On average, 55 new cybersecurity vulnerabilities were published every day in 2021. This goes on to show that preparing for every single vulnerability and running a hundred percent risk-free business is an extremely difficult task, but not entirely impossible.
Cybersecurity risk assessments help you identify the weaknesses in your organization’s security posture and let you efficiently allocate resources to mitigate them. In this post, we’ll learn about cybersecurity risk assessments for web applications and digital organizations in general.
What is Cybersecurity Risk Assessment?
The process of identifying, analyzing, prioritizing, and mitigating the risks faced by your organization on the digital front is called cybersecurity risk assessment.
Regular cybersecurity risk assessments help you recognize the assets that are most at risk, estimate the losses potentially incurred by the exploitation of such risks, and prioritize the most mission-critical risks.
For instance, if you run an e-commerce site that accepts payments and processes payment card data, you are always at risk of a payment gateway hack and that’s where you should focus more resources.
Similarly, if your organization stores personally identifiable information of customers, you always run the risk of getting hacked through an injection. You’d have to put extra stress on input validation.
So, depending on the business you are in, the risk factors shift shape. Regular risk assessments make sure that you are covering all bases as well as possible and never succumbing to a risk that you could have mitigated.
5 Types of Risk Assessment
Risk assessment is a generic term that encapsulates a lot of information. We can think of at least five types of risk assessments that deal with different aspects of an organization’s security posture.
1. Qualitative Risk Assessment
A qualitative risk assessment focuses on the probability of a risk event, the impact it might have on a project, and the areas of exposure to the risk.
It improves a project manager’s holistic understanding of risk factors and helps them prioritize one risk factor over another by looking at the data pertaining to probable impact.
2. Quantitative Risk Assessment
Quantitative risk assessment is a formal and systematic approach to assessing the risk associated with a project or operation based on historical numeric data. This approach is essential for measuring the exposure of employees, the environment, and the assets to various risk factors.
3. Generic Risk Assessment
This refers to the risk assessment methodology that is not tailored for a specific site or environment but is practiced generically. In the context of cybersecurity, an example of a generic risk assessment could be validating the SSL certificate of a site.
4. Site-Specific Risk Assessment
Site-specific risk assessments are adapted to a specific environment. This methodology takes into account information that is relevant only to the site or project at hand. This approach takes into consideration the real conditions of the project and focuses on the hazards relevant to it.
5. Dynamic Risk Assessment
By definition, dynamic risk assessment is “the continuous process of identifying hazards, assessing risk, taking action to eliminate or reduce risk, monitoring, and reviewing, in the rapidly changing circumstances of an operational incident.” This captures the essence of cybersecurity risk assessments very closely as we’ll see in the next section.
The Relationship between Cyber Security and Risk Assessment
Cybersecurity is a broad umbrella that covers a large number of processes and practices geared toward the protection of computer systems from malicious entities. Risk assessment is an intrinsic part of cybersecurity since it provides direction to cybersecurity endeavors dynamically and continuously.
For instance, when you run a vulnerability scan as part of a risk assessment campaign and it shows an SQL injection vulnerability, your security team becomes aware of the issue and applies a solution.
Cybersecurity risk assessments play a crucial part in helping you maintain compliance with industry-specific security regulations.
In a DevOps situation where you have built an agile and hyperactive system of fluid operations, continuous risk assessment becomes a necessity. The risk associated with the code has to be identified and mitigated every time you put it in production.
How to perform a Cybersecurity Risk Assessment?
In this section, we will go through a genetic flow of cyber risk assessment that may or may not apply to your specific case. Nevertheless, it’ll give you an overall understanding of the process.
- Identification of network and information assets
Your digital existence is supported by numerous appliances both software and hardware. It includes network connections, routers, switches, databases, server resources, third-party applications and extensions, and whatnot. A risk assessment identifies all assets, both internet-facing and internal along with network appliances, and creates an inventory.
- Identification of probable risk
Each one of these can potentially pose a threat to your security, but depending on your mode of business, some are more dangerous than others. A cybersecurity risk assessment aims to segregate those areas.
