Customer Review
“Nmap Online saves the convenience of doing network scans without having to install or configure the tool locally. It’s great for lightweight, quick reviews from anywhere.” – Mohit M. (Source: G2)
8. ZAP (Best for Web Application Scanning)
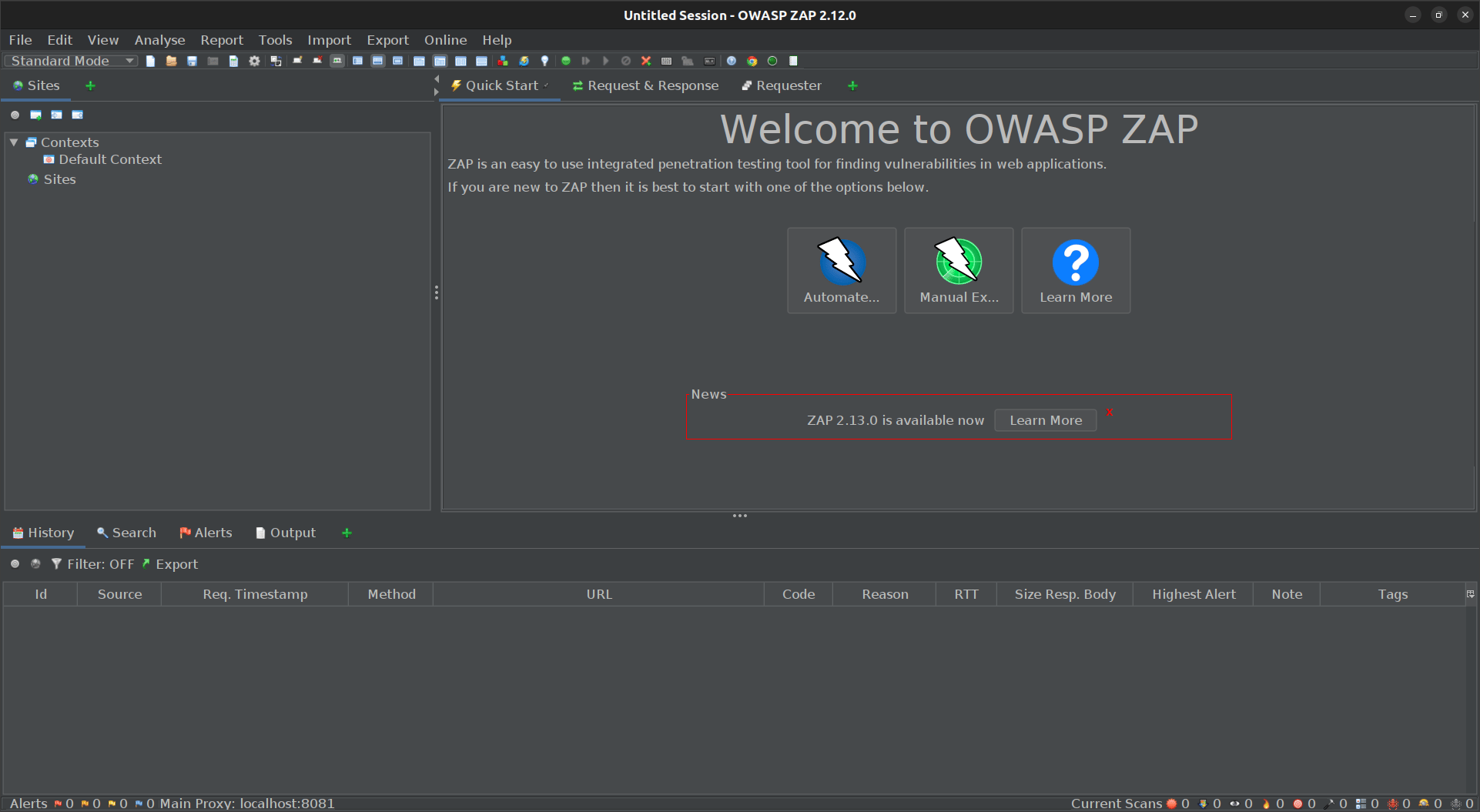
Features:
- Scanner Capabilities: Web application scanning
- Accuracy: Some false positives are possible
- Scan Behind Logins: Yes
- Compliance: No specific compliance reports
- Integrations: Jenkins, Jira, and other CI/CD tools
- Expert Remediation: No
- Deployment: Local, Docker, and Cloud
- Pricing: Open-Source
- Rating on G2: 4.7 out of 5
OWASP Zed Attack Proxy (ZAP) is an open-source web application security scanner designed to find vulnerabilities in web applications.
