TLDR;
- Organizations are now facing more than 2000 cyberattacks weekly.
- Periodic manual pentests and basic vulnerability scans struggle to keep pace with agile development cycles and constantly evolving attack surfaces.
- Unlike vulnerability scanners, automated pentesting validates exploitability, chains weaknesses into attack paths, and prioritizes real risks.
- It provides fast, scalable, and cost-effective security testing, making it ideal for CI/CD pipelines and DevSecOps workflows.
Every week, organizations face thousands of cyberattacks, many of which exploit simple gaps or low-severity vulnerabilities that somehow slipped through the cracks.
Modern infrastructures are dynamic and ephemeral, creating an attack surface that’s nearly impossible to fully map at any given moment without proper tools.
Traditional security tools and manual penetration tests can keep up, but they take too much time. By the time a thorough manual security assessment is scoped, executed, and reported, the environment has often evolved significantly, rendering the findings outdated.
On the other hand, cyberattacks have evolved into long-running campaigns, sometimes lasting days, months, or even years, where attackers start with a low-severity issue and gradually escalate it until it brings down entire systems.
In this environment, the only practical way to maintain continuous visibility and reduce risk is through automated penetration testing.
What is Automated Penetration Testing?
Automated penetration testing (often called automated pentesting) uses specialized software to simulate cyberattacks on your systems, networks, or applications in a controlled environment to detect and identify vulnerabilities. These software probes for security weaknesses, attempt safe exploitation where appropriate, and mimic real-world attack techniques with minimal human input.
Learn the basics of Pentest in just a few minutes!.
Automated Pentesting vs Vulnerability Scanning vs Manual Pentesting
When discussing automated penetration testing, comparisons often pit it directly against vulnerability scanning and manual penetration testing. To better understand their roles, the following table highlights the key differences between vulnerability scanning, automated penetration testing, and manual penetration testing.
| Feature | Automated Penetration Testing | Manual Penetration Testing | Vulnerability Scanning |
|---|---|---|---|
| Execution / Approach | Performed by specialized software tools using intelligent automation, scripts, and often AI-driven techniques | Performed by skilled human security experts (ethical hackers) | Performed by automated tools with pre-defined checks |
| Speed | Fast; can scan large systems in hours to days (e.g., 24-48 hours) | Time-consuming; in-depth analysis often takes 15-20 business days or more | Very fast |
| Cost | Generally more affordable (lower ongoing costs, minimal human overhead) | More expensive due to skilled labor and expertise | Low cost |
| Skill Level Required | Can be run by IT/security staff with minimal manual effort | Requires highly skilled penetration testers | can be operated by analysts or automated |
| Analysis of Results | Correlates vulnerabilities, prioritizes risks, and simulates potential combined impact | Deep contextual analysis with exploitation proof-of-concept and recommendations | Limited context |
| Mimicking Attacker Behavior | Almost mimics attacker behavior through automated exploits and chains | Fully mimics real-world attacker creativity and chaining | Limited |
| Accuracy / False Positives | May produce some false positives (requires validation) | Minimal to no false positives (human validation) | higher false positives |
| Scalability | Highly scalable; efficiently handles large, complex, or frequently changing environments | Limited scalability; constrained by time and resources | Highly scalable for broad, repeated scanning |
| Customization | Limited to the tool | Highly customizable based on specific threats, business logic, and needs | Limited |
| Reporting | Generates automated, actionable reports | Provides detailed, narrative reports | Produces automated lists/reports with severity scores |
| Use Case | Ideal for ongoing validation in agile/DevOps environments | Ideal for deep, context-specific assessments | Ideal as a first-line check or broad monitoring |
As the table illustrates, no single method provides complete coverage on its own. The most effective security strategy combines all three: utilizing vulnerability scanning for ongoing baseline checks, automated pentesting for frequent, dynamic coverage that keeps pace with rapid code changes, and targeted manual pentests for in-depth reviews of critical assets or compliance requirements.
This layered approach minimizes blind spots, reduces risk exposure, and supports resilient security without hindering innovation or velocity.
Recommended Reading: Explore and compare the top 15 penetration testing service providers in one place
How Does Automated Pentesting Work?
Automated penetration testing involves using sophisticated software platforms to emulate cyberattacks at scale in a controlled, safe manner. It systematically discovers vulnerabilities, validates exploitability, and maps multi-step attack paths across networks, applications, cloud environments, and identity systems.
