As an experienced web application tester, I’ve seen the web landscape evolve from static HTML pages to complex applications today with JavaScript frameworks, serverless architectures, and AI integrations.
Unfortunately, many traditional web application vulnerability scanners haven’t kept up with this evolution and aren’t equipped to handle the complexities of web apps. As a security analyst, I’ve spent several hours sifting through available web app vulnerability scanners to identify the most adaptable scanners, and I came up with the list below.
List of Top 13 Web App Vulnerability Scanners:
- Astra Pentest
- Acunetix
- Invicti
- Burp Suite
- Nessus
- Rapid7
- Intruder
- Cobalt
- BEeF
- W3af
- ZAP
- Veracode
- Checkmarx
Comparison of Top 3 Web Application Vulnerability Scanners
| Features | Astra Pentest | Acunetix | Invicti |
|---|---|---|---|
| Platform | Online | Online | Online |
| Vulnerability Tests | 10,000+ | Scans for 7000+ vulnerabilities | Scan for 1400+ vulnerabilities |
| SDLC/ Workflow Integration | Slack, JIRA, GitHub, GitLab, and Jenkins | GitHub, JIRA, and Atlassian | JIRA, GitHub, GitLab, Kenna, and Bitbucket |
| Accuracy | Zero False Positives via Vetted Scans | False positives possible | False positives possible |
| Scan Behind Login | Yes | No | No |
| Support for SPAs | Yes | Yes | Yes |
| Compliance Scanning | PCI-DSS, HIPAA, GDPR, ISO27001, & SOC2 | OWASP, SOC2, NIST, HIPAA, and ISO27001 | PCI-DSS, HIPAA, and ISO 27001 |
| Custom Reports | Yes | No | Yes |
| Price | Starting at $199/m | Available on quote | Available on quote |

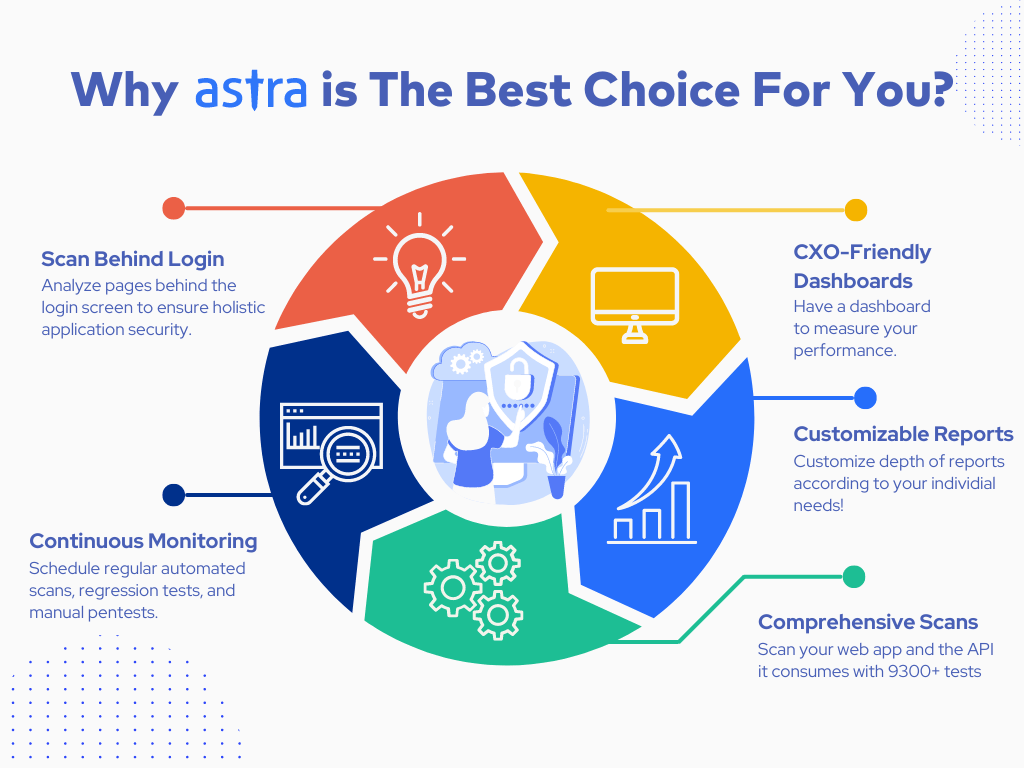
Why is Astra Vulnerability Scanner the Best Scanner?
- We’re the only company that combines automated & manual pentest to create a one-of-a-kind pentest platform.
- Vetted scans ensure zero false positives.
- Our intelligent vulnerability scanner emulates hacker behavior & evolves with every pentest.
- Astra’s scanner helps you shift left by integrating with your CI/CD.
- Our platform helps you uncover, manage & fix vulnerabilities in one place.
- Trusted by the brands you trust like Agora, Spicejet, Muthoot, Dream11, etc.

13 Best Web Application Vulnerability Scanner Tools
1. Astra Pentest

Key Features
- Scanner Capacity: Run 10,000+ tests on web applications and API
- Accuracy: Zero False Positives Assured (Vetted Scans)
- Vulnerability Management: Custom detailed reports with remediation assistance and PoC videos
- Continuous Monitoring: Yes
- Compliance: GDPR, PCI-DSS, HIPAA, ISO27001, and SOC2
- Integrations: GitHub, GitLab, Jenkins, JIRA, and Slack
- Price: Starts at $199/month
Customer Review:
“Astra is a great tool for finding vulnerabilities and can be used to address possible risks. The best part of this tool is that it provides a detailed report of much needed vulnerabilities.”
Source: Gartner
Built to identify vulnerabilities outlined by industry standards like OWASP, NIST, and SANS25, Astra’s web application vulnerability scanner runs 9300+ tests to pinpoint new, emerging, and existing vulnerabilities.
Updated every fortnight, the tool also scans the API integrations and calls your application relies on to ensure complete safety against open ports and subdomain takeover attacks.
With zero false positives guaranteed through vetted scans, a CXO-friendly dashboard, and an AI-powered chatbot, it brings you the best of both worlds. Moreover, its smart Chrome extension helps record logins for simplified scanning of protected screens and user roles.
Don’t believe us? Take a look at what our customers have to say!
Pros
- Seamlessly integrates with your CI/CD pipeline.
- Quick turnaround with GPT-powered chatbot
- Generate custom executive and developer-friendly reports
- Offers manual penetration testing and contextual expert consultation
Limitations
- Only 1-week free trial is available
It is one small security loophole v/s your entire website or web application.
Get your web app audited with
Astra’s Continuous Pentest Solution.

2. Acunetix

Key Features
- Scanner Capacity: Continuous scanning for web apps to detect 7000+ vulnerabilities
- Accuracy: False positives are possible
- Vulnerability Management: Yes
- Continuous Monitoring: Yes
- Compliance: OWASP, SOC2, NIST, HIPAA, and ISO 27001
- Integrations: GitHub, JIRA, and Atlassian
- Price: Available on quote
Customer Review:
“Acunetix has a user-friendly UI, is easy to configure and run, and produces reliable results. The licensing model is not as granular as it could be which means that planning is needed for scaling up or down.”
Source: G2
As one of the intelligent web application vulnerability scanning tools, Acunetix prioritizes automating various repetitive tasks, such as finding vulnerabilities, creating tickets for developers, and retesting fixes. It also scans SPAs and other script-heavy websites.
Designed to detect OWASP Top 10 vulnerabilities, it can detect common vulnerabilities like SQL injections, Misconfigurations, and XSS. With lightning-fast scans, it also offers detailed remediation guidance and compliance-specific scans.
