AWS is known to be one of the most secure platforms for hosting cloud data. However, it has also experienced several data breaches. The May 2022 Pegasus Airlines breach, in which over 23 million people’s private information was leaked, was one of the most significant AWS breaches.
As one of the world’s biggest cloud platforms, AWS faces some challenges in maintaining its security. However, contrary to popular belief, the onus of data security doesn’t solely fall on AWS. It is shared between the user and AWS as per the shared responsibility model.
This article will discuss an AWS vulnerability scanner, specific features to look for when choosing one, and the top 7 vulnerability scanners for AWS.
Best AWS Vulnerability Scanning Tools
- Astra Security
- AWS Inspector
- Rapid7
- Alert Logic
- Qualys
- Aqua Security
- Orca Security
What Is An AWS Vulnerability Scanner?
AWS vulnerability scanners are tools that are capable of conducting automated scans within the AWS platform to detect security gaps, vulnerabilities, and loopholes that pose a threat to the organization and its assets in AWS.
Upon detection of vulnerabilities through continuous AWS cloud security scans, security and development teams can take up the appropriate security measures to mitigate and patch them.

Why is Astra Vulnerability Scanner the Best Scanner?
- We’re the only company that combines automated & manual pentest to create a one-of-a-kind pentest platform.
- Vetted scans ensure zero false positives.
- Our intelligent vulnerability scanner emulates hacker behavior & evolves with every pentest.
- Astra’s scanner helps you shift left by integrating with your CI/CD.
- Our platform helps you uncover, manage & fix vulnerabilities in one place.
- Trusted by the brands you trust like Agora, Spicejet, Muthoot, Dream11, etc.

Top 7 AWS Security Scanning Tools
1. Astra Security [Book a Demo]

Key Features:
- AWS Scanning Capabilities: Continuous automated scans with manual tests
- Specialization: Combined automated and manual testing, zero false positives
- Compliance Scanning: PCI-DSS, HIPAA, ISO27001, and SOC2
- Workflow Integration: Slack, JIRA, GitHub, GitLab, Jenkins, and more
- Price: Starting at $1999/yr. Better pricing, tailored to you. Book a call to unlock it
Astra Pentest combines the automated Astra Vulnerability Scanner, which scans for 10,000+ test cases, including OWASP Top 10, SANS 25 vulnerabilities, and emerging vulnerabilities, with manual pentesting capabilities.
With our vetted scans, we ensure zero false positives. Astra’s login recorder plugin makes it convenient for the scanner to run authenticated scans behind login pages without requiring you to reauthenticate every scan.
Our user-friendly vulnerability management dashboard lets you stay on top of vulnerabilities throughout the scanning process. Astra’s Pentest Platform can be used for web app pentests, mobile app pentests, API pentests, and cloud-configuration reviews.
Our reports include video PoCs and step-by-step remediation guidelines to help you act immediately. The platform also enables your developers to collaborate contextually with Astra’s security engineers to resolve complex issues.
Pros
- Integrates into your CI/CD pipeline.
- Offers continuous scanning with regularly updated scanner rules.
- Ensures zero false positives.
- Helps with rapid prioritization and remediation of vulnerabilities.
Limitations
- We don’t offer a free trial yet, but we provide a $7/week trial.