It is a widely used tool by security professionals and can perform automated scans and manual testing, making it versatile for various use cases for your web application security needs.
As a pentester, ZAP helps you easily discover misconfigurations and vulnerable endpoints, which you can leverage to create severe vulnerabilities.
Experts Review
Pros
- Supports automated and manual security testing.
- Integrates well with CI/CD pipelines.
- Freely available with a large community for support.
Limitations
- The learning curve can be steep for beginners.
- May produce several false positives.
Customer Review
“The OWASP ZAP can be uses in Windows and we don’t need any Linux OS. Also it is very easy to use and free of cost. We can also customise zap according to our testing need to switch certain scripts.” – VishNu C. (Source: G2)
9. Nikto (Best for Web Server Scanning)
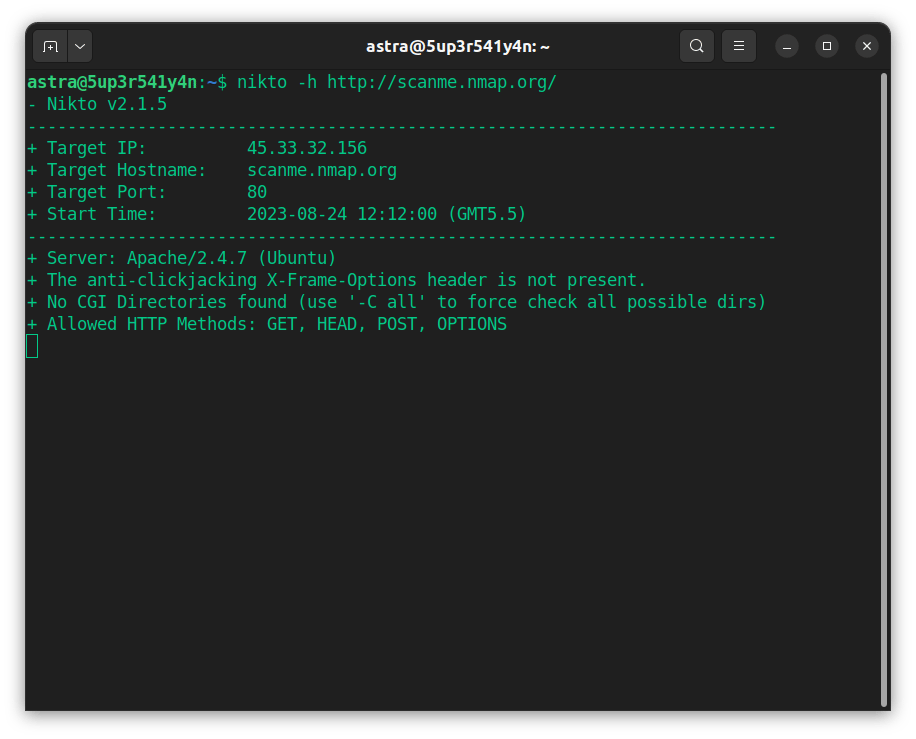
Features:
- Scanner Capabilities: Web server scanning
- Accuracy: Moderate, false positives possible
- Scan Behind Logins: No
- Compliance: No specific compliance reports
- Integrations: No
- Expert Remediation: No
- Pricing: Open Source
- Deployment: Local
Nikto is an open-source web server scanner that performs comprehensive tests against web servers for multiple items, including over 6,700 potentially dangerous files and programs. It also checks for outdated versions of servers and other issues.
Nikto is designed for penetration testing and identifying security vulnerabilities in web servers.