Pros
- Reporting template is easy to understand
- Smooth scanning of post-login modules
Limitations
- Vulnerability PoCs can be complex for beginners
- Errors with performing credential scans
3. Invicti
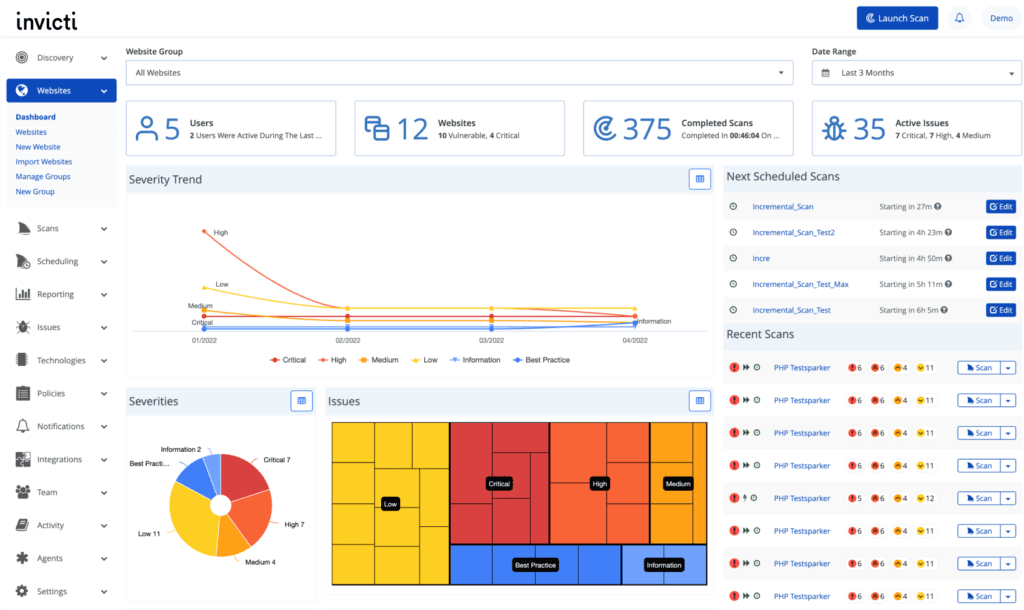
Key Features
- Scanner Capacity: Conducts 1400+ scans
- Accuracy: False positives are possible
- Vulnerability Management: Yes
- Continuous Monitoring: Yes
- Compliance: PCI-DSS, HIPAA, and ISO 27001
- Integrations: JIRA, GitHub, GitLab, Kenna, and Bitbucket
- Price: Available on quote
Customer Review:
“Invicti, which is Netsparker, provided me with a major vulnerability database to find remote execution vulnerabilities, domain invalidation, and many vulnerability patches, which allows me to find CVE scores as well. Recurrent scanning allows me to fetch files at an integrity level. Sometimes, it failed to fetch the database at server and back end levels.”
Source: G2
Boasting over 250 test cases, 1400+ tests, and proprietary Proof-Based Scanning, Invicti identifies and confirms vulnerabilities. Moreover, it integrates seamlessly with your CI/CD pipeline, promoting the “shift-left” security approach of early and frequent testing.
It pinpoints various threats, including OWASP10 CVEs across web pages, web applications, web services, and APIs, such as command injection and remote file inclusion.
Pros
- Easy to use and set up
- Active support team
Limitations
- Scanning for API endpoints can be improved
- Certain features in the on-premise version are not available in the online version
4. Burp Suite
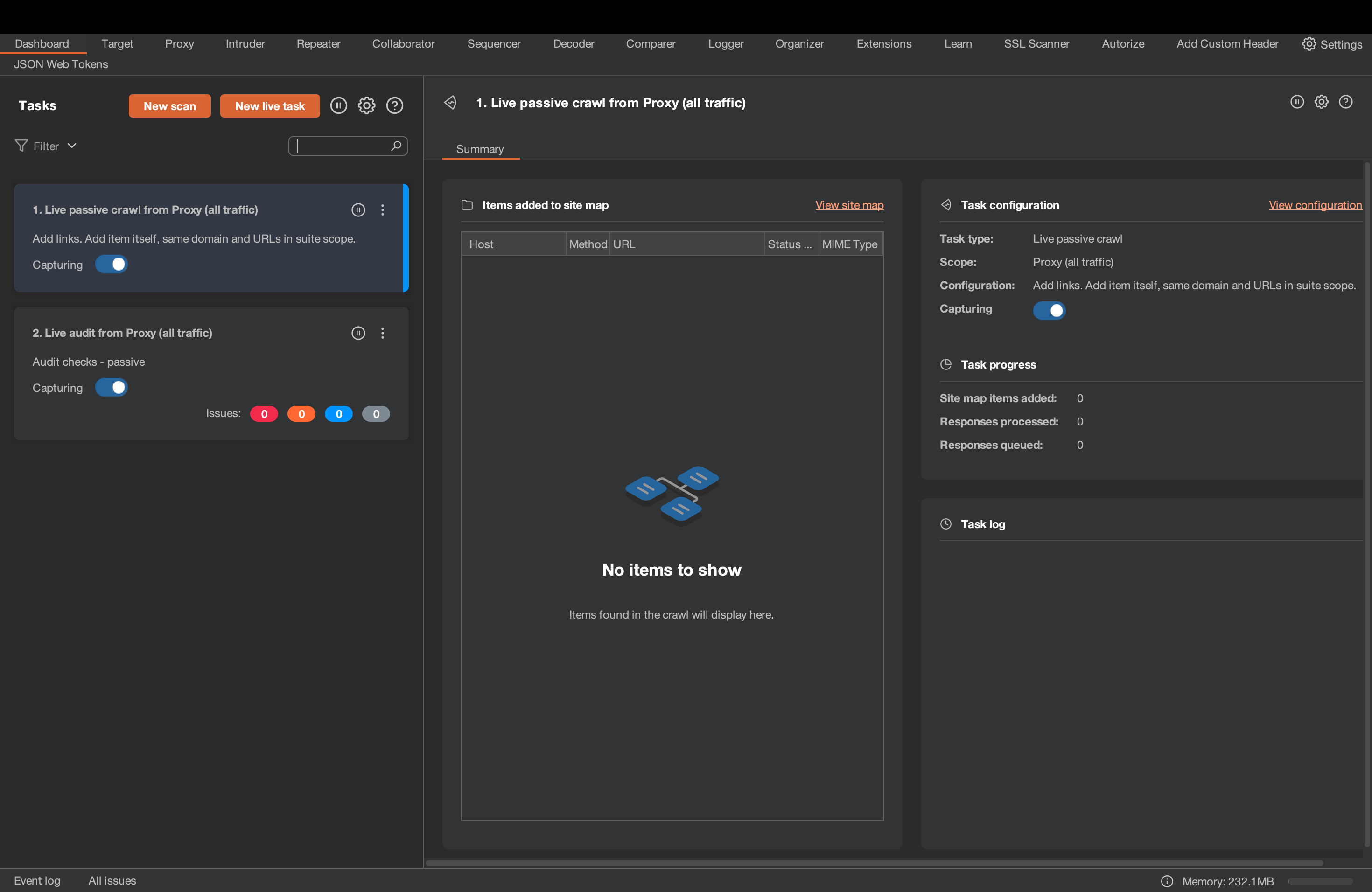
Key Features
- Scanner Capacity: Scan for over 2500+ test cases
- Accuracy: False positives are possible
- Vulnerability Management: Yes
- Continuous Monitoring: Yes
- Compliance: PCI-DSS, HIPAA, and GDPR
- Integrations: Slack, JIRA, Jenkins, and GitLab
- Price: $449/yr/user
Customer Review:
“One of the best proxy tools for bug bounty hunters and penetration testers. Nothing can be disliked; every professional loves it.”
Source: G2
The Burp Suite Scanner equips you to scan web applications by intercepting and manipulating web traffic, automating repetitive tasks, fuzzing parameters, and brute-forcing logins.
Its crawler mimics testers, tackling complex apps with dynamic content, unreliable connections, and massive API usage. With 2500+ test cases, Burp Suite helps identify 300+ vulnerabilities, including common ones like broken authentication and XSS.
