Mobile apps are a part of a larger mobile ecosystem that interacts with everything from mobile devices to network infrastructure, servers, and data centers. The attack surface presented by mobile applications is further expanded with the increased use of mobile devices with advanced capabilities. With the increasing sophistication of cyber-attacks and the million-dollar bounties offered for mobile app bugs, organizations have begun investing in mobile application penetration testing.
What Is Mobile Application Penetration Testing?
Mobile application penetration testing is the process of testing mobile apps to detect and identify loopholes or vulnerabilities before they are exploited for malicious gain to analyze the severity posed by them to the application through manual or automated penetration testing.
How does penetration testing help secure a mobile app?
With more than 4.37M apps available on the Google Play Store and Apple App Store, any organization with or plans to have a mobile app should consider mobile application penetration testing to secure their customer information stored in these apps.
Mobile security testing mobile applications/software/mobile operating systems for security vulnerabilities by using either manual or automated techniques to analyze the application. These techniques are used to identify security flaws that may occur in the mobile application. The purpose of penetration testing is to ensure that the mobile application is not vulnerable to attacks.
Mobile application penetration testing is a vital part of the overall assessment process. Mobile application security is becoming a critical element in the security of any company. Also, the data is stored locally on the mobile device. Data encryption and authentication are the essential concerns of safety for organizations having mobile applications. Mobile apps are the most lucrative target for hackers. The reason is that mobile apps are used by almost all the people on this planet.
What Are The Different Types Of Mobile Apps Organizations Use?
In the mobile app industry, there are three main types of apps developers or organizations use to cater to their customers. Each class runs code on a different kind of device. Let’s take a look at these basic types and what they involve.
1. Native Mobile Apps
Native mobile apps are the ones that are downloaded on mobile devices. These kinds of apps are usually created for a specific platform like Android or iOS. Many different types of programming languages are used to build native applications such as Java, Kotlin, Python, Swift, Objective-C, C++, and React.
2. Hybrid Apps
Hybrid mobile apps are a relatively new concept for mobile development. It combines both iOS and Android applications. These apps run on mobile operating systems and can be downloaded from Google or Apple app stores. Flutter is a UI software development kit created by Google to develop cross-platform applications for Android, iOS, Linux, Mac, Windows, Google Fuchsia, and the web from a single codebase.
3. Progressive Web Apps (PWA)
A progressive web app is a web-based software. PWA is similar to native mobile apps. The purpose of PWA is to eliminate the hassles and limitations of traditional apps. It works like a regular website and can be opened and used by any browser (including mobile browsers), but the main difference is that PWA apps also function as mobile apps and can be added to the home screen to be accessed like a native app.
Why Astra is the best in pentesting?
- We’re the only company that combines automated & manual pentest to create a one-of-a-kind pentest platform
- Vetted scans ensure zero false positives
- Our intelligent vulnerability scanner emulates hacker behavior & evolves with every pentest
- Astra’s scanner helps you shift left by integrating with your CI/CD
- Our platform helps you uncover, manage & fix vulnerabilities in one place
- Trusted by the brands you trust like Agora, Spicejet, Muthoot, Dream11, etc.

5 Parameters To Test During Mobile Application Penetration Testing
The parameters for mobile application penetration testing include the below pointers.
- Architecture, design, and threat modeling: Understanding the architecture of the mobile app while performing mobile app penetration testing is a crucial step. Once understood, the manual tests must include tests for insecure design and architecture.
- Network communication: Transferring data over public networks is where hackers steal user-sensitive data. Mobile app penetration testing must focus on network communication which includes testing how the data travels over networks.
- Data storage and privacy: Clear text storage of sensitive data is a gift of attackers or hackers. Most applications store sensitive data such as user passwords, API keys, etc., in clean text, usually held in Strings.xml file.
- Authentication and session management: Mobile application tests must include testing for session management issues such as session expiration on password change, misconfigured backup codes for multi-factor authentication, etc.
- Misconfiguration errors in code or build settings: Most mobile application developers don’t care about error messages. Mobile application developers check for debug messages and error codes while developing to reveal no application-related internal information to the end-user.
Methodology of Mobile App Penetration Testing
Mobile application penetration testing is done in 4 steps mentioned below:
Step 1. Preparation and Discovery
Information gathering is a necessary process used in the penetration testing process. A few essential things to keep in mind while performing the discovery phase are:
- Understanding the design and architecture of the application.