- Vulnerability scan
Once you have narrowed down the scope of the assessment, it is time to dive into the systems and operations to identify specific security vulnerabilities. An automated vulnerability scan can help with this.
- Pentests
A penetration test applies hacker-style methods to find out how hard or easy it is to exploit security vulnerabilities present in your system. Once the scans and the pentest are done, you get a report that lists down all the vulnerabilities along with additional information about each of them.
- Evaluation and prioritization of vulnerabilities
The next step is to evaluate the vulnerabilities contextually – that is how threatening they are for your specific business. You can then prioritize the high-risk and critical vulnerabilities and venture to fix them first.
- Resource allocation
Once you have a list of prioritized vulnerabilities ready, you can allocate time and personnel to the remediation of said vulnerabilities. This is not essentially a part of the risk assessment, but this is the culmination.
How are Cybersecurity Risk Assessments Different from Vulnerability Assessments?
Vulnerability assessment and risk assessment share a lightly complicated relationship. We’ll explain. Vulnerability assessment is a part of risk assessment and yet it goes way beyond the purview of a risk assessment.
At the same time, the first step to a vulnerability assessment is narrowing down information assets that need to be assessed through a risk assessment. If you want to dive deep into this, we’ve done a detailed comparison of Risk Assessment vs. Vulnerability Assessment.
4 Benefits of Regular Cybersecurity Risk Assessments
You have already learned the importance of keeping an eye on IT security risks at all times. There are more benefits of regular risk assessments apart from being able to keep track of your organization’s security posture.
- Creates an inventory of all crucial information assets:
You’re often unaware of the information assets your organization is dealing with. Risk assessments are a great way to keep track of these.
- Identify internal threats
