NIST penetration testing is a security control listed by NIST or the National Institute of Standards and Technology. Penetration testing provides the best representation of the risks a network faces. Penetration testers detect exploitable vulnerabilities like weak passwords, & weak firewall rules.
NIST is an agency under the U.S. government’s Department of Commerce. It provides various standards, & frameworks concerning cybersecurity and its security controls. This article mentions NIST penetration testing as a security control under NIST SP 800 -53 and NIST SP 800 – 171.
What is NIST Penetration Testing?
NIST penetration testing refers to looking for exploitable vulnerabilities in software or networks and finding out whether an organization is following the cybersecurity framework prescribed by the National Institute of Standards and Technology (NIST). These tests are conducted according to the NIST penetration testing framework.
What is NIST, and Who needs to adhere to it?
NIST is a non-regulatory governmental agency that develops technology, metrics, and standards to assist businesses and individuals in the science and technology industry by helping them reach their highest potential. They have developed a cybersecurity framework known as NIST Cyber Security Framework that businesses and governments use to secure their data and networks.
If you are a company developing, implementing, or operating critical IT infrastructure, you will need to adhere to the NIST compliance framework. The framework is a set of standards created in 2013 and updated in 2016 to address new threats and vulnerabilities in the cybersecurity industry.
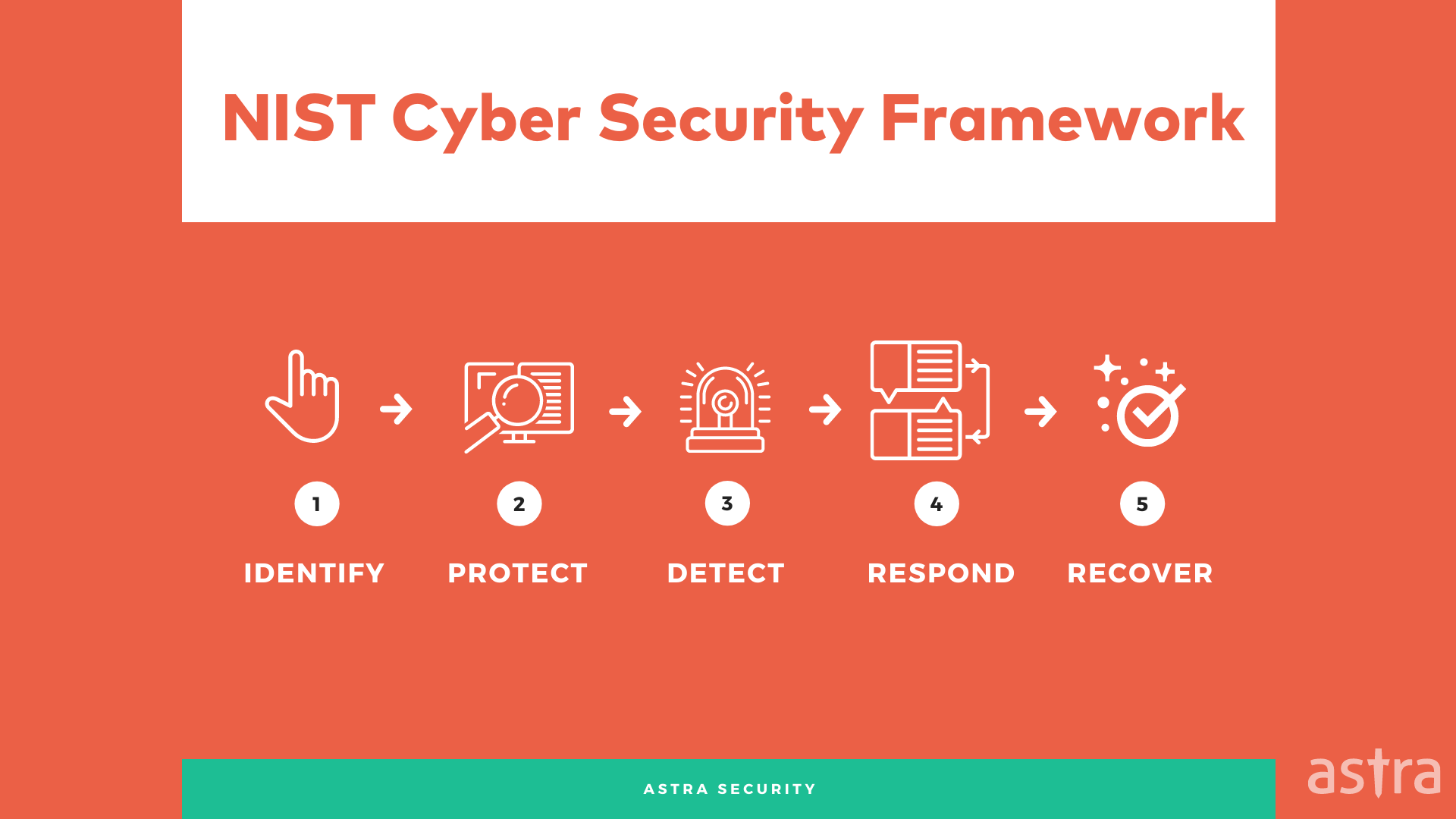
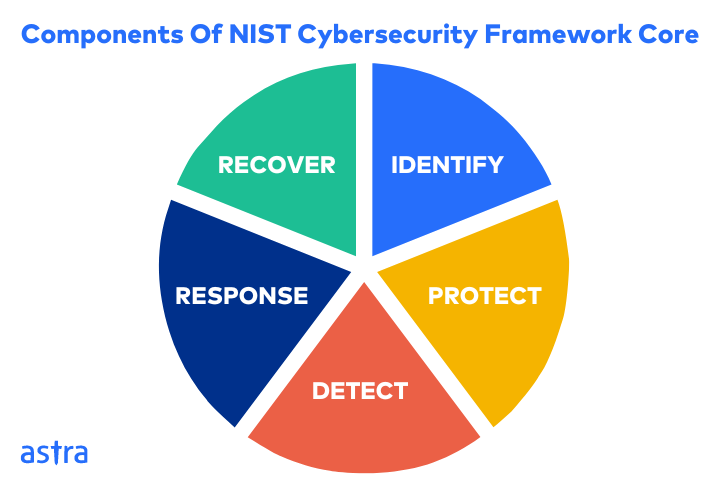
The framework is built around five critical components:
- Identify
- Protect
- Detect
- Respond
- Recover