2. AWS Inspector
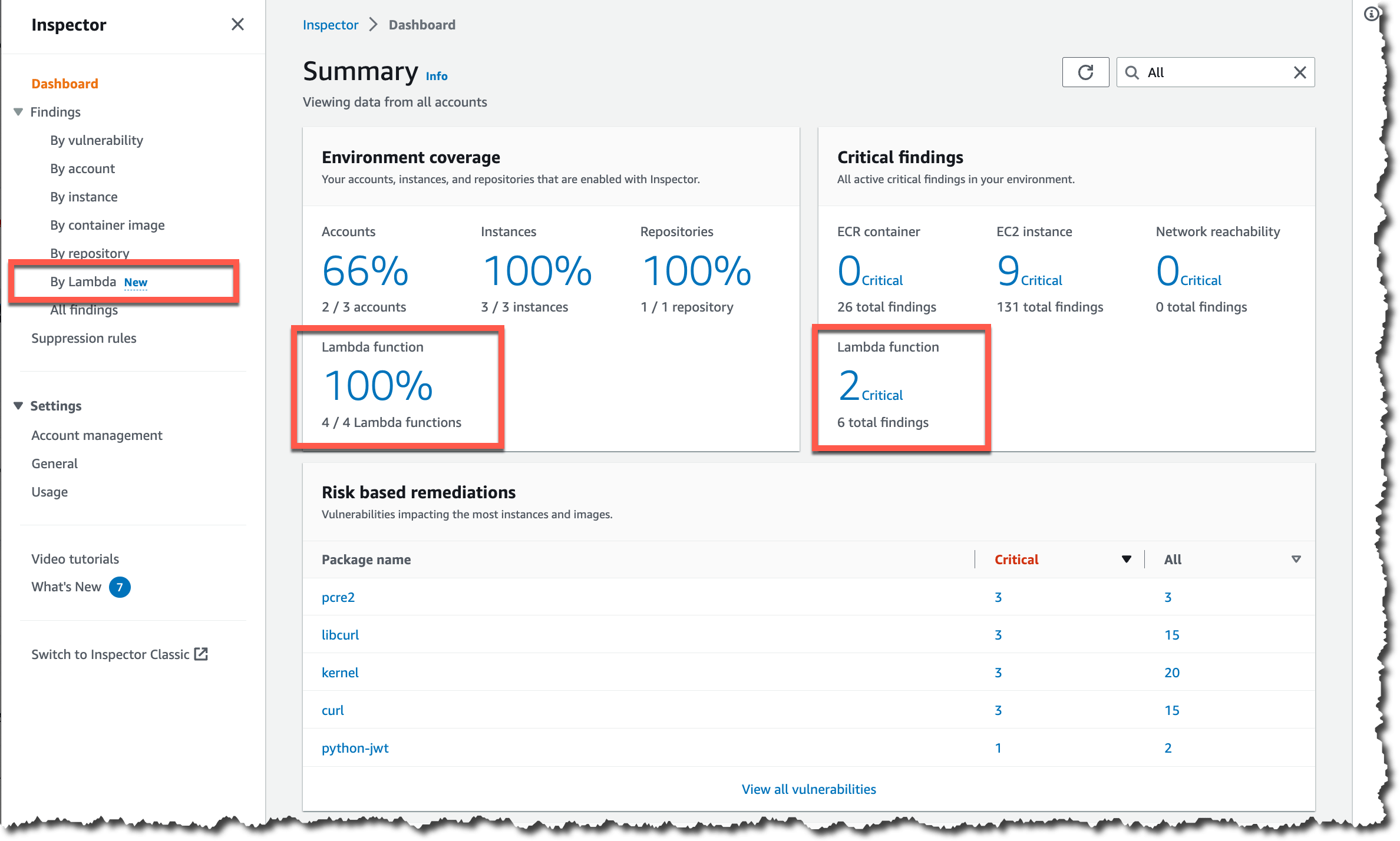
Key Features:
- AWS Scanning Capabilities: AWS only, automated security assessment service for EC2 instances
- Specialization: Detection of vulnerabilities and security deviations
- Vulnerability Management: No
- Price: Quote on Request
AWS uses an automatic security assessment tool called Amazon Inspector to verify that EC2 instances can reach the network. Applications running on the AWS platform are more secure because they stray from recommended practices and identify vulnerabilities.
Once enabled, it discovers EC2 instances and images within the Amazon ECR (Elastic Container Registry) and starts assessing them for flaws or areas of exposure. It provides a highly contextualized risk score that factors in many criteria through the correlation between CVEs, network accessibility, and exploitability.
Pros
- Proactive identification of security issues.
- Easy to use with intuitive UI.
- Reports allow the identification and tackling of issues before deployment.
Limitations
- Findings can be challenging to prioritize.
- The tool gives out inaccurate false worry warnings.