Pros
- Smooth integration with CI/CD Pipeline
- Offers a community edition as well
Limitations
- A few cases of app crashes and socket connection bugs have been reported
- Burp Crawler sometimes misses out on end-points
5. Nessus
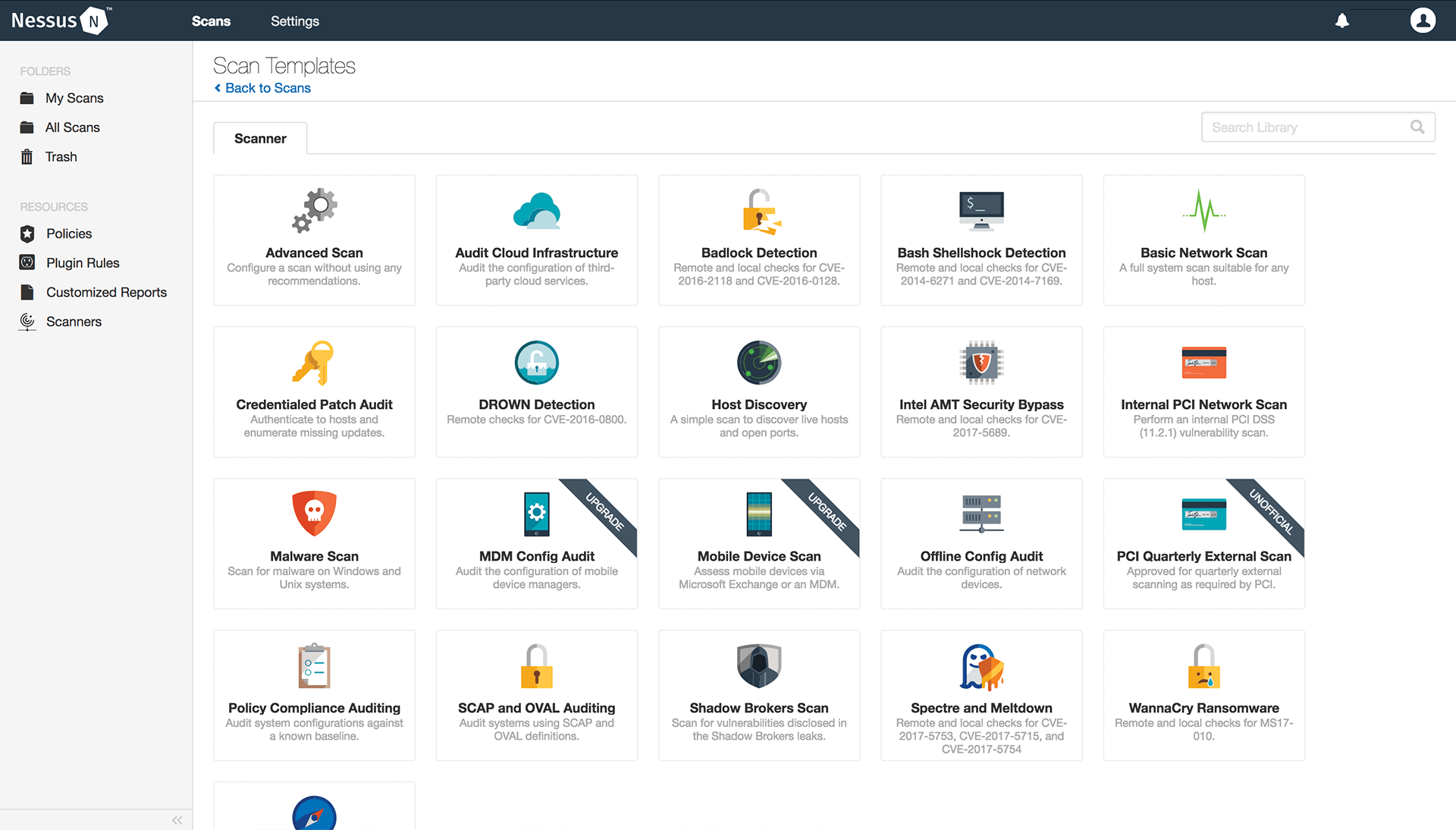
Key Features
- Scanner Capacity: Scans for 34K+ CVEs in web apps
- Accuracy: False positives are possible
- Vulnerability Management: Available at extra cost
- Continuous Monitoring: Yes
- Compliance: HIPAA, ISO, NIST, and PCI-DSS
- Integrations: GitLab, GitHub, IBM Security, and Splunk
- Price: Starting at $6195
Customer Review:
“Nessus has one of the largest libraries of vulnerability and configuration checks, covering a wide range of systems, devices, and applications. While Nessus is known for its comprehensive vulnerability scanning capabilities, it can sometimes produce false positives, leading to unnecessary work for security teams.”
Source: G2
Available under the Tenable umbrella, Nessus is a mature web application vulnerability scanner that helps you scan up to five different web application URLs per 90 days, including SPAs and third-party components it consumes.
Its extensive database of CVEs and automation features empower you to streamline your web application security testing. However, depending on the target and depth of the scan, the scanning timelines may vary significantly.
Pros
- Detailed reporting with filters and trends
- Offers significant automation capacity for scanning tasks
Limitations
- Limitations in managing false positives properly
- Scanning speed and resource consumption can be a concern
6. Rapid7
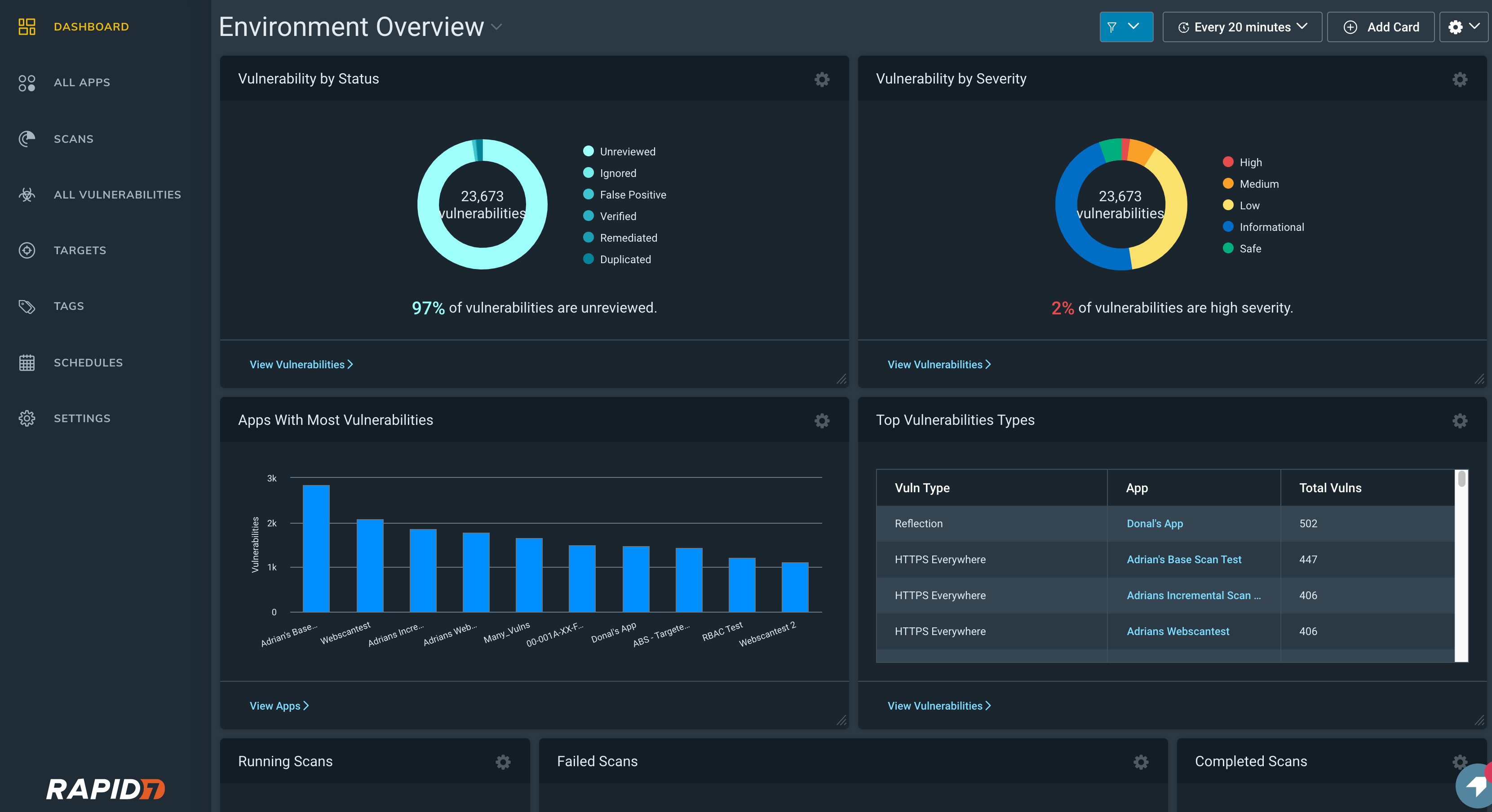
Key Features
- Scanner Capacity: Capable of running 95+ attack types on your web app
- Accuracy: False positives are possible
- Vulnerability Management: Yes
- Continuous Monitoring: Yes
- Compliance: CIS, ISO 27001, and PCI DSS
- Integrations: ServiceNow Security Operations, LogRhythm NDR, and ManageEngine
- Price: Available on quote
Customer Review:
“We’ve used Rapid7 for our Vulnerability Testing and Alert Messaging, Threat Intelligence, Risk Management, Endpoint Protection, etc. They have proved invaluable in providing a complete and effective solution.”