Using Nikto, one can quickly identify outdated software components and misconfigurations in any web server, enabling me to mitigate most of the application issues.
Experts Review
Pros
- Comprehensive web server scanning.
- Frequently updated with new vulnerabilities.
- Freely available and easy to use.
Limitations
- High number of false positives.
- Lacks advanced reporting features.
- Not suitable for stealth scanning.
10. OpenVAS (Best for Network Vulnerability Scanning)

Features:
- Scanner Capabilities: Network and web application scanning
- Accuracy: High accuracy, but some false positives are possible
- Scan Behind Logins: Yes
- Compliance: PCI-DSS, HIPAA, and other compliance frameworks
- Integrations: Various SIEM tools
- Expert Remediation: No
- Pricing: Open Source
- Deployment: Local, Docker, and Cloud
- Rating on G2: 4.4 out of 5
OpenVAS (Open Vulnerability Assessment System) is a comprehensive self-service vulnerability scanner that is part of the Greenbone Vulnerability Management (GVM) framework.
OpenVAS is designed to scan network infrastructure and web applications for security issues. It is well-suited for small and large environments and provides detailed reports and vulnerability assessments.
As security engineers say, Open VAS allows scheduled scans, saving them a lot of time by allowing them to work on other objectives while the various scans run automatically.
Experts Review
Pros
- Comprehensive scanning capabilities.
- Detailed and customizable reports.
- Frequent updates and a large vulnerability database.
Limitations
- Can be resource-intensive.
- It requires technical expertise to set up and configure it.
- The user interface can be complex for beginners.
Customer Review
“OpenVAS is a great free software for vulnerability scans, offering good performance compared to other free tools. Easy to deploy and highly configurable.” – Victor Hugo M. (Source: G2)
11. Arachni (Best for Web Application Scanning)
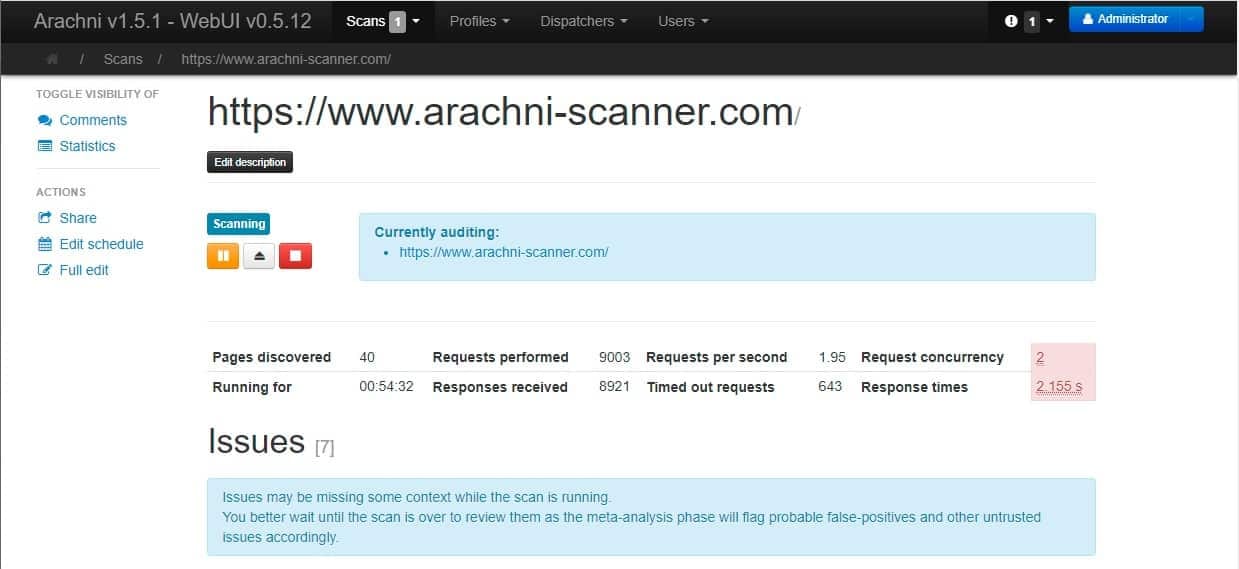
Features:
- Scanner Capabilities: Web application scanning
- Accuracy: High accuracy with low false positives
- Scan Behind Logins: Yes
- Compliance: No specific compliance reports
- Integrations: CI/CD tools
- Expert Remediation: No
- Pricing: Open Source
- Deployment: Local and Cloud
Arachni is an open-source web application security scanner designed to identify security issues within web applications. It offers a robust framework for both automatic and manual penetration testing.
