PCI penetration testing is vital if you are in the business of handling credit cards or any other personally identifiable information and payment information to ensure PCI compliance. The best way to ensure that you are a legal entity that secures its customer data is through the continuous maintenance of compliance.
PCI penetration testing is one of the most important and overlooked parts of the PCI-DSS regulation. This blog will look at what PCI pentesting is, what it involves, and why it is essential.
What is PCI-DSS?
The Payment Card Industry Data Security Standard (PCI DSS) is a set of data security standards put forth by the Payment Security Standards Council (PCI-SSC) for payment industry stakeholders to adopt for safe payments worldwide.
The standard has kept pace with the ever-changing landscape for years. The standard is an information security standard for organizations that handle branded credit cards from major card schemes.
The payments industry created the standard to provide a validated set of requirements for any business that handles credit card information. The standard is a multi-layered set of requirements that help organizations protect the integrity and security of cardholder data. It includes provisions for policies, procedures, network architecture, software design, and other critical protective measures.
The PCI DSS standard has 12 requirements that define the controls that merchants, service providers, and vendors must implement to protect cardholder data.
What is PCI Penetration Testing?
PCI Penetration testing is the process of testing a developed or in-development application for security vulnerabilities. In a fundamental sense, it is finding security flaws in applications and resolving them.
Data security is a constantly changing landscape. There are new threats to consider, new regulations to abide by, new testing products, and new technologies to learn. It is no surprise that it can get overwhelming for security teams.
While a penetration test is not a replacement for a full-scale audit, it can help a business assess its applications or websites’ security and identify potential risks and problems.
Businesses most often use PCI Compliance Penetration Testing to:
- Identify security vulnerabilities
- Reduce the risk of getting hacked
- Achieve compliance with industry standards
- Provide evidence of compliance with industry standards
- Builds trust among customers by being security-conscious.
PCI-DSS Penetration Testing Requirements and Its Importance
PCI-DSS penetration testing is an essential activity to ensure the security of payment systems. It helps you discover, prevent, and ultimately mitigate security vulnerabilities. It also allows you to identify weaknesses and vulnerabilities.
PCI pentesting is also an essential part of the compliance process as it verifies that the deployed solutions are in line with the security standards and protection requirements.
According to PCI DSS Requirement 11.3:
Develop and implement a methodology for penetration testing that includes external and internal penetration testing at least annually and after any significant upgrade or modification. If segmentation is used to reduce PCI DSS scope, perform penetration tests at least annually to verify the segmentation methods are operational and effective.
Requirement 11.3 is part of the Payment Card Industry Data Security Standards (PCI DSS) that requires you to develop and implement a methodology for penetration testing that includes external and internal penetration testing at least annually and after any significant upgrade or modification.
See Also: How to Achieve Security Compliance with NIST Penetration Testing?
How is PCI-DSS Penetration Testing Performed?
PCI compliance penetration testing involves several steps that need to be followed in a specific order. Let’s understand what these steps are and how they are performed.
Step 1: Scoping
Scoping is the first step in penetration testing in which the scope is defined for the penetration testing. The scope of the testing must be defined before the start of the testing. Scope determines the limitations and rules of the testing.
Step 2: Reconnaissance & Discovery
It includes gathering information about the target network. The data collected during this step can be used to determine the attack vectors. This step also involves the identification of all the hosts in the target network and their respective services.
Step 3: Exploitation
In this step, the attacker tries to exploit vulnerabilities in the available services to get unauthorized access to the target system. Exploitation can take multiple forms, including DoS attacks, SQL injections, or a buffer overflow.
Step 4: Reporting
The final step of a penetration test involves reporting all the findings to the organization. The report should contain detailed information about the vulnerabilities found in the network, their possible impacts, and recommendations to fix them.
Step 5: Re-scanning
After the remediation of the vulnerabilities, the penetration test needs to be repeated to ensure that the vulnerabilities have indeed been fixed.
