Vulnerability scanning reports are essential tools for identifying potential weaknesses in a system’s security by providing a detailed analysis of vulnerabilities, their severity, and possible risks.
The size of your business does play a role in pulling a hacker’s attention. But if you think your website is too small to attract malicious actors, think again. On average, a website is visited by 1100+ malicious bots in search of exploitable vulnerabilities per week. (Source: Check Point Research) But before we jump in, let’s understand what vulnerability scanning refers to.
What is Vulnerability Scanning?
A vulnerability scanner is an automated software tool commonly used to detect security weaknesses and exploitable vulnerabilities in your website, web app, IT network, or devices. It is an automated tool that helps you discover anomalies in your systems related to a vulnerability database.
After that, the scanner produces a vulnerability scanning report that documents all the issues found during the scan, along with some recommendations on how to get rid of them. The following section gives you five essential pieces of information about a vulnerability report.

Why is Astra Vulnerability Scanner the Best Scanner?
- We’re the only company that combines automated & manual pentest to create a one-of-a-kind pentest platform.
- Vetted scans ensure zero false positives.
- Our intelligent vulnerability scanner emulates hacker behavior & evolves with every pentest.
- Astra’s scanner helps you shift left by integrating with your CI/CD.
- Our platform helps you uncover, manage & fix vulnerabilities in one place.
- Trusted by the brands you trust like Agora, Spicejet, Muthoot, Dream11, etc.

What is Included in a Detailed Vulnerability Scanning Report?
A detailed vulnerability scanning report helps you attain the true picture of your web app’s security posture. It has two primary purposes: helping you prioritize critical vulnerabilities and assisting you in fixing them. The following are different components that a vulnerability scanning report should have.
1. Executive Summary
This section of the security vulnerability scan report provides a concise overview of the vulnerability assessment, highlighting key findings, duration, and methodology without delving into technical details. It clearly defines the purpose and scope of the testing.
To enhance understanding, consider including graphical representations of vulnerabilities by type and severity. Additionally, a list of identified vulnerabilities should be provided, along with their CVSS scores and corresponding severity levels (low, medium, high, critical). The current status of each vulnerability should also be indicated.
2. Details of the Vulnerabilities Discovered
This section provides in-depth information about each identified vulnerability. You’ll learn about its specific nature, potential impact on your website and business, current status, and CVSS score. It also includes suggestions for fixing the issue.
Additionally, the section also offers recommendations for remediation, ranging from brief suggestions to detailed step-by-step guides to help you address the issue effectively.
3. Scan Details
A comprehensive vulnerability scan involves hundreds of test cases documented for each test case, including its category, severity level, scan type, and other relevant details that may vary depending on the application type, such as web, Android, iOS, or blockchain-based apps.
Some vulnerability scans may include video proof-of-concepts (POCs) in addition to the standard PDF report. These POCs can be invaluable to developers as they visually demonstrate identified vulnerabilities, making it easier to understand and reproduce the issue.
How Does a Vulnerability Scan Report Aid Your Security Efforts?
The impact of an actionable vulnerability scan report is quite simple.
- It identifies vulnerabilities that pose a threat to your organization.
- It analyses the severity of those vulnerabilities so that you can prioritize the most dangerous ones.
- It gives you suggestions and guidance for fixing the vulnerabilities.
The easier it is for you and your developers to read and understand the report, the sooner the issues will be fixed, thus restoring your organization’s security health. Some additional benefits also include:
- Get a competitive edge by being secured and certified.
- Stay aware of your security posture.
- Stay informed about your standing regarding relevant security compliance regulations.
- Protect your website against automated and malicious hackers.
- Protect sensitive information belonging to both you and your customers.
How to Pick the Right Vulnerability Scanning Tool?
You need a scanner that comes with a robust interface, conducts tests according to relevant security standards, and conducts enough of them. Finally, it should produce an actionable report.
