In the year 2021, 74% of Indian SMBs faced some kind of security incident, 85% of them lost customers because of cyberattacks. 92% of these companies were affected by Malware whereas the websites of 76% victims were used for Phishing. The primary goal of these attacks is to steal data – personal information of customers, credit card information, important credentials, intellectual property. Both the company as well as the clients and customers it serves are at risk in a hack situation.
Surprisingly, a majority of these hacks take place by exploiting known vulnerabilities – by an absence of adequate security measures, and error in judgment. In fact 90% of hacks around the world can be attributed to similar reasons. Hence, every industry that involves sensitive data has certain security regulations, and many of them require Penetration Testing Compliance.
What is Penetration Testing?
Penetration Testing refers to the process of simulating a hack-like situation to expose and exploit vulnerabilities and security loopholes existing in a website, web application, or network. This is an offensive security measure where you employ security engineers to try and break into your system in order to spot and fix the vulnerabilities.
What is Penetration Testing Compliance?
When your systems are Pen tested, the security experts prepare a Pentest report. This report documents the vulnerabilities as well as the remediation steps. Once you have fixed the vulnerabilities, a rescan takes place to verify that all the loopholes are taken care of and your system is protected. This sort of testing and certification is mandated by various industries in order to achieve certain local and global security compliance for their business.
The prescribed scope of the pen test, its frequency, all vary according to the security regulations under consideration. We will learn all about that in the course of this guide.
Who Needs Penetration Testing Compliance?
There are certain industries, especially those dealing with sensitive customer data, that require Vulnerability Assessment and Penetration Testing as a rule. We will talk about a few of the various security regulations of which Penetration Testing Compliance is a part. Those are
- HIPAA for healthcare institutions
- PCI-DSS for companies that process payment
- RBI-ISMS for banks and non-banking financial institutes
- SOC 2 for service organizations
- ISO 27001 for any organization willing to formalize business around information security.
Also Read: Continuous Penetration Testing: The Best Tool You’ll Find in 2022 | API Penetration Testing: What You Need To Know
HIPAA: Health Insurance Portability and Accountability Act
HIPAA is a federal law from 1996 that focused on creating national standards for protecting patients’ data from being shared without their consent.
Does HIPAA require Vulnerability Assessment and Penetration Testing? No, not on paper. However it requires the complying entities to run risk analysis which effectively translates to testing the security controls. VAPT is one of the most surefire ways of testing security control. So, you can say that Penetration Testing is necessary to gather adequate evidence to comply with HIPAA.
Healthcare institutions are favorite targets for hackers because of the unpreparedness of the staff for a cyber attack, lack of awareness, legacy systems and low security budget, and high value for patient data in black market. Healthcare facilities are often subject to ransomware attacks where the hackers make important patient data inaccessible until the ransom is paid.
While health care facilities are not essentially technology firms, they handle more data than one can imagine. Mandated by HIPAA or not, Penetration Testing is highly recommended for these organizations.
Also Read: Top 6 Web Pentest Tools You Should Not Miss in 2022 | Top 7 Cyber Security Auditors for SaaS Companies
PCI-DSS: Payment Card Industry Data Security Standard
The name is quite self-explanatory. This compliance scheme was formed in 2004 to secure credit and debit card transactions from data theft and fraud. It is governed by the Payment Card Industry – Security Standard Council (PCI-SSC)
The PCI SSC does not have the legal authority to compel compliance, but it is pretty much written in stone that every company processing credit card and debit card transactions should achieve the PCI DSS compliance. Not only does it help a company protect its data but it also helps in securing a trusting relationship with the customers.
Does the PCI DSS require Penetration Testing Compliance? Yes and No. We will explain how.
The PCI DSS compliance scheme is divided into 4 levels depending on the number of real-world credit and debit card transactions handled by a certain organization. Level 1 is for companies that handle more than six million transactions while level 4 is for companies that handle less than 20 thousand transactions.
A PCI scan is required in all the levels whereas the level 1 companies must undergo internal audits and a scan by an Approved Scan Vendor.
Now, the PCI certification requires you to use a firewall, encrypt transcription, and install antivirus. But it also requires you to qualify in the audits and the scans. You must take recourse to Penetration Testing to ensure zero security loopholes, while the rule one paper does not mandate it directly.
Read also: What is PCI Data Security Standard | Why Firewall Penetration Testing is Essential to Your Security Strategy
RBI-ISMS: Reserve Bank of India – Information Security Management System
It is very difficult to imagine the Indian banking industry as a single unified entity – it has fully networked and computerized private banks and foreign banks at one end of the spectrum and rural public sector banks (PSB) with little scanty computerization on the other end of the spectrum. Nevertheless, RBI has put together comprehensive and exhaustive checklists for banks and NBFCs from all parts of the spectrum.