Arachni effectively discovers common vulnerabilities like SQL injection, XSS, and more. It allows your security team to identify complex vulnerabilities like DOM XSS as it provides detailed and actionable insights.
Experts Review
Pros
- High accuracy and detailed vulnerability detection.
- Supports authenticated scans and can scan complex web applications.
- Freely available with extensive documentation.
Limitations
- The user interface could be more user-friendly.
- Requires significant resources for large-scale scanning.
- Limited community support compared to other tools like OWASP ZAP.
Astra Pentest is built by the team of experts that helped secure Microsoft, Adobe, Facebook, and Buffer

Features to Consider When Choosing a Vulnerability Scanner
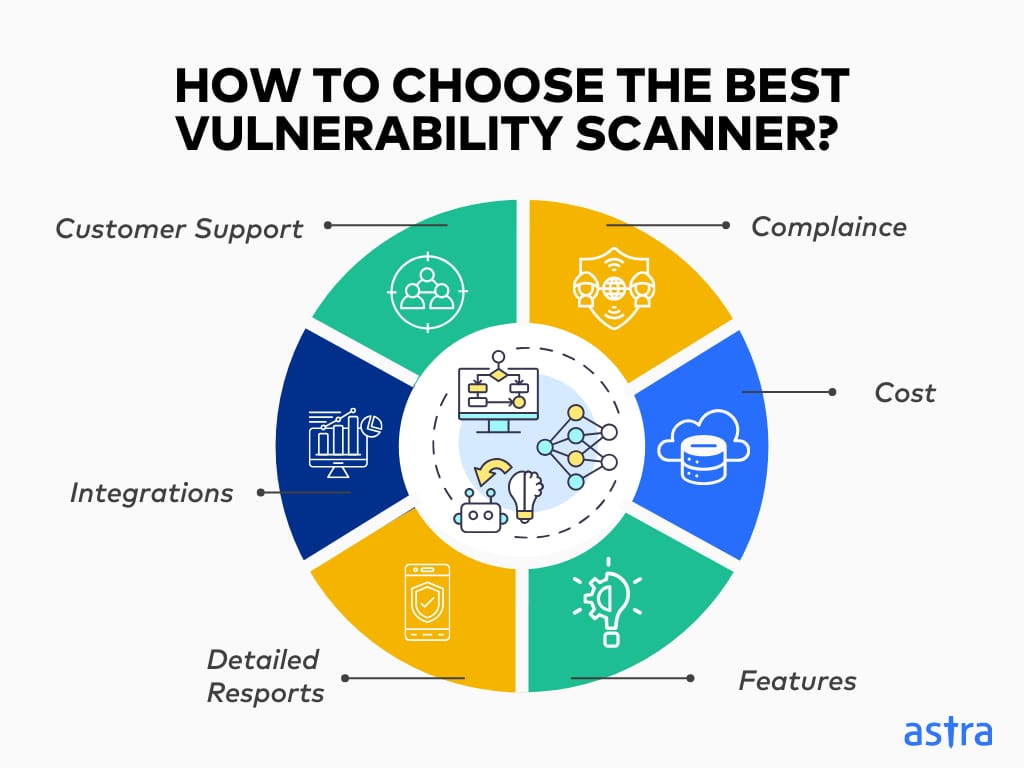
1. Cost
Based on its features and the assets it supports, an average scanner can cost anywhere from $200/month to $5000/year. Your budget should align with your assets’ needs and the extensive features required to test them.
2. Features
Analyze the features offered by each tool in your consideration to see which comes out as the winner. Every organization has different needs according to their assets and can go for scanners without extensive features, but some features that are a must can be:
- Accurate Vulnerability Detection: It should be able to test and assess the type of assets they have for a wide range of vulnerabilities precisely.
