In a world where cyber crimes are seeing an exponential rise, maintaining the security of your internet-facing assets has become just as crucial.
Cyber security assessments are the way to go to keep assets secure assets and this article will highlight some of the best cyber security assessment companies for you to consider.
Best Cyber Security Assessment Companies in 2025
Top Cyber Security Assessment Companies
Here is a quick comparison of the best cyber security assessment companies –
[affiliatable id=’194958′]
1. Astra Security
Features:
- Scanner Capacity: Unlimited continuous scans
- Accuracy: Zero false positives
- Vulnerability management: Comes with dynamic vulnerability management dashboard
- Compliance: PCI-DSS, HIPAA, ISO27001, and SOC2
- Price: Starts at $199/month or $1,999/year
Astra Security is the leading provider of VAPT security services for web and mobile applications, networks, cloud, and APIs. Its comprehensive vulnerability and malware detection make speedy remediation possible for any malware or vulnerabilities found.
It also provides world-class firewalls and continuous vulnerability scanning as well as periodic penetration tests to ensure maximum safety for your cloud environment.
Automated Vulnerability Scanner
Astra Vulnerability Scanner is capable of conducting more than 8000 tests to detect vulnerabilities that match an extensive vulnerability database which includes OWASP Top Ten, SANS 25, known CVEs, and more.
Easy compliance checks
Continuous compliance scans ensure that compliance is maintained with industry-specific standards like HIPAA, PCI-DSS, GDPR, and SOC 2.
Intuitive Dashboard
Astra Pentest dashboard is unique in that it is entirely CXO-friendly and allows seamless collaboration between team members and pentesters for easy vulnerability fixing.
Manual Pentest
Astra’s comprehensive manual pentest can detect business logic errors, and conduct scans behind logins.
Zero False Positives
Astra’s Pentest team assures zero false positives in the report through thorough vetting after the automated scans.
Actionable Reports
It provides extensively detailed reports as well POC videos to help organizations patch the vulnerabilities found quickly.
Gap Analysis
Astra also conducts a gap analysis of an organization’s security systems to find the gaps in security and performance that can be improved on.
Publicly Verifiable Certificate
Provision of publicly verifiable certificate upon completion of security analysis and remediation which enhances the company’s reliability and trustworthiness.
Pros
- Can be integrated into the CI/CD pipeline.
- Ensure zero false positives through thorough manual vetting of scan results.
- Has a comprehensive malware and vulnerability scanner.
- Helps with cloud vulnerability management.
- Provides round-the-clock customer support.
Cons
- Does not provide a free trial.
- More scope for integrations.
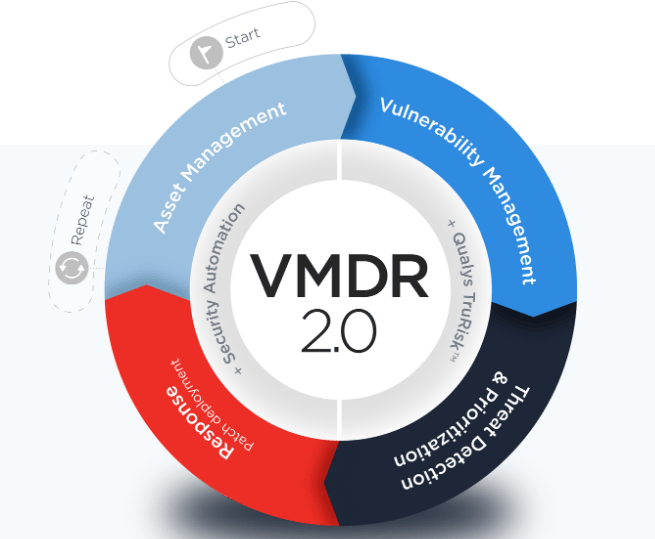
2. Qualys
Features:
- Scanner Capacity: Web applications, cloud
- Accuracy: False positives possible
- Compliance: OWASP, ISO 27001, PCI-DSS, NIST
- Vulnerability Management: Yes
- Price: Quote on Request
Qualys provides its cloud customers with continuous monitoring, vulnerability management, compliance solutions, and web application firewalls.