The Information Security Audits are so fashioned as to test even the smallest assets for security loopholes. It would make a lot of sense for financial institutes to undergo Penetration Testing to ensure compliance with RBI-ISMS.
Related Read: Banking Application Testing
SOC 2: Service Organization Control 2
The SOC 2 was created under American Institute of Certified Public Accountants (AICPA) to regulate five organizational control issues – security, availability, processing integrity, confidentiality, and privacy.
The SOC 2 compliance scheme is designed for technology companies that store customer data in the cloud. It applies to nearly all SaaS companies.
Complying with SOC 2 involves monitoring of network assets, regular audits, setting up anomaly alerts, and actionable forensics.
Penetration Testing Compliance is an indispensable part of the SOC 2 compliance scheme as it deeply focuses on vulnerability assessment and actionable forensics.
Read also: A Comprehensive Guide to SOC2 Penetration Testing
ISO 27001: International Organization for Standards 27001
The ISO 27001 compliance scheme is designed to standardize adequate and controlled measures to ensure information security.
It encompasses all legal, technical, and physical aspects of an organization’s information security management process. It is placed to monitor, maintain, and improve information security management systems.
The ISO 27001 is an umbrella that covers areas ranging from human resources security to business continuity management.
Annual Penetration Testing is a requirement for complying with ISO 27001 as it allows organizations to test their security posture against an ever evolving threat landscape.
The benefits of Penetration Testing Compliance
Whether you are running a SaaS platform or in charge of information security at a healthcare institute, you can never escape the threat of cyberattacks. The best recourse is to try and find out vulnerabilities before hackers do.
- You are able to optimize your security posture for the latest vulnerabilities.
- Get rid of misconfigurations, and vulnerable network components.
- Get ready for any security audit.
- Build trust among customers.
How can Astra Security Help You with Compliance?
Astra Security has a bunch of Penetration testing compliance programs that are globally acknowledged. For instance, the Astra Certified VAPT, Astra Safe To Host Certificate.
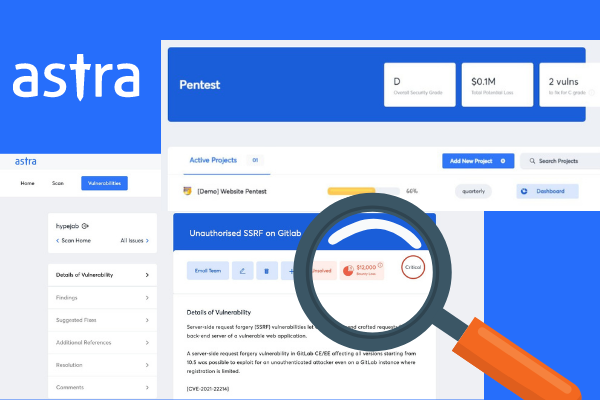
Astra Pentest is empanelled by CERT-In for providing information security auditing services. The solution can also help you certify for ISO 27001. Astra handles VAPT and manages end-to-end compliance with SOC2, PCI DSS, and HIPAA with the help of vetted auditors. It is safe to say that Astra Security leaves very little for you to worry about when it comes to Penetration Testing Compliance.
Conclusion
With the ever-evolving cyber threat landscape and the increasing fear around security breaches, Penetration Testing is what binds you to the reality of your organization’s security posture. That is why Penetration Testing Compliance is so important for so many security regulations.
And Successful vulnerability remediation goes beyond just ensuring compliance – it builds trust inside your organization and among your clients.
FAQs
1. What is compliance based penetration testing?
A number of security compliance regulations require pentesting. So, pentesting constitutes one essential part of the entire compliance process. Astra’s pentest compliance feature lets you view the compliance status on your dashboard after a scan is run.
This post is part of a series on penetration testing, you can also check out other articles below.
Chapter 1. What is Penetration Testing
Chapter 2. Different Types of Penetration Testing?
Chapter 3. Top 5 Penetration Testing Methodology to Follow in 2024
Chapter 4. Ten Best Penetration Testing Companies and Providers
Chapter 5. Best Penetration Testing Tools Pros Use – Top List
Chapter 6. A Super Easy Guide on Penetration Testing Compliance
Chapter 7. Average Penetration Testing Cost in 2024
Chapter 8. Penetration Testing Services – Top Rated
Chapter 9. Penetration Testing Report
