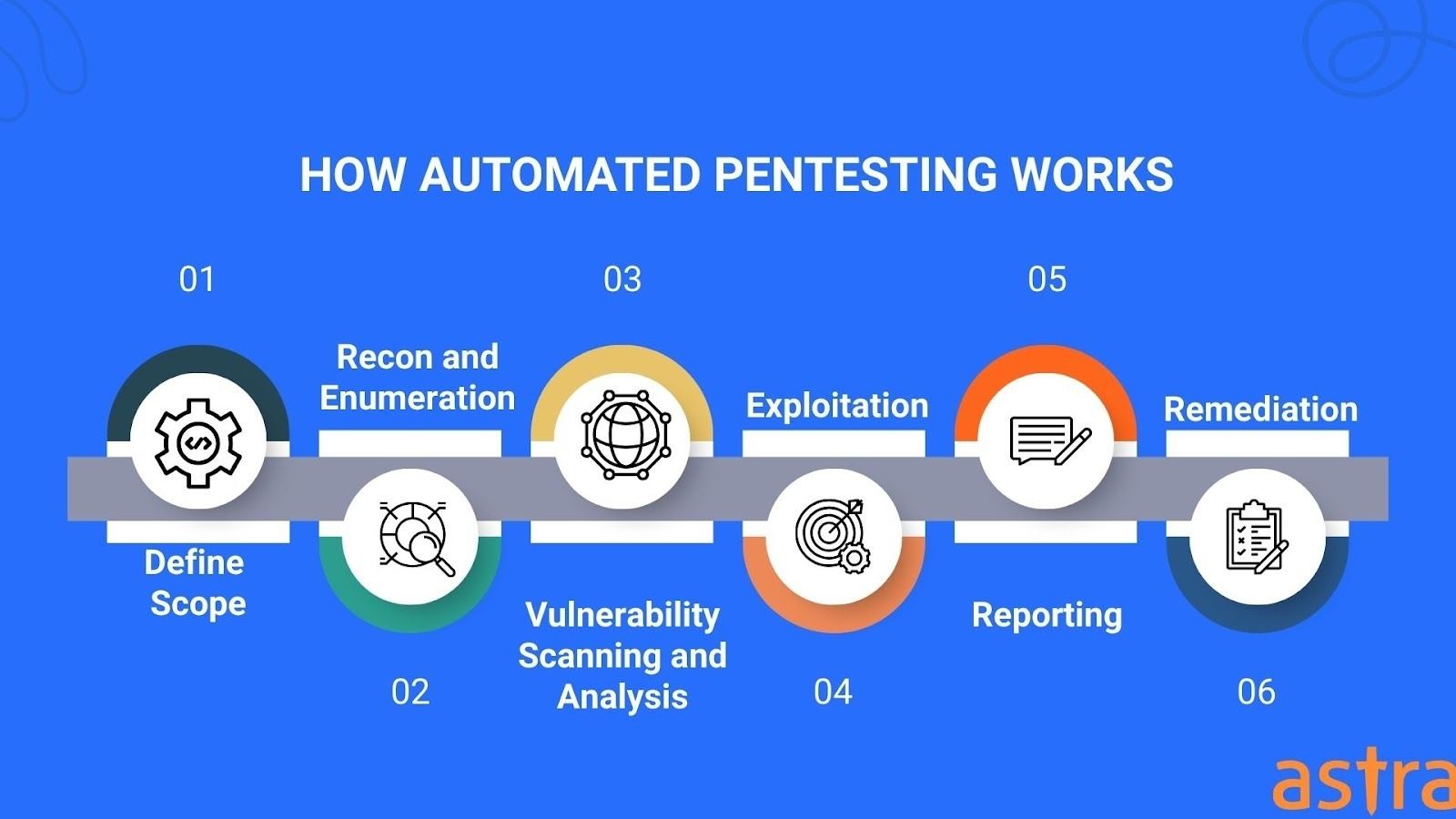
The workflow typically follows a structured sequence inspired by frameworks like MITRE ATT&CK or the Cyber Kill Chain.
1. Defining Scope
Before any test begins, the platform requires users to define the target scope: IP ranges, CIDR blocks, domain names, API base URLs, or cloud resource identifiers (e.g., AWS ARNs or Azure subscription IDs). Authentication configurations are also set at this stage (e.g., OAuth flows or recorded login sequences via browser extension capture).
Rules of engagement (rate limits, out-of-bounds hosts, fragile systems) are set to prevent disruption.
2. Reconnaissance and Enumeration
Automated scanners gather information on the target. This involves port scanning, service fingerprinting, and asset discovery to map out hosts, endpoints, open ports, and running services.
For example, tools often integrate Nmap-style scripts to map hosts, open ports, running services, endpoints, and technologies in use.
3. Vulnerability Scanning and Analysis
Once the target is mapped, the platform tests the identified assets against its library of test cases and known CVEs. Leading tools use extensive vulnerability databases, custom rulesets, and proprietary signatures to detect security weaknesses across applications, networks, and services.
4. Exploitation
This is where automated pentesting meaningfully separates itself from basic scanning. Rather than reporting vulnerabilities in isolation, the engine attempts to chain weaknesses into realistic multi-stage attack paths.
For example:
- An initial SQL injection (SQLi) flaw might be exploited to dump credentials from a database.
- Those credentials enable lateral movement via weak SMB signing.
- This leads to privilege escalation attacks(Pass-the-Hash), ultimately reaching domain admin or sensitive data.
5. Post-Exploitation
After successful exploitation, the identified attack paths are evaluated to determine their potential impact. This includes:
- Identifying sensitive data exposure (PII, credentials, internal configs)
- Mapping reachable internal services or network segments
- Calculating business impact based on an asset.