A survey by Verizon in 2022 reported that 82% of data breaches are caused by human error. Cyber security risk assessments can help you identify the areas where human error is highly probable. You can then take the necessary steps to educate the employees about the matter.
- Maintain compliance
Regular risk assessments and mitigation campaigns ensure that you periodically eliminate the vulnerabilities that might mess with your organization’s compliance with relevant security standards. Moreover, the documentation generated by the assessments keeps you audit ready.
- You develop a vision for a secure organization
When you build a habit of regular risk assessments, your organization becomes more incident-ready. You realize the importance of investing in cybersecurity and the ROI of vulnerability assessments and pentest. When you have a clear idea of the potential loss through security risks, it becomes easier to pour the necessary resources in to mitigate the same.
How can Astra Help with Risk Assessments?
Astra Security has built a comprehensive pentest suite that effectively takes care of your vulnerability assessment and penetration testing needs. Astra’s pentest platform is suited for web applications, mobile applications, APIs, and cloud infrastructures.
The following are what Astra’s Pentest Platform brings to your cybersecurity risk assessments
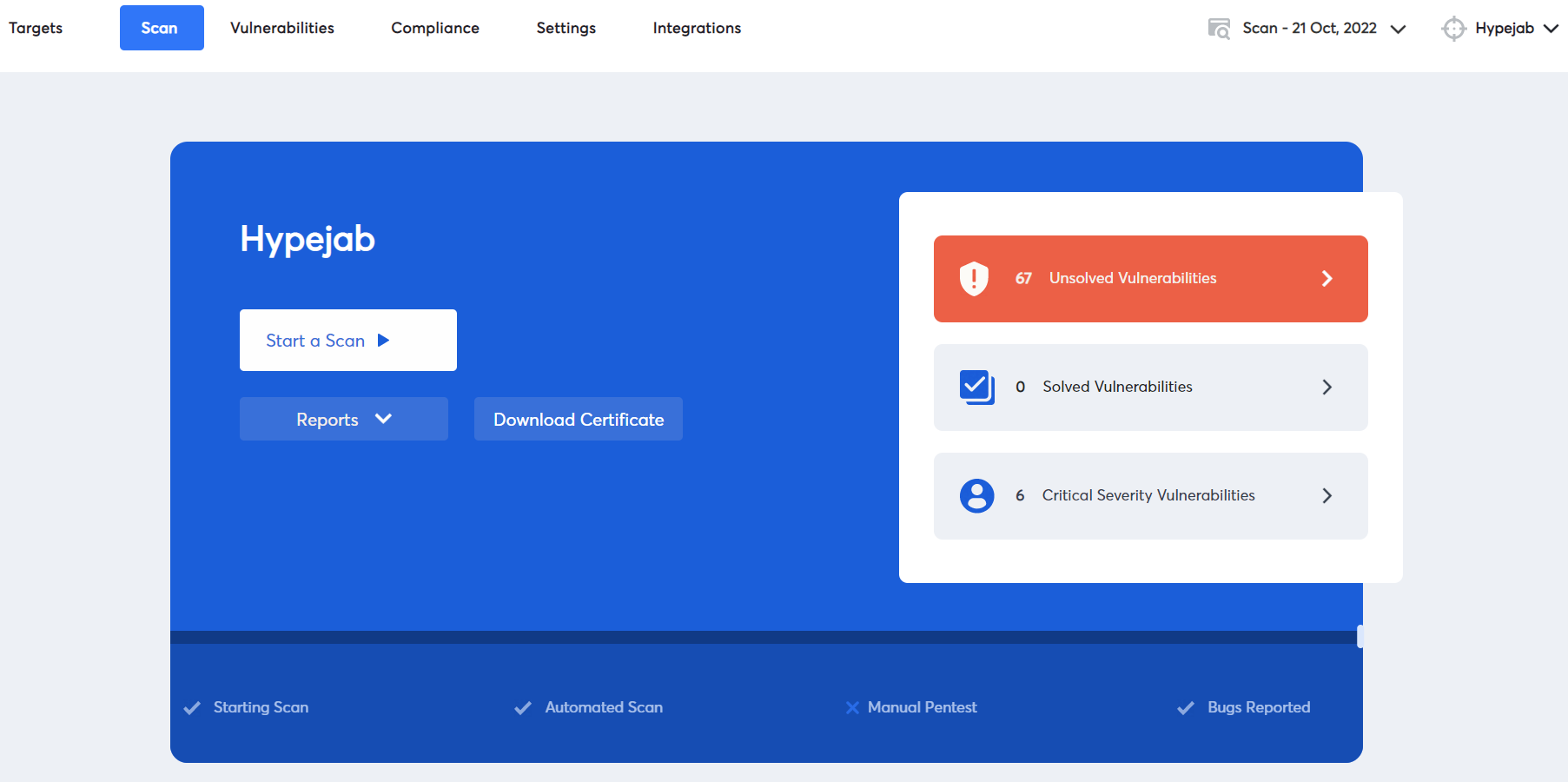
Vulnerability Management Dashboard
A dynamic and interactive dashboard that lets you monitor the vulnerabilities, view their CVSS scores, get a prioritized list of issues, connect with security professionals, and assign and update vulnerabilities. It is a complete solution for your vulnerability management needs, built right into the pentest suite.
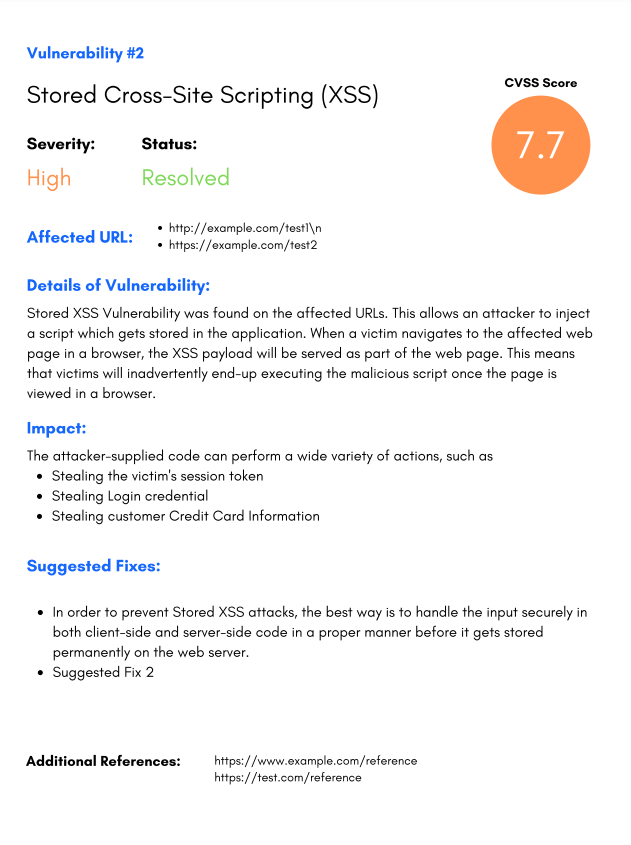
Actionable Vulnerability Reports
The vulnerability scan report generated by Astra is geared toward prompting immediate action. On top of CVSS scores and description of vulnerabilities, the reports present potential loss associated with each vulnerability. Your developers also get detailed remediation guidelines, complete with video PoCs.