Qualys maintains a large vulnerability database which helps the scanner stay relevant and current. You can use this tool to scan on-premise devices, cloud instances, IoT endpoints, etc.
You can integrate the scanner with the Qualys continuous monitoring (CM) tool to keep an eye on your assets.
The tool claims to be 99.999% accurate in its findings. These services make Qualys a top cloud security solution contender.
Pros
- Timely alerts and responses.
- Well-designed and easy-to-navigate user interface.
- Constant updates ensure the current security measures for the cloud environment.
Cons
- Limited scheduling options.
- Scans are not applicable to all applications.
Checkout: Qualys vs. Tenable Comparison
3. Cobalt Iron
Features:
- Scanner Capacity: Web and mobile applications, APIs, Networks, and Cloud
- Accuracy: False positives possible
- Vulnerability Management: Yes
- Compliance: SOC2, PCI-DSS, HIPAA, CREST
- Price: Quote on Request
Cobalt Iron assures data security and resilience through hands-free intelligence to back up important data. It provides layered security controls for protection from ransomware. It eliminates any vulnerabilities found during the backup process.
Cobalt has other services including manual and automated penetration testing. They have programs that allow you to get a pentest done in a short time. This tool is automated and generally availed for web applications. It provides management service for an organization’s infrastructure.
Cobalt’s SaaS platform helps you gather real-time insights so that your teams can get on with the remediation quickly. It helps you with cloud scanning and other forms of pentesting.
Discover the top Cobalt alternatives to find a more comprehensive pentesting platform.
Pros
- The product is easy to use
- Provides ease in data backup and resiliency
Cons
- Pricing not mentioned
- Difficult to navigate for beginners.
- Slightly on the expensive end.
4. Sophos
Features:
- Scanner Capacity: Web, Mobile, Cloud, Network and API scanning
- Accuracy: False positives possible
- Compliance: PCI-DSS, HIPAA, GDPR
- Vulnerability Management: Yes
- Price: Quote upon request
Established in 1985 Sophos Cloud offers simplified enterprise-level solutions for cloud security including vulnerability scanning, 24/7 cloud threat detection and response, native protection, and security automation for DevOps.
These services are typically offered as part of Sophos’ larger suite of cybersecurity solutions, which also include endpoint protection, email security, and network security.
Pros
- Available for AWS, GCP, and Azure.
- Helps with security automation through DAST, SAST, and SCA code analysis.
- Intuitive user-friendly dashboard.
Cons
- It can be expensive.
- Difficult to set up.
- Customer support could be better.
5. Palo Alto Networks
Features:
- Scanner Capacity: malware detection, zero day monitoring
- Accuracy: False positives possible
- Compliance: PCI-DSS, HIPAA, GDPR
- Vulnerability Management: Yes
- Price: Quote upon request
Palo Alto Networks provides an all-around malware detection service as well as a next-generation firewall with high-end capabilities.
It provides network speed and threat protection due to its streamlined organization.
Pros
- Palo Alto Network’s cloud security solution is easy to set up.
- Provides zero-day monitoring.
- Provides scope for integrations.
Cons
- Can be an expensive choice to opt for.
- No alerts for cloud performance degradation.
6. Rapid7
Features:
- Scanner Capacity: Cloud and Web Applications
- Accuracy: False positives possible
- Vulnerability Management: Yes
- Compliance: CIS, ISO 27001
- Price: $175/month
Rapid7 provides world-class services for application security, vulnerability management, and SIEM. Other services provided by this company include penetration testing services and vulnerability scanning.
Nexpose by Rapid7 is an on-premises vulnerability management and scanner tool. It is a great choice for small and mid-sized companies.
Key features include adaptive security, policy assessment, and remediation reporting.