6. Report Generation
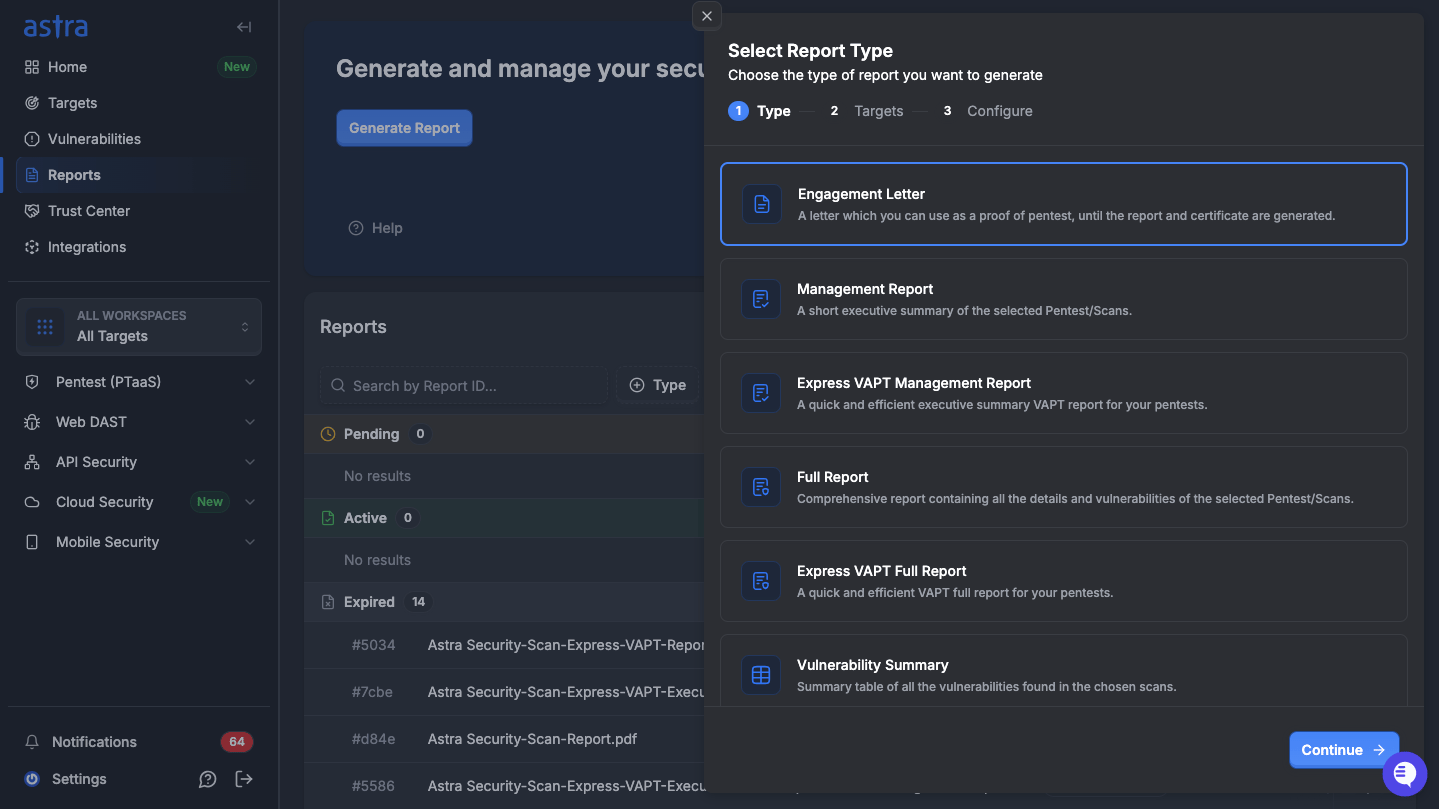
Findings are compiled into structured, audience-specific reports:
- Developer-facing output: CVE references, reproduction steps, affected endpoints, code-level remediation guidance, and severity scores
- Executive report: It is a quick-read doc with minimal technical jargon for C-level executives to quickly grasp the key information without having to sift through multiple pages of deep technical information.
- CI/CD integration output: Machine-readable JSON/SARIF formats that feed directly into GitHub Advanced Security, Jira, or Slack notifications for immediate triage
When Automated Pentesting Makes Sense?
Automated penetration testing shines in environments where speed, frequency, and scale matter more than exhaustive human creativity.
It makes the most sense in the following scenarios:
- Fast-moving development teams using agile or DevOps workflows with weekly or daily releases.
- Large or dynamic attack surfaces where manual testing becomes impractical due to size and constant evolution.
- Continuous compliance and monitoring needs for standards like PCI DSS, SOC 2, HIPAA, or ISO 27001. Frequent automated scans provide ongoing evidence, track posture drift, and reduce audit surprises.
- Resource-constrained organizations that need cost-effective, repeatable security validation without paying for expensive annual engagements.
However, automated pentesting falls short in certain situations:
- Highly complex business logic or custom workflows (e.g., intricate financial calculations or domain-specific rules) that require a nuanced understanding and creative chaining beyond scripted paths.
- Final validation before major launches or high-stakes compliance audits, where regulators or stakeholders often expect detailed human-led reports with proof-of-concept exploits and tailored risk narratives.
The answer to these gaps is knowing when to layer human expertise on top. For complex business logic, bring in a manual pentester who can spend time understanding your specific workflows before probing them.
In practice, the organizations with the strongest security posture use automated penetration testing to run security tests continuously in the background, while reserving human expertise for the moments when creativity, context, and accountability matter most.
What are the Best Automated Penetration Testing Software Tools?
Every automated pentesting tool comes with its own mix of strengths and limitations. Only a handful of tools truly emulate full-attacker behavior from initial access through to impactful compromise, and those stand out as the ones that deliver value.
To cut through the noise, we rigorously tested leading platforms on various criteria.
We focused first on practical effectiveness:
- How capably does the tool tackle complex, multi-stage attack scenarios?
- Can it reliably scan behind login walls while preserving session integrity?
- How it handles false positives, etc
We also evaluated ongoing monitoring features, because a one-off scan loses relevance the instant your environment changes.
Here are the three tools we recommend most highly.
