Vulnerability scanning is a critical security practice that identifies and assesses potential vulnerabilities in computer systems, networks, and applications to help organizations reduce their risk of cyberattacks and protect sensitive data.
There are several types of vulnerability scanners, each with its own strengths and weaknesses. We shall discuss five different vulnerability scanning types and try to understand how each can help us evaluate security.
Automate your security checks with AI-driven Vulnerability Scanning Services for continuous monitoring and compliance.
Five Types of Vulnerability Scanning
- Host-based vulnerability scanning is the scanning of network hosts to find vulnerabilities.
- Network vulnerability scanning is vital to an organization’s network infrastructure to find any vulnerabilities.
- Database vulnerability scanning refers to scanning databases where all confidential and application-related data is stored to detect security risks.
- Cloud vulnerability scanning refers to scanning cloud deployments to find flaws.
- Application vulnerability scanning involves scanning web and mobile applications to identify security vulnerabilities.
External vs Internal Scanners
| Feature | External Scanners | Internal Scanners |
|---|---|---|
| Scope | Primarily assess the external attack surface, identifying vulnerabilities exposed to the public. | Scan internal systems and networks, providing deeper insights into vulnerabilities. |
| Accuracy | Limited accuracy as they cannot access internal systems or protected resources. | More accurate in identifying vulnerabilities as they can access privileged information. |
| Coverage | Can identify vulnerabilities exposed externally, such as open ports and services. | Can detect vulnerabilities hidden behind firewalls or other security measures. |
| Risk | Lower risk as they don't require privileged access. | Higher risk as they require access to privileged accounts, increasing the potential for unauthorized access. |
| Use Cases | Suitable for external penetration testing, identifying publicly exposed vulnerabilities, and assessing external attack surfaces. | Ideal for internal network assessments, compliance audits, and risk management. |
Lock down your security with our 10,000+ AI-powered test cases.
Discuss your security needs
& get started today!
What Are the Different Vulnerability Scanning Types?
1. Host-Based Vulnerability Scanning
A host is a TCP/IP network device that connects with others to exchange data. It can offer network access through various means, including user interfaces and specialized software.
In the open systems interconnection model, the host communicates with other hosts using transport layer protocols. For companies with a website, the host is a web server responsible for transmitting and storing data. If the company uses cloud hosting, then multiple servers located at different locations are responsible for the functionality of their website.
Similarly, there are other virtual hosts and remote hosts. Our real concern here is host-based vulnerability scanning, so let us not delve further into hosts’ particulars.
What is Host-Based Security?
Host-based security protects individual workstations, servers, and other network devices by creating a perimeter around them.
It means installing firewalls and intrusion prevention systems and patching software regularly to avoid vulnerabilities. Host-based security not only prevents a host from being infected but also ensures that if a host is infected, it doesn’t spread the infection to neighboring hosts.
What is Host-Based Vulnerability Scanning?
Host-based vulnerability scanning is scanning a network host for security loopholes. A scan of this kind can reveal
- The history of security patches in said host
- Vulnerabilities incurred through outdated patches
- The damage that the detected vulnerabilities can cause
- The level of access a hacker can gain by infecting the said host
- Possible ways of mitigating the situation.
2. Network Scanning
This is one of the most vital vulnerability scanning types. Network vulnerability scanning is the process of identifying security vulnerabilities in an organization’s network infrastructure.
What does Network Vulnerability Scanning Entail?
To assess the security of your network infrastructure, a vulnerability scanner identifies all systems and devices connected to it. It then creates an inventory of these assets, analyzes them for common vulnerabilities, scans exploitable ports and services, and checks for weak passwords and authentication errors.
You get a detailed report of the vulnerabilities found during the assessment and suggestions for fixing the issues.
3. Database Vulnerability Scanning
The primary goal of many malicious actors is to access sensitive data stored in databases. As such, database security involves various measures to protect the confidentiality, integrity, and availability of databases and their management systems.
A hacked database can severely damage a business, affecting its operations, reputation, finances, and intellectual property. It may also lead to fines and penalties.
What is a Database Vulnerability Scanner?
A database vulnerability scanner is a tool specially designed to scan your database for vulnerabilities such as faulty security configuration and a lack of encryption.
Database vulnerability scanning helps you evaluate your organization’s overall data security health, detect vulnerabilities, and mitigate them before hackers exploit them.
4. Cloud Vulnerability Assessment
The process of scanning a cloud deployment for common vulnerabilities is called cloud vulnerability scanning. Cloud vulnerability scanning is a part of the holistic cloud security strategy that can be implemented to monitor, manage, and improve the overall security of cloud infrastructure.
What are Some Cloud-Related Vulnerabilities?
- Server misconfigurations, such as misconfigured S3 buckets,, are among the most common cloud vulnerabilities.
- Using weak passwords can expose your cloud accounts to brute-force attacks.