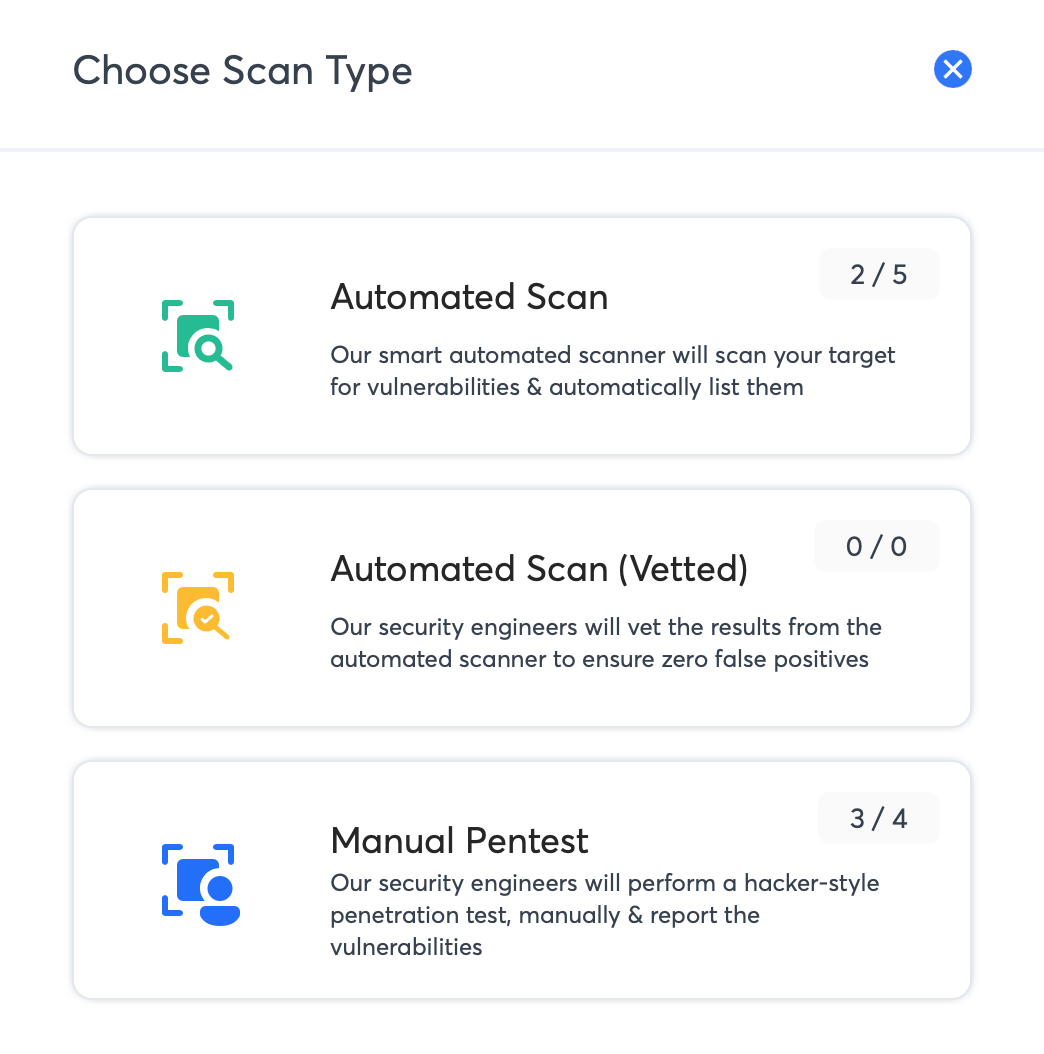
Vetted Scans
Astra’s security engineers vet the vulnerabilities found by the automated vulnerability scanner to ensure the genuineness of each vulnerability. This eliminates false positives and saves you a ton of time and effort.
