Mobile application security testing often happens too late: after the product roadmap is locked, features are live, and pressure is on to scale. At that point, it’s not just about finding bugs but managing the cost of fixing them under user and investor scrutiny.
What’s rarely said: absolute mobile app security is a product decision, not a technical one. Your trade-offs on SDKs, user flows, and integrations bake in security debt from day one. Pentesting is your only shot to uncover how those trade-offs might fail under a real-world attack. And the earlier you do it, the cheaper and safer it gets.
In this blog post, you’ll explore some of the most common risks threatening modern apps and how to approach end-to-end security testing, from foundational basics to practical steps.
What is Mobile Application Security Testing?
Mobile application security testing refers to analyzing mobile applications for potential flaws through hacker-style testing. This is done before the app is produced to ensure zero errors during implementation on various platforms like iOS, Android, and Windows. One can use or make a mobile application security testing checklist to be well-prepared for iOS or Android application security testing.
The security of mobile applications can be tested at two stages
- One during the initial development phase and throughout development.
- Towards the end stage of development or the application’s final build.
Why is Mobile App Security Testing Important?
Mobile application vulnerability testing is vital for the following reasons:
- Detection of Vulnerabilities: Timely detection of vulnerabilities ensures that the developers don’t release a flawed application susceptible to malicious attacks.
- Elimination of Vulnerabilities: Eliminating the detected vulnerabilities ensures that a well-secured application is released and customer data will remain safe.
- Maintain Compliance: Mobile applications are strictly required to maintain compliance since many such applications deal with payments and customers’ personal information, thus making compliance with various security standards crucial.
- Free of Security Risks: Mobile application security testing successfully secures one’s application against any risks that could result in data breaches, theft, or loss of confidential information.

Why Astra is the best in Mobile Pentesting?
- We’re the only company that combines automated & manual pentest to create a one-of-a-kind PTaaS platform with SOC 2 vulnerability tags.
- Runs 250+ test cases based on OWASP Mobile Top 10 standards.
- Integrates with your CI/CD tools to help you establish DevSecOps.
- A dynamic vulnerability management dashboard to manage, monitor, assign, and update vulnerabilities.
- Astra pentest detects business logic errors and payment gateway hacks.
- Award publicly verifiable pentest certificates which you can share with your users.
- Helps you stay compliant with SOC2, ISO27001, PCI-DSS, HIPAA, etc.
- Trusted by the brands you trust like Agora, Spicejet, Muthoot, Dream11, etc.

Types Of Mobile Apps
- Web apps: Normal web applications built in HTML and accessed from your mobile.
- Native apps: Specifically built for a particular OS and use OS-specific features.
- Hybrid apps: Similar to native apps but behave like web apps, leveraging the benefits of both types.
Criteria For Mobile Application Security Testing
1. Analyzing Threats
The first step is to produce and analyze any potential threat. This is done by checking the parameters as mentioned below:
- While downloading an app, if it stores any logs within the app store, including credentials or account information, there might be a chance of a data leak.
- If apps store user credentials, the developers need to analyze any potential threat to the user data.
- Users need to scrutinize the data shown on an app, as attackers can exploit this data by hijacking sessions or snooping.
- Apps can quickly send and receive data thanks to high-speed internet connectivity. Attackers can capture this data; to avoid this, all transmitted data can be encrypted.
- Interconnection with other apps or third-party services needs to be secured. Any vulnerability in the structure can endanger all services of the app.
2. Analyzing Mobile Application vulnerabilities
During vulnerability analysis, you need to check the app for any security gaps, the responsiveness of the security defenses, and whether they can counter any attack in real time. Before jumping into this stage, ensure that there is a list of vulnerabilities to check and a format to capture all findings.
A complete vulnerability analysis consists of checking components at a broader level, including the network, the operating system of the phone, and the hardware.
How to Perform Mobile Application Security Testing?
1. Define the Goal
Security audits are vast and multi-purpose. Hence, before you begin the process, know your number one reason for doing the audit. What is it that you hope to find or correct? Will there be actions at the end of the process?