- SQLi, XSS, and CSRF bugs are quite common in cloud-based applications, and hackers can easily exploit them.
- Running outdated, unpatched software on your cloud platform can compromise the cloud services.
Performing regular cloud vulnerability assessments ensures you stay on top of these issues.
5. Application Vulnerability Assessment
Application vulnerability scanning is one of the most widely used vulnerability scanning types. It involves scanning your web apps and mobile apps for security vulnerabilities.
Both web applications and mobile applications are updated with new features on a regular basis. New vulnerabilities may creep in with each new code update. That aside, an application needs various external components like themes and plugins to function properly. These external components may also incur exploitable vulnerabilities.
It is essential to incorporate a security regime in your application development lifecycle and an application vulnerability scanner plays a vital role in it.
Application Vulnerability Assessment Helps you Assess –
- The current state of security of your application
- The existing vulnerabilities and the risk posed by them
- The amount of potential damage caused by the vulnerabilities.
It also helps you find efficient ways of removing vulnerabilities.
Now that you have learned about five different vulnerability scanning types, it is time to understand some more categories of vulnerability assessment.

Why is Astra Vulnerability Scanner the Best Scanner?
- We’re the only company that combines automated & manual pentest to create a one-of-a-kind pentest platform.
- Vetted scans ensure zero false positives.
- Our intelligent vulnerability scanner emulates hacker behavior & evolves with every pentest.
- Astra’s scanner helps you shift left by integrating with your CI/CD.
- Our platform helps you uncover, manage & fix vulnerabilities in one place.
- Trusted by the brands you trust like Agora, Spicejet, Muthoot, Dream11, etc.

Authenticated vs Unauthenticated Vulnerability Scanning
| Feature | Authenticated Scanning | Unauthenticated Scanning |
|---|---|---|
| Scope | Can scan internal systems and networks, providing deeper insights into vulnerabilities. | Primarily focuses on external systems and networks, identifying vulnerabilities exposed to the public. |
| Accuracy | More accurate in identifying vulnerabilities as it can access privileged information. | Less accurate as it cannot access internal systems or protected resources. |
| Coverage | Can detect vulnerabilities hidden behind firewalls or other security measures. | Limited to vulnerabilities exposed externally. |
| Risk | Higher risk as it requires access to privileged accounts, increasing the potential for unauthorized access. | Lower risk as it doesn't require privileged access. |
| Use Cases | Ideal for internal network assessments, compliance audits, and risk management. | Suitable for external penetration testing, identifying publicly exposed vulnerabilities, and assessing external attack surfaces. |
Essential Features to Look For in Vulnerability Scanning
There are a variety of parameters that can help you judge a vulnerability assessment provider or even vulnerability scanners. Here are some crucial features you should look for in a vulnerability scanning provider and their vulnerability scanners.
Coverage of all CVEs:
Go for a vulnerability assessment that covers all CVEs mentioned on the OWASP top 10, SANS 25, and has all the tests required for major compliances. Incorporate tests aligned with major compliance standards (like PCI DSS, HIPAA, or GDPR) to demonstrate your commitment to regulatory adherence and risk mitigation.
Continuous Scanning:
In today’s dynamic IT environments, new software updates, patches, and configuration changes are introduced frequently. As such, choose a type of continuous scanner that can perform automated vulnerability scanning periodically and every time there is a code update.
Scan Behind the Login Screen:
To maximize the benefits of authenticated scanning, you need a solution that can seamlessly navigate behind login screens without requiring constant user intervention, significantly reducing the workload and increasing the accuracy of your vulnerability assessments.
Vulnerability Monitoring:
You should be able to monitor the vulnerabilities and their risk scores as they are found. Such real-time monitoring of vulnerabilities allows your security team to respond promptly to incidents, reduce the risk of data breaches, and maintain a high security posture.
Detailed Suggestions for Fixing CVEs:
Choose a vendor who offers a detailed vulnerability scanning report with suggested fixes to significantly streamline the process of mitigating vulnerabilities. These suggestions often provide specific steps, scripts, or configuration changes that can be directly applied to address the identified weaknesses.
Apart from these features, you should also look at the presence of a particular vulnerability scanning company in the industry, their clientele, and online reviews, and also judge the price with respect to the quality of service you are promised.
How can Astra Help?
Astra’s Pentest is a complete vulnerability assessment and penetration testing solution with top-notch automated and manual pentesting capabilities. Even if you use it in the capacity of only an automated vulnerability scanner, it could be a win for you.