NIST helps businesses securely supply, operate, and own their critical infrastructure. It is a framework developed by the people, collaborating with businesses, academia, and federal agencies. The framework can be used by anyone in any industry that manages or operates critical infrastructure.
What is NIST 800-53?
NIST Special Publication 800 – 53 is titled “Security and Privacy Controls for Federal Information Systems and Organizations“. It is also used for developing and implementing IT protocols for government agencies. Some security controls mentioned include risk assessments, access control, and configuration management.
NIST special publication 800-53 is the set of guidelines or security controls that should be followed by federal institutions and data systems. The security controls help determine the requirements for securing federal agencies with various impact levels like low-impact, moderate-impact, and high-impact.
What is NIST 800-171?
NIST 800-171 is the national standard for unclassified information developed by the National Institute of Standards and Technology. It covers compliance within federal civilian departments and agencies (companies on contract), as well as non-federal country organizations that are operating in accordance with the law.
NIST 800-171 is a set of standards that helps to protect classified information from leaking out of a computer system. The publication was developed by the National Institute of Standards and Technology (NIST) to help companies, organizations, and even government agencies protect CUI from unauthorized disclosure.
The main difference between NIST 800-53 and NIST 800-171 is the target audience, i.e. NIST 800-53 is governmental and federal agencies and organizations whereas NIST 800-171 mostly applies to civilian companies that have contracts with federal institutions.
Understanding NIST Cyber-Security Framework
The National Institute of Standards and Technologies Cyber Security Framework (NIST CSF) is a set of standards to help companies improve their overall cybersecurity posture.