Once all this is answered, list the priority security areas you must assess first. Then, as you go on and cover these areas, you can always add new ones. The goal of mobile application security testing methodology can be any of the following things:
- To check if there’s a security mechanism in place
- To confirm that a management control framework exists
- To check if the right configurations are set
- To check if the application has been tested in each stage and with different test cases
- To check all communication between a user and the application, and between the application and the server, is encrypted
- To detect and manage all threats and risks to the app
- To check that the proper authentication process is implemented
- To check that the session and cookies are properly handled
- To confirm that security requirements are met in contract management
- To check whether the secure data storage process is implemented
High-priority security areas in a mobile app include:
- App permissions
- Configurations
- Authentication and Authorization
- Session and cookies
- Data storage
2. Threat Analysis and Modelling
Next on the list of mobile application security testing steps, threat analysis is the process of identifying potential threats in a system. Threat analysis & modeling have four components:
- App architecture
- App resources
- Third-party interaction
- Threat agents
While evaluating your mobile app for vulnerabilities, being pessimistic is the key. Think of all the components and functionalities that could allow a hacker in. Since you already have a list of high-priority areas, start with them first.
List down all potential security risks in them. For an even precise result, develop test cases (usually a permutation of different app functions, operating systems, versions, user roles, permissions, and so on) and analyze your app for those.
To quicken the process of threat analysis and modeling for your mobile app, you can use these automated tools:
- Android Debug Bridge: Android Debug Bridge (ADB) is a command-line tool used to assess and debug mobile apps. ADB is a client-server program consisting of Client, Daemon, and Server. ADB is a great security testing tool; however, it is limited to the Android OS, which brings us to the next tool. ADB is available in the Android SDK Platform-Tools package. However, you can download ADB with the SDK Manager or directly from here.
- Mobile Security Framework (MobSF): Mobile Security Framework (MobSF) is an automated security testing framework for Android, iOS, and Windows platforms. It performs static and dynamic analysis for mobile app security testing. Follow this guide to install MobSF.
- iMAS: iMAS (iOS Mobile Application Security) is an iOS security testing framework that identifies vulnerabilities in iOS mobile applications. iMAS works great in detecting vulnerabilities related to security controls, CWE, system Passcode, jailbreak, debugger/run-time, flash storage, and keychain.
3. Exploitation
Threat analysis is half the work done. By now, you know what the possible vulnerabilities are threatening your app and the test case in which it is occurring. Now, all you need to do is estimate the scope of these vulnerabilities. By scope, I mean the penetration of these vulnerabilities that cause damage to your app. In other words, the severity of the vulnerabilities.
The tools you can use for this are:
- QARK (Quick Android Review Kit): Developed by LinkedIn, QARK is an automated Android pen-testing tool. You can scan all your mobile app’s components to detect misconfigurations and threats. QARK also highlights issues in your Android version.
To install QARK, use the following command:
~ git clone https://github.com/linkedin/qark
~ cd qark
~ pip install -r requirements.txt
~ pip install . --user # --user is only needed if not using a virtualenv
Follow this detailed guide on how to use QARK for Mobile application security testing.