Source: G2
Rapid7’s InsightAppSec automates web security with black-box testing, prioritizing vulnerabilities to streamline risk remediation. It allows you to scan multiple targets simultaneously with no downtime.
The user-friendly tool identifies over 95 attack types, including common threats like CSRF and SQL injection, with transparent reporting and integration options.
Pros
- Simple interface and resources for beginners
- Offers graph representation and vulnerability management
Limitations
- Slow turnaround on fixing bugs in the product
- Can be high priced for SMEs and startups
Astra Pentest is built by the team of experts that helped secure Microsoft, Adobe, Facebook, and Buffer

7. Intruder
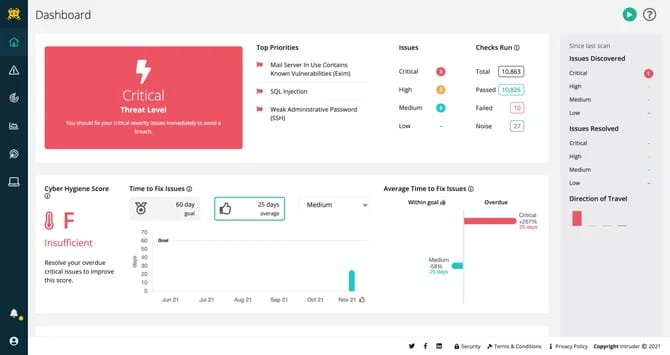
Key Features
- Scanner Capacity: Automated scanner that scans for 65000+ vulnerabilities
- Accuracy: False positives are possible
- Vulnerability Management: Yes
- Continuous Monitoring: Yes
- Compliance: SOC2 and ISO 27001
- Integrations: GitHub, JIRA, and Azure DevOps
- Price: Starts at $1652/ year
See how emerging Intruder.io alternatives outperform older platforms in cloud asset discovery and remediation tracking.
Customer Review:
“Their quality of service and expertise are both of high standard, and I’d have no hesitation in recommending to others who are serious about security. However, since the last price increase they are significantly more expensive than competitors.”
Source: G2
Capable of scanning multi-page and SPAs, Intruder’s online web application vulnerability scanner for web apps also scans their underlying infrastructure and protected screens. It offers straightforward and actionable reports that are evidence-based to guide remediation and foster a proactive security culture.
Built on efficiency, your teams receive prioritized tickets for identified vulnerabilities within hours of a scan. Once patches are implemented, a quick rescan confirms their effectiveness.
Pros
- Automated zero-day/ emerging threat scans
- Intuitive and comprehensive user interface
Limitations
- The pricing is a bit steep
- Remediation guidance can be a bit generic at times
8. Cobalt
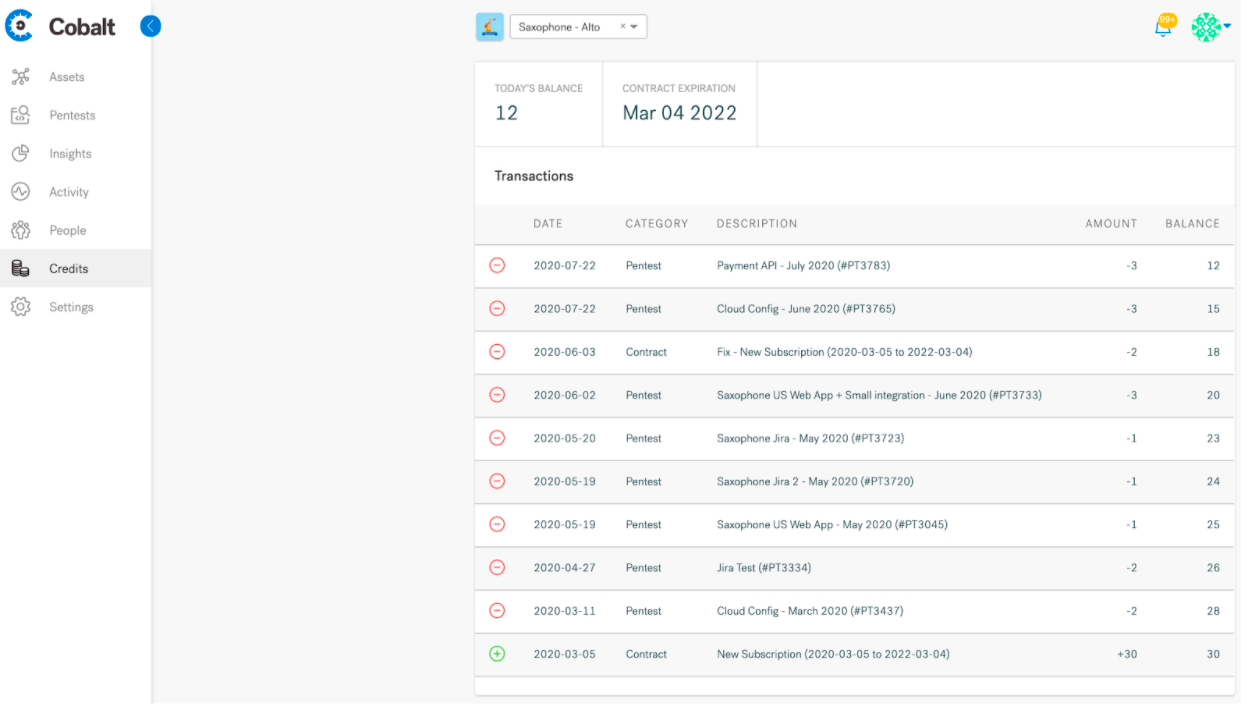
Key Features
- Scanner Capacity: Automated scanner that scans for 13+ categories of vulnerabilities
- Accuracy: False positives are possible
- Vulnerability Management: Yes
- Continuous Monitoring: Yes
- Compliance: PCI-DSS, HIPAA, SOC 2, and ISO 27001
- Integrations: JIRA, GitHub, Azure DevOps, and JupiterOne
- Price: Starts at $8,500
Customer Review:
“Very good at penetration testing. They knew to ask questions about our solution implementation so that the functionality was clear before getting into the pentest. They could have been more updates given as testing was conducted. Once the functionality was cleared up, there was only communications that the test had started and ended.”
Source: G2
Cobalt’s DAST for web apps keeps you constantly secure. It provides continuous monitoring with regression testing to catch new vulnerabilities and ensure successful remediation. It’s login form authentication that helps you scan behind login screens.
