As businesses rely more on technology, they face greater cyber threats. From Discord’s 4-billion-record breach to Zenlayer’s 384-million-account hack, the cost of attacks is high. As such, our security experts have hand-picked the top 41 leading cyber security companies and pentest platforms to help you protect your business and get started in the right direction!
Top Cybersecurity Companies to Know
- Microsoft Security
- Cisco
- Palo Alto Networks
- CrowdStrike
- Astra Security
- Fortinet
- Zscaler
- Check Point
- SentinelOne
- Tenable (Nessus)
Best 41 Cybersecurity Companies Worldwide
| Features | Category | No. of Employees | Headquarters | Market Cap |
|---|---|---|---|---|
| Microsoft Security | Cybersecurity testing, SIEM, threat identification, and access management | 10,001+ | Washington, USA | $3.182 Trillion |
| Cisco | Holistic cybersecurity protection suite for various assets from cloud to networks | 10,001+ | California, USA | $222.44B |
| Palo Alto Networks | AI-driven data protection with threat intel and incident response | 10,001+ | California, USA | $119.31 B |
| CrowdStrike | Endpoint Security, Threat Intelligence & Extended Detection and Response (XDR) | 7,500+ | Texas, USA | $73.36 Billion |
| Astra Security | PTaaS Platform | 11 - 50 | Delaware, USA | <$5 Million |
| Fortinet | Secure Networking & Security Operations, Endpoint, Intrusion Detection | 13,500+ | California, USA | $61.47 Billion |
| Zscaler | Cloud security platform with VPN, ZTA, and cyber threat protection | 5,001-10,000 | California, USA | $28.20 Billion |
| Check Point | Complete Cybersecurity (Network Security, Endpoint Security, Cloud Security) | 6,000+ | Tel Aviv, Israel | $22.78 Billion |
| SentinelOne | Next-Generation Endpoint Protection Platform (NG-EPP), Machine Learning for Threat Prevention | 2,400+ | California, USA | $8.01 Billion |
| Tenable (Nessus) | Vulnerability Management | 1,900+ | Maryland, USA | $4.95 Billion |
1. Microsoft Security
As one of the most well-established cyber security companies, Microsoft effectively leverages endpoint protection, threat detection, and advanced security analytics to ensure the safety of your infrastructure.
Its tools, like Defender for Endpoint and Sentinel, shield against threats, while Purview and Information Protection keep data compliant and secure, empowering businesses to navigate the ever-changing cybersecurity landscape confidently.
- Founded year: 1975
- Best For: Cybersecurity testing, SIEM, threat identification, and access management
- Number of Employees: 10,001+
- Headquarters: Washington, USA
- Customers and Accolades: Heineken, EY, ING
- Market Cap: $3.182 Trillion
Pros:
- Automates labeling and retention policies.
- Delivers advanced threat detection using AI-driven algorithms.
2. Cisco
As one of the best cyber security companies, Cisco offers an exhaustive suite of solutions, including the SASE platform, which secures access for users and devices anywhere. Its XDR solution leverages AI to proactively find and combat threats across your network, endpoints, cloud, and applications.
It also helps protect data and applications in multi-cloud environments with endpoint security to safeguard devices, network security solutions for perimeter defense, and Identity and Access Management (IAM) to ensure only authorized users access sensitive data.
- Founded year: 1984
- Best For: Holistic cybersecurity protection suite for various assets from cloud to networks
- Number of Employees: 10,001+
- Headquarters: California, USA
- Customers and Accolades: Marriott, NFL
- Market Cap: $222.44B
Pros:
- Offers detailed remediation guidance.
- Allows segmentation of security issues by either device type or vulnerability.
3. Palo Alto Networks
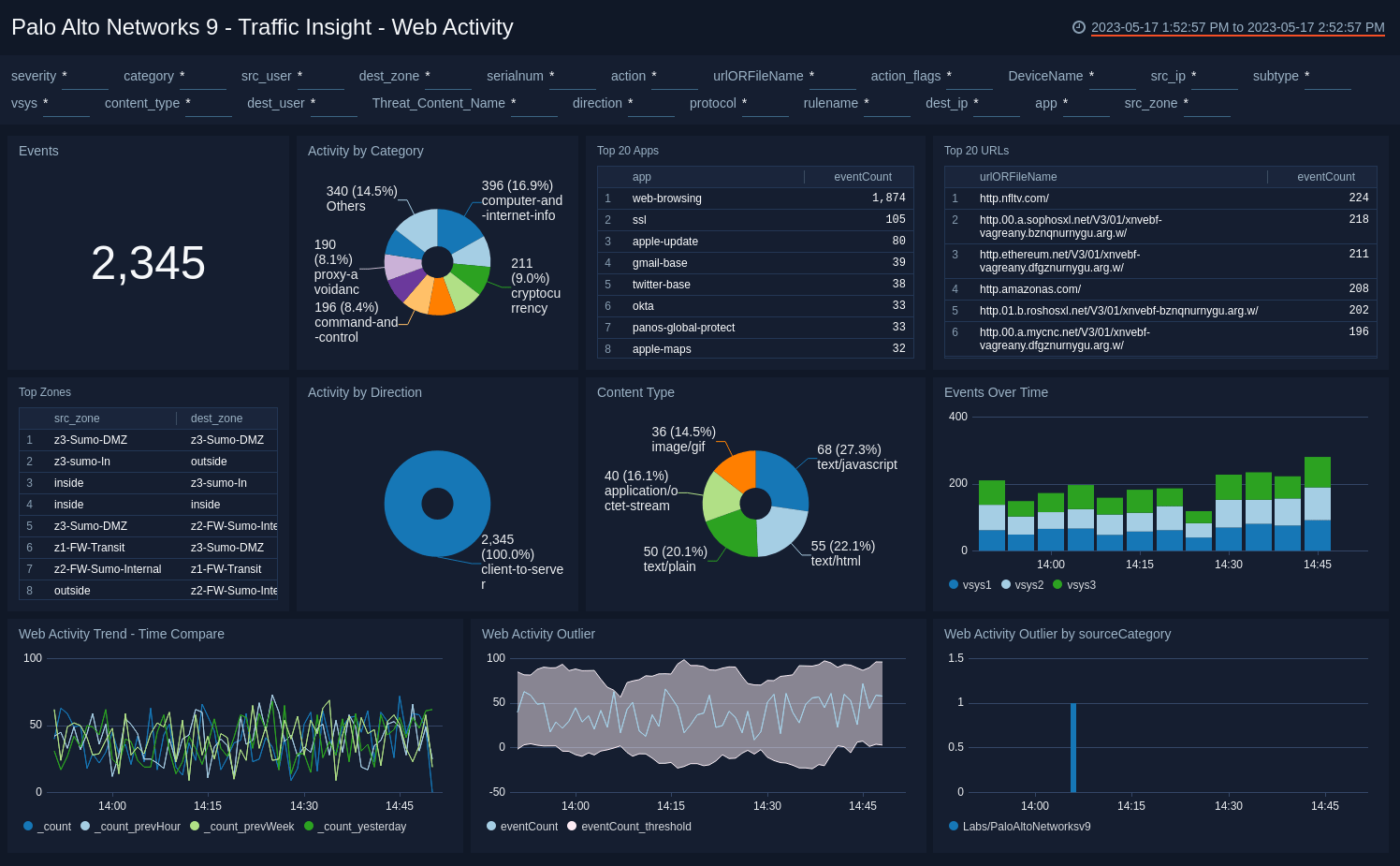
Powered by AI and automation, Palo Alto Networks unifies your cybersecurity. Its next-generation firewalls shield your network, while Prisma Cloud protects cloud applications, and Cortex XDR uses AI to find and fight threats across everything from your network to the cloud.
The Cortex XSOAR automates tasks and integrates security tools, streamlining your operations while its threat intel unit, Unit 42, keeps you ahead of attackers with actionable insights.
- Founded year: 2001
- Best For: AI-driven data protection with threat intel and incident response
- Number of Employees: 10,001+
- Headquarters: California, USA
- Customers and Accolades: ADT, Salesforce, Accenture
- Market Cap: $119.31 B
Pros:
- Offers a reliable VPN with relatively low downtime.
- Supports MFA via third-party apps such as Okta.
4. CrowdStrike
CrowdStrike specializes in extended detection and response (XDR), threat hunting, and endpoint security. Their Falcon platform uses a cloud-native architecture to deliver endpoint protection and threat detection.
They also feature a GenAI platform called Charlotte AI, enabling smarter and faster AI workflows. CrowdStrike’s cloud-based approach allows for rapid deployment and scalability, making it a popular choice for large enterprises.
