Most network security testing tools do one thing very well: make you feel busy. Alerts ping, dashboards glow, reports stack up, yet critical vulnerabilities slip past, unnoticed. Simply having network security testing tools is not the same as having real security.
Are your tools finding the threats that matter or just generating noise? Are they helping your team fix issues or slowing them down? It is time to cut through the clutter and focus on network security testing tools that actually protect the business.
10 Best Network Security Testing Tools
- Astra Security
- NMAP
- Wireshark
- OpenVAS
- Metasploit
- Nikto
- PRTG Network Monitor
- Snort
- Intruder
- Syxsense
Top 3 Network Pentesting Tools
| Feature / Tool | Astra Security | NMAP | Wireshark |
|---|---|---|---|
| Platform | Online | Online | Online |
| Capabilities | Expert-led & AI-augmented pentests for networks, workspaces & IoT devices | Network discovery, port scanning, OS fingerprinting, vulnerability scanning via NSE | Real-time packet capture/analysis, protocol inspection, filtering, troubleshooting |
| Remediation Support | Yes | None | Yes |
| Compliance | HIPAA, GDPR, SOC 2, PCI-DSS, ISO 27001 | None | None |
| Integrations | Slack, JIRA, GitHub, GitLab, CircleCI, Jenkins, etc. | Metasploit | TCPdump, other pcap-based tools, custom plugins |
| Price | Starts at $5999/year | Open-source | Open-source |
| Best For | Thorough network security testing | Penetration testers, IT/network admins needing network insight | Network security analysts, administrators, forensic experts |
| Pros | - AI-assisted pentesting - Publicly verifiable certifications - CXO-friendly dashboard - Customizable reports | - Reliable reconnaissance scans - Flexible scanning with scripting | - Deep protocol inspection - Cross-platform & plugin extensible |
| Limitations | Trial starts at $7 | Steep learning curve for CLI & script-focused use- Limited reporting & visualization | Decrypting encrypted traffic is complex |
10 Best Network Penetration Testing Tools
Network security is one of the most significant concerns for any business. Cybercriminals are continually developing new methods to breach network security and steal valuable information. Network security tools are used to defend a network, and network security testing tools are used to assess the security strength.
You need to be thorough in your network security testing and find vulnerabilities in networks before hackers do. There are numerous network security testing tools available. Some of the best are listed below.
1. Astra Security [Get Started]
Key Features
- Platform: Online
- Capabilities: Expert-led and AI-augmented pentests for networks, workspaces, & IOT devices
- Remediation Support: Yes
- Compliance: HIPAA, GDPR, SOC 2, PCI-DSS, and ISO 27001
- Integrations: Slack, JIRA, GitHub, GitLab, Circle CI, Jenkins, etc.
- Price: Starts at $5999/ yr
- Best For: Thorough Network Security Testing
Astra Security offers one of the most comprehensive network security service tool, running over 15,000+ tests across a multitude of networks, devices, workstations, and more, utilizing network asset discovery, perimeter testing, and firewall configuration review.
With AI-augmented test cases, expert remediation by CERT-IN and CREST empanelled security analysts, alongside manual rescans and tailored reporting, Astra security offers a holistic testing for your network devices.