The NIST CSF defines a set of best practices that enables IT organizations to more effectively manage cybersecurity risks. The NIST CSF is made up of five core functions, or sets of activities, that can be used to manage cybersecurity risks.
The NIST Cybersecurity Framework is a unified way of thinking about cybersecurity. It has five pillars, which you can see here, but in essence, it is a list of best practices that will allow businesses to be proactive in the face of cyberattacks, rather than just being reactive.
Well-known security firms have already started to adopt this framework, and the government is in the process of doing the same, making it easier for businesses to comply with their regulations.
Why is NIST Framework important?
The National Institute of Standards and Technology, better known as NIST, plays a major role in protecting our nation’s information systems. NIST is responsible for developing standards, guidelines, and associated methods and techniques to strengthen the security and privacy of all U.S. Federal computer systems, including those used by the Defense Department, the intelligence community, and the judiciary.
The organization is also responsible for developing standards that all federal agencies can secure their information systems.
The NIST Framework aims to help organizations secure their data and network. It is an internationally accepted cybersecurity standard that is used by many countries in the world.
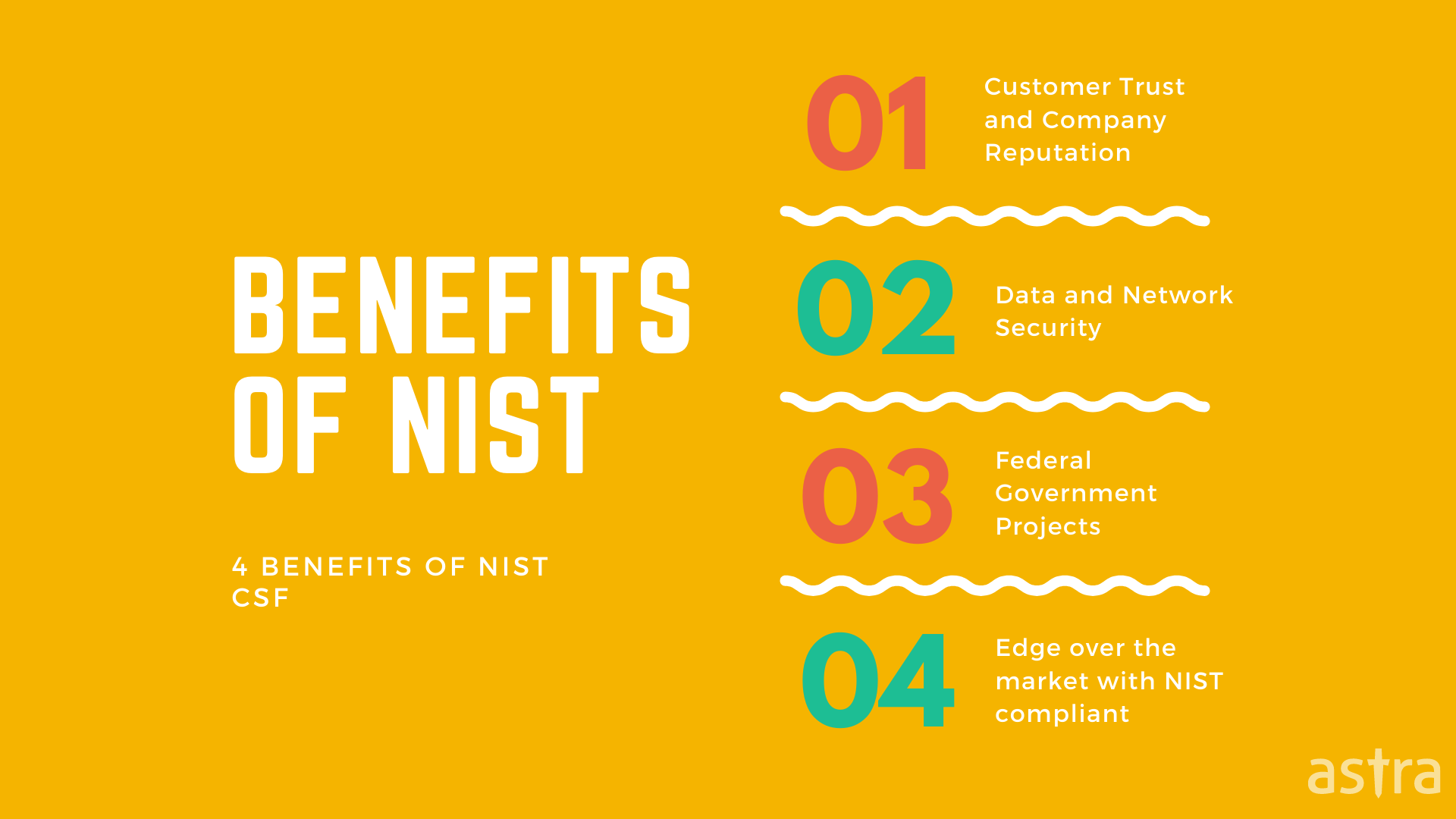
Some of the most common benefits to comply with NIST are:
1) Keeping the customer’s data safe and secure from cyber-attacks
2) Having the edge over the market with a better reputation and customer trust.