Detailed reports help you meet compliance standards effortlessly, keeping your applications secure around the clock, while retests verify patches for complete peace of mind.
Pros
- High-quality pentest reports
Limitations
- Requests for retesting can take longer than expected
- The pricing model can be slightly confusing
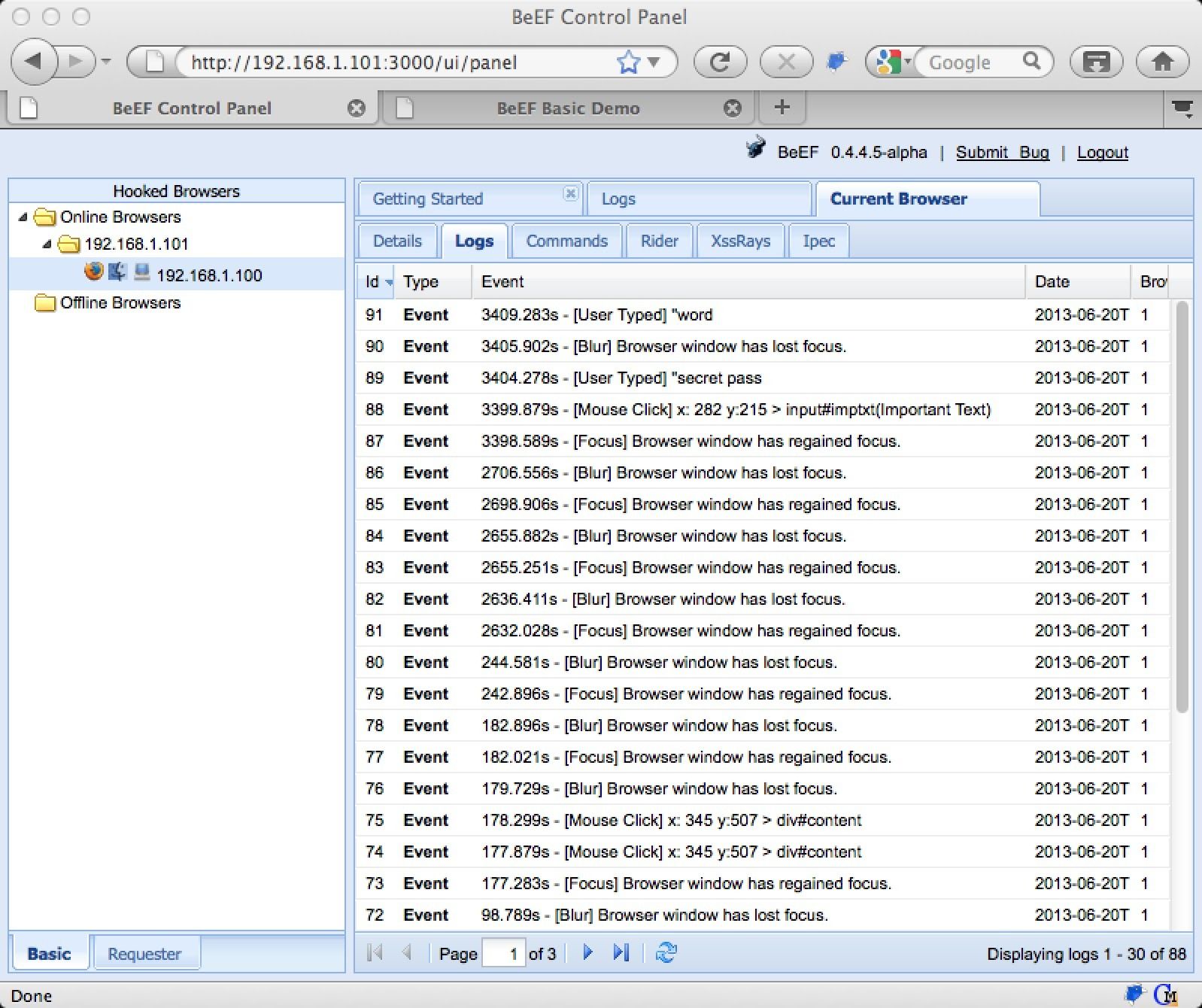
9. BeEF
Key Features
- Scanner Capacity: Social engineering for in-depth vulnerability assessments
- Accuracy: False positives are possible
- Deployment Capabilities: Can be installed from sources, pre-built packages, and via Docker
- Vulnerability Management: No
- Continuous Monitoring: No
- Compliance: None
- Price: Open-source
Customer Review:
“It uses a client-side attack vector to assess the security posture. No complex setup, ease of use. Initial setup takes time but it’s smooth once done.”
Source: G2
BeEF (Browser Exploitation Framework) is an open-source web security scanner that hooks into web browsers to simulate real-world attacks and expose vulnerabilities. It helps you assess an asset’s overall security posture.
Known for its simple UI, it equips you to analyze the potential consequences of a breach, such as traffic redirection, keystroke logging, and sensitive data theft.
Pros
- Helps analyze post-exploitation impacts
- Easy to include additional payloads
Limitations
- Database configuration can be a little difficult
- Not supported on Linux and macOS
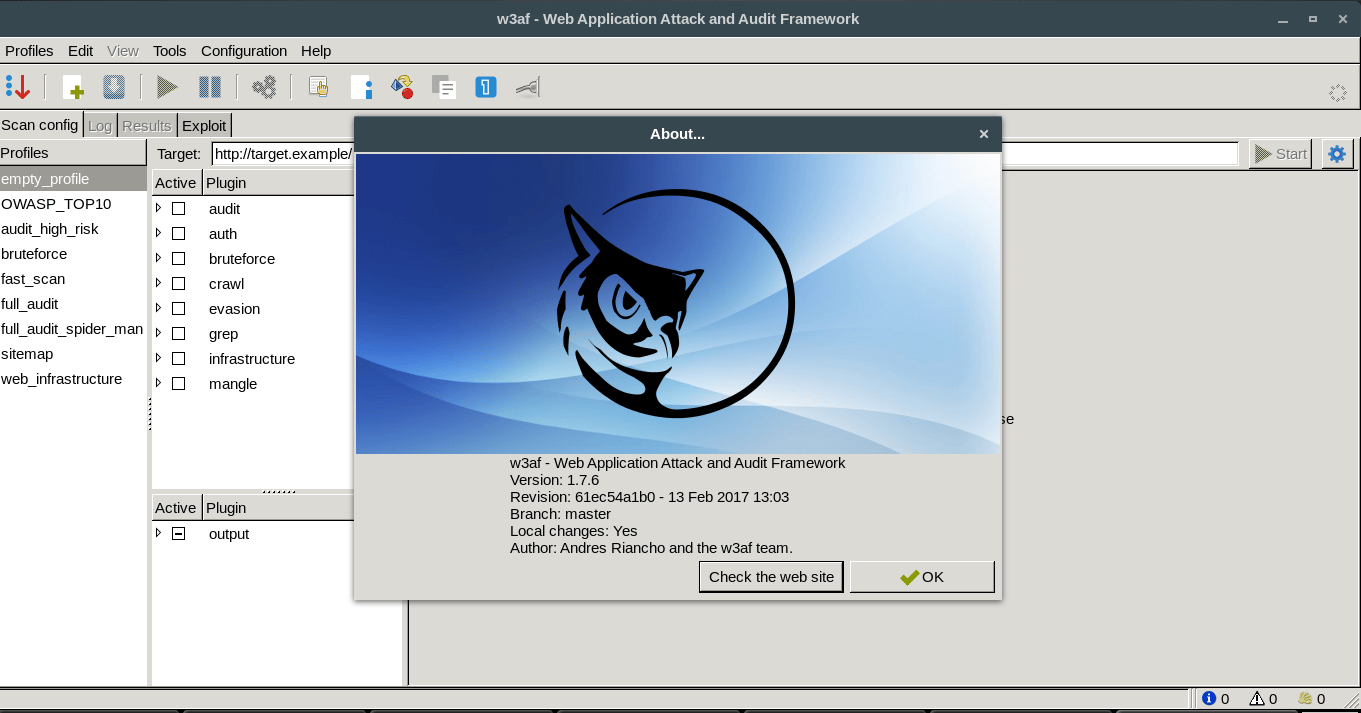
10. W3af
Key Features
- Scanner Capacity: Automated and manual penetration testing
- Accuracy: False positives are possible
- Deployment Capabilities: Manual installation from source code pre-built packages and Docker
- Vulnerability Management: No
- Continuous Monitoring: No
- Compliance: None
- Price: Open-source
Customer Review:
“Haltdos WAF is a reliable security solution that provides comprehensive protection for websites and APIs from OWASP top 10 attacks, as well as known and 0-day vulnerabilities. It offers robust layers of defense against malicious threats, making it an ideal choice for organizations that value security and performance.”