- Founded Year: 2011
- Best For: Endpoint Security, Threat Intelligence & Extended Detection and Response (XDR)
- Number of Employees: 7,500+
- Headquarters: Texas, USA
- Customers and Accolades: Fortune 100 companies and government agencies, 2024 Cyber Security Awards – Data Leakage Prevention
- Market Cap: $73.36 Billion
Pros
- The Falcon platform utilizes advanced technologies such as machine learning and behavioral analysis to detect and prevent sophisticated cyberattacks.
- XDR capabilities enable businesses to quickly identify and respond to security incidents, minimizing the potential damage.
No other pentest product combines automated scanning + expert guidance like we do.
Discuss your security
needs & get started today!

5. Fortinet
Fortinet’s core concept is providing a complete security fabric that secures the entire IT infrastructure, including network, endpoint, cloud, and operational technology (OT).
Fortinet offers a wide range of security products, including firewalls, network access control appliances, intrusion prevention systems (IPS), endpoint protection, and secure access service edge (SASE) solutions. Their primary focus is secure networking and fortifying the entire security operating system.
- Founded Year: 2000
- Best For: Secure Networking & Security Operations, Endpoint, Intrusion Detection
- Number of Employees: 13,500+
- Headquarters: California, USA
- Customers and Accolades: Toyota Material Handling, IHG Hotels, Carrefour
- Market Cap: $61.47 Billion
Pros
- Uses GenAI and AI-powered threat intelligence to enable automation that is free from error.
- It provides various products, including firewalls, SASE, endpoint protection, NOC management, and automated security operations.
6. Zscaler
Zscaler secures organizations with a cloud-native security platform that integrates SASE, ransomware protection, data loss prevention, and cloud security services.
Leveraging AI and a massive global security cloud to defend against evolving cyber threats proactively, it offers features like zero-trust access, browser isolation, and advanced threat intelligence to combat existing threats and emerging zero days proactively.
- Founded year: 2008
- Best For: Cloud security platform with VPN, ZTA, and cyber threat protection
- Number of Employees: 5,001-10,000
- Headquarters: California, USA
- Customers and Accolades: USMC, Eramet, Dairy Crest
- Market Cap: $28.20 Billion
Pros:
- Seamless internet access management.
- Quick turnaround on customer support.
7. Check Point
Check Point Software Technologies is a leading provider of cybersecurity solutions, offering a vast suite of products for network security, endpoint security, and cloud security. Its flagship product, Check Point Firewall, is a market leader in network security.
Check Point provides AI-powered solutions delivered via the cloud to protect your workspace end-to-end.
- Founded Year: 1993
- Best For: Complete Cybersecurity (Network Security, Endpoint Security, Cloud Security)
- Number of Employees: 6,000+
- Headquarters: Tel Aviv, Israel
- Customers and Accolades: Hallmark, Clarks, Alkem, StrongPoint, Leader in Gartner Magic Quadrant for Network Firewalls
- Market Cap: $22.78 Billion
Pros
- AI-powered threat intelligence is used across channels, such as the network, cloud, and applications.
- Offers advanced threat prevention capabilities with unique features like its SandBlast technology, which utilizes threat emulation and sandboxing to stop zero-day attacks, malware, etc.
8. SentinelOne
SentinelOne provides holistic security solutions for enterprise-wide protection. Their Singularity platform leverages artificial intelligence and machine learning to detect, prevent, respond to, and remediate cyber threats in real time.
This complete security solution protects endpoint, cloud, and identity. The platform ingests and analyzes data from all sources, such as email, SASE, web, sandbox, firewall, log, etc.
- Founded Year: 2013
- Best For: Next-Generation Endpoint Protection Platform (NG-EPP), Machine Learning for Threat Prevention
- Number of Employees: 2,400+
- Headquarters: California, USA
- Customers and Accolades: Samsung, EA, Hitachi, Pandora
- Market Cap: $8.01 Billion
Pros
- The Singularity platform offers advanced capabilities beyond traditional antivirus software, including detecting and preventing zero-day attacks and ransomware.
- It uses machine learning to improve its ability to detect and respond to threats continuously.
9. Tenable (Nessus)
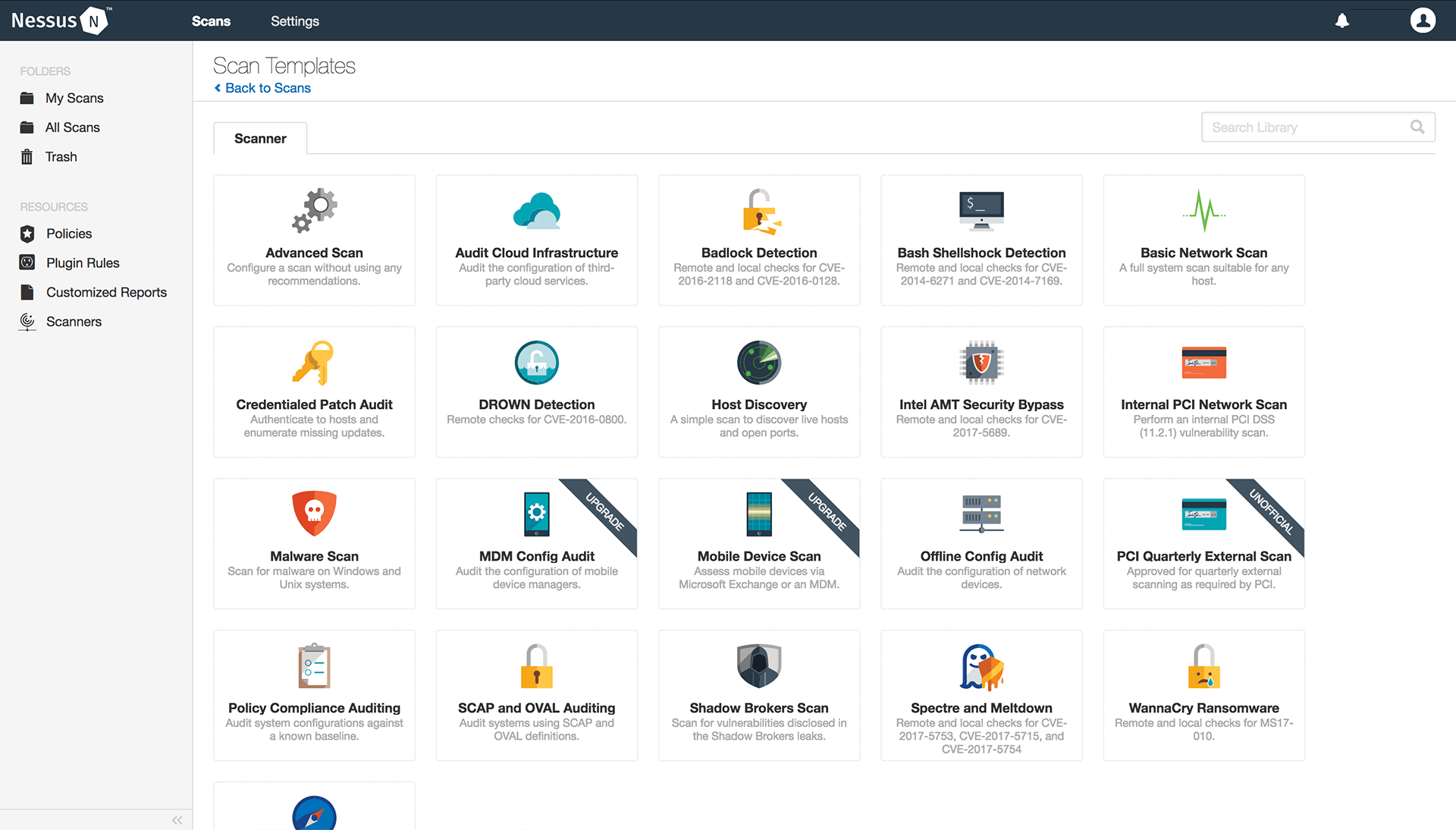
As one of the intelligent cyber security companies, Tenable provides vulnerability management services. Its flagship product, Nessus, is a web application vulnerability scanner organizations use to identify and remediate security weaknesses in their IT infrastructure.
It helps with point-in-time analysis of security systems to find vulnerabilities and focuses on automated scanning to understand cloud infrastructure better. As one of the top cyber security companies, it offers configurable reports, round-the-clock support, and unlimited vulnerability assessments.