- Understanding network-level data flow of the application
- Using OSINT to gather data
Step 2. Analysis, Assessment, and Evaluation
After the completion discovery phase, pentesters begin the analysis & assessment phase. In this phase, the application is observed before and after installation in the device. Some joint assessment techniques are as follow:
- Static and dynamic analysis
- Architecture analysis
- Reverse engineering
- Analysis of file system
- Inter application communication
Step 3. Exploitation
The exploitation phase includes testing the application with simulated real-world attacks to understand how it will behave when an attack occurs. Target mobile applications are tested with malicious payloads, for example, a reverse shell or a root exploit. A team tries all the vulnerabilities that are found by penetration testers with self-crafted and publicly available exploits.
Step 4. Reporting
Once the exploitation phase is done, the team prepares a detailed report of the attacks performed. The information usually includes which endpoints were tested, how much damage was done, risk analysis, and the vulnerabilities found with their respective steps of exploitation and remediation.
Top 5 Mobile App Security Risks

1. Insecure Data Storage
Data storage is one of the most important aspects of any application or device. If the application stores, transmits or processes sensitive information, they need to keep it secure. This usually occurs when developers incorrectly assume users or malware cannot access specific devices or system files. Hackers can access your device’s data or steal your information if you fail to store it securely.
Impact
Insecure storage of data can make it easily accessible to malicious actors. This in turn would lead to data theft and manipulation. With the data obtained, hackers can impersonate individuals and carry out identity theft. Having insecure data storage is also a violation of all privacy laws and can result in hefty fines, legal issues, and loss of revenue.
Prevention
Ensure proper encryption of data using encryption keys, TLS, and encryption of data at rest. and secure storage mechanisms. Avoid storing data on devices.
2. Untrusted Inputs
The concept of trusted user input is not new. However, most developers are not aware of how it works, what problems it might cause, and how to protect themselves from it. This is especially important for mobile applications, as most of their source code is available online, so there is no point in hiding it.
Impact
Mobile apps that don’t validate and sanitize inputs are susceptible to attacks such as SQL injections and cross-site scripting. This allows attackers to gain access to the mobile app backend, manipulate app functionality, and access sensitive information.
Prevention
Ensure proper input validation measures are in place. Additionally, enable output encoding to prevent injection attacks. Follow the best secure coding practices and use frameworks that offer built-in security against vulnerabilities.
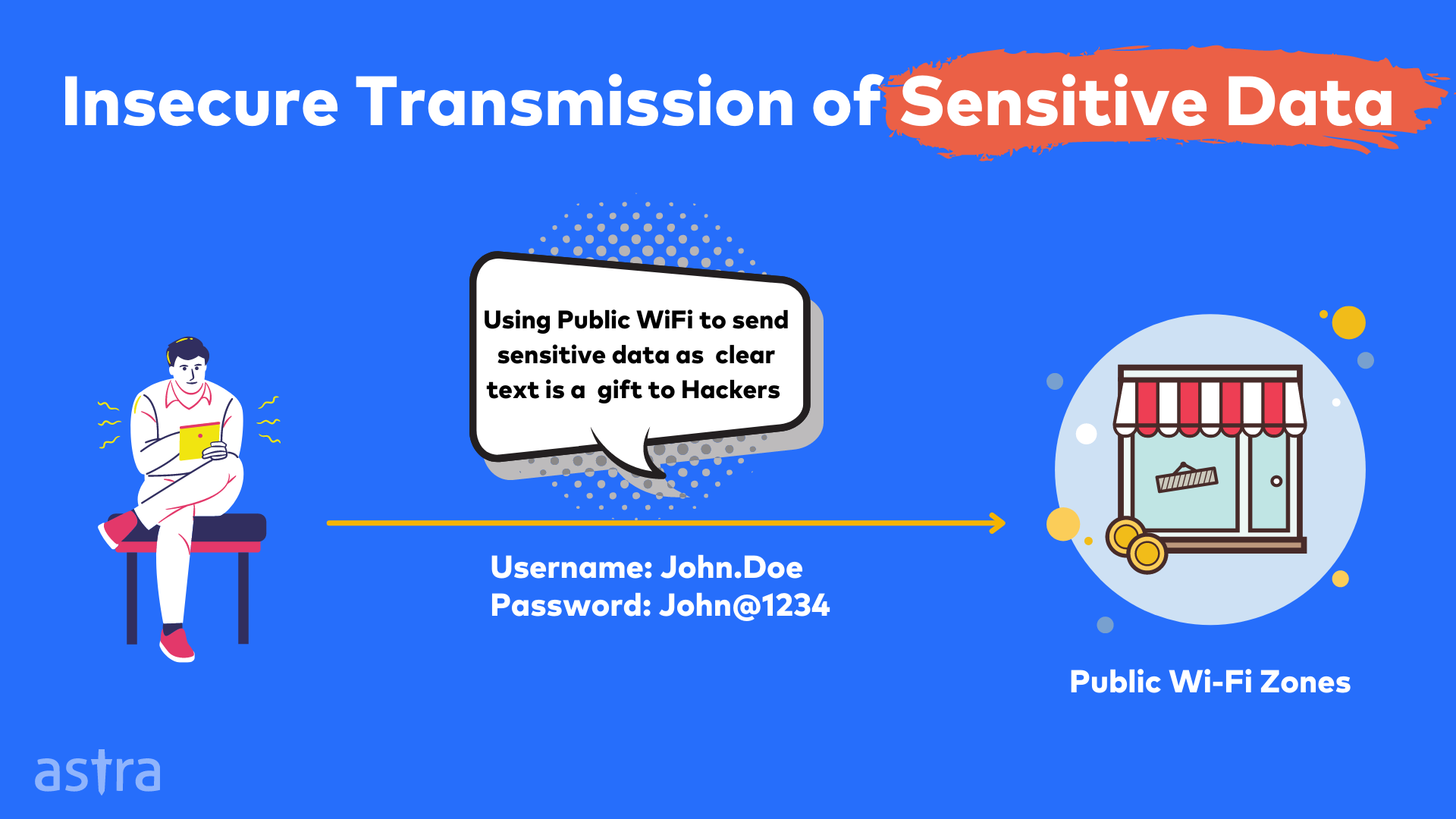
3. Insecure Communication
Insecure communication is a threat that can never be underestimated. When mobile applications are not developed carefully, they can leave their backend systems exposed to hackers. When mobile apps transmit data over the public Internet, mobile carrier networks disclose sensitive data to attack.
Impact
Inadequate communications security exposes data to interception by attackers, leading to eavesdropping, data theft, and man-in-the-middle attacks.
Prevention