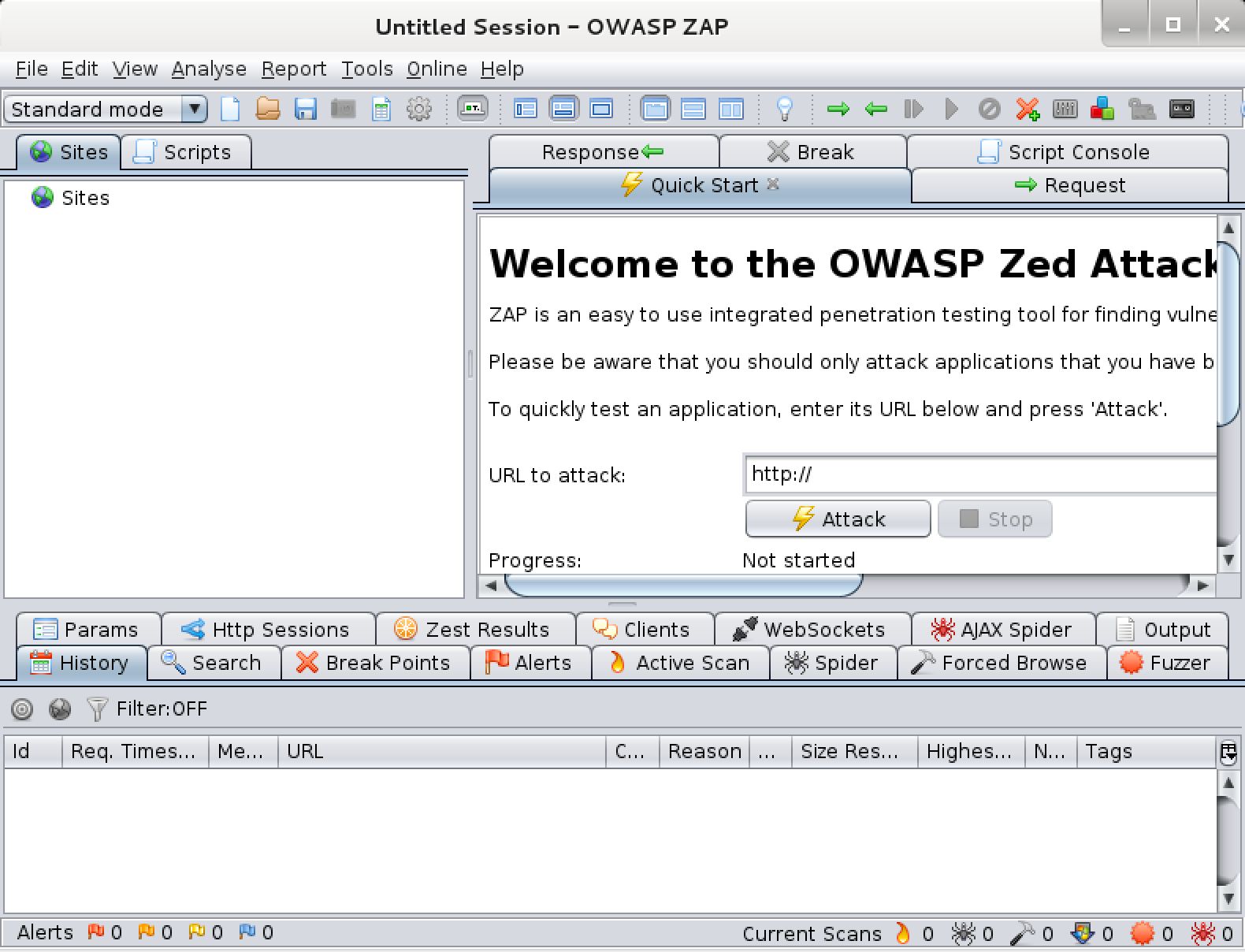
- Zed Attack Proxy (ZAP): ZAP is a free security testing tool used by thousands of pen-testers around the globe. ZAP is developed by OWASP and is one of the most preferred tools for manual security testing.
To download ZAP for Linux OS, use this link.
- Mitmproxy: Mitmproxy is a free and open-source tool to identify MITM (Man-in-the-Middle) vulnerabilities in a mobile app. It is an HTTP proxy that can be used to intercept, inspect, modify, and replay web traffic such as HTTP/1, HTTP/2, WebSockets, or any other SSL/TLS-protected protocols in a mobile app. It is a great way to exploit client-server communications of your mobile app and identify the underlying vulnerabilities.
4. Remediation
So far, you have set a definitive goal for the audit, analyzed your app and its supporting infrastructure for vulnerabilities, and exploited vulnerabilities to determine their criticalness. By the end of the previous step, you should have a list of vulnerabilities segregated according to severity.
In this step, you fix the vulnerabilities, focusing on the critical ones.
How can Astra Help?