- Founded Year: 2002
- Best For: Vulnerability Management
- Number of Employees: 1,900+
- Headquarters: Maryland, USA
- Customers and Accolades: 65% of Fortune 500 companies, Siemens, G2 Top 50 Security Products
- Market Cap: $4.95 Billion
Pros
- Uses six-sigma accuracy to provide the lowest false-positive rate in the industry.
- It provides continuous vulnerability assessment, updating businesses on their security posture.
10. McAfee
With multiple accolades and certifications, including SELabs AAA Certification, McAfee, as a cyber security company, safeguards PCs, Macs, Android, and iOS devices from viruses, malware, and other cyber threats.
It goes beyond antivirus protection, offering identity monitoring and a robust firewall under its Business Protection plans to secure your home and office networks against unauthorized access.
- Founded year: 1987
- Best For: Antivirus, mobile security, and identity monitoring solutions
- Number of Employees: 1,001-5,000
- Headquarters: California, USA
- Customers and Accolades: Best Protection and Best Advanced Protection awards by AV-Test
- Market Cap: $4.89 Billion
Pros:
- Easy to use Antivirus for personal and business use.
- Offers a web advisor plugin for Chrome.
Best Penetration Testing Companies
11. Astra Security
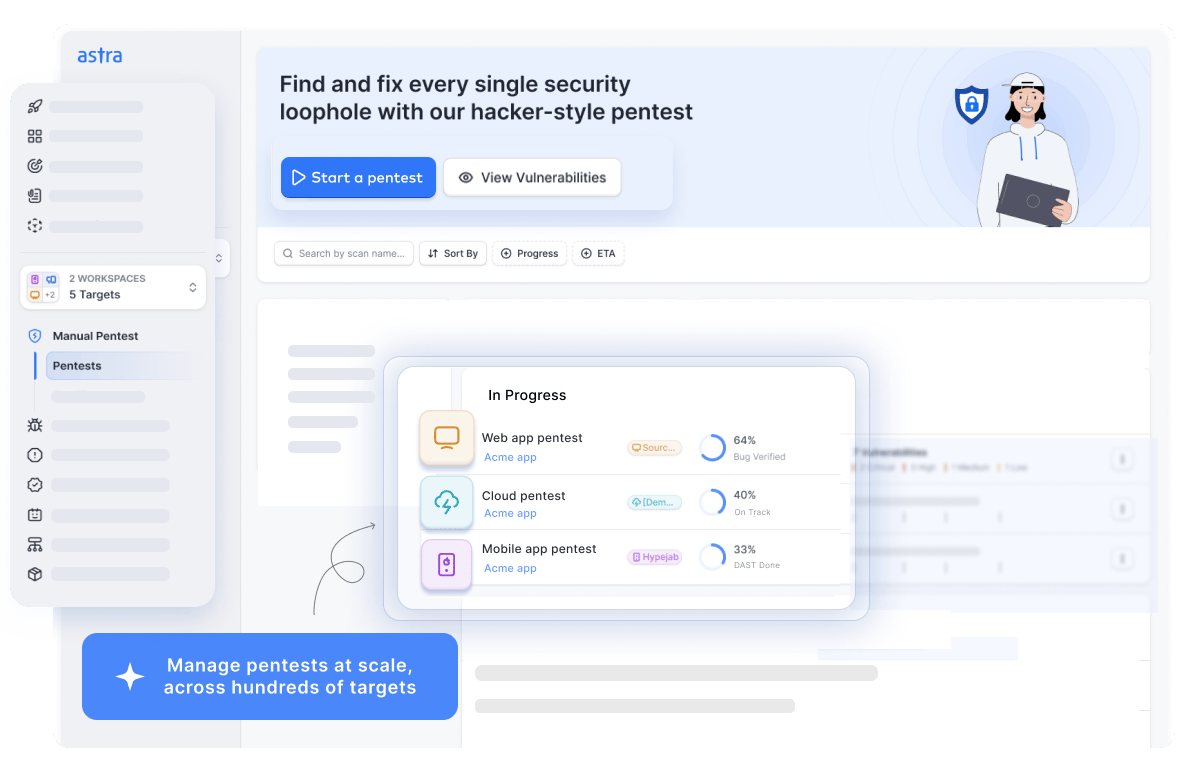
Accelerated at Techstars in Berlin, awarded a grant under the French Government’s Tech Ticket program by President François Hollande, Astra Security is one of the leading SaaS cyber security companies specializing in innovative solutions. Our comprehensive suite blends automation and manual expertise to run 10,000+ tests and compliance checks, ensuring complete safety.
With zero false positives, seamless tech stack integrations, and real-time expert support, we strive to make cybersecurity simple, effective, and hassle-free for thousands of businesses worldwide.
Moreover, recognized as the Most Innovative Security Company by Prime Minister Modi at GCCS’17, our industry-specific AI test cases, world-class Astranaut Bot, and customizable reports are designed to make your experience smoother while saving you millions of dollars.
- Founded year: 2018
- Best For: PTaaS Platform
- Number of Employees: 11 – 50
- Headquarters: Delaware, USA
- Customers and Accolades: Ford, GoDaddy, Dream11

Pros:
- Conducts pentest by security experts with OSCP, CEH & CVEs under their name.
- Offers tailored executive and engineer-friendly reporting.
- Scans behind logged-in pages.
- Guarantees zero false positives with vetted scans.
Astra Pentest is built by the team of experts that helped secure Microsoft, Adobe, Facebook, and Buffer

12. Acunetix by Invicti

Acunetix, as one of the top 10 cybersecurity companies offers a powerful web application security scanner to identify and fix vulnerabilities (SQL injection, XSS, etc.) across websites and APIs. It automates scans, assesses server-side code, and integrates with developer tools for faster patching.
With Acunetix, you can gain a complete view of your web security for virtual patching for web application firewalls and seamless integration with issue trackers, CI/CD systems, and developer tools to streamline remediation.
- Founded year: 2005
- Best For: VAPT and compliance assistance
- Number of Employees: 51-200
- Headquarters: London, UK
- Customers and Accolades: American Express, Cognizant, US Air Force
Pros:
- Minimizes false positives in automated penetration testing.
- Offers OWASP scans and reports.
13. BurpSuite
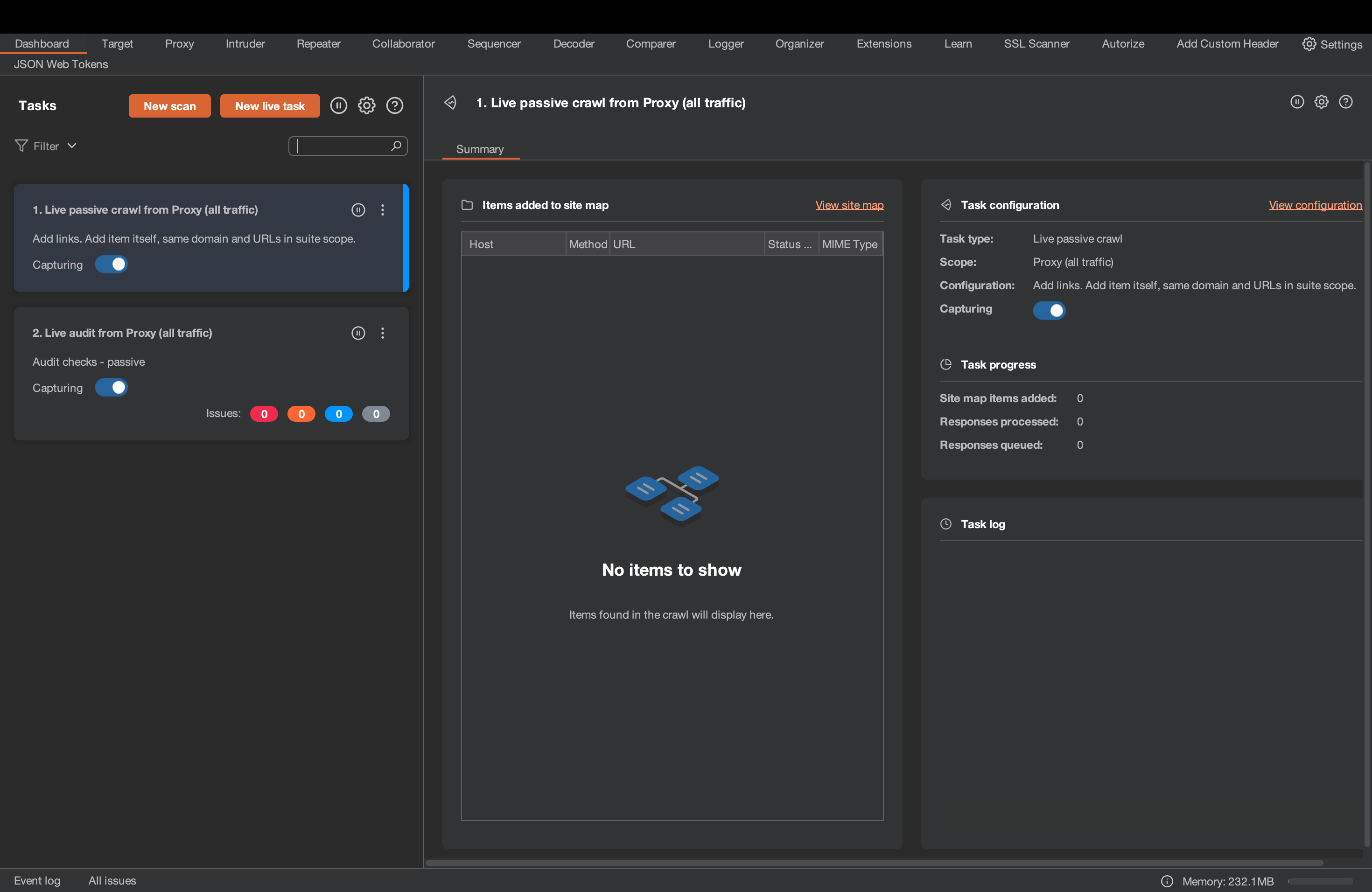
Burp Suite’s PTaaS platform equips your company with a powerful proxy for in-depth traffic analysis. Scanning for vulnerabilities like SQL injection and XSS, it automates attacks to pinpoint CVEs, maps hidden pages and generates detailed reports.