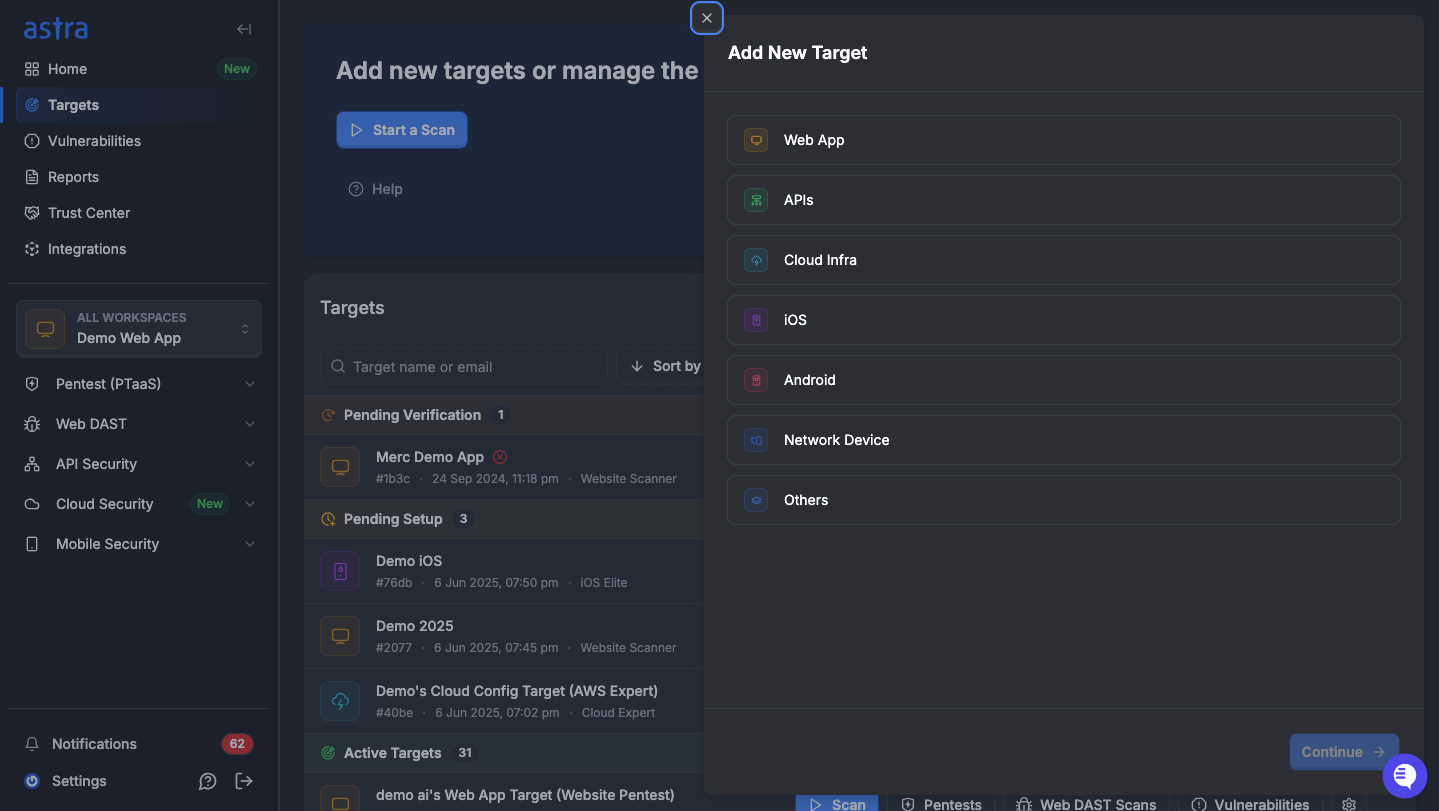
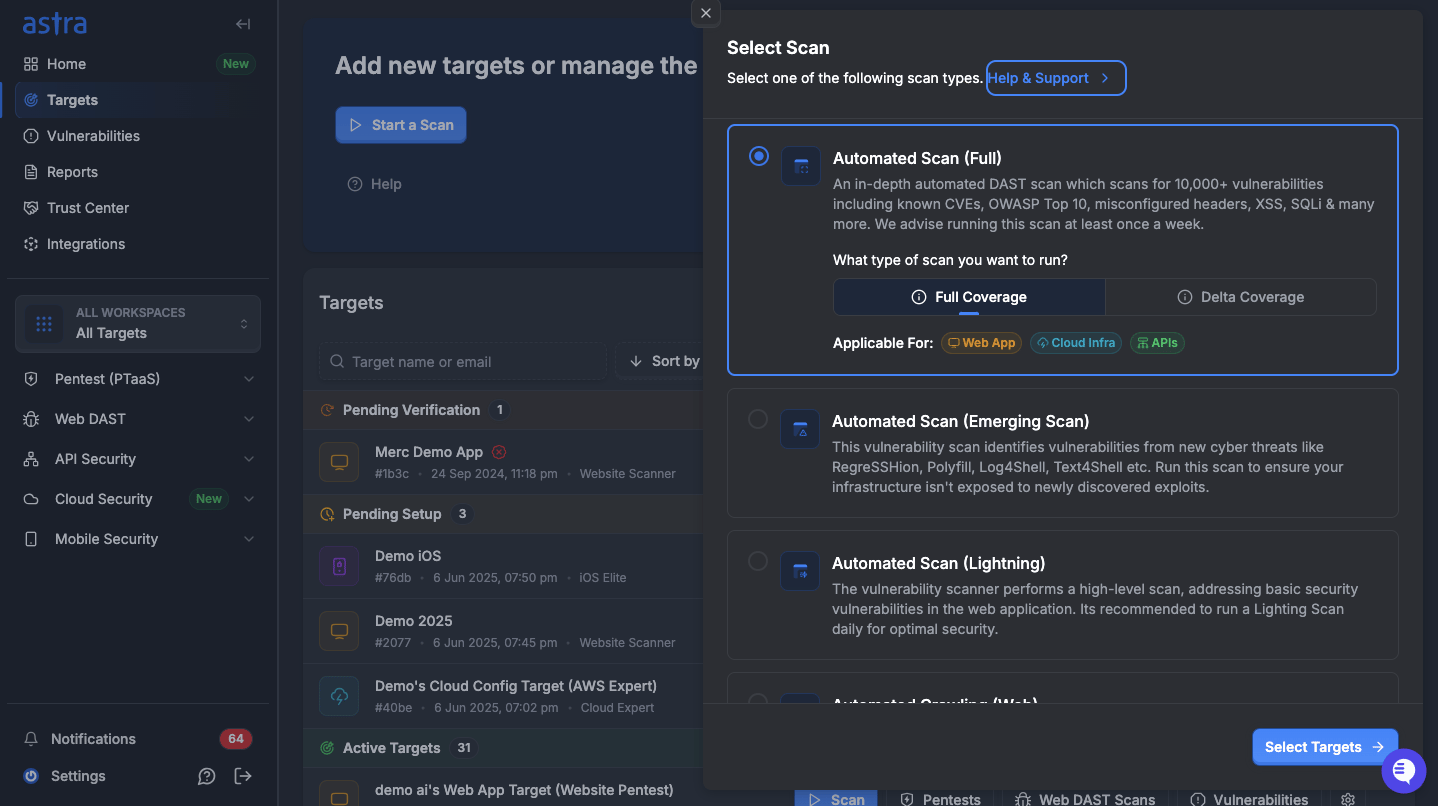
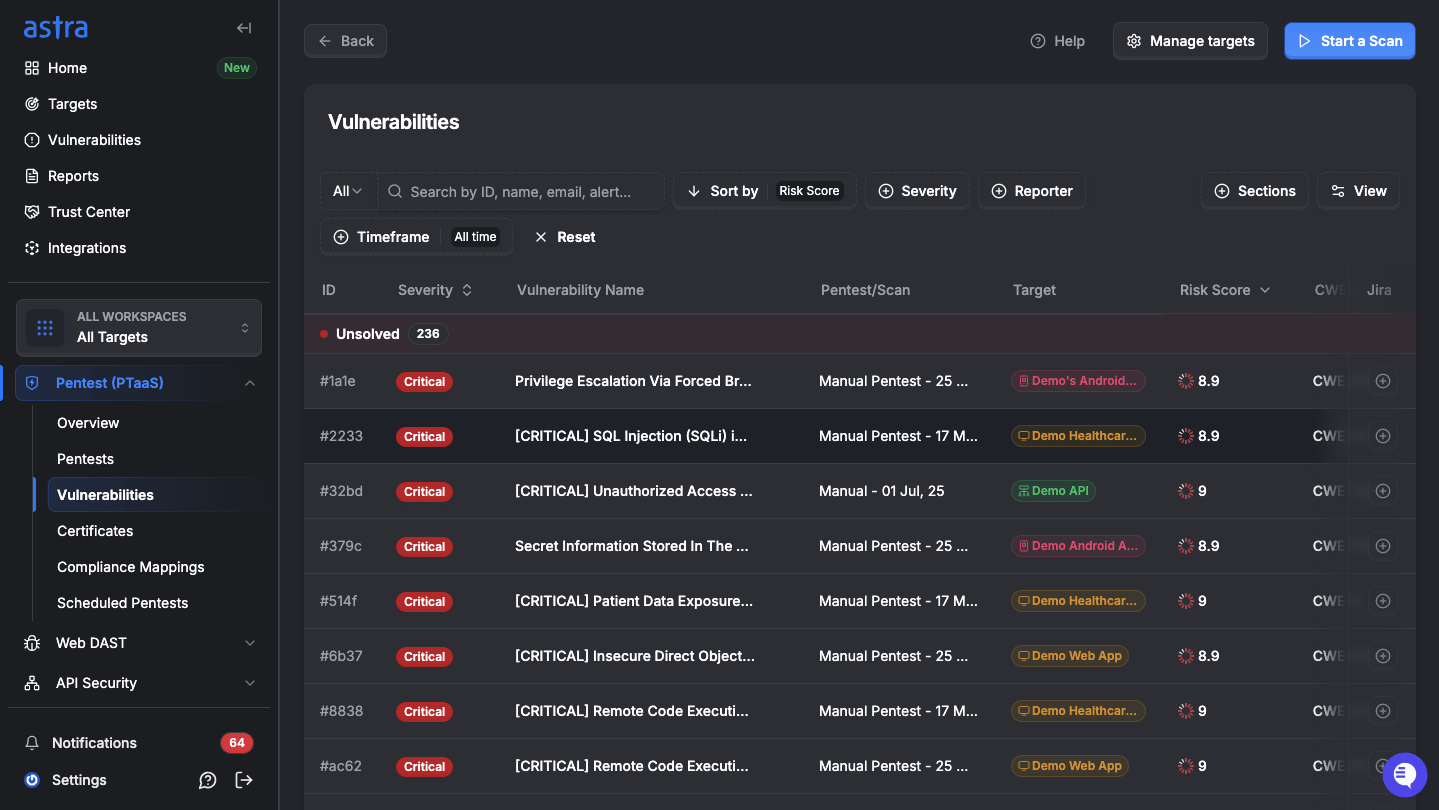
1. Astra Security Automated Pentest
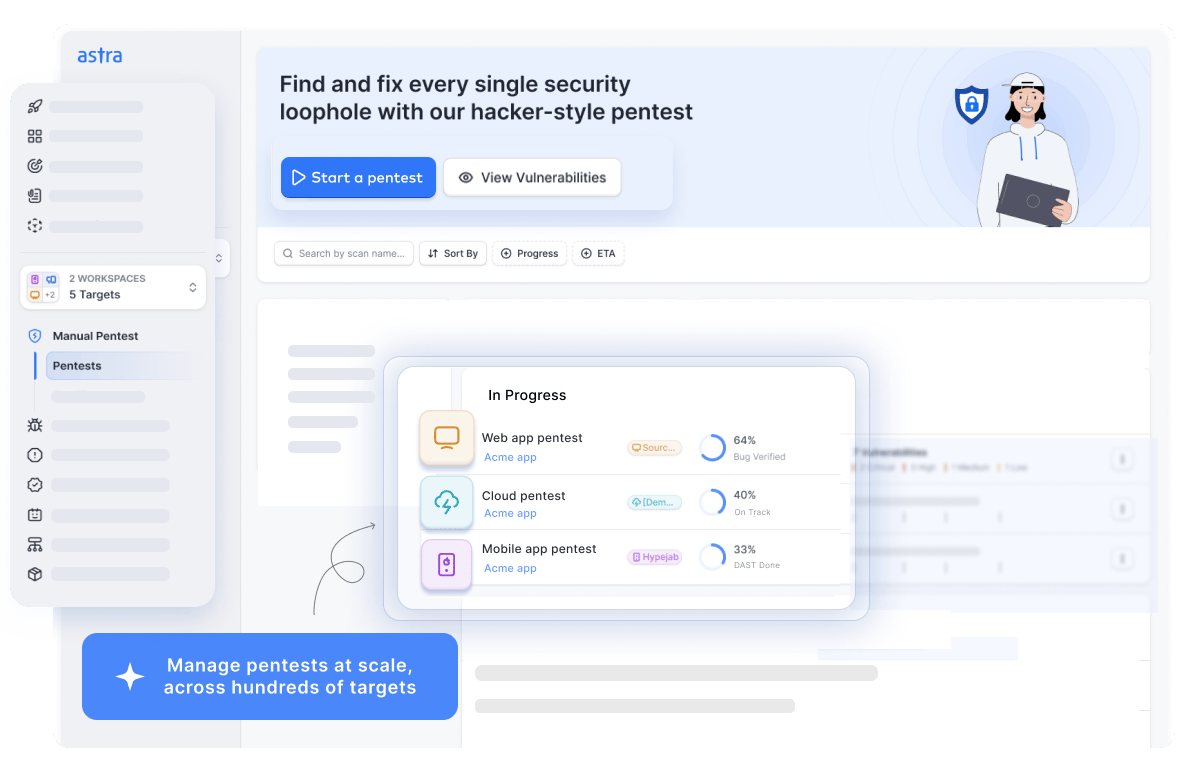
Astra Security is one of the premier providers of automated penetration testing, delivering powerful, continuous security testing that keeps pace with today’s dynamic environments.
Astra Security’s automated penetration testing platform executes over 15,000 security tests to detect both existing and emerging vulnerabilities across web applications, APIs, and other assets.
With expert-vetted scans, Astra security achieves zero false positives, while its in-depth, hacker-style automated penetration tests uncover high-severity issues that matter most/The