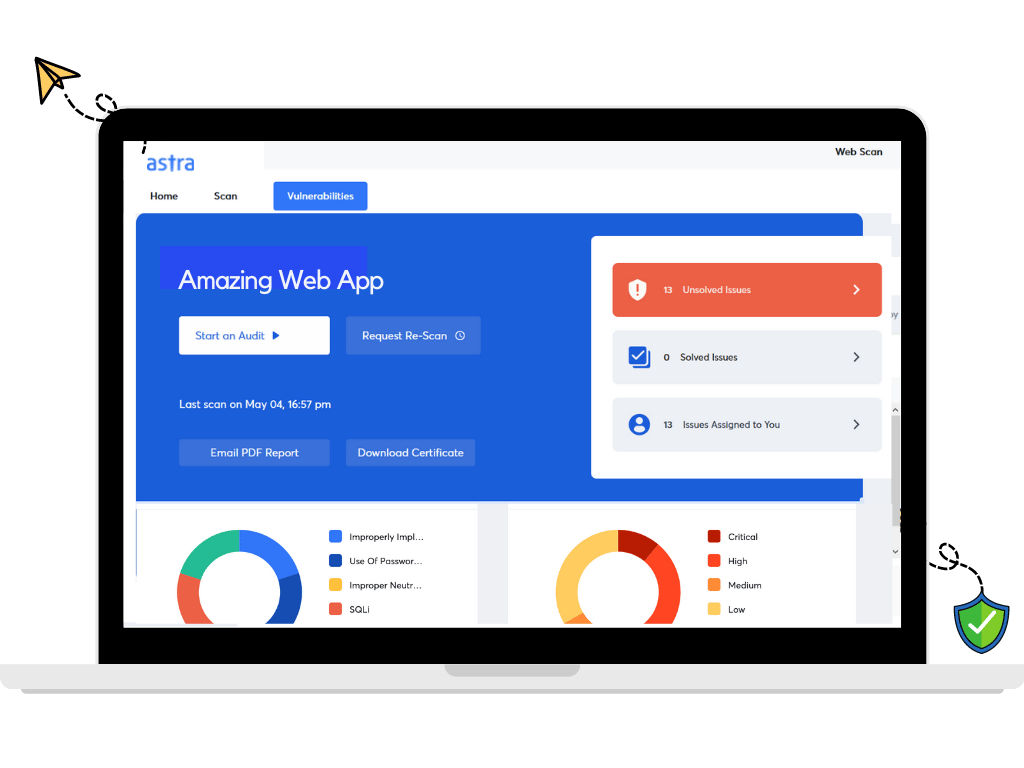
Astra Pentest conducts 10,000+ automated tests that cover every CVE mentioned in the OWASP top 10, SANS 25, and other CVEs.
Not only does it conduct all the tests required for compliance with ISO 27001, HIPAA, SOC2, and GDPR, but the pentest suite also has a compliance reporting feature that shows you where you are falling short in terms of meeting the compliance requirements based on the results of the vulnerability scans.
The interactive pentest dashboard allows you to monitor vulnerabilities, assign them to team members, update their status, and practically do anything else you might like. The CI/CD integration feature lets you automate vulnerability scans before the new code is shipped.
The login recorder extension allows the vulnerability scanner to scan behind the logged-in pages. Overall, it is a package you cannot pass up without reaping the benefits.
Let experts find security gaps in your cloud infrastructure
Pentesting results without 100 emails,
250 google searches, or painstaking PDFs.

Final Thoughts
To conclude, there are five types of vulnerability scanning. From host-based and network scanning to database, cloud, and application assessments, each type offers distinct advantages in identifying and mitigating potential vulnerabilities.
By understanding the different types of vulnerability scanning tools, you can effectively identify and address potential security risks, protect your assets, and maintain a strong security posture in today’s ever-evolving threat landscape.
FAQs
1. What is the cost of web app vulnerability scanning?
The cost of a web app assessment can vary widely depending on the size and complexity of the application, the scope of the assessment, and the experience and expertise of the provider. However, you can generally expect to pay between $1,000 and $5,000 per assessment.
2. How often should I conduct vulnerability scans?
Vulnerability scans should be conducted regularly, ideally every quarter or more frequently for critical systems or after every code update. This helps identify and address security weaknesses before malicious actors can exploit them.
Explore Our Vulnerability Scanning Series
This post is part of a series on Vulnerability Scanning. You can also check out other articles below.

- Chapter 1: What is Vulnerability Scanning?
- Chapter 2: Types Of Vulnerability Scanning
- Chapter 3: Vulnerability Scanning Report: Things You Should Know
- Chapter 4: Best Vulnerability Scanners of 2025
- Chapter 5: Best Web Application Vulnerability Scanners
- Chapter 6: Top Cloud Vulnerability Scanners for AWS, GCP & Azure
- Chapter 7: Top 7 GCP Vulnerability Scanning Tools
- Chapter 8: 7 Best AWS Vulnerability Scanners
- Chapter 9: Best Free Vulnerability Scanners
- Chapter 10: Best Android Vulnerability Scanners
- Chapter 11: Best Vulnerability Assessment Tools