Source: G2
W3af, or the Web Application Attack and Audit Framework, empowers you to manually test vulnerabilities, assess their severity, and even exploit them in a controlled environment. It delivers exceptional stability across various OSs, such as Windows, Linux, and OS X.
Its modular design allows you to write custom plugins and leverage existing ones that seamlessly communicate with each other. Moreover, it offers a user-friendly graphical interface (GUI) and a powerful command-line interface (CLI) to suit your preferences.
Pros
- Provides manual exploit customizations
- Offers a fuzzy and manual request generator
Limitations
- Some cases of connector run failures have been observed
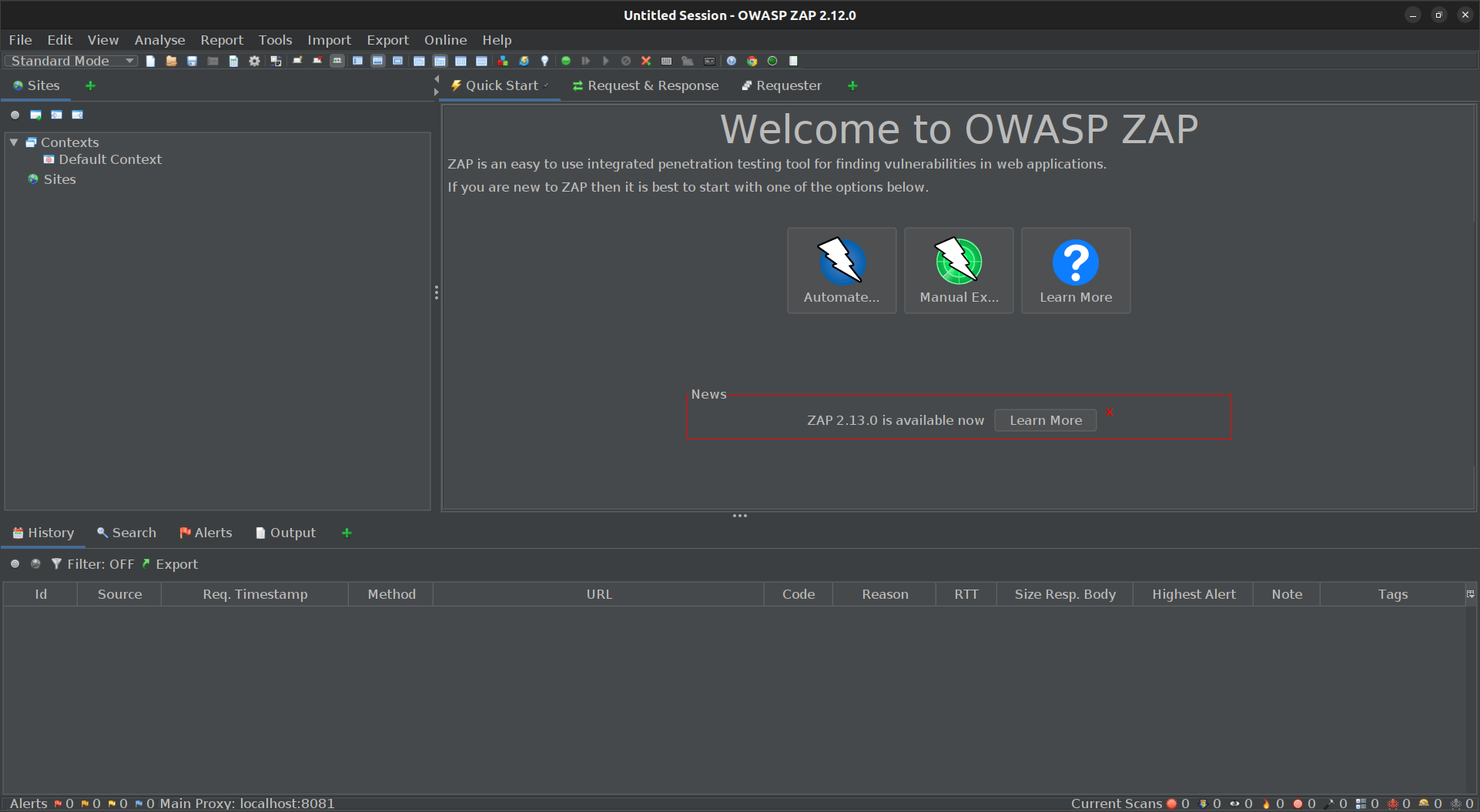
11. ZAP
Key Features
- Scanner Capacity: Automated and manual penetration testing
- Accuracy: False positives are possible
- Deployment Capabilities: Manual installation from source code pre-built packages and Docker
- Vulnerability Management: No
- Continuous Monitoring: No
- Compliance: OWASP
- Price: Open-source
Customer Review:
“The data extract and transformation process, using ZAP Data Hub, has opened up our ability to consume data from a myriad data sources and data source types. It used to be that excel was needed to join the data into a comprehensive data set. With ZAP Data Hub we can set up the pipelines once for all to use. Values are now reported consistently across the organization.“
Source: G2
ZAP (Zed Attack Proxy) empowers security analysts with various scanning modes, such as passive, active, and fuzzing, for a well-rounded approach. It acts as a MitM Proxy, letting you intercept, analyze, and modify traffic between your browser and any web application.
It helps you manipulate sessions, probe for vulnerabilities with fuzzing, and simulate brute-force attacks. This cross-platform tool works on Linux, Mac, and Windows.
Pros
- Designed as per OWASP10 and WSTG
- Community-developed plugins improve functionality
Limitations
- Can consume a lot of memory or CPU resources
- Loading optimization for session files could be improved.
Additional Knowledge:
What is a web vulnerability scanner?
A web vulnerability scanner is your digital watchdog, tirelessly inspecting your web application for potential weaknesses.