platform’s intelligent vulnerability scanner also includes a convenient Chrome extension for capturing login sequences and authentication flows. This lets you run authenticated scans behind login pages, eliminating the need to re-enter credentials every time
Pros:
- Seamlessly integrates with your CI/CD pipeline.
- Run compliance-specific scans.
- Scan behind logins for comprehensive security.
- Offers manual penetration testing and contextual expert consultation.
Limitations:
- Only 1-week free trial, available at $7.
Experts Review
What our Customers Have to Say?
“I appreciated that Astra Pentest was very responsive and professional. They are attentive and very accommodating, with quality advice. They provided an important pentest certificate for our business. Thanks to a chat on Slack, they were able to answer all our questions quickly and perfectly assisted us in resolving issues. I consider their service to be good value for money, with good support.” – SMB Owner (Source: G2)
2. NodeZero by Horizon3
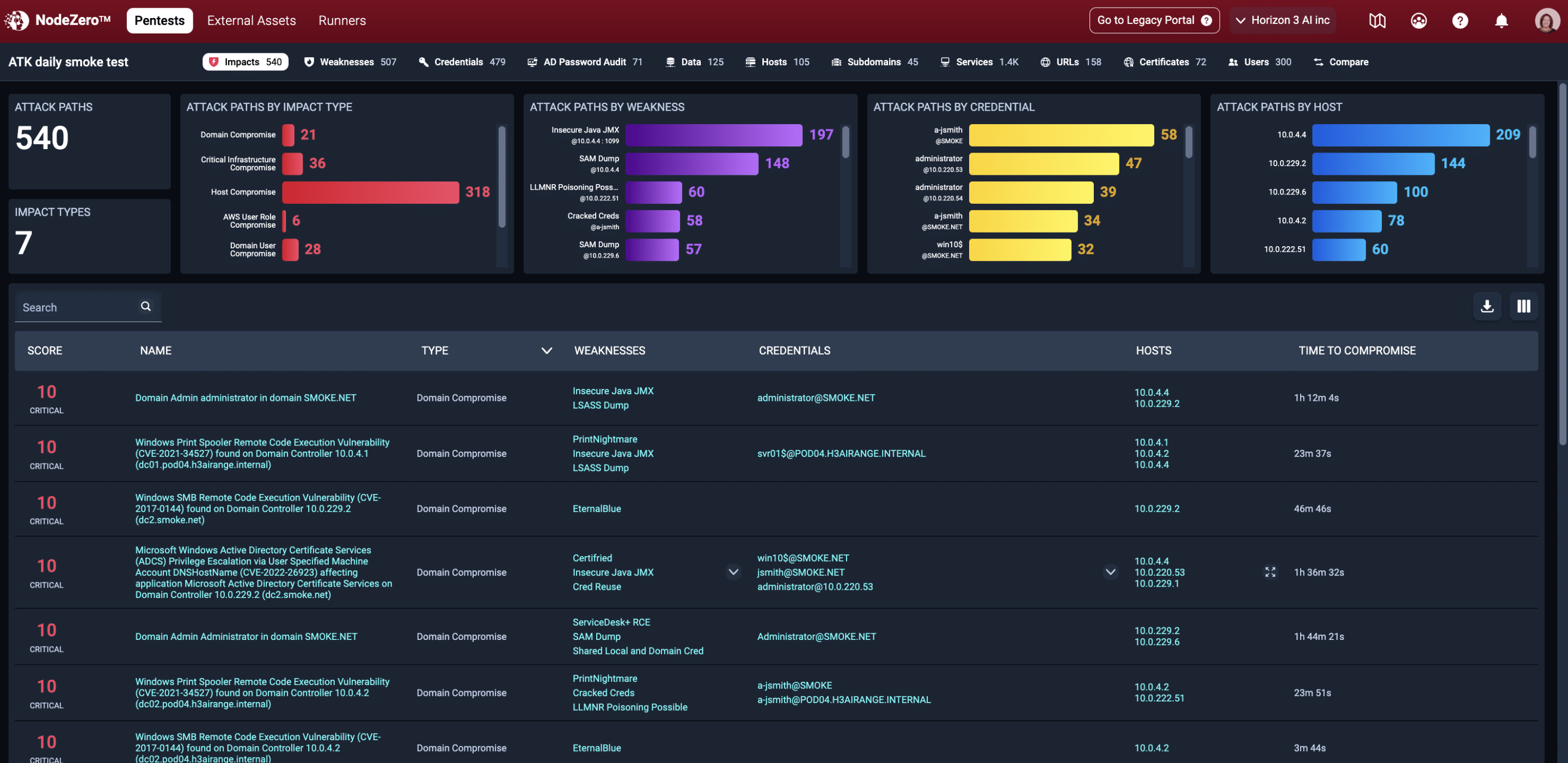
NodeZero by Horizon3 takes a comprehensive approach to an automated pentest by leveraging your organization’s existing infrastructure access. It seamlessly integrates with your cloud, IAM, and network infrastructure to run grey-box pentests that probe for vulnerabilities.
Pros:
- Easy to set up.
- Provides detailed steps for remediation.
Limitations:
- Overall, risk-based categorization can be better explained.
- It can be a little expensive for SMEs.