With extensive remediation guidance and manual penetration testing services, Burp Suite’s extensibility with BApps allows customization catering to specific testing needs and proactively identifies vulnerabilities.
- Founded year: 2008
- Best For: Cybersecurity testing and asset mapping
- Number of Employees: 51-200
- Headquarters: Cheshire, UK
- Customers and Accolades: Amazon, Barclays, NASA
Pros:
- Helps automate crawling and auditing
14. Rapid7
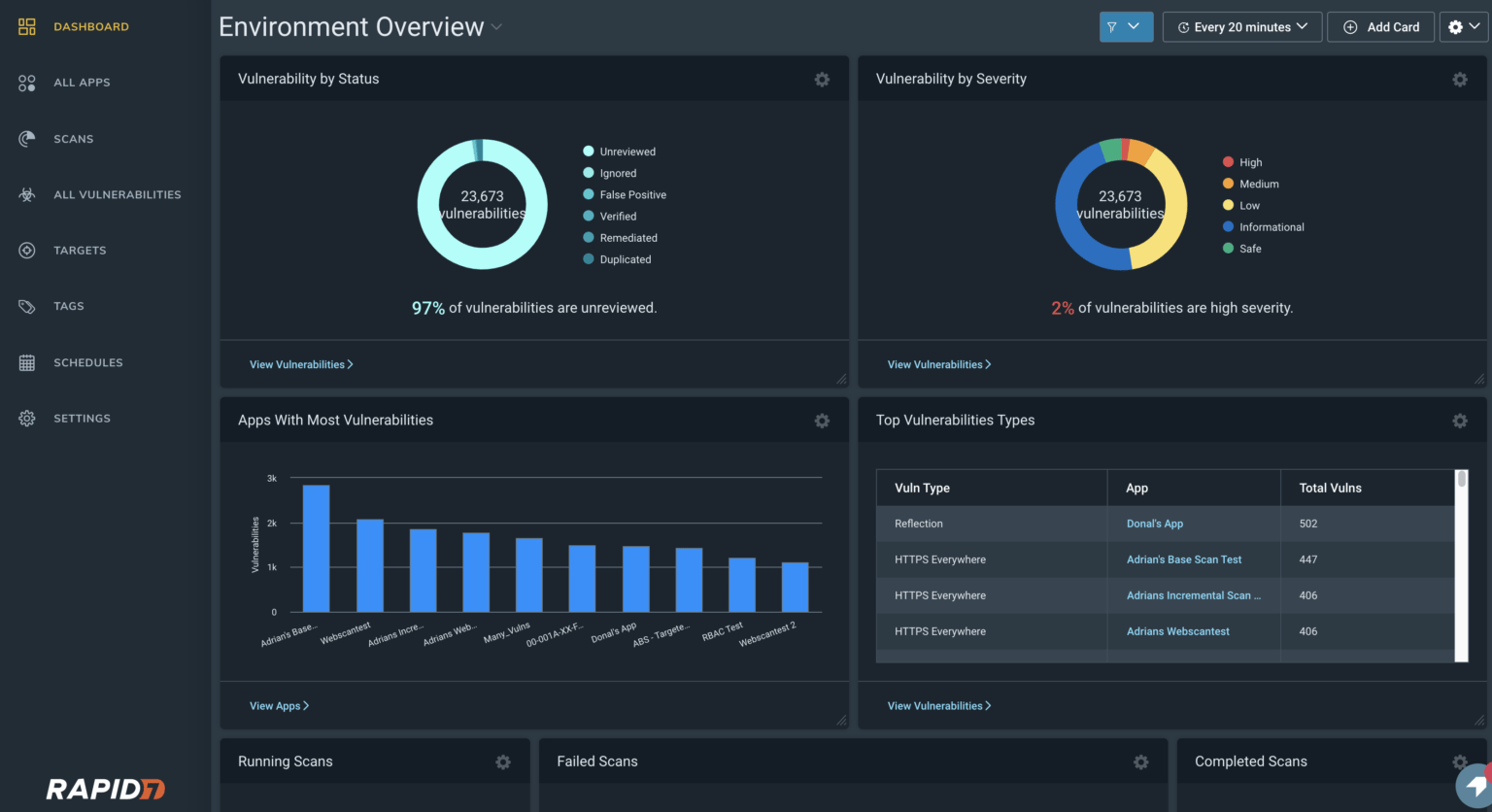
Rapid7’s robust cloud-based toolkit, the Insight Platform, offers real-time vulnerability assessment with InsightVM, continuous attack surface monitoring with the Project Sonar, and 24/7 threat detection and response with MDR.
Further, their penetration testing services help identify application CVEs, while compliance tools ensure regulatory adherence. Backed by industry-leading research projects (Metasploit, Velociraptor), Rapid7 delivers the visibility, automation, and insights needed for comprehensive security.
- Founded year: 2000
- Best For: Managed cybersecurity detection and response with skill development for professionals
- Number of Employees: 1,001-5,000
- Headquarters: Massachusetts, USA
- Customers and Accolades: Discovery, Dominos, Bloomberg
Pros:
- Reports provide in-depth visibility into the vulnerabilities and threats.
- Offers easy-to-navigate dashboards.
Network Security Companies
15. Cybereason
Cybereason’s Extended Detection and Response (XDR) platform uses real-time behavioral analytics to identify and respond to cyberattacks. They provide incident response, security risk assessment, threat intelligence, and complete MDR services.
The platform prevents malicious attacker behaviors, regardless of the specific malware or exploits used.
- Founded Year: 2012
- Best For: Endpoint Detection & Response, Antivirus, Networks
- Number of Employees: 1,500+
- Headquarters: Massachusetts, USA
- Customers and Accolades: CNBC’s 10th Annual CNBC Disruptor 50, Forbes 2022 Cloud 100
Pros
- They provide automated remediation, which reduces the manual errors involved in expert intervention for multiple alerts.
- It uses behavior-based detection, which studies the different chains of behaviors that led to the attack. It also uses an operation-centric MalOps approach, which looks at the root cause of the attack rather than flagging individual alerts.