Apart from these typical features, you can look for additional features, such as:
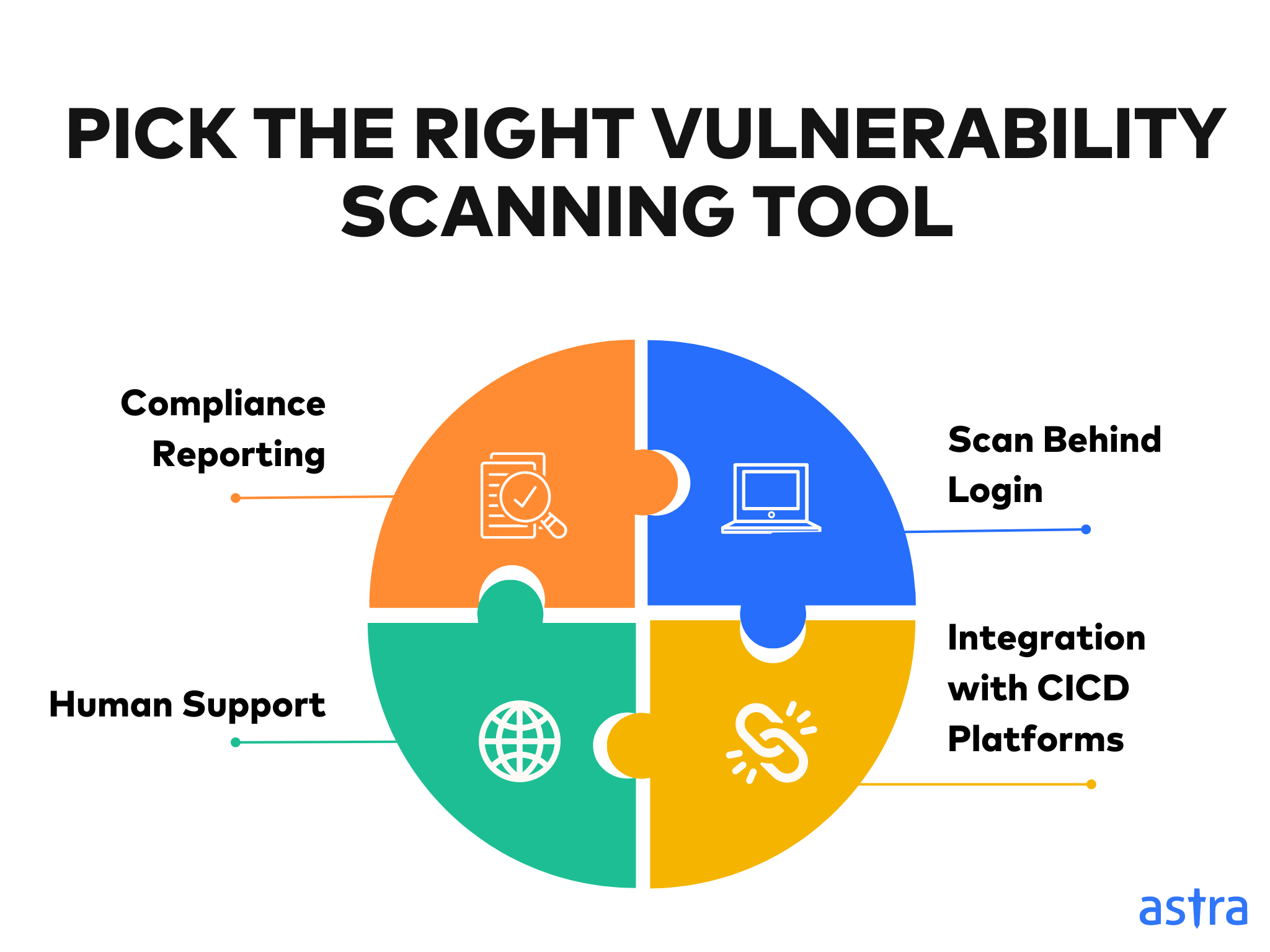
Scan Behind Login
This feature allows vulnerability scanning to be conducted within protected areas of an application, such as logged-in user interfaces. By simulating user behavior and accessing authenticated areas, scanning behind login can identify vulnerabilities that might otherwise be hidden from traditional scanning methods.
Compliance Reporting
Compliance reporting generates detailed reports demonstrating adherence to various industry standards and regulations, such as PCI DSS, HIPAA, and GDPR, as evidence of your commitment to security and can be essential for audits, certifications, and legal requirements.
Human Support
Human support offers access to security experts who can provide guidance, assistance, and tailored recommendations based on your specific needs and findings. This personalized support can be invaluable for interpreting scan results, prioritizing vulnerabilities, and developing effective remediation strategies.