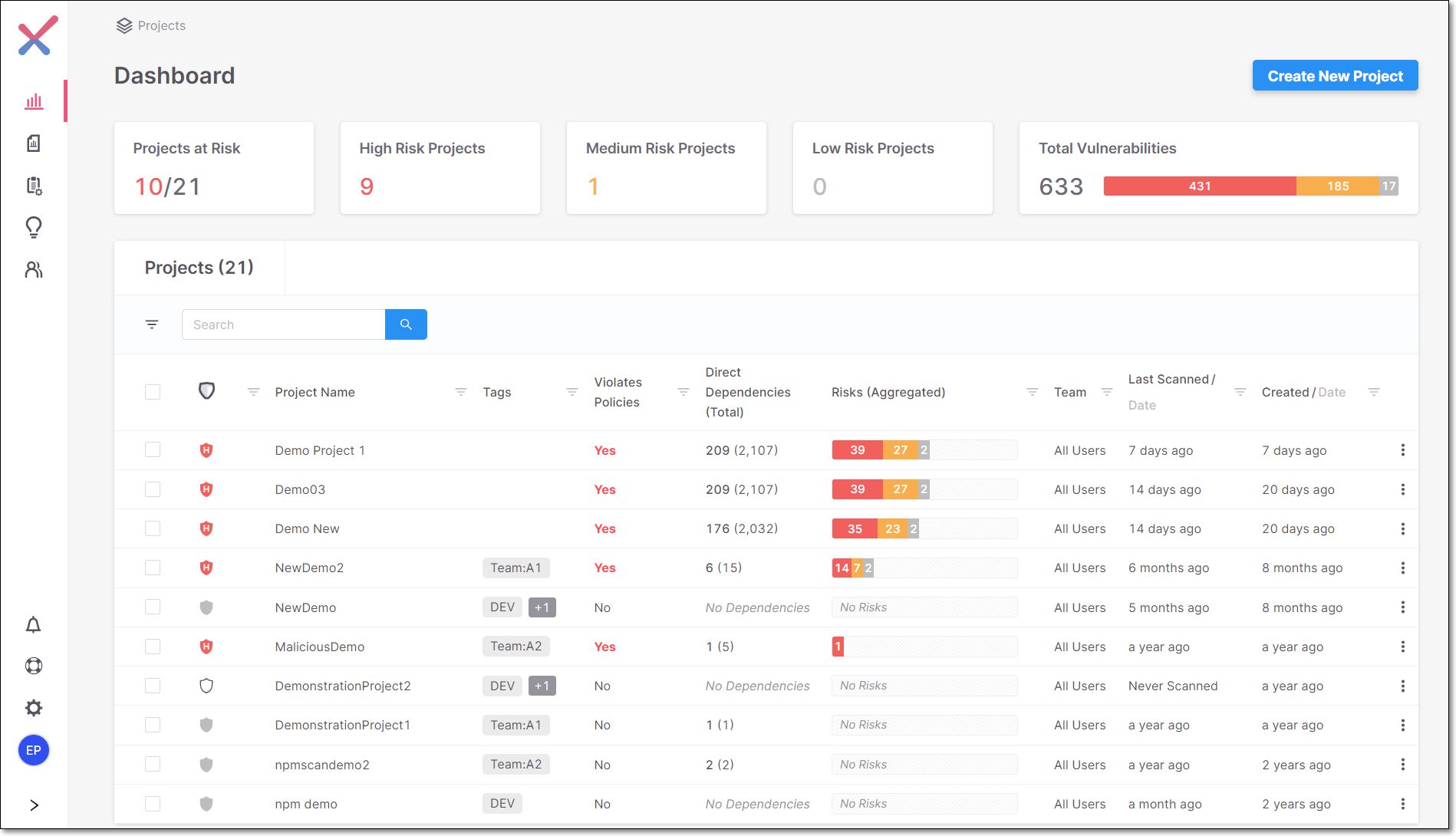
12. Veracode

Key Features
- Scanner Capacity: Static and dynamic application security testing
- Accuracy: Focuses on reducing false positives
- Vulnerability Management: Yes
- Continuous Monitoring: Yes
- Compliance: PCI DSS, HIPAA, SOX, and others
- Integrations: Jira, Jenkins, and DevOps tools
- Price: Available on quote
Customer Review:
“It’s a tool to make a static code scan and detect the exposed secrets or passwords before the application is released. We can create multiple sandboxes and run various parts of the code individually. Veracode can be easily integrated with CI/CD pipelines, making it easy to trigger the scan.”
Source: G2
Veracode offers a comprehensive application security platform that includes static and dynamic analysis. It focuses on identifying vulnerabilities early in the development lifecycle and providing actionable remediation guidance. Veracode also offers a software composition analysis (SCA) component to address open-source vulnerabilities.
Pros
- Strong focus on developer integration
- Extensive vulnerability database
- Supports multiple programming languages
Limitations
- Can be expensive for smaller organizations
- May require additional tools for specific vulnerability types
13. Checkmarx
Key Features
- Scanner Capacity: Static, dynamic, and interactive application security testing
- Accuracy: False positives are possible
- Vulnerability Management: Yes
- Continuous Monitoring: Yes
- Compliance: PCI DSS, HIPAA, and SOX
- Integrations: Jira, Jenkins, and DevOps tools
- Price: Available on quote
Customer Review:
“I like the SAST-ification thing overall; it has all offerings that vary from source code scans to license scanning and does a great job finding vulnerabilities. It is easy to use and visually easy to look around for the bugs. Similarly very optimized so that we can integrate with the CI/CD pipelines.”
Source: G2
Checkmarx is a comprehensive application security platform that includes a web application vulnerability scanner. It offers static, dynamic, and interactive application security testing (IAST) to provide a comprehensive view of application security risks. The tool emphasizes code analysis and security best practices.
Pros
- In-depth code analysis capabilities
- Strong focus on preventing vulnerabilities
- Supports multiple programming languages
Limitations
- Can be complex to set up and configure
- May require specialized expertise for effective use
What Features Should You Look For in A Web App Scanner?
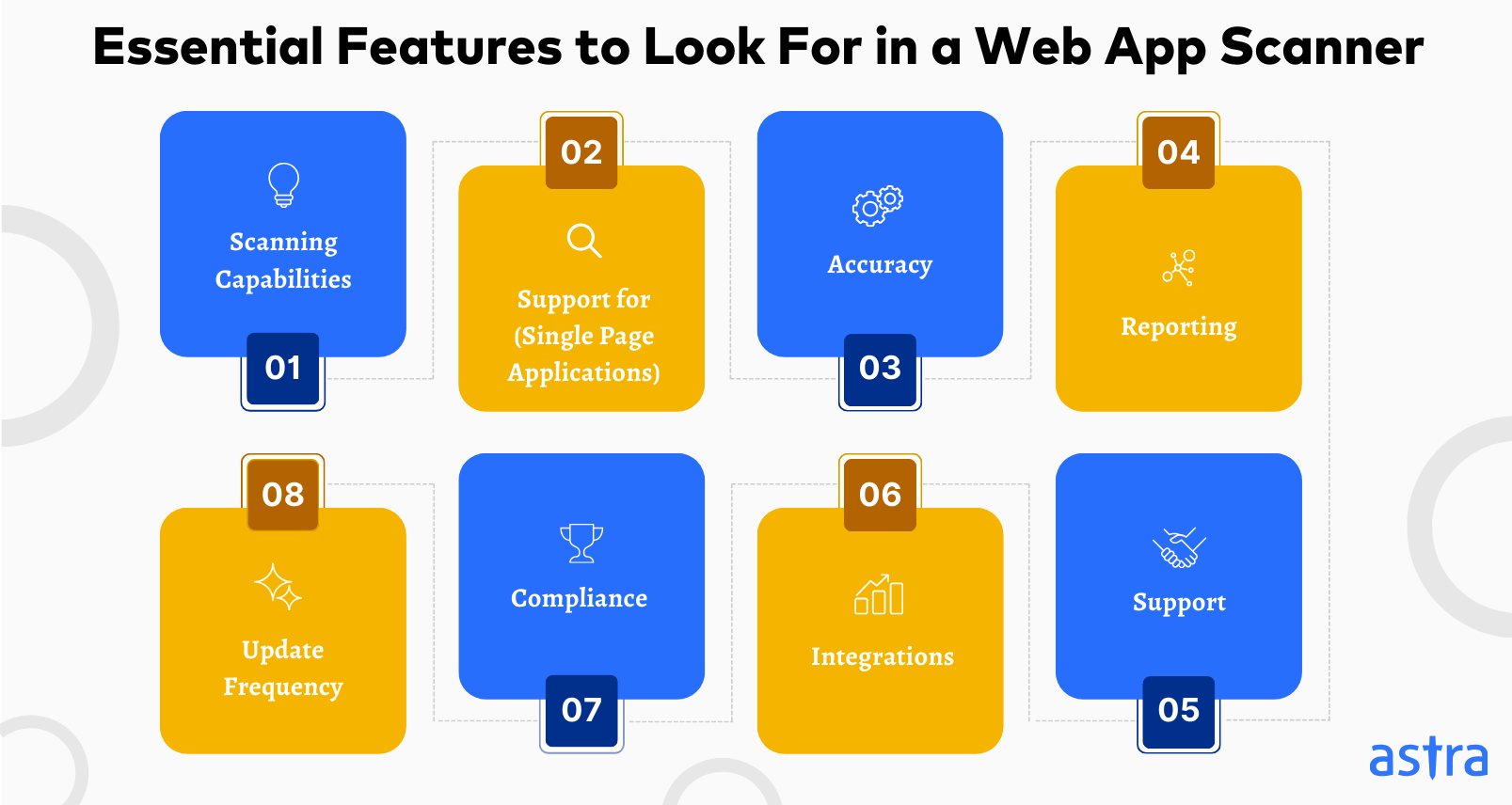
1. Comprehensive DAST Scanning Capabilities:
Opt for a DAST web app scanner with a library of pre-configured tests targeting common vulnerabilities like SQL Injections and Cross-Site Scripting (XSS) with pattern matching, fuzzing, contextual analysis, and brute force attacks.