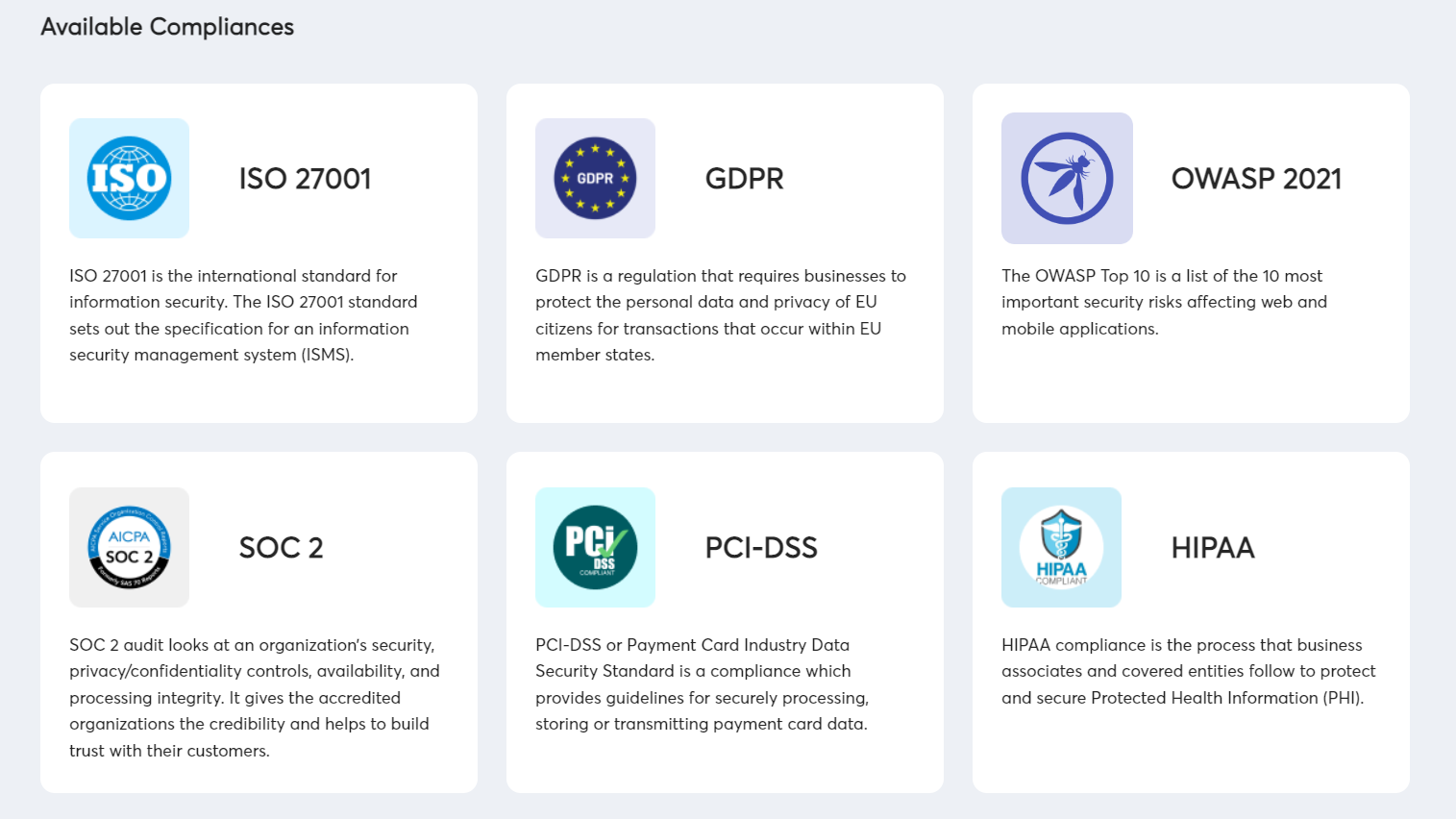
Compliance-Specific Scans
Astra’s pentest dashboard allows you to identify vulnerabilities that block specific compliance requirements. You also get the steps to fix the problems. So, it doesn’t get better than that.