3) Protecting company data and network
4) Getting in line for government projects or contracts.
Checkout Astra’s Sample Penetration Testing Report (VAPT Report)
How important is Penetration Testing for NIST?
According to NIST (National Institute of Standards and Technology), vulnerability scanning of systems and devices needs to be conducted to ensure that systems are safe and secure.
Let’s understand the NIST penetration testing requirements. According to NIST 800-171, 3.11.2 and 3.11.3 are compliance requirements that need NIST penetration testing.
3.11.2: Scan for vulnerabilities in organizational systems and applications periodically and when new vulnerabilities affecting those systems and applications are identified.
According to 3.11.2, organizations that need to comply with NIST need to make sure that the software. Applications and the systems of the organization are very well tested. Companies opt for NIST penetration testing to ensure that everything is tested well and that there are no security risks in any organization’s assets.
Security analysis while NIST penetration testing may also require different approaches such as:
- Static Analysis
- Dynamic Analysis
- Binary Analysis
- Hybrid Analysis
3.11.3: Remediate vulnerabilities in accordance with risk assessments.
According to 3.11.3, all the vulnerabilities found while NIST penetration testing needs to be remediated considering the related risk assessment.
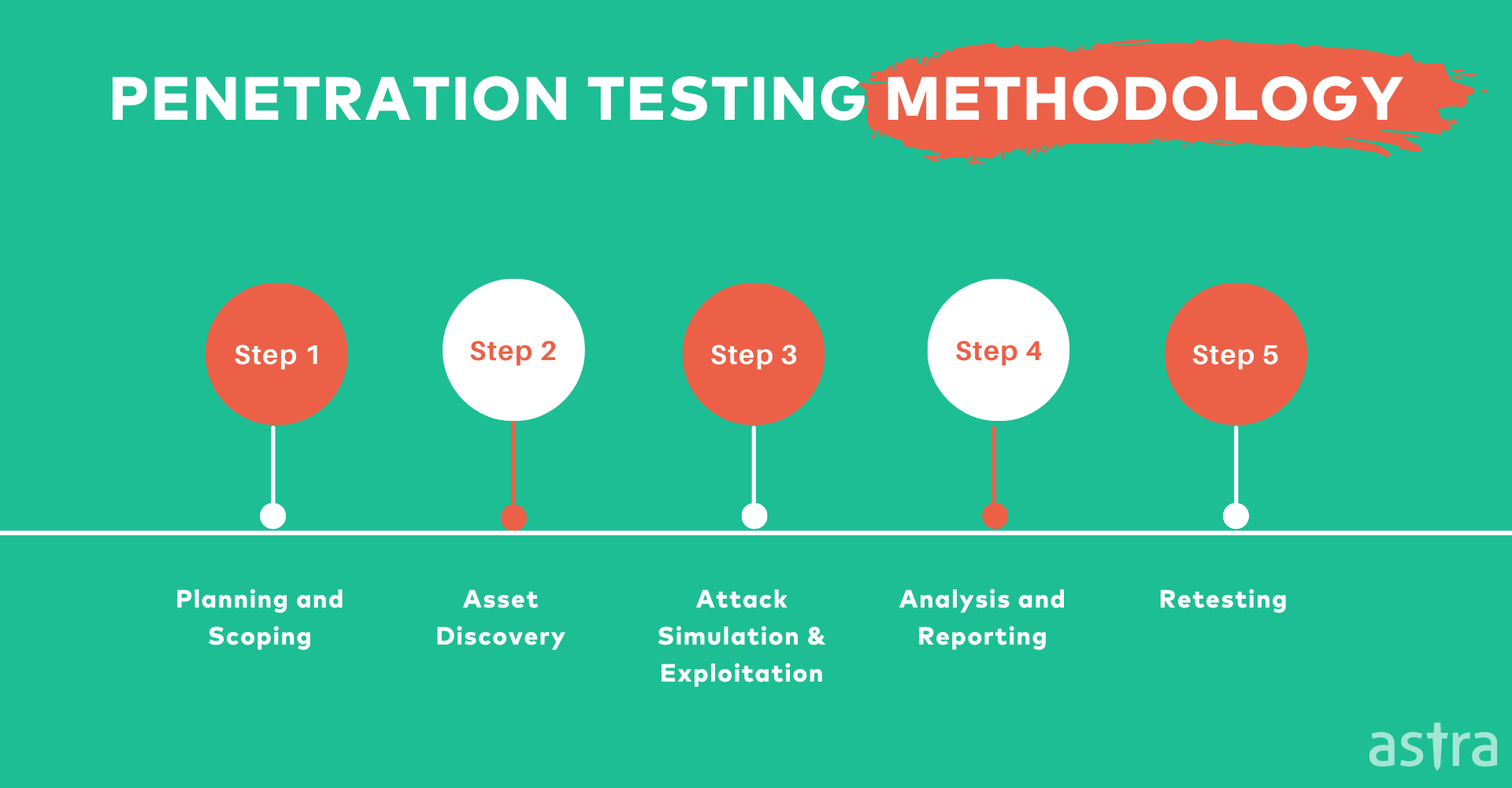
NIST Penetration Testing Phases
The following are the steps that are followed during the NIST penetration testing process.
Reconnaissance of Target
It includes gathering information about the target network. The data collected during this step can be used to determine the attack vectors. This step also involves the identification of all the hosts in the target network and their respective services.
Identification Of Vulnerabilities
Once the reconnaissance and associated planning are carried out prior to the pentest, the next step is to use the information to carry out scans on the assets to detect the vulnerabilities. The vulnerabilities detected are then identified for exploitation.
