Did you know? Just 10 stolen credit cards from every hacked website can earn hackers $2.2 million per month. A significant strike like the British Airways attack of 2018, in which the details of 380,000 credit cards were stolen, must have earned the hackers around $17 million, assuming they sell one credit card for $45 in underground selling forums.
Protecting your valuable data is your responsibility. A consistent and systematic evaluation of your cyber defenses is essential. Discover more about Network Security Testing and its crucial role in safeguarding your business.
What is Network Security Testing?
Network security testing is a process that helps find security vulnerabilities and loopholes across a network that may contain multiple network devices and applications while in direct contact with customers, other businesses, and the government.
Regular security tests of a network lead to the revelation of vulnerabilities and allow the owners to take responsive and preventive measures to ensure better security.
Importance of Network Security Testing
We are often tricked into thinking that buying a firewall or running a security audit once in a while is enough to maintain a network’s security posture. While these measures are important, they are not quite adequate, given the threats you are dealing with.
If you follow the OWASP top 10 or SANS 25 vulnerabilities, you will notice that several CWEs or Common Weakness Enumerations are mapped to each. For instance, in 2021, there were more than 318,000 occurrences of the 34 CWEs mapped to just one vulnerability category—Broken Access Control.
Now, we are talking about one vulnerability off one list of vulnerabilities in a network security testing report. The intention behind establishing this is to help you realize how difficult it can be to maintain a near-perfect security posture. All it takes to wreak havoc is a line of loosely written code.
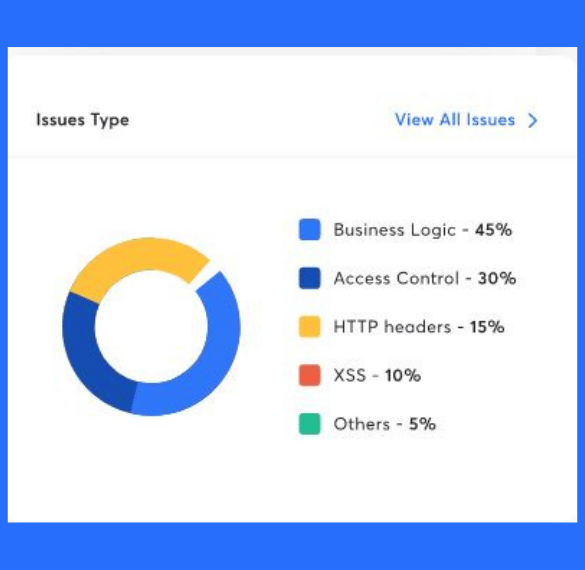
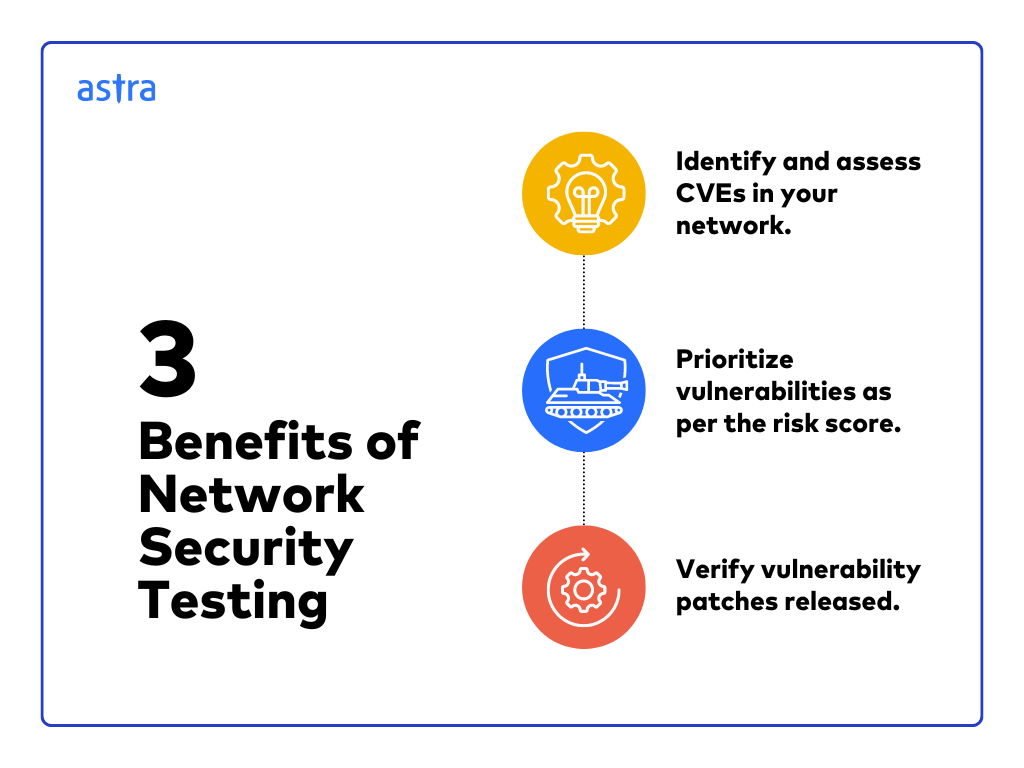
Network Security Testing helps you –
Different Approaches to Network Security Testing
Network security is a broad term that involves different strategies and methodologies. We will briefly discuss some of those approaches.