16. Sophos
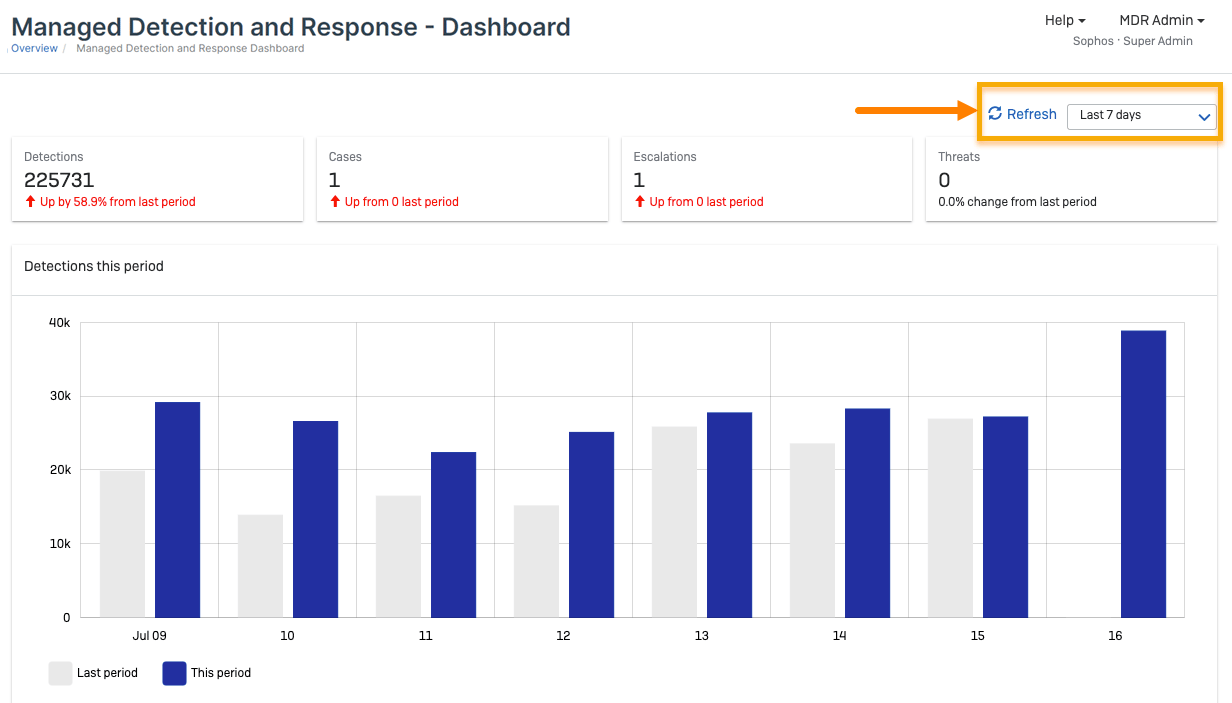
Sophos protects organizations with a unified security suite as a top cybersecurity company. It safeguards devices (Endpoint Security), networks (advanced firewalls), and cloud environments with its 24/7 MDR service to provide constant threat monitoring and response.
Powered by Sophos X-Ops intelligence and managed via Sophos Central, it offers centralized control, user-friendly interfaces, and top-notch support.
- Founded year: 1985
- Best For: Managed security services, compliance with IT protection, and security awareness training
- Number of Employees: 1,001-5,000
- Headquarters: Abingdon, UK
- Customers and Accolades: Norman’s Hallmark, Shutterfly, Diana Holdings
Pros:
- Delivers round-the-clock continuous monitoring.
- Simplify integration with existing tech stack.

Why Astra is the best in pentesting?
- We’re the only company that combines automated & manual pentest to create a one-of-a-kind pentest platform.
- Vetted scans ensure zero false positives.
- Our intelligent vulnerability scanner emulates hacker behavior & evolves with every pentest.
- Astra’s scanner helps you shift left by integrating with your CI/CD.
- Our platform helps you uncover, manage & fix vulnerabilities in one place.
- Trusted by the brands you trust like Agora, Spicejet, Muthoot, Dream11, etc.

17. Symantec
Recently acquired by Accenture, Symantec’s cyber security software safeguards businesses and shields networks, data, and devices like PCs, Macs, and mobiles from viruses and malware.
With advanced solutions like Endpoint Protection, ProxySG for web gateways, DLP for data security, and SiteMinder for access control, its DeepSight Intelligence provides threat insights, while managed security services offer 24/7 security expertise.
- Founded year: 1982
- Best For: Endpoint, network, information, and email security solutions
- Number of Employees: 10,001+
- Headquarters: Arizona, USA
- Customers and Accolades: Threatscape, Makro, Finastra
Pros:
- Dashboard offers a complete health check of the system.
- Simplifies integrations with existing tech stack.
18. Sciencesoft

Sciencesoft is a global IT consulting and software development company focusing on cybersecurity. As part of their cybersecurity solutions, they offer:
- Security assessments and penetration testing
- Network protection
- Security software development and integration
- Managed security services (MSS)
- Security awareness training
- Founded Year: 1989
- Best For: IT Consulting & Custom Software Development (with a focus on Cybersecurity)
- Number of Employees: 700+
- Headquarters: Texas, USA
- Customers and Accolades: IBM, eBay, Walmart, Nestle, Top 10% European Software Development Companies 2024
Pros
- Aside from having expertise in cybersecurity, Sciencesoft specializes in developing software, making it perfect for start-to-finish consulting in building a secure digital product.
- They have offices worldwide, enabling them to serve clients in several locations.
19. Arctic Wolf

Arctic Wolf’s Security Operations Cloud analyzes data from all corners (endpoints, networks, cloud) to detect and respond to cyber threats proactively. Their 24/7 monitoring (MDR), continuous risk management, and employee security awareness training work together to fortify your defenses.
Should a breach occur, as one of the best cyber security companies, their incident response services ensure a swift recovery while the Concierge Security Team equips you to build a robust security posture.
- Founded year: 2012
- Best For: Managed detection, risk, security, and awareness services platform
- Number of Employees: 1,001-5,000
- Headquarters: Minnesota, USA
- Customers and Accolades: Oracle Red Bull Racing, Minnesota Vikings, Taaleri
Pros:
- Offers exhaustive weekly reports.
- Offers a user-friendly and intuitive dashboard.
20. Avast
Avast safeguards your entire digital landscape, leveraging real-time endpoint protection with robust antivirus and anti-malware to secure network filtering. Its cloud security protects data and applications, with managed services offering 24/7 monitoring and threat response.
As a cybersecurity firm for advanced defense, Avast provides IT professionals with automated patch management and remote control capabilities backed by a vast global threat detection network.
- Founded year: 1988
- Best For: Antivirus, MSP, and data protection
- Number of Employees: 1,001-5,000
- Headquarters: Prague
- Customers and Accolades: Charity Digital, Southern Imaginations, Citynet
Pros:
- Leverages an intuitive user interface.
- Easy to install and deploy for individuals and organizations.
21. Barracuda Networks
Barracuda Networks provides enterprise-grade cloud-first security solutions for networks, email, applications, and data.
As one of the top 10 cyber security companies, they test for all major attack vectors, preventing data breaches, ransomware attacks, phishing, and AI cyber threats.
- Founded Year: 2003
- Best For: Network Security, Email Security, Cloud Security
- Number of Employees: 2,000+
- Headquarters: California, USA
- Customers and Accolades: SuperCareHealth, Bank of Botetourt, Primary Care Networks, Best AI Email Security in 2023
Pros
- The solutions are designed to be easy to deploy and manage, even for businesses with limited IT resources.
- It is usually more affordable than some prominent security vendors, making it a good option for businesses on a budget.
22. Bitdefender
Bitdefender offers services for individuals, small businesses, and large enterprises. Acclaimed as a leader in endpoint and cloud-native security, it delivers high-quality threat prevention, detection, and response solutions.
Their products include antivirus for individuals, endpoint protection, and network security solutions. Bitdefender’s antivirus software consistently ranks high in independent testing by security organizations.
- Founded Year: 2001
- Best For: Antivirus, Endpoint Protection, Network Security
- Number of Employees: 1,800+
- Headquarters: Bucharest, Romania
- Customers and Accolades: Ferrari, Blaze Networks, The Forrester Wave: Extended Detection and “AI-Powered Threat Detection & Response,” plus 2025 MSP Today Product of the Year for Barracuda Managed XDR and a spot on the 2025 CRN AI 100 list.
Pros
- They offer a multi-layered security approach beyond antivirus protection, including features like endpoint detection and response (EDR) and network security tools.
- Provides scalable solutions for businesses of all sizes, from small and medium-sized businesses to large enterprises.
Data Security Companies
23. Alert Logic

AlertLogic is a vulnerability management provider that provides managed threat detection and response (MDR), SOC-as-a-service, compliance services, and web application firewall (WAF) services.
The platform analyzes over 140 billion log messages daily, providing unique threat intelligence. It is also an AWS Partner. Its services include 24/7 threat monitoring, incident validation, remediation, log management, and more.
- Founded Year: 2011
- Best For: Managed Security Services across targets
- Number of Employees: 600+
- Headquarters: Texas, USA
- Customers and Accolades: McArthurGlen, PCI Pal, Cloudspace USA, G2 MDR Leader, Cybersecurity Breakthrough Award
Pros
- Leadership in cloud vulnerability management.
- Scalable, customized pricing plan.