2. Support for SPAs (Single Page Applications)
Traditional web app scanners struggle with single-page applications (SPAs) because they rely on crawling server-side responses, missing vulnerabilities hidden in client-side logic and dynamic content. Scanners should mimic user interactions, navigate complex routing, and understand API calls.
3. Minimal False Positives
To avoid wasting time and resources, focus on scanning tools for your web app that offer minimal or zero false positives. Opt for tools that employ configurable scan profiles to flag common patterns that align with secure coding practices and can help identify potentially malicious use of special characters.
4. Tailor-Fitted Reporting
Choose an automated web application vulnerability scanner that offers custom, exhaustive reports with vulnerability details, CVSS score, prioritization, and step-by-step remediation. Look for concise reports for management executives to facilitate smooth decision-making and exhaustive reports with PoC (Proof of Concept) videos for developers, avoiding bottlenecks.
5. Seamless Integrations
A good web vulnerability scanner should offer integrations for vulnerability data to be seamlessly fed into existing ticketing systems like JIRA, pre-populated with relevant details of the CVE to streamline the process of assigning and tracking remediation tasks. Consider scanners that integrate with your development environment, such as GitHub or GitLab.
6. Round-the-Clock Support
Immediate or quick turnaround on technical support is a priority in a web app scanner. While AI chatbots can be helpful, human support is non-negotiable in addressing complex issues and avoiding bottlenecks. Consider scanners that offer various support channels, such as Slack, email, and live chat.
7. Frequent Updates
With 40,009 new vulnerabilities and CVEs identified in 2024 alone, our security scanners, among other measures, need to keep pace with such a changing landscape. Choose a scanner that offers frequent updates with new test cases, specifically designed to detect recently discovered vulnerabilities, known zero-day exploits, and evolving attack vectors.
8. Compliance-Specific Scans
All commercial enterprises are often subject to national and international regulations and standards, such as GDPR, HIPAA, SOC2, and PCI DSS. Pick a year-round compliance-specific scan tailored to address specific control requirements, like a PCI DSS scan or a HIPAA scan.
“As a cyber security professional, using tools that provide in-depth scans , have a large knowledge base and provide easy integrations with your internal development tools like Jira and GitHub help you proactively measure your security posture on a regular basis.”
How to Choose the Best Web App Scanning Tool For You?
Meet Your Security Requirements:
First and foremost, identify your specific security needs. Are you primarily concerned with common vulnerabilities like SQL injections (often detected by SAST) or zero-day exploits requiring a DAST approach?
Moreover, while general scanners cast a wide vulnerability net, ideal for broad security checks, compliance scanners target specific regulations (PCI DSS) with tailored controls and reporting. Thus, while highly accurate, they might miss vulnerabilities outside the regulation’s scope.
Pro Tip: Prioritize your security needs first to choose a scanner that delivers the most relevant, efficient, and effective protection without a feature overload or potential gaps in coverage.
Ensure Scalability and Performance:
While SAST and DAST offer complementary security assessments, SAST excels at finding code vulnerabilities early (like SQL injection) but might miss runtime issues. On the other hand, DAST catches real-world vulnerabilities but requires a running application.
Consider both technical fit and impact. For large applications, prioritize scalability and features like integration with development environments (SAST) or context-aware scanning (DAST) to minimize bottlenecks and streamline remediation.
Leverage Remediation Support:
Does the scanner provide clear guidance on fixing vulnerabilities it identifies? The best web application vulnerability scanner offers detailed remediation steps (e.g., code patches for SQL injection flaws), prioritization based on severity, and PoC videos.
Consider whether the vendor offers additional support options, such as training or integration with your existing tech stack and vulnerability management tools. Moreover, A quick turnaround on tickets can be the difference between a successful and a 3-month delay.
Vendor Reputation and Support:
Research the vendor’s track record in security expertise, product updates, and customer support. Choose a vendor with a strong reputation, good ratings on aggregator platforms such as G2 & Gartner, and reliable support to ensure you have the resources to utilize the scanner effectively.
Final Thoughts
Securing your web applications requires a vigilant approach, and choosing the right web app scanning tools is a critical first step. Understanding your distinct needs as a company or a security analyst will guide you toward a tool that delivers actionable insights and efficient vulnerability management.
Prioritize features like extensive scanning capabilities, robust SPA support, and minimal false positives. Consider seamless integrations, responsive support, and regular updates when choosing the best web application vulnerability scanner.
Most importantly, don’t settle for generic solutions. Invest in a PTaaS platform like Astra that aligns with your priorities, scales efficiently, and keeps you ahead of evolving threats.
FAQs
What is the #1 most commonly reported web vulnerability?
There isn’t a single universally agreed-upon “#1” but according to the OWASP Top 10, Broken Access Control takes the crown. This means websites have flaws in how they restrict access to data and functionality, potentially allowing unauthorized users to see or modify sensitive information.
How to secure a web application from vulnerabilities?
Securing your web application involves vigilance throughout its lifecycle. Always validate user input to prevent injection attacks and encrypt sensitive data. Enforce strong access controls, and regularly test your application with security scans and web app penetration tests to identify and fix vulnerabilities.
What is the difference between web application scanning and DAST?
The terms web application scanning and DAST (Dynamic Application Security Testing) are often used interchangeably. Web application scanning can refer to any automated test that checks a web application for security vulnerabilities. DAST (Dynamic Application Security Testing) is a specific type of web application scanning that mimics real-world attacks to uncover weaknesses.
What is web application vulnerability scanning?
Web application vulnerability scanning is a process of identifying security weaknesses and vulnerabilities in a web application. It can be performed manually or using automated tools, and helps to protect the application from cyberattacks.
What is Vulnerability Scanning?
Vulnerability scanning looks for weaknesses and loopholes in computer systems and their software that could be exploited by hackers with malicious intent. Significant risks can be mitigated by preventatively finding and resolving these vulnerabilities. This can be performed using an automated scanner or manually, but combining both is the most effective.
What are Web Vulnerability Scanning Tools?
Web vulnerability scanning tools are automated tools that scan web applications for security weaknesses. Some examples of the vulnerabilities they look for are insecure server configuration, cross-site scripting (XSS), SQL injection, and cross-site request forgery (CSRF).
Explore Our Vulnerability Scanning Series
This post is part of a series on Vulnerability Scanning. You can also check out other articles below.

- Chapter 1: What is Vulnerability Scanning?
- Chapter 2: Types Of Vulnerability Scanning
- Chapter 3: Vulnerability Scanning Report: Things You Should Know
- Chapter 4: Best Vulnerability Scanners of 2025
- Chapter 5: Best Web Application Vulnerability Scanners
- Chapter 6: Top Cloud Vulnerability Scanners for AWS, GCP & Azure
- Chapter 7: Top 7 GCP Vulnerability Scanning Tools
- Chapter 8: 7 Best AWS Vulnerability Scanners
- Chapter 9: Best Free Vulnerability Scanners
- Chapter 10: Best Android Vulnerability Scanners
- Chapter 11: Best Vulnerability Assessment Tools