White Box Security Testing
The white box method refers to a security testing methodology in which the testers know how the system works. They examine control flow, data flow, code implementation, and error handling to determine whether the code implementation is in line with the intended design.
Black Box Security Testing
Black box testing service is a mode of testing in which the testers do not have internal information about the target network. This process of testing emulates a real attack. Black Box testing is helpful in testing server misconfigurations and deployment issues.
Grey Box Security Testing
The Grey Box method combines the White Box and Black Box methods of Network Security Testing. In this process, the testers work with limited information, such as login credentials. These tests are great for understanding how much access a privileged user has and how much damage a hacker with similar privileges can cause.
Astra Pentest is built by the team of experts that helped secure Microsoft, Adobe, Facebook, and Buffer
Different Types of Network Security Testing
Depending on the nature of your business, the industry you operate in, and your specific goals, you can choose a certain type of security testing. It would be best if you often combined multiple of those to get the desired results. We will look at some of the different forms of security testing.
Network Scanning
Network scanning is a routine procedure by network administrators to identify the active devices within a network. The goal is to monitor and manage the systems and inventory devices and compare the inventory to the expected number of devices to assess the network’s health.
Network administrators usually employ a feature in the network protocol to identify the responding devices. Attackers use a similar strategy. They first determine the IP address range assigned to a company using DNS or WHOIS protocol.
This is followed by scanning the addresses within that range to find servers, operating systems, and services running on them and a way to breach the same. Attempting a network scan from an attacker’s perspective to find vulnerabilities and patch them up is a pretty neat way of assessing and maintaining security health.
Vulnerability Scanning
Vulnerability scanning is the process of scanning networks, servers, and applications for security vulnerabilities and loopholes using automated scanners. These scanners are computer programs that list all IT assets operating within a network and find out operational details about them along with the vulnerabilities.
When it comes to network security scanning, vulnerability scanners look into the devices and access servers connected to a network and find unknown perimeter points, such as remote access servers.
Password Cracking
Password cracking is one of the many ways attackers gain access to a network. For instance, if an attacker wants to upload and execute a file on a target application, having the credentials of a legitimate user makes the job much easier. With the privileges granted to users, a hacker can do a lot of damage to a network.
There are generally two kinds of password-cracking attacks
- Dictionary attack: It uses a long list of passwords to guess the actual password. The program runs until either the passwords match or the list is exhausted.
- Brute force attack: In this case, the password cracking program checks all possible combinations of a given character set to guess the password.
Network users often use easy-to-remember passwords for login and authentication. While these passwords might qualify as strong according to a company’s password strength standards, they are easy to crack and, therefore, a major threat to an organization.
System administrators and pentesters use Password cracking to identify users who might be using weak passwords and remedy the situation.
Ethical hacking
Ethical hacking is the authorized emulation of a hack to discover security vulnerabilities in a network, a website, or an application. Ethical hackers, also known as White Hats, are security experts who use their skills to gain access to a system and discover the vulnerabilities and risks associated with them.
Ethical hacking follows certain rules, such as,
- It has to be a legal procedure.
- It is conducted under predetermined rules of engagement.
- The scope of the hack is decided and strictly followed.
- The ethical hackers often have to sign a non-disclosure agreement.
- The hack should not interfere with business functionality.
The goal of an ethical hack is to report vulnerabilities before hackers with malicious intent exploit them.
Penetration Testing
Penetration Testing refers to the process of finding vulnerabilities in a network, website, or application, discovering the risks they pose, and helping the target organization fix them.
The term Penetration Testing is often used interchangeably with Ethical Hacking. Remember, ethical hacking is a broad term that covers a lot of different methods, and penetration testing is just one of them.
Nevertheless, Penetration Testing, also known as Pentest, is one of the most popular ways to conduct Network Security Testing.
In this method, security experts uncover vulnerabilities inherent in a network and try to exploit each of them to some extent. The goal is to find out how much access a certain vulnerability may yield to an attacker. Then, they prepare a Pentest report that documents the vulnerabilities along with the degree of risk posed by them. The report also recommends steps to remediate the uncovered vulnerabilities.