Step 6: Continuous Scanning
Continuous scanning through CI/CD integration so that new features are checked for vulnerabilities as well.
Also Read: A Brief Look into Penetration Testing Methodology | API Penetration Testing: What You Need to Know
PCI Pentest Checklist
The PCI pentest checklist mentions the points to carry out during each phase of a PCI pentest.
- Using DNS querying, port scanning, and packet sniffing to discover target information.
- Carrying out authenticated and unauthenticated vulnerability scans to identify vulnerabilities in software and networks.
- Exploitation of vulnerabilities using concept-based attacks unique to each vulnerability and post-exploitation removal of codes, or configurations from the pentest.
- Creating a report with major components such as an executive summary, findings and recommendations, methodologies, and conclusion.
3 Things to consider while choosing PCI Penetration Testing Provider?
During your search for pentest providers, you will come across a lot of companies that provide this service. This can be a good thing, as you will have plenty of options.
However, it also means that you will have to make a considerable effort to sort the wheat from the chaff. Therefore, in the following lines, we will outline 3 things you should consider when choosing a Penetration Testing Provider.
1. Remediation Assistance: With penetration testers who are experts in their field, collaborating to fix vulnerabilities is made easy. You will find a large number of service providers in the market, but you need to confirm that they are well-versed in providing this service to you.
2. Check the Service Level Agreement: A good service level agreement will have all the details about the testing methodology, deliverables, and exclusions. This will help you to understand the service quality and the time period for which you are going to get the service.
3. Reputation: Before choosing a service provider, you should research their reputation and reviews. Check out their past projects and talk to their previous or existing clients.
4. Continuous Scanning: Ensure the company provides continuous scans to ensure that any vulnerabilities arising from new features or patches are found quickly. Continuous scans are also important to maintain compliance with regulatory standards like PCI-DSS and HIPAA.

How often should I perform PCI Penetration Testing?