Integration with CI/CD Platforms
Integration with continuous integration/continuous delivery (CI/CD) platforms enables seamless integration of vulnerability scanning into your development and deployment pipelines. This allows you to automate security testing, identify vulnerabilities early in the development process, and prevent them from being introduced into production environments.
Recommended Reading: All-in-one guide on vulnerability scanning tools and methodology
Types of Vulnerability Scanners
1. Network-Based Scanners
As the name suggests, a network-based vulnerability scanner searches an entire network with all the devices and applications running on it for vulnerabilities. The scanner creates an inventory of all the network assets and the vulnerabilities in each of them.
2. Host-Based Scanners
Host-based scanners scan servers and workstations, checking their security configurations and patch history. Unlike network-based scanners that examine network traffic, host-based scanners directly analyze target systems’ configuration, software, and running processes.
3. Wireless Scanners
Wireless scanners identify unauthorized access points in a network and find inconsistencies in security configurations. They offer greater mobility and flexibility, allowing users to scan items from a distance without being tethered to a computer or other device.
4. Application Scanners
Application scanners are used to scan websites and applications for common security vulnerabilities. We will be talking about these scanners at length.
5. External Vulnerability Scanners
As the name suggests, such external scanners are responsible for scanning a target’s external network or web applications for vulnerabilities such as open ports, outdated software, misconfigurations, and known exploits.
6. Internal Vulnerability Scanners
Designed to identify and assess security weaknesses within an organization’s internal network infrastructure, these scanners meticulously examine systems, applications, and devices to uncover potential vulnerabilities that malicious actors with access could exploit.
Vulnerability Scanning with Astra’s Pentest
Software development is a continuous process. With each updated version of a web app, new vulnerabilities creep in. Hence, security needs to be a continuous process too and it needs to be simple.
Astra Security has built the most elegant solution for scanning web apps, mobile apps, and networks for potential vulnerabilities (with over 10000+ test cases). Astra’s Vulnerability Scanner is a part of their comprehensive offering called Astra Pentest Suite.
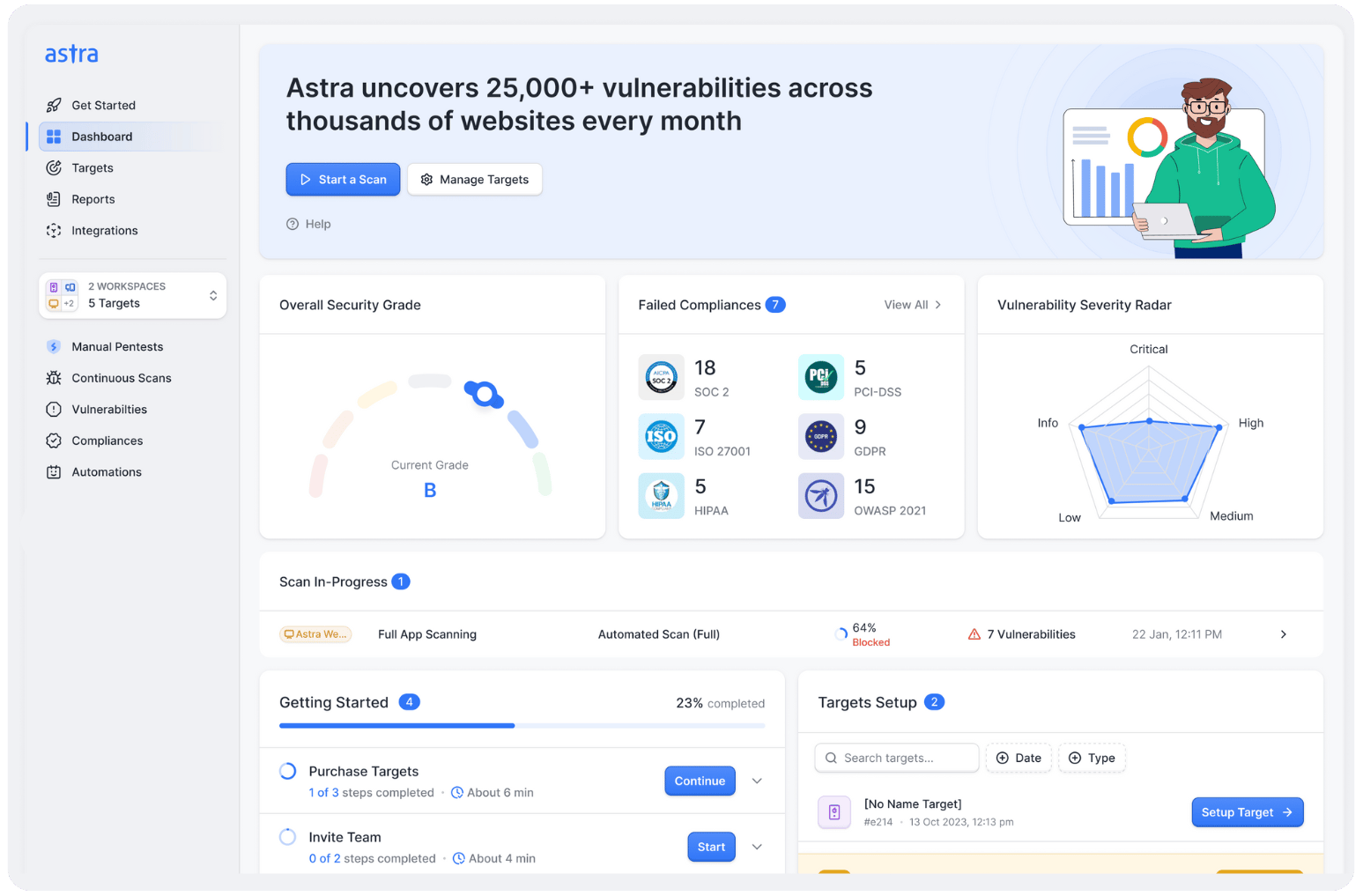
Here are some unique features of Astra Pentest Suite:
- Zero false positives: When vulnerabilities are detected, security engineers manually ensure that each one of the reported vulnerabilities is genuine.