- Glitches in the software.
3. Rapid7
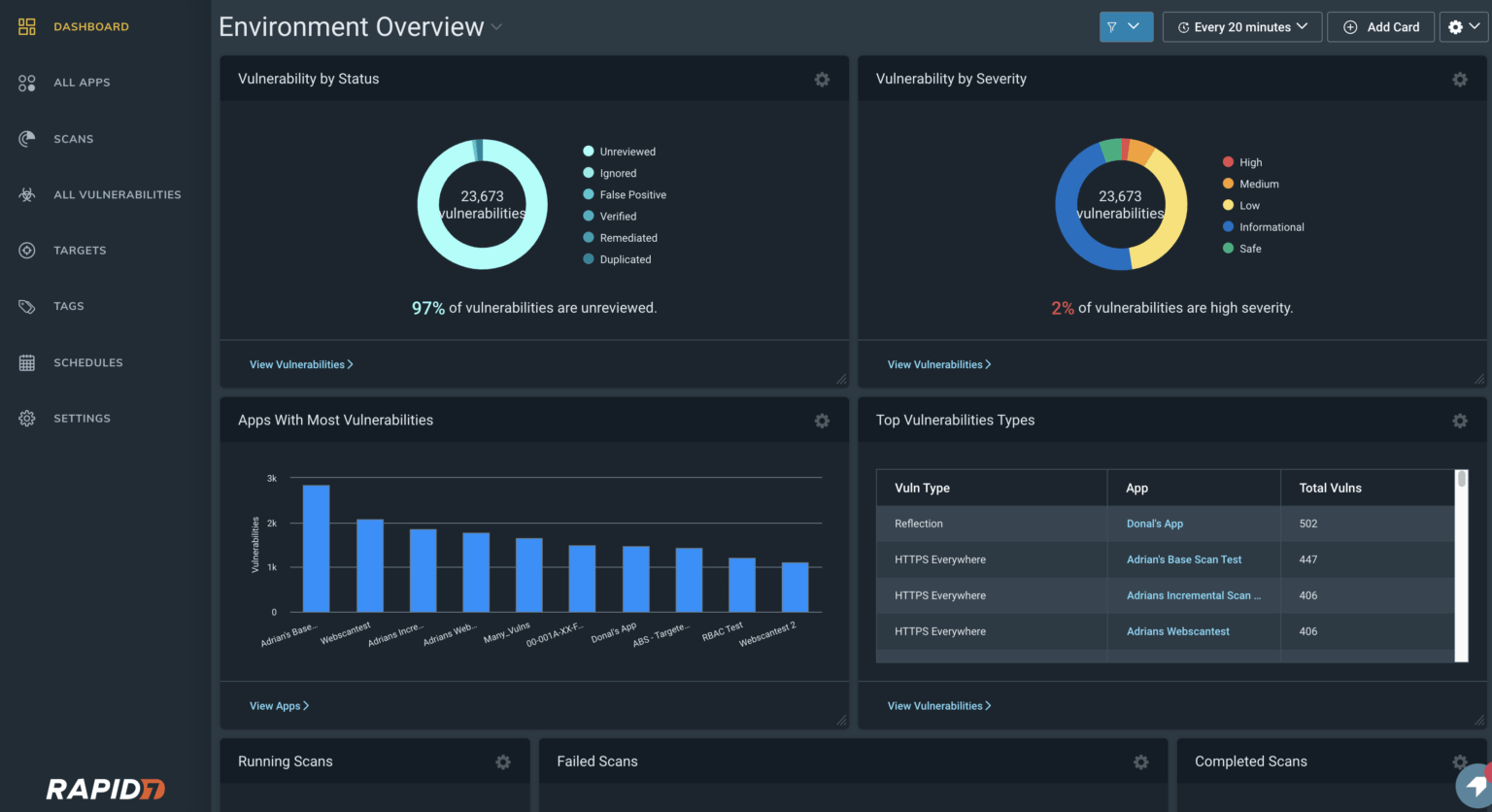
Key Features:
- AWS Scanning Capabilities: Cloud and Web Applications
- Specialization: Provides threat intelligence and risk management
- Vulnerability Management: Yes
- Price: $175/month
Rapid7 is an upcoming vulnerability scanning service that will also be available for AWS. Its powerful cloud-based toolbox, the Insight Platform, provides continuous attack surface monitoring with Project Sonar, real-time vulnerability assessment with InsightVM, and round-the-clock threat detection and response with MDR.