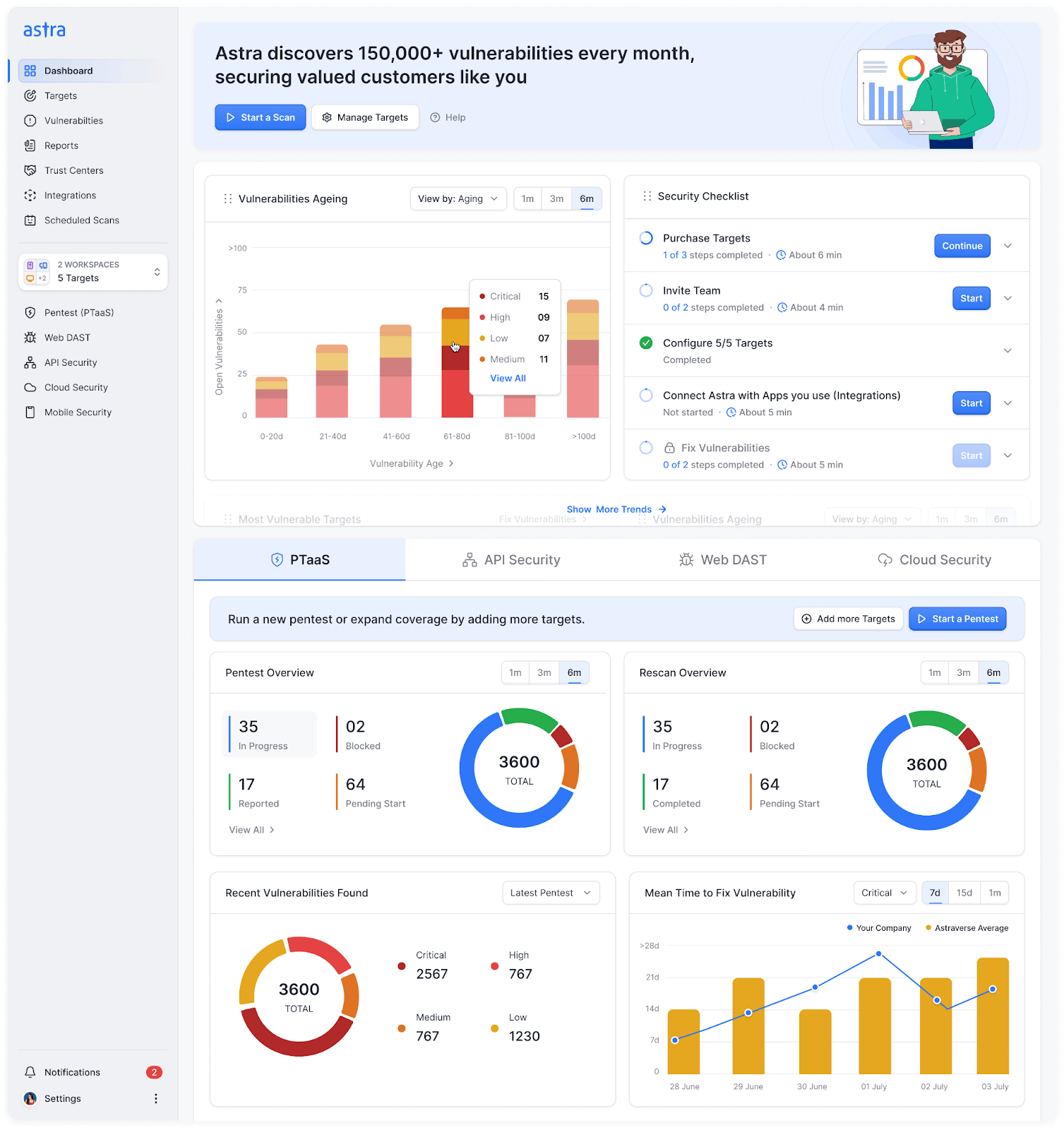
Pros:
- AI-powered test cases that facilitate manual pentesting and chained vulnerability analysis
- Set up seamless CI/CD and workflow integrations with Slack, Jira, GitHub, GitLab, Circle CI and Jenkins
- Flaunt publicly verifiable certifications post 2 free manual rescans
- Accelerate decision-making with a CXO-friendly dashboard with a dedicated CSM
- Generate customizable reports for management and developers, respectively
Limitations:
- Trial starts at $7
2. NMAP
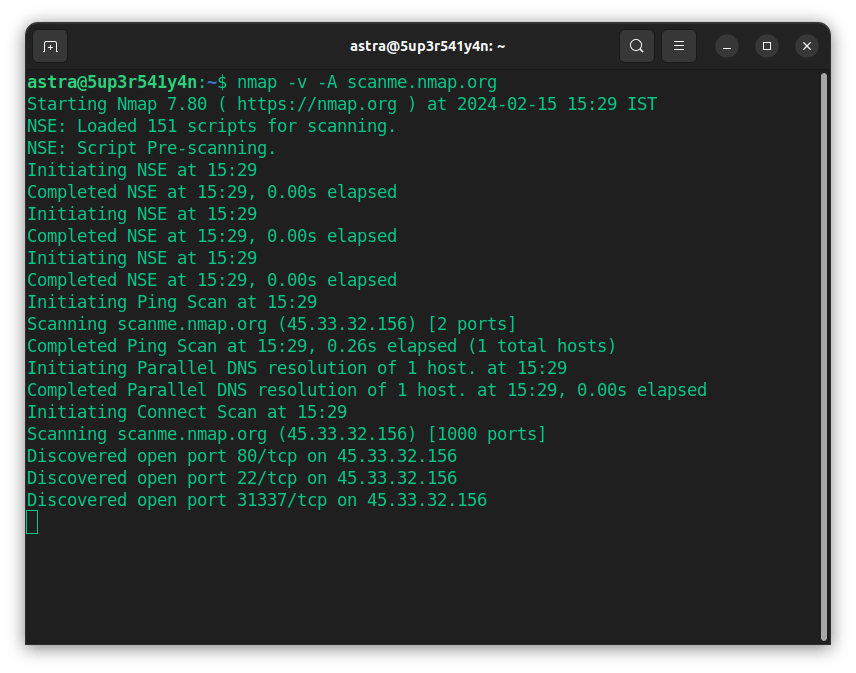
Key Features
- Platform: Online
- Capabilities: Network discovery, port scanning, OS fingerprinting, vulnerability scanning via NSE
- Remediation Support: None
- Compliance: None
- Integrations: Metasploit
- Price: Open-source
- Best For: Penetration testers, IT/network admins needing network insight
Network Mapper, or Nmap, is an open-source utility designed for network exploration, security auditing, and network discovery, enabling rapid scanning of large networks and