- Continuous Scanning: The tool should continuously monitor and scan assets to find hidden or new vulnerabilities that may have emerged.
- Vulnerability Management: Ensure the vulnerability scanner has a vulnerability management function that detects and remediates flaws.
3. Compliance
An ideal self-service vulnerability scanner should help you maintain compliance requirements for your assets and provide actionable insights. It should ideally support and follow the rules of major compliances like PCI-DSS, HIPAA, SOC2, GDPR, and ISO 27001.
4. Customer Support
Ensure the vulnerability scanning provider’s customer support is good and has a quick query clearance rate. Check customer reviews to understand the companies’ customer support better.
5. Integrations
A reliable vulnerability scanner should have smooth integrations with your vulnerability management and CI/CD pipeline (GitHub, GitLab, and more) and workflow software like Slack, JIRA, and more to allow a comfortable and comprehensive oversight of all tested assets.
6. Detailed Reports
Ensure that the tool provides a well-detailed report with CVSS-based risk scores, explaining and summarizing the findings of the vulnerability scan based on the scope you set. They should also include steps to reproduce and actionable mitigation suggestions to help you resolve the vulnerabilities.
Types of Vulnerability Scanners
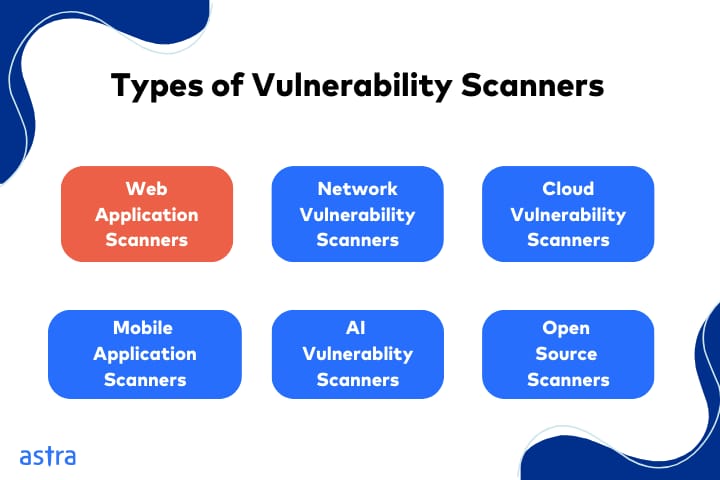
1. Web Application Vulnerability Scanners
A web application scanner is an automated tool for detecting website security weaknesses.
It performs comprehensive scans of web applications, servers, and services to detect a wide range of vulnerabilities, including but not limited to SQL Injection, Cross-Site Scripting, Session management threats, and even minor misconfigurations.
It is best suited for Web apps, Web Services, e-commerce websites, CMS Platforms.
2. Network Vulnerability Scanners
A network vulnerability scanner deeply analyzes the security posture of the network and its complete infrastructure, including routers, servers, and endpoints.
It performs scans to detect outdated or unpatched software, open ports, and misconfigurations in the network.
It is best suited for Networks, Servers, and Network devices (routers, switches, etc.).
3. Cloud Vulnerability Scanners
A cloud vulnerability scanner is a tool that assesses cloud environments, including hosted applications, for vulnerabilities and weaknesses.
It simulates attacks by sending requests from unknown entities and looking for vulnerabilities like poor access controls, weak encryptions, misconfigurations, or exposed systems within the network.
It is best suited for Cloud Infrastructure (AWS, Azure, GCP), Cloud services (SaaS, PaaS, IaaS), Containers, and Cloud storage.
4. API Vulnerability Scanners
An API vulnerability scanner is an automated tool for rigorously pentesting APIs for security weaknesses.
It performs intensive scans for vulnerabilities such as weak authorization, improper authentication, sensitive information leakage, or even injection attacks.
It is best suited for REST, SOAP, GraphQL, Microservices, etc.
5. Mobile App Vulnerability Scanners
A mobile application vulnerability scanner is a tool that tests mobile applications for security weaknesses.