Experts Review
What do Customers Have to Say?
”Nodezero has given our organization the ability to conduct penetration testing in a reliable, repeatable en affordable way. Horizon3 excels at identifying vulnerabilities that can be exploited. Nodezero helps to reduce the attack surface.” – Manager/ Business Consultant (Source: Gartner)”
For Security Analysts:
3. Burp Suite Professional Edition
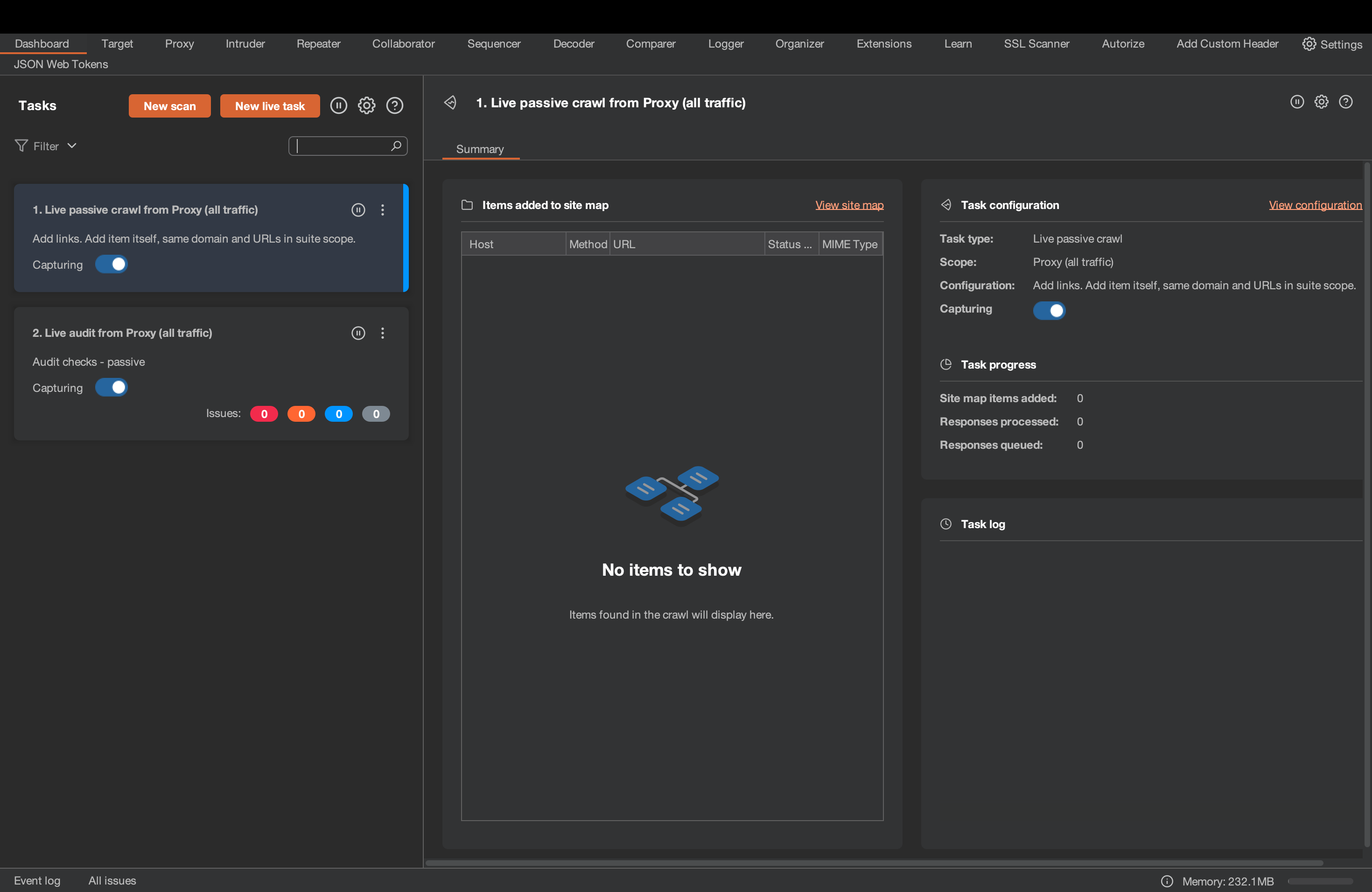
Burp Suite Professional’s automated tool for penetration testing takes a targeted approach to vulnerability management lifecycle with identification, prioritizing efficiency and accuracy. It leverages a powerful crawler to map your web application and APIs, ensuring comprehensive coverage meticulously.