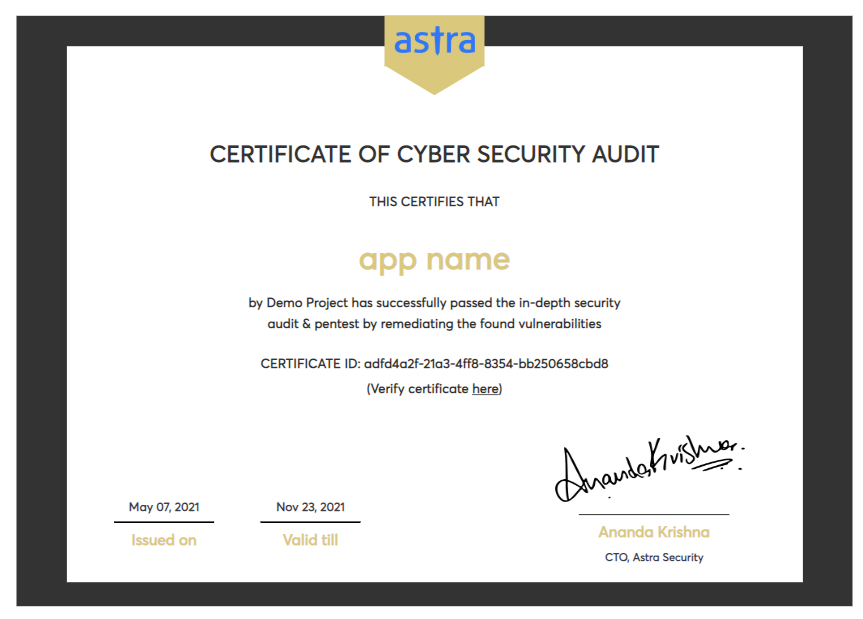
Publicly Verifiable Certificate
After the vulnerability assessment is done and the identified issues are resolved and verified, Astra Security issues a publicly verifiable certificate to your organization. You can use this certificate to establish a security-conscious brand image.
Wrapping Up
Cybersecurity risk assessments are not point-in-time events. You need to make it a regular part of business operations. It’s not that hard if you have the right kind of security partners. You need a risk assessment provider that can streamline the entire process of risk management, from the identification of information assets to the remediation of vulnerabilities.
Educating your employees and creating a security-aware work environment is also very important, given the dominance of the bring-your-own-device tradition and the proliferation of third-party apps. Proactive security and enterprise-wide awareness are the keys to a stable digital organization.
FAQs
1. Are risk assessment and vulnerability assessment the same?
No, they are related processes that involve different methodologies. You can find the differences between the two here.
2. Why is it important to practice regular cybersecurity risk assessments?
Cybersecurity is a dynamic discipline. There are new vulnerabilities emerging every week. You need regular assessments to stay on top of the evolving cyber threat landscape. That aside, you use numerous third-party appliances to run an application, and any of them can introduce a vulnerability to your systems at any point in time. You need regular risk assessments to reduce the probability of being exploited through such vulnerabilities.
3. What is the cost of vulnerability assessment?
Depending upon the scope, environment, and scale of the assessment, vulnerability assessments can cost up to $5000 per year.