24. Qualys
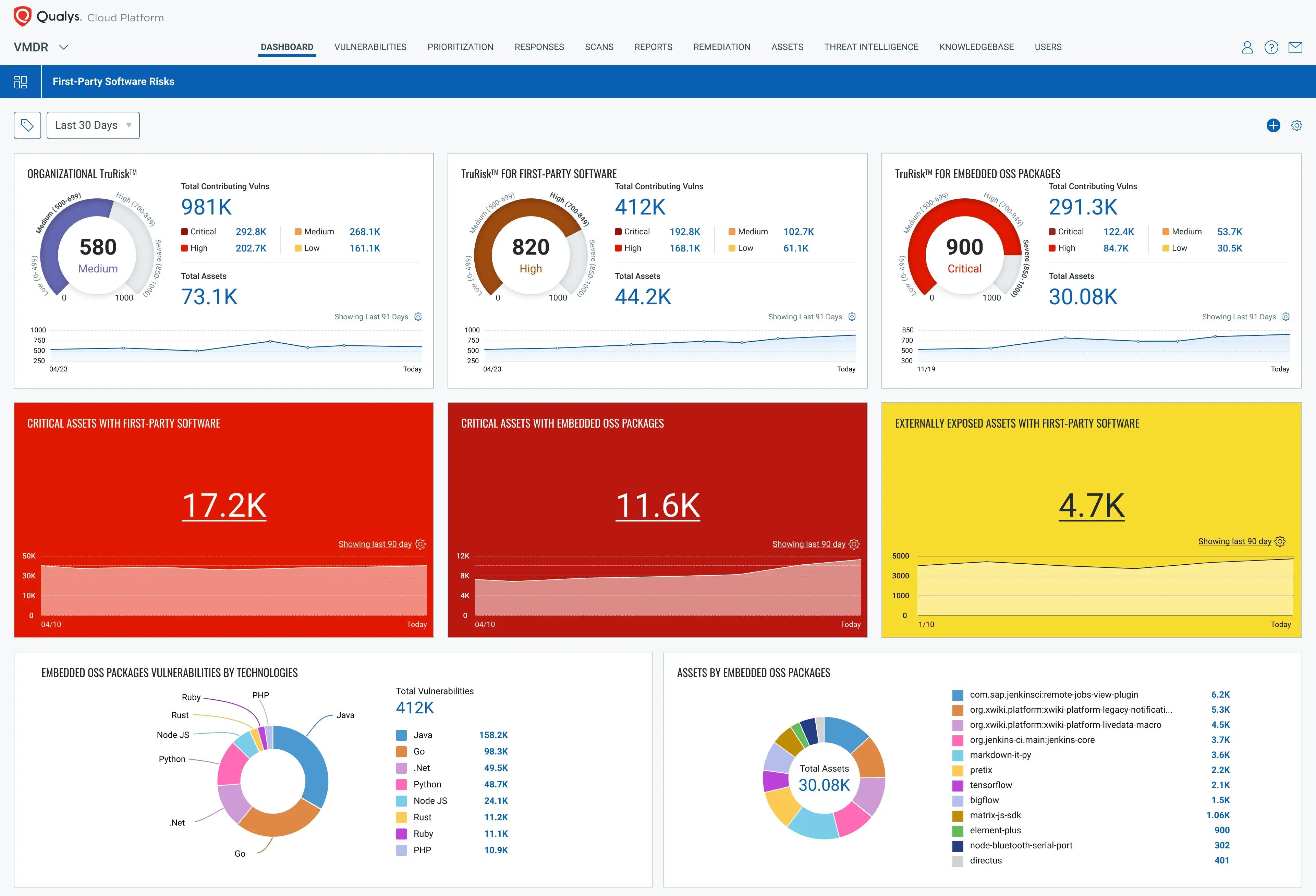
With expertise in cyber security, Qualys secures hybrid IT with a unified cloud platform that continuously discovers, prioritizes, and patches vulnerabilities across all devices with its VMDR and Threat Protection.
As the name suggests, Cloud Inventory & Assessment handles inventory and misconfiguration detection, while Cloud Agent handles real-time unmanaged device discovery to ensure complete visibility. Thus, the integrated vulnerability scanning, web application firewalls (WAF), and compliance automation under Qualys Policy & PCI Compliance fortify your defenses.
- Founded year: 1999
- Best For: Managed vulnerability detection, compliance, and protection for IT systems
- Number of Employees: 1,001-5,000
- Headquarters: California, USA
- Customers and Accolades: CapitalOne, Edinburgh Airport, Home Depot
Pros:
- Simplifies vulnerability and patch management.
- Helps select and customize the specific types of scans.
Make your SaaS Platform the safest place on the Internet.
With our detailed and specially
curated SaaS security checklist.

25. Cobalt Iron
Cobalt Iron’s Compass goes beyond backup with built-in cybersecurity (Cyber Shield) to actively safeguard your enterprise data against unauthorized access, misuse, and contamination with strong authentication and data control.
Powered by analytics, it continuously monitors for threats and automates mitigation, eliminating vulnerabilities in traditional backups. Cobalt Iron offers comprehensive protection for ransomware attacks, including readiness, detection, impact analysis, and rapid recovery – adapting to real-time threats.
- Founded year: 2013
- Best For: Cloud backup SaaS with ransomware protection services
- Number of Employees: 11-50
- Headquarters: Kansas, USA
- Customers and Accolades: Capital City Bank, Cheney Brothers, Ingeus
Pros:
- Offers unified data protection management.
- SaaS delivery eliminates the security exposures common in traditional backup environments.
Find the best fit by comparing Cobalt alternatives on deployment flexibility, DevSecOps integrations and remediation workflows.
26. CyberOps
CyberOps is a VAPT company based in India that offers pentesting services and vulnerability assessment for an end-to-end workspace, including networks, cloud, and applications. They also provide digital forensics, incident response, and compliance testing for SOC2. PCI DSS, and ISO 27001.
CyberOps offers managed security services (MSS), including 24/7 security monitoring and threat detection expertise.
- Founded Year: 2016
- Best For: Vulnerability Assessment & Pentesting (VAPT)
- Number of Employees: 30+
- Headquarters: Jaipur, India
- Customers and Accolades: Law enforcement agencies, financial institutions, educational institutions
Pros
- CyberOps’ XDR platform provides an overall view of security data across all digital functions.
- Continuous monitoring to identify emerging threats.
27. Darktrace
Darktrace leverages self-learning AI that adapts to the customer environment for threat detection, investigation, and response across channels like endpoint, cloud, network, application, and e-mail security.
Their Enterprise Immune System platform uses self-learning algorithms to analyze network traffic, user behavior, and system activity to identify and respond to cyber threats in real-time. Darktrace’s AI uses anomaly detection to identify and isolate even unknown threats.
- Founded Year: 2013
- Best For: AI-Powered Threat Detection & Extended Detection and Response (XDR)
- Number of Employees: 2,300+
- Headquarters: Cambridge, UK
- Customers and Accolades: Steve Madden, Aston Martin, KPMG, McLaren, named a Customer’s Choice in the 2025 Gartner® Peer Insights™ Voice of the Customer for Email Security.
Pros
- AI algorithms can detect sophisticated threats that traditional security tools might miss, including zero-day attacks and insider threats.
- The platform continuously learns about your network activity and user behavior, allowing it to identify the slightest anomalies.
28. Deepwatch
Deepwatch provides managed security services and deep threat management. Its platforms include vulnerability management, threat signal management, endpoint detection and response, and firewall management.
Their unique security center dashboard has features such as tracking metrics and KPIs of threats to increase visibility, providing insights on efficiency by analyzing top-line metrics, and a Deepwatch Security Index Framework for continuous improvement.
- Founded Year: 2019
- Best For: Managed Security Services (MSS), Threat Intelligence & Security Information and Event Management (SIEM)
- Number of Employees: 400+
- Headquarters: Florida, USA
- Customers and Accolades: GPC, St. John’s University, RJ O’Brien, 2024 Global Infosec Awards – Cyber Defense Magazine, and was highlighted in multiple 2025 MDR/Managed Security Leader reports for excellence in continuous monitoring and threat response.
Pros
- It provides businesses 24/7 security monitoring and integration into the CI/CD pipeline.
- A customizable dashboard that facilitates communication and security transparency across teams to enable stress-free remediation.
29. Deloitte
Deloitte is a professional services network that offers several cybersecurity consulting services. Their Cyber Risk program provides a complete list of services to help organizations identify, assess, manage, and mitigate cybersecurity risks.