Use secure data transmission protocols like HTTPS with strong encryption, and secure socket layer (SSL/TLS). Avoid insecure communication methods like HTTP or change it to HTTPS which offers more security.
4. Insufficient Cryptography
If there is one thing that the world knows about cryptography, it is essential to keep our data safe. Insufficient cryptography can be caused by many reasons, including the lack of knowledge of the developers on a good encryption process or the inability to implement good encryption on the software.
Impact
Improper cryptography results in data breaches and compromised user credentials. Attackers can exploit vulnerabilities in encryption and decryption processes.
Prevention
Use strong encryption algorithms and proper key management. Regularly update the application’s cryptographic libraries to protect it from the latest vulnerabilities.
5. Code Obfuscation
Code obfuscation is the process of transforming the source code of a software application to hinder attempts at reverse engineering or decompilation. Attackers use reverse engineering to understand how an app works to formulate exploits.
Impact
Code obfuscation, often a protective measure, if not implemented correctly can hinder security analysis. This makes it easier for attackers to reverse engineer the application to gain access.
Prevention
Code Obfuscation implementation should be done carefully. Use additional security measures such as application hardening and runtime application self-protection (RASP) to avoid reverse engineering attempts. Constantly update and patch the mobile app without fail.

Difference Between Static and Dynamic Analysis
Static and Dynamic analysis of mobile applications plays an important role in the mobile application penetration testing methodology. Let’s understand the differences between them.
| S No. | Static Analysis | Dynamic Analysis |
|---|---|---|
| 1 | Static Analysis is done without executing the mobile application. | Dynamic Analysis is done when the mobile application runs on the device. |
| 2 | Static Analysis is done on the decompiled source code and the provided files | Dynamic Analysis is done on local filesystem, inter application communication and the communication with server. |
| 3 | Static Analysis includes testing of code quality, debug & error messages and business logic issues. | Dynamic Analysis includes testing of network level communication, forensics and weak cryptography, etc. |
Common Open Source Mobile Application Penetration Testing Tools
- MobSF: Mobile Security Framework is an open-source automated Android pen-testing, malware analysis, and security assessment framework capable of performing static and dynamic analysis.
- Drozer: Drozer is an open-source Android penetration testing tool by F-Secure Labs which allows users to search for security vulnerabilities in apps and devices.
- Clutch: Clutch is an open-source iOS decryption tool. Clutch supports the iPhone, iPod Touch, iPad, and all iOS versions, architecture types, and most binaries.
- Cycript: Cycript is an open-source tool used to explore and modify running applications on either iOS or Mac OS X using a hybrid of Objective-C++ and JavaScript syntax.
- Frida: Frida is a free and open-source dynamic code instrumentation toolkit that works by injecting the QuickJS JavaScript engine into the instrumented process.
- Radare2: radare2 is a popular open-source tool used for disassembling, debugging, patching, and analyzing binaries that are scriptable and support many architectures and file-formats, including Android and iOS apps.