While a free Community Edition is available for basic exploration, the Professional focuses on pinpointing high and critical vulnerabilities to help you address the most pressing threats first.
Pros:
- Offers a variety of extensions to enhance performance.
- Offers a free community edition.
Limitations:
- Limited coverage of limited and informational findings.
- Crashes and socket connection errors have been reported.
Experts Review
What do Customers Have to Say?
“As a Cyber security analyst i use burpsuite every day its the one and only option for web application and android penetration testing. Its has the best user friendly interface and even a beginner can easly study its working”- Security Analyst (Source: G2)
What is the Cost and ROI of Automated Pentesting?
Automated penetration testing platforms typically cost $1,500 to $10,000 per year, depending on coverage depth, testing frequency, and compliance features. This makes them far more affordable than traditional manual penetration tests, which often range from $5,000 to $50,000+ per engagement.
Since these platforms handle correlation, retesting, and real-time verification, you can eliminate 40–70% of the manual work tied to scheduling tests, validating fixes, and coordinating with external consultants, avoiding the engineering slowdowns that manual bottlenecks often create.
Simply put, automated pentesting often delivers a 5–10× ROI in the first year for organizations with active development cycles, alongside measurable reductions in breach likelihood as estimated below:
- Penalty avoidance from $10,000+ (SOC 2) to $50,000–$100,000+ for PCI DSS or HIPAA
- 30–50% faster remediation cycles thanks to early regression detection
- 60–80% fewer high-severity audit surprises due to continuous issue discovery
What are Some Essential Features to Look For in an Automated Penetration Testing Tool?
Automated penetration testing tools can look similar on the surface, but their fundamental differences show up in how they handle depth, accuracy, scalability, and reporting. Here are the most critical features to evaluate when selecting one for modern security needs:
1. Pentesting Depth and Breadth
Select a tool capable of broad vulnerability coverage (high volume of tests across OWASP Top 10, CVEs, misconfigurations, and business-logic issues) combined with deep simulation of real-world attack chains. It should go beyond surface scans to test authenticated areas, behind the login wall, and provide complete visibility into exploitable paths.
2. Zero False Positives
Simply put, false positives refer to the number of times the tool incorrectly identifies a harmless issue as a critical vulnerability. Look for automated pentesting software that minimizes or provides manual validation to verify and eliminate false positives.
3. Integration
Look for automated tools that integrate seamlessly with your Continuous Integration / Continuous Deployment (CI/CD) pipeline. This helps automate regression testing after every staging or production environment update.
4. Compliance-Aligned Testing
Focus on automated scanners that help you identify vulnerabilities that specifically violate compliance standards and industry regulations, such as SOC2, HIPAA, GDPR, PCI DSS, and ISO.
5. Exhaustive Reports
Choose an automated pentest tool that generates exhaustive reports tailored to different audiences. It should provide in-depth reports for developers and executive summaries for management to facilitate quick decision-making.
Final Thoughts
Automated penetration testing stands as a powerful, scalable ally in modern cybersecurity strategy. It delivers the speed, frequency, and cost-efficiency needed to match agile development cycles, catch issues early, and maintain continuous security validation.
Yet no automated tool can match the human pentest. For the strongest defense, the most effective approach combines the best of both worlds. Platforms like Astra Security exemplify this hybrid model, blending intelligent AI-driven automation with expert-vetted scans and manual oversight to minimize blind spots while maximizing efficiency.
In the end, AI and machine learning are undeniably shaping the future of penetration testing smarter and more accessible, but the human element remains essential for true depth and assurance.
FAQs
1. What is Penetration Testing?
Penetration testing is a simulated cyberattack that identifies vulnerabilities in systems, networks, or applications to strengthen the overall security posture before a real attacker can exploit them.
2. Should I do manual or automated penetration testing?
An automated pentest is fast and cost-effective, while manual penetration testing offers a deeper dive by security experts, uncovering trickier vulnerabilities.
A hybrid approach delivers the best coverage. For most organizations, starting with automated testing continuously and layering in manual engagements quarterly or pre-release strikes the right balance
3. Can AI do penetration testing?
Although AI can’t fully replace penetration testers, it is a powerful sidekick. AI-powered tools automate repetitive tasks, analyze vast data for vulnerabilities, and prioritize threats. This frees up testers for strategic thinking and complex exploits, making pentesting more efficient.
4. What are some open-source automated penetration testing tools?
Popular options include:
Nmap (network discovery)
OpenVAS (vulnerability scanning)
Metasploit (exploitation framework)
OWASP ZAP and Burp Suite Community Edition (web app testing).
5. What are the advantages of automated penetration testing?
It’s fast (scans large systems in hours), cost-effective, repeatable, scalable, and provides continuous security validation. This frees up security professionals for deeper analysis while also reducing the risk of human error in testing.
Automated tools also enable consistent coverage across environments, so every new deployment or code change gets tested.