single hosts. Using raw IP packets in novel ways to determine what hosts are available on the network, their offerings, their operating systems, packet filters/firewalls are in use, and dozens of other characteristics.
Pros
- Highly reliable and widely adopted for reconnaissance scans
- Flexible scanning options with a powerful scripting engine
Limitations
- Steep learning curve for CLI and script-focused use
- Limited reporting and out-of-the-box visualization
3. Wireshark
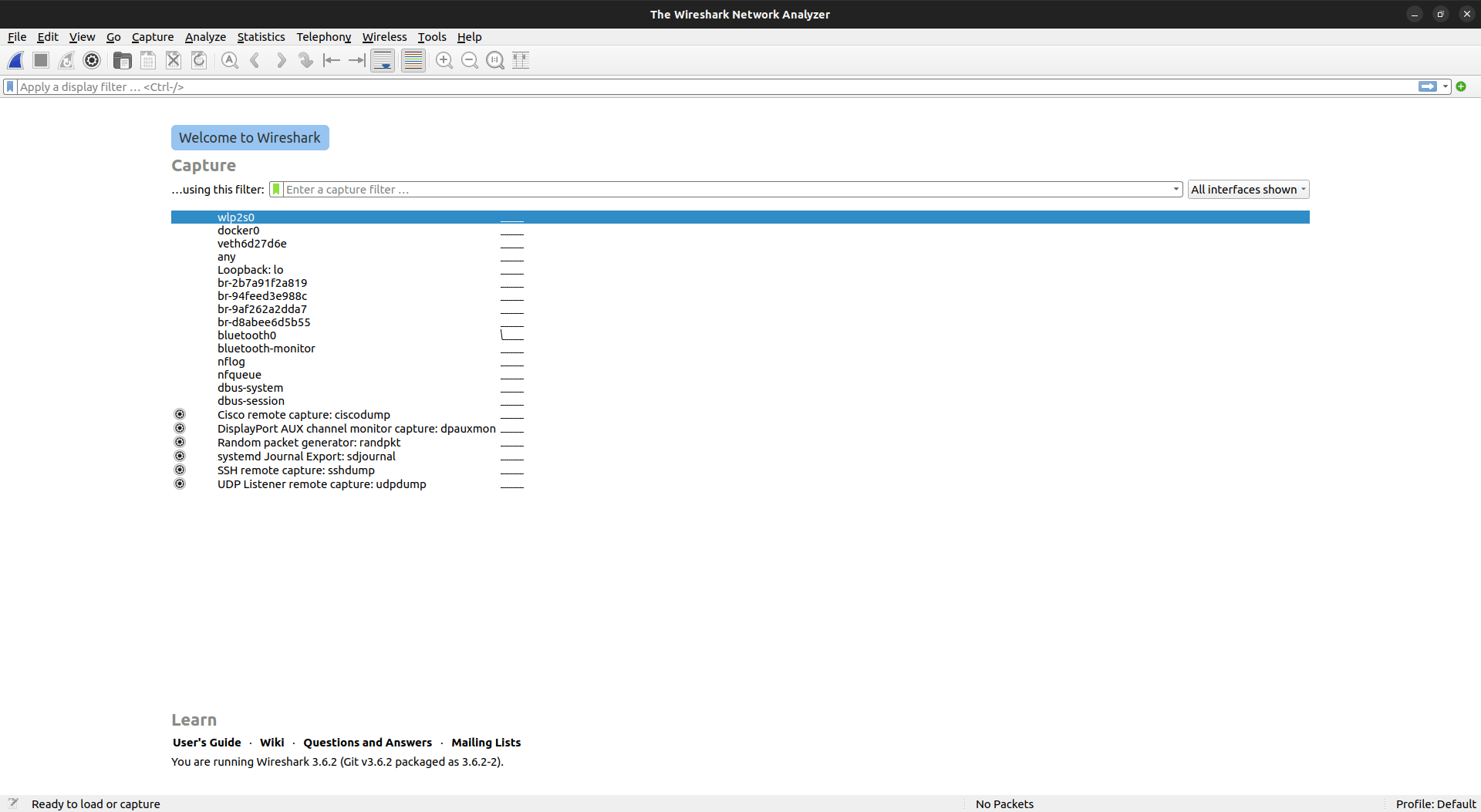
Key Features
- Platform: Online
- Capabilities: Real-time packet capture/analysis, protocol inspection, filtering, troubleshooting
- Remediation Support: Yes
- Compliance: None
- Integrations: TCPdump, other pcap-based tools, custom plugins
- Price: Open-source
- Best For: Network security analysts, administrators, forensic experts
Wireshark is a free and open-source packet analyzer used for network troubleshooting, analysis, software, and communications protocol development. It captures and interactively browses the contents of network traffic to analyze data from a trace file, typically in the form of a pcap (the file format used by libpcap). Wireshark has a GUI and comes in both 32-bit and 64-bit versions.
Pros
- Deep protocol inspection across hundreds of protocols
- Cross-platform and extensible with plugins for automation
Limitations
- Decrypting encrypted traffic is complex
4. OpenVAS

Key Features
- Platform: Online
- Capabilities: Vulnerability scanning, plugin architecture, compliance auditing, prioritized reporting
- Remediation Support: Yes
- Compliance: None
- Integrations: SIEM, ticketing platforms, third-party management tools
- Price: Open-source
- Best For: Robust, continuous vulnerability management at no cost
OpenVAS is a free network security testing tool that can be used to run comprehensive scans on private and commercial products with scheduling and automation capabilities. Owned and maintained by Greenbone, it often helps pinpoint misconfigurations, dated software, and exploitable flaws.