Their compliance tools guarantee regulatory compliance, and their penetration testing services assist in locating CVEs for application. Rapid7 provides the automation, visibility, and analytics required for all-encompassing security.
Pros
- The services are scalable based on customer requirements.
- Easy to use and has a short learning curve.
Limitations
- Scanned devices can only be removed manually.
- Inadequate customer satisfaction.
4. Alert Logic

Key Features:
- AWS Scanning Capabilities: Threat detection and response for AWS, Google, & Azure
- Specialization: SOC-as-a-service vulnerability management
- Vulnerability Management: Yes
- Price: Quote on Request
AlertLogic is a well-known SOC-as-a-service and vulnerability management provider that provides managed threat detection and response services (MDR) for cloud platforms.
Their holistic services include 24*7 threat monitoring, incident validation, remediation, log management, and more.
Pros
- User-friendly solution.
- Precise and timely notifications.
- Easy-to-navigate dashboards.
Limitations
- Could have better end-point protection.
Astra Pentest is built by the team of experts that helped secure Microsoft, Adobe, Facebook, and Buffer

5. Qualys
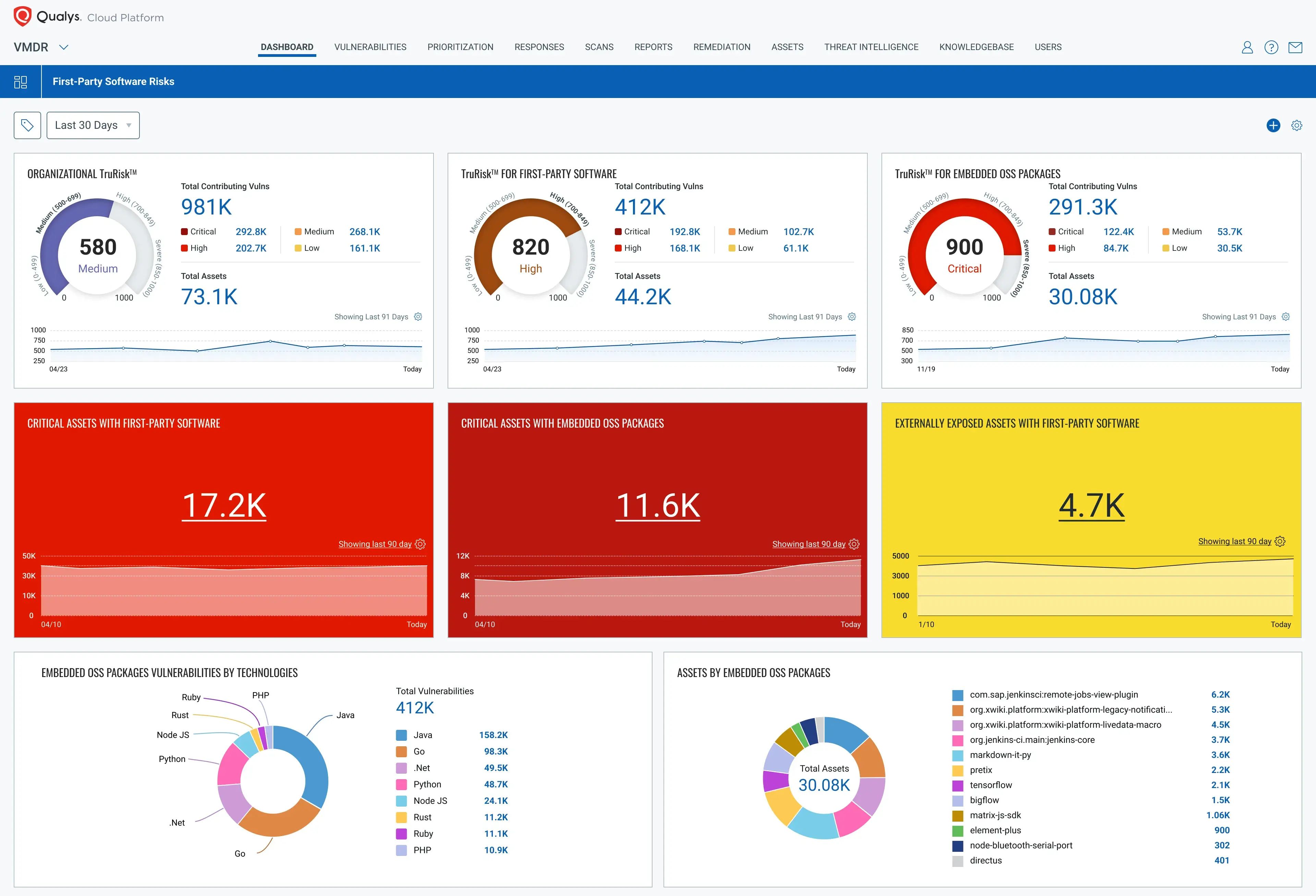
Key Features:
- AWS Scanning Capabilities: Scans both cloud environment and web applications
- Specialization: Cloud inventory & assessment and cloud agent
- Vulnerability Management: Yes
- Price: Quote on Request
Qualys’ subscriber base is distributed across five industries and 130 countries. This self-updating vulnerability management application enables you to handle various operations from a single platform, including vulnerability scanning, assessment, remediation, and compliance reporting.
While Qualys’ Cloud Agent manages real-time unmanaged device discovery to provide total visibility, Cloud Inventory & Assessment manages inventory and misconfiguration detection.
Pros