These scanners simulate Code Reviews, SAST, and DAST techniques to look for vulnerabilities such as weak encryption, sensitive information in source code, and insecure data storage.
It is best suited for Android, iOS, and hybrid apps (React Native, Flutter, etc.)
5. Enterprise Vulnerability Scanners
An Enterprise Vulnerability scanner is extremely scalable and suitable for large companies with many assets.
Such tools also often offer vulnerability management services as a part of their package to ensure a hassle-free vulnerability detection and remediation experience for customers.
They combine application, network, cloud, and API scanners.
It is suitaible for the complete IT infrastructure of an enterprise, including networks, servers, workstations, endpoints
6. Open-Source Vulnerability Scanners
An open-source vulnerability scanner is a cost-effective solution for security personnel and small companies that provide most of the features of a commercial tool.
It can detect misconfigurations, unpatched or old software, and other vulnerabilities but necessitate technical know-how, in-depth knowledge of assets, and pentesting techniques.
It is best suited for Web Applications, e-commerce platforms, and Networks.
7. AI Vulnerability Scanners
An AI Vulnerability scanner is a tool that tests AI models and systems for security vulnerabilities. These tools test AI algorithms, datasets, and deployment configurations for vulnerabilities like model inversion, data poisoning, or data privacy breaches.
It is best suited for organizations that develop AI models (Image Recognition, NLP, and more).
Recommended Reading: Detailed guide to vulnerability scanning process and types
How Astra Vulnerability Scanner Helps?
As a leading tool, Astra vulnerability scanner offers a unique blend combining automation and manual expertise to offer a 360° view of an organization’s security posture with continuous proactive insights, real-time reporting, and AI-first defensive strategies.
Designed to help CTOs shift left at scale with continuous scanning, our seamless tech stack integrations, tailored reporting solutions, and expert support help make cybersecurity simple, effective, and hassle-free for hundreds of businesses worldwide.
Still don’t believe us? Check out what 700+ customers have to say!
Final Thoughts
In conclusion, scanning tools help you adopt a proactive approach to security by detecting security weaknesses beforehand. While Qualys and Nessus offer good enterprise plans, Astra Vulnerability scanner offers good plans for startups and enterprises to help you secure every type of asset and provide the most extensive features.
Selecting the right vulnerability scanning software based on your asset’s needs is important for efficient and effective security management. Moreover, although vulnerability scanners have their own limitations, combining them with a pentest can help navigate them.
Lastly, although they may be an annual investment, the benefits of continuous monitoring and regression scanning are definitely worth it!
FAQs
What can vulnerability scanners not do?
A vulnerability scanner provides an in-depth view of a vulnerability’s impact if it is exploited. However, vulnerability scans can also raise false positives, which can result in companies spending time and money fixing vulnerabilities that didn’t exist.
What are the advantages of vulnerability scanners?
Security vulnerability scanner can help companies assess their security systems in a budget-friendly manner with continuous monitoring and fast results. They help organizations meet the regulatory compliance requirements for all their digital assets.
How does a vulnerability scanner detect threats?
Vulnerability scanners have a database with all known CVEs.They send customized requests to the endpoints and review the responses, to which the vulnerabilities detected are matched for correct identification.
Explore Our Vulnerability Scanning Series
This post is part of a series on Vulnerability Scanning. You can also check out other articles below.

- Chapter 1: What is Vulnerability Scanning?
- Chapter 2: Types Of Vulnerability Scanning
- Chapter 3: Vulnerability Scanning Report: Things You Should Know
- Chapter 4: Best Vulnerability Scanners of 2025
- Chapter 5: Best Web Application Vulnerability Scanners
- Chapter 6: Top Cloud Vulnerability Scanners for AWS, GCP & Azure
- Chapter 7: Top 7 GCP Vulnerability Scanning Tools
- Chapter 8: 7 Best AWS Vulnerability Scanners
- Chapter 9: Best Free Vulnerability Scanners
- Chapter 10: Best Android Vulnerability Scanners
- Chapter 11: Best Vulnerability Assessment Tools