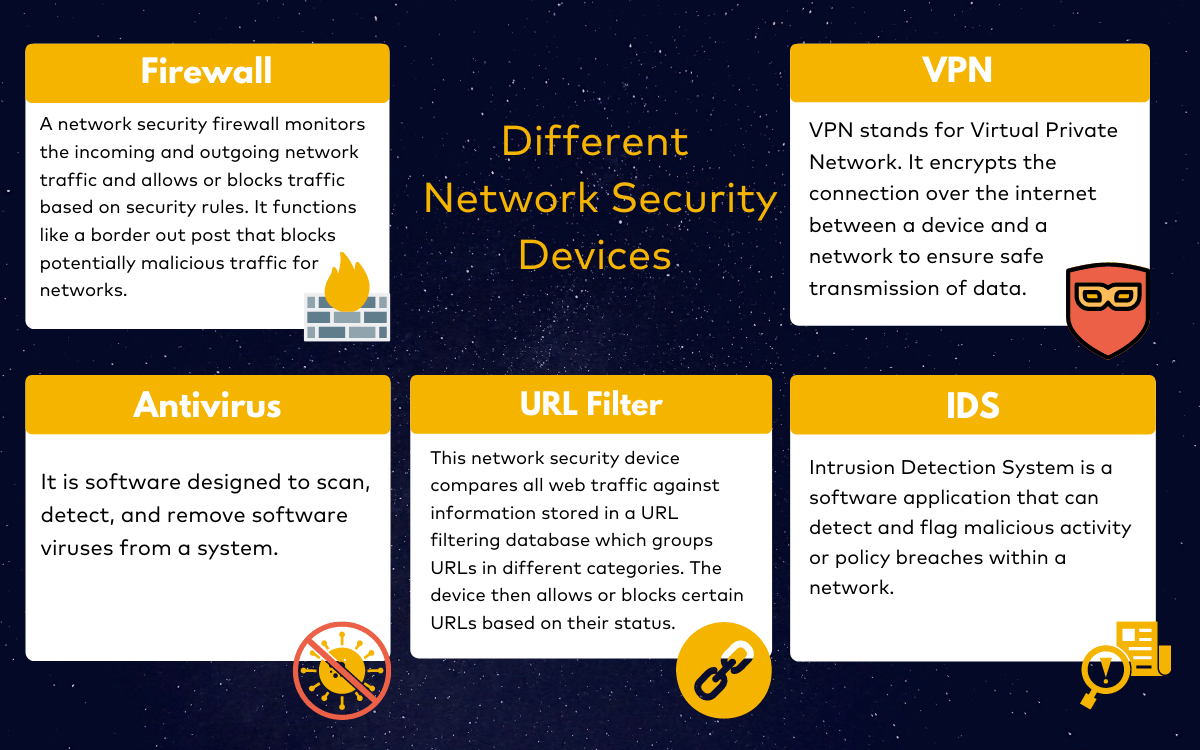
Different Network Security Devices
Network security devices are placed to monitor and control network traffic. These are used to flag malicious traffic and protect the network from threats. As an aftermath of Network Security Testing, the experts can recommend one or more of these devices. Let us look at some popular Network Security Devices.
Make your Web Application the safest place on the Internet.
With our detailed and specially
curated Web security checklist.

Business Outcomes of Network Security Pentesting
There are some very clear benefits to performing regular network security testing. This practice has a genuine ROI and long-term advantages.
- The average cost of a security breach is between $4 and $5 million. A security test every once in a while can help you avoid that peril.
- Protect partners, third parties, and stakeholders by securing your network.
- With adequate security measures, you can significantly reduce network downtime, aiding business continuity.
- Comply with regulatory requirements with ease by conducting consistent network security testing.
- Build trust among customers and clients by protecting their data adequately.
Final Thoughts
Network Security Testing is not a one-time procedure, nor is there a one-size-fits-all approach to it. You have to take it seriously, practice it consistently, and enlist the best quality help that you can find. Whether operating within a private network or connecting to a public network, you have to stay accountable for security, which is why it is important for you and your business.
A practice of regular network security peneration testing can support your efforts to protect your assets, stay compliant, build trust, and save money.
FAQs
How much time does it take to perform a Network Penetration Test?
The duration of a network penetration test can vary significantly depending on the size and complexity of the network being tested. On average however, it usually takes up to 5-10 business days to complete a network penetration test. Factors such as the scope of the test, the availability of resources, and the identification of vulnerabilities can also influence the overall timeline.
What is the cost of performing a networking pentest?
The cost of network penetration testing can vary significantly depending on several factors, including the size and complexity of your network, the scope of the testing, the experience and expertise of the network pentesting teams, and your geographic location. A ballpark figure would be between $5,000 and $20,000 per scan.
Additional Resources on Security Testing
This post is part of a series on Security Testing. You can
also check out other articles below.

- Chapter 1: What is Security Testing and Why is it Important?
- Chapter 2: Security Testing Methodologies
- Chapter 3: What is Web Application Security Testing?
- Chapter 4: How to Perform Mobile Application Security Testing
- Chapter 5: What is Cloud Security Testing?
- Chapter 6: What is API Security Testing?
- Chapter 7: What is Network Security Testing?
- Chapter 8: A Complete Guide to OWASP Security Testing?
- Chapter 9: What is DAST?
- Chapter 10: What is SAST?