Deloitte’s cybersecurity consultants can help businesses develop and implement a cybersecurity strategy, conduct security assessments, respond to security incidents, and improve their overall security posture.
- Founded Year: 1845
- Best For: Cybersecurity Consulting Services
- Number of Employees: 415,000+
- Headquarters: London, UK
- Customers and Accolades: Metlife, Morgan Stanley, Berkshire Hathaway, Microsoft, GM, Procter & Gamble
Pros
- Deloitte’s deep industry expertise and range of services allow them to offer tailored cybersecurity consulting solutions for businesses of all sizes.
- Deloitte’s global reach and established reputation in cybersecurity consulting evoke trust and ensure consistent security practices.
30. Guidepoint Security
Guidepoint Security offers tailor-made cybersecurity solutions and consulting across mediums like networks, cloud, applications, endpoints, email, etc. It helps organizations identify and manage digital risks associated with cyber threats, fraud, and misconduct.
The company is known for its Cloud Governance plan, which completely secures the cloud. It also offers specialized services such as incident response, forensic investigations, security assessments, and digital intelligence gathering.
- Founded Year: 2011
- Best For: Cybersecurity Consulting
- Number of Employees: 870+
- Headquarters: Florida, USA
- Customers and Accolades: Nuance, Follett, GPC, 2024 Splunk AMER Regional Partner of the Year, and was named 2025 CrowdStrike Global Solution Provider of the Year, recognizing leadership in helping organizations advance cloud and SIEM security.
Pros
- Provides a thoroughly tailored plan based on each customer’s specific environment.
- Acts as a team of advisories/partners rather than an external service provider.
31. HackerOne
- Founded Year: 2012
- Best For: Bug Bounty & Vulnerability Management Platform
- Number of Employees: 350+
- Headquarters: California, USA
- Customers and Accolades: Google, Uber, PayPal, The United States Department of Homeland Security, General Motors
Pros
HackerOne has a leading bug bounty platform that connects organizations with ethical hackers (white hat hackers) to discover and remediate security vulnerabilities in their applications, software, and infrastructure.
They also offer a vulnerability management platform that helps businesses streamline managing and remediating vulnerabilities, which features application security, attack resistance management, and cloud security.
- HackerOne connects businesses with the world’s largest community of ethical hackers, providing access to diverse security expertise worldwide.
- Bug bounties can help businesses patch security holes faster and reduce cyberattack exposure by incentivizing rapid vulnerability reporting.
32. iboss
iboss empowers secure remote and hybrid workforces with a cloud platform that enables access to cloud applications and the Internet. Its robust SASE solution seamlessly blends security (web filtering, cloud access control, firewalls, zero-trust) with network optimization.
Built on a powerful, patented cloud architecture, iboss tackles large encrypted traffic volumes while safeguarding users with remote browser isolation, data loss prevention, and advanced threat intelligence to combat cyberattacks proactively.
- Founded year: 2003
- Best For: Advanced data discovery and threat protection across assets
- Number of Employees: 201-500+
- Headquarters: Massachusetts, USA
- Customers and Accolades: NHS (UK), Petroc College, McLaren Group
Pros:
- Zero trust network with wide range coverage.
- Offers robust reporting features.
Book a pentest for your Indian Business and stay protected with our 10,000+ AI-powered test cases.
Discuss your security needs & get started today!
33. Indusface WAS
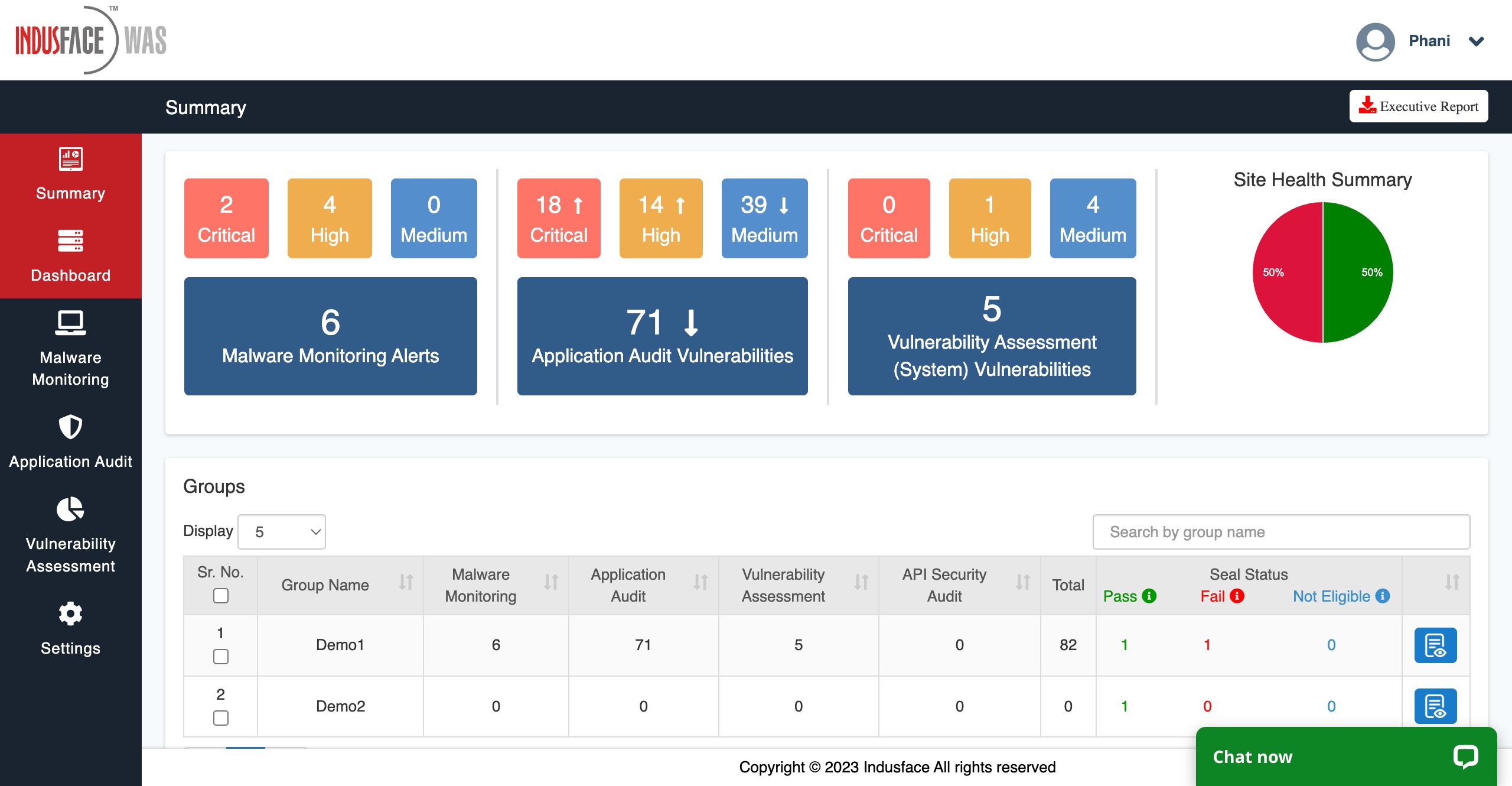
Based in India, Indusface safeguards web applications, mobile apps, and APIs with robust security solutions, including an AI-powered WAAP platform (AppTrana) that shields against modern threats like DDoS attacks and zero-day vulnerabilities.
It goes beyond scanning, offering pentesting, continuous malware monitoring, and providing SSL certificates and compliance tools (SwyftComply) for a holistic security approach. Delivered through a global network with regional deployment options, the cybersecurity company empowers businesses of all sizes to secure digital assets.
- Founded year: 2012
- Best For: VAPT, asset discovery, MSSP, and SSL certifications
- Number of Employees: 51-200
- Headquarters: Bangalore, India
- Customers and Accolades: ICICI Bank, Shoppers Stop, Acko
Pros:
- Facilitates with asset discovery.
- Has a shallow learning curve.
34. KnowBe4
KnowBe4 is the world’s first and largest new-school platform that provides security awareness training and real-world phishing simulations. Its mission is to educate and empower users to make smarter security decisions, ultimately creating a human firewall against cyberattacks.
They’re known for their great customer support, which has earned them several awards and recognition. They offer a variety of training modules and simulations that cover a wide range of security topics, including phishing attacks, social engineering, and malware threats.
- Founded Year: 2010
- Best For: Security Awareness Training & Phishing Simulations
- Number of Employees: 1,200+
- Headquarters: Florida, USA
- Customers and Accolades: Forrester 2022 Wave Leader – Security Awareness Training, G2 Spring 2024 Leader, and is trusted by 65,000+ organizations worldwide, including enterprises and government agencies.