- The highly scalable vulnerability scanning solution.
- Provides vulnerability management, detection, and response.
- Accurate reporting that is easy to follow.
Limitations
- Can be slow when scanning.
- Difficult to navigate for beginners.
- Slightly on the expensive end.
- No zero false positive assurance.
6. Aqua Security

Key Features:
- AWS Scanning Capabilities: Threat prevention for AWS, Google & Azure
- Specialization: Cloud-Native Security, Runtime Protection, & Compliance Management
- Vulnerability Management: Yes
- Price: Quote on Request
Aqua Security offers a cloud-native security platform to safeguard your cloud-hosted application. The platform provides runtime protection, compliance management, and cloud vulnerability screening, among other services.
Additionally, you can use the cloud agent provided by Aqua Security to assess your cloud infrastructure for vulnerabilities.
Pros
- Offers a cloud agent for scanning cloud infrastructure.
- Provides runtime protection and compliance management.
- Allows you to generate reports and share them with stakeholders.
- Helps you to track vulnerabilities over time.
Limitations
- Can be an expensive solution
- Better suited for larger companies.
7. Orca Security

Key Features:
- AWS Scanning Capabilities: Cloud Vulnerability Scanning for AWS, Google, Azure
- Specialization: Sidescanning
- Vulnerability Management: No
- Price: Quote on Request
Orca security promotes a new approach to cloud vulnerability scanning called Sidescanning. It takes the role of the cloud agent and gathers data straight from your cloud setup.
Orca helps you cover vulnerabilities that might have escaped the agent-based vulnerability scanning solutions.
Pros
- Combines all your cloud assets in a single graph.
- It supports more than forty CIS benchmarks and all major security regulations.
- It makes actionable data readily available to the right teams.
Limitations
- No upfront pricing is provided.