Exploitation of Vulnerabilities
This is the step in NIST cybersecurity framework penetration testing the attacker tries to exploit vulnerabilities in the available services to get unauthorized access to the target system. Exploitation can take multiple forms, including DoS attacks, SQL injections, or a buffer overflow.
Reporting Vulnerability Findings
The final step in the NIST penetration testing methodology involves reporting all the findings to the organization. The report should contain detailed information about the vulnerabilities found in the network, their possible impacts, and recommendations to fix them.
Core Functions of NIST Framework
This section deals in detail with the core functions under NIST penetration testing guidelines.
Identify
This function relates to laying a solid foundation for an effective cybersecurity program. Identification is beneficial in gaining a thorough understanding of the cybersecurity risks posed to the assets, users, data, and other processes.
It entails listing out all of one’s organizational assets, equipment, users, software and more thus enabling companies to take a more focused approach to cybersecurity implementation. The function stresses the value of knowing the business context, critical resources, and related risks within them.
Protect
This CSF function ensures the development and implementation of appropriate safeguards to ensure the smooth delivery of critical infrastructure services.
Essentially this involves setting certain cyber measures such as access controls, data security measures such as encryption, and more.
Detect
This step refers to the detection and identification of a cybersecurity event based on the implemented detection activities in a timely manner.
Detection usually involves:
- Quick detection of anomalies and events to understand their potential impact.
- Constant monitoring of cybersecurity events to verify the effectiveness of protective measures.
- Computers, other devices, and even software are monitored.