Astra simplifies mobile app security testing by combining automated scans (SAST + DAST) with expert-led manual pentesting. With over 250 test cases mapped to OWASP Mobile Top 10 and custom business logic testing, we uncover technical and contextual vulnerabilities that scanners miss.
You can easily upload your Android or iOS app, and our security engineers handle the rest, delivering clear, actionable insights. The CXO-friendly dashboard offers AI-generated test cases, contextual support, and seamless integration with real-time collaboration tools like Slack, Jira, and GitHub.
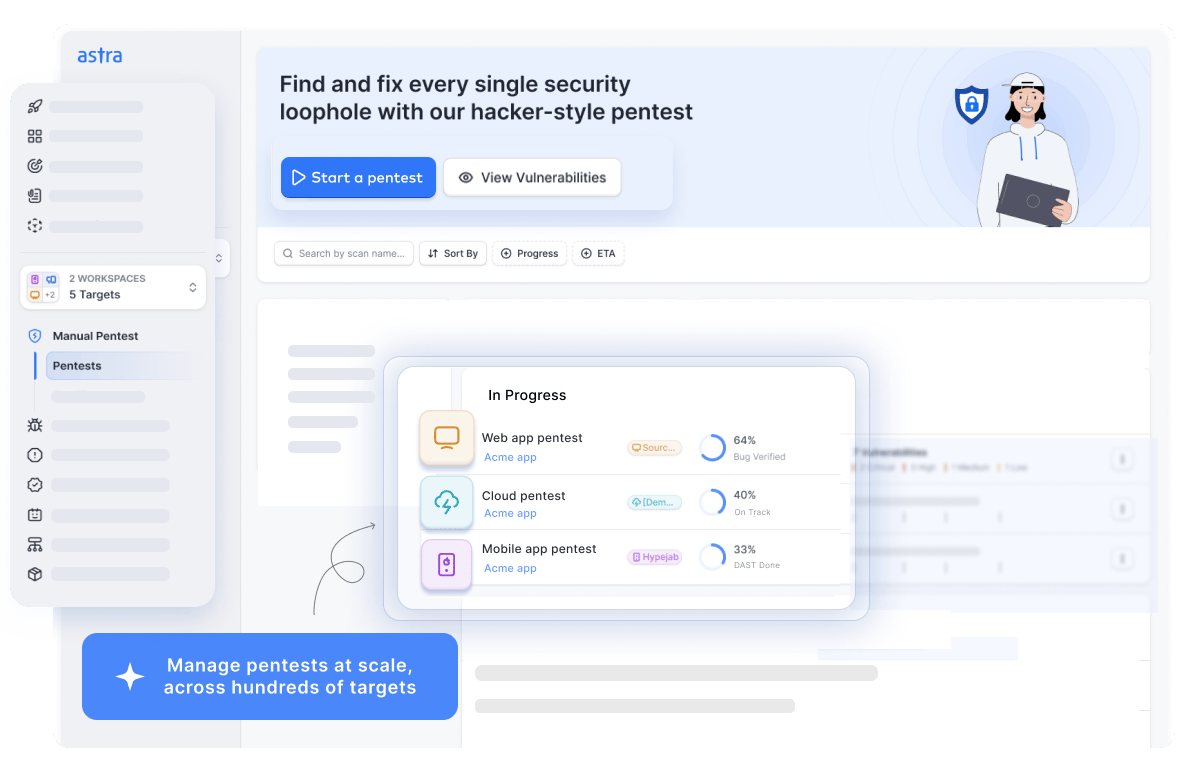
Get publicly verifiable security certificates after two free rescans, customizable reports for tech and non-tech teams, and access to certified security experts. Astra transforms the mobile app VAPT process from a compliance hurdle into a scalable, secure, and stakeholder-ready process.
Key Features
- Tests authenticated user flows with scan-behind-login.
- Secures mobile APIs and backend integrations.
- Detects hardcoded secrets, API keys, and tokens.
- Validates role-based access and session management.
- Assesses resistance to reverse engineering and data leaks.