The list of open-source tools is limitless, and it’s impossible to get all of them listed here..
Astra’s Solution to Your Insecure Mobile Apps
It is a well-known fact that mobile application penetration testing is time-consuming and requires a lot of effort and money. Astra’s mobile app penetration testing solutions will help you to save a lot of your time and effort. A solution is a web-based tool that will keep you from all the worries of mobile application penetration testing.
Get your mobile application tested by a team of experts and uncover weaknesses in your mobile application before hackers discover them.
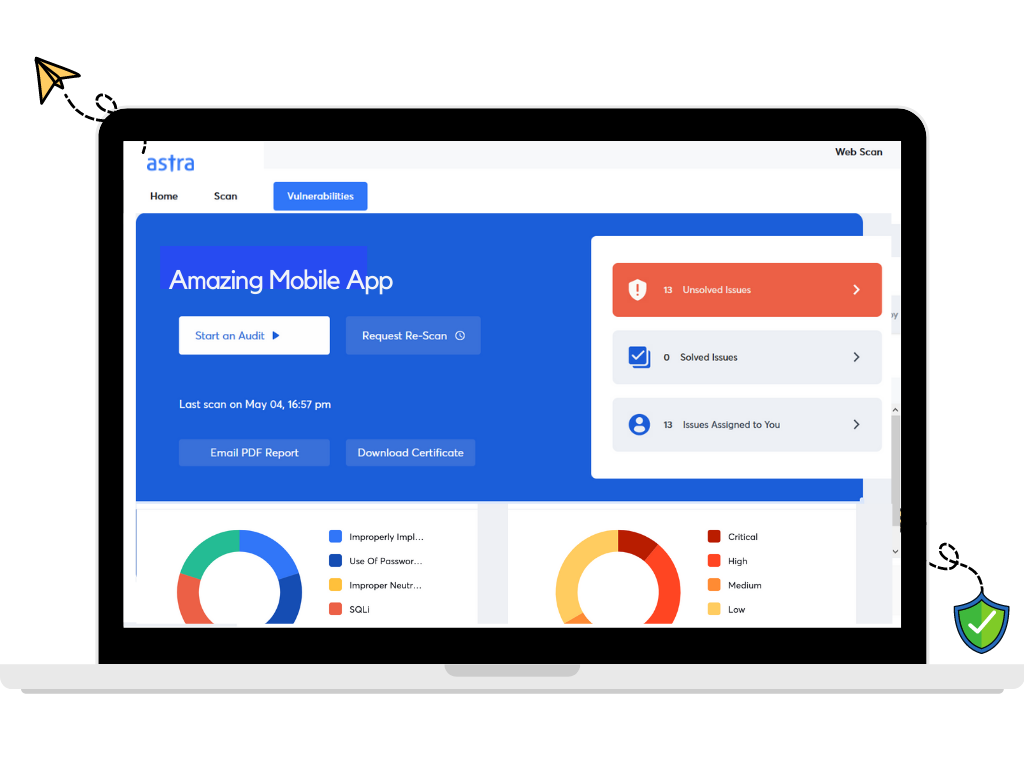
The top features of Astra’s Mobile VAPT solution are:
- Vulnerability Assessment & Penetration Testing (VAPT)
- Static & dynamic code analysis
- Network devises Configuration
- Server Infrastructure Testing & DevOps
- Keep in the loop with an intuitive dashboard
- A common solution for android and iOS applications
Summary
Do you know, 43% of Android mobile apps, 38% of iOS mobile apps are prone to high-risk vulnerabilities. With more than 4.5M applications, it is a necessity to have penetration testing for mobile applications. It is essential to make sure that your application is safe and secure from hackers. Astra’s Mobile App VAPT Solution is a one-stop solution for all your needs. Astra’s experts in the field of mobile application penetration testing help organizations identify vulnerabilities and secure their apps before they get exposed to malicious attacks.
FAQs
1. What is the timeline for mobile application penetration testing?
A mobile application penetration testing takes 7-10 days. The rescans take half as much time. Also, read about Android penetration testing.
2. How much does penetration testing cost?
The cost of mobile penetration testing depends on the scope of the test along with some other factors. Hence, it is difficult to provide a definitive figure. Read about Penetration Testing Cost.
3. Why choose Astra for Pentesting?
The security engineers at Astra perform extensive manual pentest on top of machine learning-driven automated scans. The vulnerability reports appear on your dashboard with detailed remediation guides. You will have access to a team of 2 to 10 security experts to help you with the fixes. Know about Astra’s hacker-style pen-testing.
