Pros
- A dedicated customer success team that works with you very closely.
- The only training platform that offers real-world phishing simulations.
35. Lacework
Lacework’s CNAPP platform leverages AI and machine learning to continuously hunt threats, including zero-days, across cloud environments. Your developers benefit from its built-in security features to find and fix risks before deployment.
As one of the leading cyber security companies, Lacework further streamlines workflows by automating compliance reporting and evidence collection, equipping your security team to prioritize and address the most critical issues efficiently.
- Founded year: 2015
- Best For: Data-driven cloud-native application protection platform
- Number of Employees: 1,001-5,000
- Headquarters: California, USA
- Customers and Accolades: Clari, Snowflake, TSB
Pros:
- Offers easy traceback capabilities for threat alerts.
- Leverages AI-driven reporting for quality insights.
36. NordLayer
As one of the leading companies for cyber security, Nordlayer empowers your business with a unified cloud-based cybersecurity platform that protects your network and data with remote access configurations, IAM controls, and threat mitigation features.
Moreover, its segmentation and compliance tools simplify adherence to industrial regulations, while the activity monitoring provides real-time detection.
- Founded year: 2019
- Best For: Holistic network, SaaS, and cloud security solutions with VPN and access management
- Number of Employees: 51-200
- Headquarters: New York, USA
- Customers and Accolades: Hostinger, WeTransfer, Calendy
Pros:
- UI/UX is quite user-friendly.
- Necessitates device posture checks.
37. Orca Security
Orca Security is a platform that safeguards your entire cloud environment from data breaches and misconfigurations. Leveraging agentless technology, Orca provides complete visibility and simplifies security for cloud workloads across multi-cloud deployments.
Trusted by industry leaders like SAP, Orca enables businesses to identify and address cloud security risks like misconfigurations, data security, and API exposure.
- Founded Year: 2019
- Best For: Cloud Security Platform (CNAPP)
- Number of Employees: 400+
- Headquarters: Oregon, USA
- Customers and Accolades: Autodesk, SAP, Forbes Cloud 100, 2023 GigaOm Radar for CSPM, Global AWS Security Partner
Pros
- Achieve compliance with over 100 frameworks being utilized to test multiple cloud environments.
- Use a combination of API testing, shift left security, and cloud detection for thorough cloud security.
38. Proofpoint
Proofpoint specializes in email security and cloud-based threat protection. Their solutions protect organizations from email-borne threats such as phishing attacks, malware, and business email compromise (BEC).
Proofpoint offers various products related to digital security awareness, cloud security, email protection, and compliance. It also offers on-call personal assistance.
- Founded Year: 2002
- Best For: Email Security & Cloud-Based Email Protection
- Number of Employees: 4,200+
- Headquarters: California, USA
- Customers and Accolades: Nearly 50% of the Fortune 100 companies, over 30% of the Fortune 1000, 2024 Cybersecurity Excellence Awards – Best Cybersecurity Company
Pros:
- Uses advanced threat detection techniques such as machine learning and behavioral analysis to identify sophisticated email-borne threats in real time.
- Offers a multi-layered approach to email security, combining email filtering, data loss prevention (DLP), and user education to protect organizations from a wide range of email threats.
39. StrongDM
As one of the best cyber security companies, StrongDM redefines privileged access management (PAM) with a zero-trust approach, enforcing continuous, granular access controls based on real-time user actions and context, allowing for immediate blocking of risky activity and preemptive breach prevention.
Thus, StrongDM’s easy-to-use policy creation ensures that the right people have access at the right time, while comprehensive audit trails provide unmatched oversight.
- Founded year: 2015
- Best For: Zero Trust PAM, access management, and compliance assistance
- Number of Employees: 51-200
- Headquarters: California, USA
- Customers and Accolades: Seismic, Beekeeper, Axos Financial
Pros:
- Gives robust access control features.
- Simplifies managing the RBAC in the system.
40. Trellix (Formerly McAfee Enterprise)
Trellix offers a unified endpoint security and extended detection and response (XDR) platform and has recently introduced Trellix Wise. This product uses over ten years of AI modeling and machine learning to produce GenAI.
Their endpoint security platform combines endpoint protection, detection and response (EDR), and vulnerability management capabilities in a single solution. Trellix also offers a cloud-native XDR Engine that provides security teams a central location to manage and investigate security incidents across their entire IT infrastructure.
- Founded Year: 2022 (as Trellix, McAfee Enterprise has a longer history)
- Best For: Unified Endpoint Security & Extended Detection and Response (XDR)
- Number of Employees: 3,800+
- Headquarters: California, USA
- Customers and Accolades: 80% of Fortune 100 companies, 2024 Cybersecurity Excellence Awards – Extended Detection and Response (XDR)
Pros
- It uses GenAI for adaptive threat detection and has a zero-trust strategy.
- Complete control of your SOC and integrated protection that finds vulnerabilities continuously.
41. Veracode
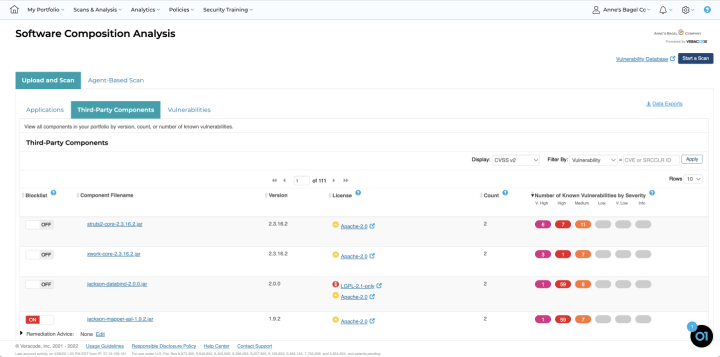
- Founded year: 2006
- Best For: AI-powered application risk management
- Number of Employees: 501-1,000
- Headquarters: Massachusetts, USA
- Customers and Accolades: HDI Global SE, Manhattan Associates, Everbridge
Veracode’s cloud platform streamlines application security across your development lifecycle. It integrates SAST, DAST, SCA, IAST, and penetration testing to give your company a unified view of vulnerabilities in web, mobile, and third-party apps.
Designed for developers, Veracode empowers collaboration and helps you “shift left” by identifying and fixing security flaws early.
Pros:
- Seamlessly integrates with CI/CD pipelines.
- Quick turnaround on support response.
It is one small security loophole v/s your entire website or web application.
Get your web app audited with
Astra’s Continuous Pentest Solution.

Final Thoughts
While the above-curated list of leading cyber security companies is not exhaustive, it equips you to combat the top 5 threats, from AI-powered attacks to devious supply chain exploits.
Whether you require a comprehensive security suite, AI-powered threat hunting, or vulnerability management solutions, there’s a cybersecurity company here to partner with you. Remember, proactive defense is crucial. Don’t wait for a breach to choose your security partner – take action today and safeguard your valuable data and systems.
FAQs
What is the best cybersecurity company?
From the leading solutions and demand for cybersecurity, it can be said that companies like Astra Security, McAfee, and Symantec are some of the best cybersecurity companies out there providing a diverse range of security products.
Why is there a high demand for cybersecurity?
The need and demand for cybersecurity are on the rise since cybercrime and attacks are at an all-time high. The recent shift to an online mode of working has only contributed to the increase in such threats, thus increasing the awareness about the need for good cybersecurity.
What do cybersecurity companies do?
Cybersecurity companies provide various products like malware and virus scanners, VAPT services, firewalls, ransomware, anti-virus, and more to ensure the safety and security of your organization’s assets.
Explore Our Cybersecurity Series
This post is part of a series on Cybersecurity. You can also check out other articles below.

- Chapter 1: 160 Cybersecurity Statistics 2026 [Updated]
- Chapter 2: Top Cybersecurity Trends Shaping 2026
- Chapter 3: How Cybersecurity Audits Can Help Organizations Being Secure?
- Chapter 4: How to Respond to a Cybersecurity Breach?
- Chapter 5: 6 Practical Cyber Security Tips for Startups on a Budget
- Chapter 6: Top 10 Cyber Security Audit Companies
- Chapter 7: Top 9 Cyber Security Assessment Companies
- Chapter 8: What Is a Cyber Security Report?
- Chapter 9: AI in Cybersecurity: Benefits and Challenges
- Chapter 10: How to Build a Cyber Security Culture?
- Chapter 11: What is CTEM (Continuous Threat Exposure Management)?