- Security professionals with various certifications & CVEs
Security Tips for Safe Mobile App Development
Lastly, after you have tested your solution for security risks, it is time you protect it too. Besides patching and updating your mobile application regularly, you can also undertake other security practices. To learn more, follow this exhaustive guide on 10 security tips for your mobile app development.
Understanding Challenges in Mobile Application Security Testing
Although it wouldn’t be entirely accurate to say that app developers are shoddy about security, it can’t be ruled out either. The fact that so many apps are getting hacked increasingly has something to do with the poor security infrastructure of these apps.
Now, the apps on Android are a bit differently developed and distributed than their iOS counterparts. This means the security issues on both these platforms differ, too.
Mobile App Security Issues in Android:
Recent mobile app hacking stats show that Android apps are more badly hit than iOS. One primary reason behind this is Android’s open-source environment, meaning anyone can use or change Android’s source code for app development. The immediate drivers behind this are:
- Android’s open-source environment allows anyone to use or change the Android source code for app development.
- The lack of a strict screening process by the Android OS for apps leads to an increased number of vulnerable mobile applications.
Such issues can be easily detected using mobile application security testing techniques and tools. Major security issues in an Android app include:
- MitM (Man-in-the-Middle Attacks)
- Cryptojacking
- Malvertising
- Phishing and Social Engineering
- Component-related threats
- Permissions-based issues
- Rooting
Mobile App Security Issues in iOS:
iOS apps are less vulnerable than Android apps because of their closed development environment. Also, Apple follows a meticulous screening process for its apps. That said, iOS apps are not free from security risks entirely.
Market share analysis tells us that the affluent divide uses the iOS operating system more frequently, making it a hot target for hackers. Despite the security measures, there have been instances where iOS apps, devices, and other data were hacked. Major security issues found in an iOS app include:
- Storing data locally on the device
- Jailbreaking
- Phishing and Social Engineering
- Allowing 301 Redirects
- Stolen certificates to host apps
Besides security risks emanating from the basic structure and build of the two operating systems, there are other common mobile app security issues faced by Mobile apps regardless.
It is one small security loophole v/s your Android & iOS app.
Get your mobile app audited & strengthen your defenses!
Top 10 Mobile App Security Issues By OWASP
According to a list issued by OWASP in 2016, the top 10 mobile app security issues are:
- Improper Platform Usage
- Insecure Data Storage
- Insecure Communication
- Insecure Authentication
- Insufficient Cryptography
- Insecure Authorization
- Client Code Quality
- Code Tampering
- Reverse Engineering
- Extraneous Functionality
Development Fall-Outs In Mobile Application Protection
Several other mobile application protection issues in Android and iOS stem from poor development practices and maintenance. Here’s what developers have been doing wrong while building an app:
- Not securing components of their apps
- Ignoring insecure interprocess communication
- Not thinking about secure data storage
- Not using universal links
- Overlooking configuration flaws (Configuration flaws include disclosure of sensitive information in error messages, fingerprinting in HTTP headers, and TRACE availability.)
- Not testing their code in every development stage and at runtime
- Not planning for caching & logging Vulnerabilities
- Not patching your code fast enough
Final Thoughts
Treating mobile application security testing as a last-mile task is no longer viable. By the time you’re scaling or demoing to investors, fixing a bug isn’t just technical debt, it’s reputational damage. Security must move upstream and become part of how you make product decisions.
Vulnerability scans are helpful, but real resilience comes from rigorous, context-aware pentests done early and often. Because in mobile security, what you don’t test will break you, and what you test late will cost you.
Additional Resources on Security Testing
This post is part of a series on Security Testing. You can
also check out other articles below.

- Chapter 1: What is Security Testing and Why is it Important?
- Chapter 2: Security Testing Methodologies
- Chapter 3: What is Web Application Security Testing?
- Chapter 4: How to Perform Mobile Application Security Testing
- Chapter 5: What is Cloud Security Testing?
- Chapter 6: What is API Security Testing?
- Chapter 7: What is Network Security Testing?
- Chapter 8: A Complete Guide to OWASP Security Testing?
- Chapter 9: What is DAST?
- Chapter 10: What is SAST?