Pros
- Simple and easy-to-navigate interface.
- Capable of finding hidden vulnerabilities
- Great and easy-to-understand reports.
Cons
- Customer support can be improved.
- Removal of scanned devices must be done manually.
Checkout: Rapid7 Vs Nessus Comparison
7. Zscaler
Features:
- Scanner Capacity: Cloud, Network
- Accuracy: False positives possible
- Compliance: ISO 27001, ISO 27701, SOC 2
- Vulnerability Management: Yes
- Price: Quote on Request
Yet another among the leading cyber security risk assessment companies, Zscaler provides users with a tight zero-trust security posture that can be managed at all aspects, thus making navigation easy and the security posture more secure.
Distributed cloud-based security for web, email, and mobile computing regardless of client locations.
It helps identify SaaS application misconfigurations and improper access authentication to provide remediation measures and provide secure access to the SaaS application with alerts for any anomalies or threats found.
Pros
- Offers services like file recovery and integrity monitoring.
- Inspection of SSL traffic for malicious activity.
- User-friendly interface.
Cons
- Pricing options are available only on contact.
8. Burp Suite
Features:
- Scanner Capacity: Web applications
- Accuracy: False positives possible
- Vulnerability management: No
- Compliance: PCI-DSS, OWASP Top 10, HIPAA, GDPR
- Price: $449/per user/per year
Burp Suite is one of the popular manual penetration testing tools that is very useful for ethical hackers, pentesters, and security engineers. Let us explore some of the tools included in Burp Suite.
- Spider: It is a web crawler used for mapping the target application. You can create an inventory of all the endpoints, monitor their functionalities, and look for vulnerabilities with Spider.
- Proxy: A proxy is placed between the browser and the internet to monitor, and modify the in-transit requests and responses.
- Intruder: It runs a set of values through an input point and lets you analyze the output for success, failure, and content length.
These aside the suite includes Repeater, Sequencer, Decoder, Extender, and some other add-on tools.
Burp Suite has both a free community edition and a commercial edition.
Who is it for?
Beginners, professional ethical hackers, and also security professionals.
Pros
- Has both open-source and commercial editions.
- User-friendly interface.
- Best internal penetration testing tools.
Cons
- Requires better integrations.
- The commercial product is pricey.
- The free version has lesser features.
9. Nessus
Features:
- Scanner Capacity: Web applications
- Accuracy: False positives possible
- Vulnerability management: Yes (Additional Cost)
- Compliance: HIPAA, ISO, NIST, PCI-DSS
- Price: $5,880.20/ year
Among various cyber security risk assessment companies, Tenable’s Nessus aims to simplify vulnerability assessments and make remediation more efficient.
Tenable Nessus helps you extend your security assessment from traditional IT assets to cloud infrastructures. It keeps the zero false positives low while also covering a wide range of vulnerabilities.
Out of all the best-automated penetration testing tools, Nessus can test your systems for 65k vulnerabilities and allows efficient vulnerability assessment.
Who is it for?
Cybersecurity professionals, and security teams of enterprises.
What is best?
- Has a free version.
- Accurate identification of vulnerabilities.
- Good automated penetration testing tool.
What could be better?
- The free version does not have a lot of features.
- The commercialized version can be expensive.
Explore the best Tenable alternatives and competitors trusted by security teams for accurate scanning and seamless DevSecOps integration.
Benefits Of Cyber Security Risk Assessment Companies
Employing a cyber security assessment company comes with numerous benefits which include:
Uncover Security Threats
Services like malware scanners, vulnerability scanners, and VAPT services all help uncover security risks and threats before they are exploited by hackers. These vulnerabilities are then fixed with the help of the remediation measures within the reports provided by the cybersecurity companies.
Security Consciousness
Cyber security assessment companies help ensure that your organization, its assets, and services all remain safe and secure which increases your reliability and trustworthiness in the eyes of your customers.