Process of an AWS Vulnerability Scan
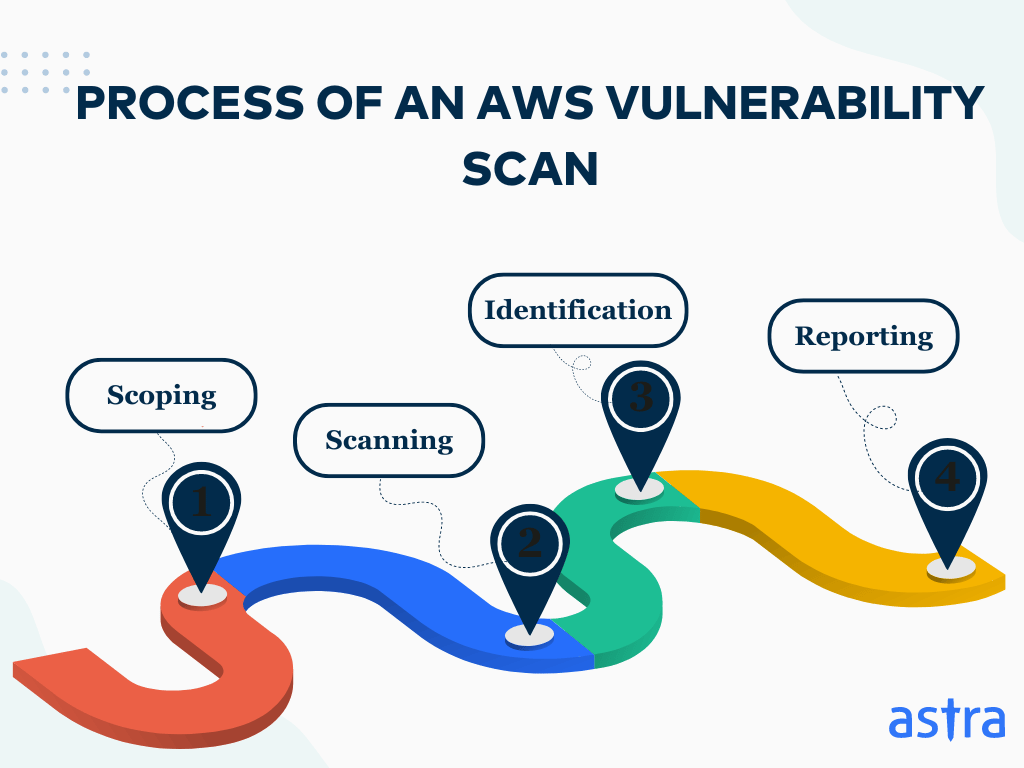
1. Scoping
The initial step before starting a vulnerability scan is to set the scope. This decides which assets are to be excluded and included in the scanning process, along with other rules and agreements between the scanning team and the company. This step is done to avoid scope creep and any possible legal issues.
2. Scanning
The AWS vulnerability scanner then scours through the agreed-upon assets within the AWS platform to find any vulnerabilities, loopholes, or security gaps that could threaten the organization’s business flow, revenue, and data security. Some providers also combine this with manual testing.
3. Identification
Based on the scan, the detected vulnerabilities are identified using various vulnerability databases, such as CVEs, OWASP Top 10, SANS 25, bug bounty data, etc. Once identified, they are prioritized based on their severity, potential impact on the applications, and CVSS scores.
4. Reporting
After identifying and prioritizing vulnerabilities, an AWS vulnerability report contains an executive summary, a list of all tests performed, vulnerabilities discovered with their remediation measures, CVSS scores, and contextual details. The customer’s development team then mitigates and patches the detected vulnerabilities.
Shared Responsibility Model
Like many other cloud services, AWS employs a Shared Responsibility Model. This approach divides cloud security into two parts: you safeguard your data, and AWS secures the infrastructure.
Thus, the security testing of an AWS platform may be divided into two sections:
1. Security of the Cloud
Amazon (AWS) guards cloud computing environments against security flaws and cyberattacks to keep businesses utilizing AWS services safe. Cloud security encompasses all zero-days and logic defects that may be leveraged to interfere with an AWS server’s operation at any point.
2. Security in the cloud
When we talk about cloud security, we mean that the user’s or business’s duty is to ensure that the assets and applications they have placed on AWS infrastructure are safe from cyberattacks.