- Compliance reporting: The pentest compliance feature shows you the compliance regulations you meet or fail to meet with reference to the vulnerabilities found during a scan.
- CI/CD integration: You no longer have to go to the pentest dashboard to run a vulnerability scan after each product update. You can automate the scan after each update by integrating the pentest suite with CI/CD platforms.
- Detailed report with video POCs: The vulnerability scanning report sample by Astra Security is as detailed and comprehensible as it gets. You get easy access to security experts if the remediation process hits a roadblock.
Final Thoughts
A vulnerability scan without a detailed and actionable report is akin to searching for treasure without a map. The ideal report clearly outlines identified vulnerabilities, their severity levels, and recommended solutions with steps and video POCs.
By effectively combining technical expertise with open communication, your organization can harness the power of vulnerability scanning reports to bolster its security defenses and safeguard against potential threats.
FAQs
What is the importance of vulnerability scanning for organizations?
Vulnerability scanning is essential for organizations to identify and address potential security weaknesses in their systems. By proactively identifying vulnerabilities, organizations can mitigate risks, prevent data breaches, and protect their sensitive information and operations from cyber threats.
How do you analyze a vulnerability scan?
To analyze a vulnerability scan, prioritize critical vulnerabilities, evaluate their potential impact, and research available patches. Consider the system’s environment and prioritize remediation based on risk. Document findings and track remediation progress for ongoing security management.
What information is in a vulnerability report?
A vulnerability report provides detailed information about a security weakness in a system or software. It typically includes the vulnerability’s unique identifier, severity level, description, potential impact, and recommended mitigation or remediation steps. This information helps organizations prioritize and address security risks effectively.
Explore Our Vulnerability Scanning Series
This post is part of a series on Vulnerability Scanning. You can also check out other articles below.

- Chapter 1: What is Vulnerability Scanning?
- Chapter 2: Types Of Vulnerability Scanning
- Chapter 3: Vulnerability Scanning Report: Things You Should Know
- Chapter 4: Best Vulnerability Scanners of 2025
- Chapter 5: Best Web Application Vulnerability Scanners
- Chapter 6: Top Cloud Vulnerability Scanners for AWS, GCP & Azure
- Chapter 7: Top 7 GCP Vulnerability Scanning Tools
- Chapter 8: 7 Best AWS Vulnerability Scanners
- Chapter 9: Best Free Vulnerability Scanners
- Chapter 10: Best Android Vulnerability Scanners
- Chapter 11: Best Vulnerability Assessment Tools