Not only this, but it also helps in boosting your clientele since more and more customers are beginning to prioritize the security of the services in tandem with the services required by them.
Cost Effective
Employing cyber security assessment companies that provide anti-virus, malware and vulnerability scanners, VAPT services and more can help in the early detection of malware and vulnerabilities which can then be remediated.
This is much more cost-effective in comparison to dealing with a data breach or theft which can costly in terms of recovery of money lost and sensitive data acquired by malicious attackers.
Achieve Compliance
Employing cyber security assessment companies not only makes for effective security but also helps in achieving compliance through compliance-specific scans and remediation of non-compliant areas found.
According to compliance standards like HIPAA, PCI-DSS, and GDPR, maintaining security is of the utmost priority without which the organizations are liable to hefty penalties and even criminal charges.
Steps in Cyber Security Assessments
In this section, we will go through a genetic flow of cyber security assessment that may or may not apply to your specific case. Nevertheless, it’ll give you an overall understanding of the process.
Identification of information assets
Your digital existence is supported by numerous appliances both software and hardware. It includes network connections, routers, switches, databases, server resources, third-party applications and extensions, and whatnot. A risk assessment identifies all assets, both internet-facing and internal along with network appliances, and creates an inventory.
Identification of Cyber Security Risks
Each one of these can potentially pose a threat to your security, but depending on your mode of business, some are more dangerous than others. A cybersecurity risk assessment aims to segregate those areas.
Vulnerability Scan
Once you have narrowed down the scope of the assessment, it is time to dive into the systems and operations to identify specific security vulnerabilities. An automated vulnerability scan can help with this.
Pentests
A penetration test applies hacker-style methods to find out how hard or easy it is to exploit security vulnerabilities present in your system. Once the scans and the pentest are done, you get a report that lists down all the vulnerabilities along with additional information about each of them.
Prioritization of Vulnerabilities
The next step is to evaluate the vulnerabilities contextually – that is how threatening they are for your specific business. You can then prioritize the high-risk and critical vulnerabilities and venture to fix them first.
Remediation
Once you have a list of prioritized vulnerabilities ready, time and personnel are allocated for the remediation of vulnerabilities. This is not essentially a part of the cyber security assessment, but this is the culmination.
Conclusion
This article has mentioned the top 9 cyber security assessment companies, the benefits that come from employing them, and also the steps usually taken in a comprehensive cyber security assessment. Make your choice today and safeguard your cyber assets for the future.
FAQs
How long does cyber security assessment take?
Cyber security assessments take near 1-2 weeks after which a detailed report containing information regarding the discovered risks and vulnerabilities is given. Based on the report, remediation efforts are carried out.
What is a cyber security assessment company?
Cyber security assessment companies are organizations that provide effective tools to safeguard your assets in cyberspace through penetration tests, vulnerability assessments, risk assessments, or vulnerability scanning.
What is the best framework for cyber security risk assessment?
The best framework to follow for cyber security risk assessment is the NIST methodology. NIST helps analyze cybersecurity, identify security flaws and gaps, and also to meet compliance regulations.
Explore Our Cybersecurity Series
This post is part of a series on Cybersecurity. You can also check out other articles below.

- Chapter 1: 160 Cybersecurity Statistics 2026 [Updated]
- Chapter 2: Top Cybersecurity Trends Shaping 2026
- Chapter 3: How Cybersecurity Audits Can Help Organizations Being Secure?
- Chapter 4: How to Respond to a Cybersecurity Breach?
- Chapter 5: 6 Practical Cyber Security Tips for Startups on a Budget
- Chapter 6: Top 10 Cyber Security Audit Companies
- Chapter 7: Top 9 Cyber Security Assessment Companies
- Chapter 8: What Is a Cyber Security Report?
- Chapter 9: AI in Cybersecurity: Benefits and Challenges
- Chapter 10: How to Build a Cyber Security Culture?
- Chapter 11: What is CTEM (Continuous Threat Exposure Management)?