Secure your AWS environment with Astra Security’s expert cloud pentesting.
Get started today!

Factors to Consider in an AWS Vulnerability Scanning Tool
1. Your AWS Needs
The hunt for a good AWS vulnerability scanner starts with recognizing the needs of your AWS environment and your organization’s services.
Since there is no single fixed solution to anything in the cyber world, it goes without saying that having a clear resolution to your requirements can significantly help you narrow down your choices.
2. Continuous Scanning
The AWS security scanner should provide continuous automated vulnerability scanning as a part of its services. It should be capable of detecting and providing alerts for vulnerabilities and risks upon discovery and should be easily integrated into your CI/CD pipeline.
Continuous monitoring of the AWS assets should correctly identify known vulnerabilities from CVEs, SANS 25, OWASP Top 10, and risks based on intel.
3. Scalability of the Scanner
Ensure that the AWS vulnerability scanner you consider is scalable according to the growing needs of your organization.
Switching scanners during daily operations can be tedious if the current tool you’ve chosen isn’t scalable, making finding a scalable AWS scanning solution all the more relevant.
4. Services Offered Beyond Scanning
Look for AWS scanning tools that provide other services such as vulnerability patching, vulnerability management, pentesting, and remediation assistance for the vulnerabilities through continuous AWS scans.
This can provide an additional mile in terms of security and vulnerability management of assets.
5. Easy-To-Navigate Dashboard
The AWS vulnerability scanner should be easy to navigate, with a good dashboard that provides timely vulnerability alerts and reports. It should also show the vulnerabilities discovered, their present status, and scan statuses.
It’s also a bonus if the dashboard enables seamless communication with your team. It should be easy for people from varying technical backgrounds to use.
Final Thoughts
While it is assumed to be secure, AWS is not immune to data breaches. The shared responsibility model underlines the roles played by both AWS and its users in data security. This article identified AWS vulnerability scanners’ crucial roles in keeping cloud environments safe.
Compare and contrast leading scanners, such as Astra Security, AWS Inspector, and Alert Logic, to choose the one that best suits your needs. The critical factors in this decision revolve around continuous scanning, scalability, remediation assistance, and compliance coverage.
A holistic strategy for securing the organization’s data will feature the proper tooling, implementation of best practices, keeping pace with emerging threats, and establishing a security culture within the organization.
FAQs
1. What are the four pillars of comprehensive cloud security?
The four pillars of comprehensive cloud security are compliance maintenance, proper implementation of access controls, continuous vulnerability scans, and immediate remediation of vulnerabilities.
2. How do you secure data stored in the cloud?
Enabling data encryption and multi-factor authentication, installing good security software, conducting regular vulnerability scans, and using strong passwords can ensure the safety of data stored and transmitted within the cloud.
3. Does AWS have vulnerability scanning?
AWS offers vulnerability scanning via services like Amazon Inspector, which identifies software vulnerabilities and unintended network exposure in AWS workloads. You can also scan your AWS cloud environment using an external security scanner.
4. What are the three types of vulnerability scanners?
There are mainly three significant vulnerability scanners: network-based, intended to scan a network’s infrastructure; host-based, used for assessing individual systems; and application scanners, meant for web and application vulnerabilities.
Explore Our Vulnerability Scanning Series
This post is part of a series on Vulnerability Scanning. You can also check out other articles below.

- Chapter 1: What is Vulnerability Scanning?
- Chapter 2: Types Of Vulnerability Scanning
- Chapter 3: Vulnerability Scanning Report: Things You Should Know
- Chapter 4: Best Vulnerability Scanners of 2025
- Chapter 5: Best Web Application Vulnerability Scanners
- Chapter 6: Top Cloud Vulnerability Scanners for AWS, GCP & Azure
- Chapter 7: Top 7 GCP Vulnerability Scanning Tools
- Chapter 8: 7 Best AWS Vulnerability Scanners
- Chapter 9: Best Free Vulnerability Scanners
- Chapter 10: Best Android Vulnerability Scanners
- Chapter 11: Best Vulnerability Assessment Tools