PCI-DSS recommends penetration testing to be conducted at least annually for all merchants that store, process, or transmit payment card data as well as upon having major updates to the systems. It recommends quarterly vulnerability scanning for merchants that use a third party to store, process, or share payment card data on their behalf.
The requirement to perform quarterly penetration testing does not apply to merchants that use a third-party service provider that conducts penetration testing in accordance with PCI-DSS requirements on the merchant’s behalf.
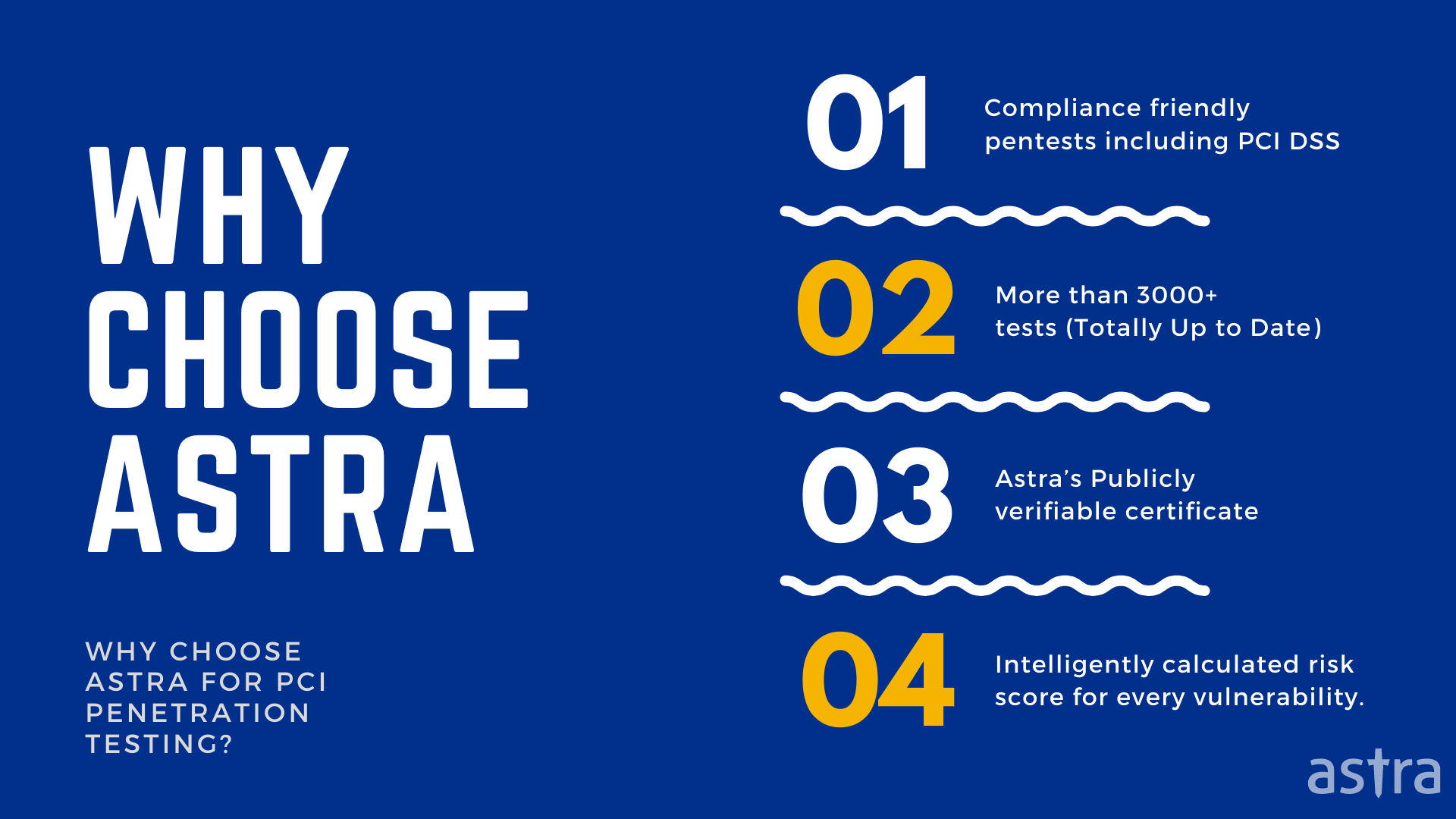
Why is Astra a trusted PCI Penetration Testing Provider?
The answer to the question above is pretty simple. Astra is a trusted PCI Penetration Testing Provider and CREST-accredited platform because of how we work. Our team works day and night to make sure no vulnerability is left. We have a proven track record of delivering top-notch penetration testing services to our clients.
Performance, accuracy, and stability are the three fundamental pillars that define Astra’s security testing and vulnerability assessment approach. We have the most skilled and experienced security experts who can uncover vulnerabilities that may otherwise be missed.
P.S: All Our Pentests are Compliance Friendly
Conclusion
Penetration Testing is the way to go if you want to ensure that your company is protected against cybercriminals and hackers. A hacking attempt can have devastating effects on your company’s reputation.
A successful penetration test will help you find and fix these vulnerabilities before someone else does. You’ve worked hard on building your business and protecting your customers, so don’t let a single misstep cause substantial financial losses or public humiliation. If you need help with Penetration Testing, feel free to contact us.
Thank you for reading. We are always excited when one of our posts can provide helpful information on this topic!
FAQs
Who needs penetration testing for PCI compliance?
Companies and merchants that deal with cardholder data, technology, and processes are required according to PCI-DSS to conduct penetration tests at least annually or after major updates to their applications or systems.
What are the qualifications for a PCI penetration tester?
Qualifications for PCI penetration testers come in the form of certifications such as OSCP (Offensive Security Certified Professional), CEH (Certified Ethical Hacker), CREST penetration testing certifications, and GIAC certifications.