- The network is scanned for the presence of unauthorized users.
Respond
Based on the detected cybersecurity events, appropriate actions are taken as a response to it and work towards containing the impact of the incident.
Essentially activities that come under response are:
- Ensuring that there is a well-set response plan in place.
- Ensure the execution of the response plan before and after the cyber incident.
- Managed communication with various stakeholders.
- Incident analysis to ensure that appropriate response and recovery activities have taken place to determine the impact.
Recover
Appropriate plans are taken and implemented to take a stance against cybersecurity events. Activities in recovery include:
- Recovering and restoring parts of the assets that faced the damages i.e. networks and computers.
- Employees and customers are highly aware of response and recovery activities.
NIST Penetration Testing Guidelines
The following guidelines are a part of NIST’s special publication 800 – 53 which addresses penetration testing as one of the security controls to be implemented.
- The organization decides and defines the systems and system components to be pentested.
- The organization should base the frequency and coverage of pentest on the risk assessment results.
- Pretest analysis should be carried out with full knowledge of the systems and their components.
- All potential vulnerabilities should be identified before exploitation.
- The exploitability of the identified vulnerabilities is determined through rigorous testing.
How Astra’s Pentest can help you achieve NIST?
Astra is a leading provider of penetration testing services. We provide organizations with the tools they need to achieve compliance, optimize risk management, and protect their networks from internal and external threats.
As a trusted partner of leading organizations, we have the skills and expertise to seamlessly integrate penetration testing, vulnerability assessments, and security management into your existing processes. Astra’s penetration testing is completely compliance-friendly, be it NIST, PCI DSS, or any other.
Benefits of using Astra’s Compliance Friendly Pentest:
- Automated Scanner with more than 2600+ tests to keep your application safe.
- Manual scanning along with scanner to make sure no security risk is left.
- Easy, accessible reports that you can interpret at a glance with the dashboard.
- Get detailed steps on bug fixing tailored to your issues and know exactly how to reproduce vulnerabilities with video Proof of Concepts (PoCs).
- Why keep your security status private? Showcase Astra’s Publicly verifiable certificate.
- A post penetration test, Astra shows a potential loss in $$$ for each vulnerability, making it easier for everyone to understand the impact.
- For each vulnerability, Astra gives an intelligently calculated risk score.
Check out how amazing Astra’s Penetration Testing Dashboard is:
Conclusion
Whether it’s a security audit or an assessment of your overall security posture, penetration testing is an important part of the NIST cybersecurity framework. Contact the amazing team of penetration testers at UI today to learn more about how we can help your organization.
FAQs
1. What is the timeline for NIST penetration testing?
It takes 4-5 days to perform penetration testing and assess the vulnerabilities. Businesses have up to 30 days after the initial test completion to fix the vulnerabilities and achieve NIST compliance. Also, learn about SOC2 compliance.
2. How much does NIST penetration testing cost?
Penetration testing for NIST compliance can cost between $490 and $999 per scan based on your plan. Learn more about penetration testing costs.
3. Why choose Astra Pentest for NIST compliance?
Astra’s penetration testing is completely compliance-friendly, be it NIST, PCI DSS, or any other. It fits into your existing processes smoothly and leads you to fast and hassle-free NIST compliance.
4. Do I also get rescans after a vulnerability is fixed?
Yes, you get 2-3 rescans depending on the plan you are on. You can use the rescans within a period of 30 days from initial scan completion even after a vulnerability is fixed.

















is there any basic difference between NIST compliance and penetration testing of NIST?
Hey, so NIST is a framework with a set of requirements that help companies uphold an internationally accepted cybersecurity posture. Penetration testing of NIST is one of the requirements that need to be followed to find any vulnerabilities and fix them to ensure compliance with the NIST framework. Hope this clears it up for you.
How NIST SP 800-115 informs information security practices?
Hey Lewis, so NIST information security practices are a set of standards that when followed by companies ensure its smooth functioning and continued compliance. The practices include NIST penetration testing, security assessments, and other strategies that help increase the dependability of organizations.