Pros
- Constantly updated vulnerability database
Limitations
- Complex initial configuration and resource-intensive
- Occasional false positives and basic remediation guidance
5. Metasploit
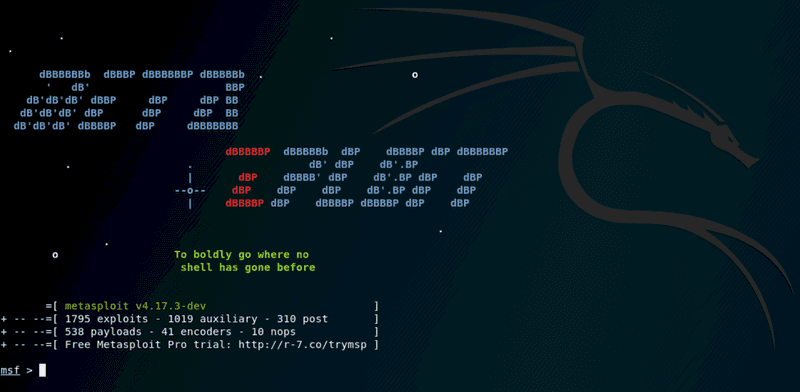
Key Features
- Platform: Online
- Capabilities: Exploit framework, payload generation, vulnerability validation, post-exploitation modules
- Remediation Support: Yes, in premium model
- Compliance: None
- Integrations: NMAP, Nessus, Social Engineering Toolkit (SET), SIEM platforms
- Price: Open-source
- Best For: Security teams, penetration testers verifying vulnerabilities
The Metasploit Project is an open-source computer security software that aids in penetration testing and IDS signature development with an extensive library of pre-built exploits, payloads, and auxiliary modules. Metasploit helps identify security gaps, test defenses, and validate patching strategies. Beyond detection, it also delivers custom exploit development and detailed reporting.
Pros
- Industry-leading exploit database and payload framework
- Integrates with other tools like NMAP and Nessus
Limitations
- Requires advanced scripting/CLI skills
6. Nikto
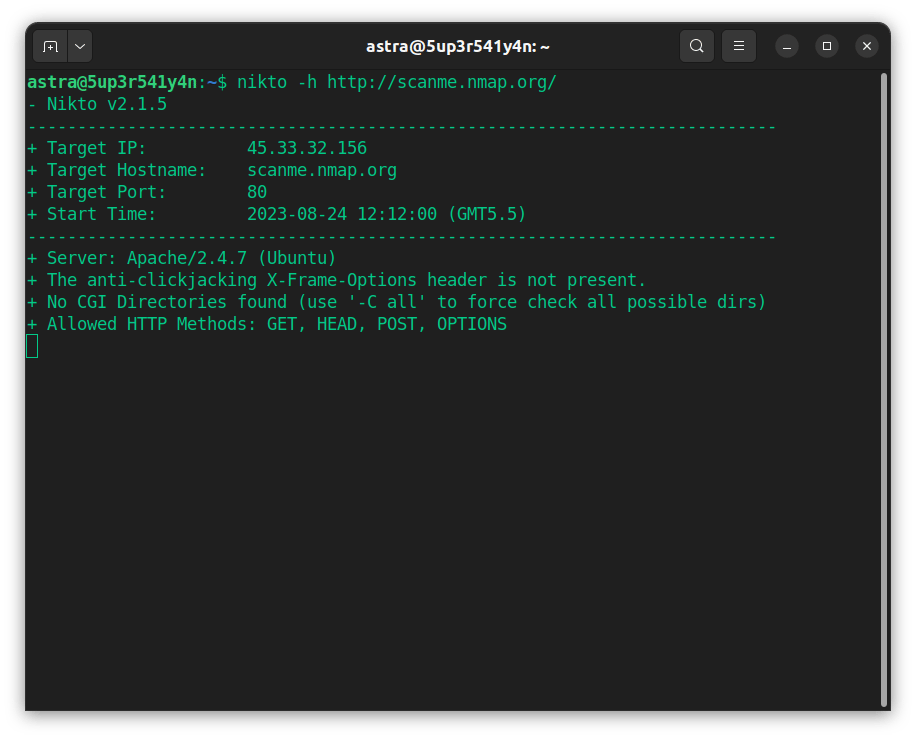
Key Features
- Platform: Online
- Capabilities: Web server vulnerability scanning, misconfiguration detection, plugin-based
- Remediation Support: Yes
- Compliance: None
- Integrations: Can export to reporting platforms
- Price: Open-source
- Best For: Web servers’ analysis
As an open-source web server scanning tool, Nikto can be used to detect suspicious behavior on a network rapidly. It helps you run security tests on HTTP servers and server configurations, alongside offering full HTTP proxy and customized reporting in XML, HTML, and CSV formats.
Pros
- Lightweight, easy-to-use web vulnerability scanner
- Detects outdated software, misconfigurations, and common issues
Limitations
- Only targets web servers (HTTP/HTTPS)
7. Sophos NDR
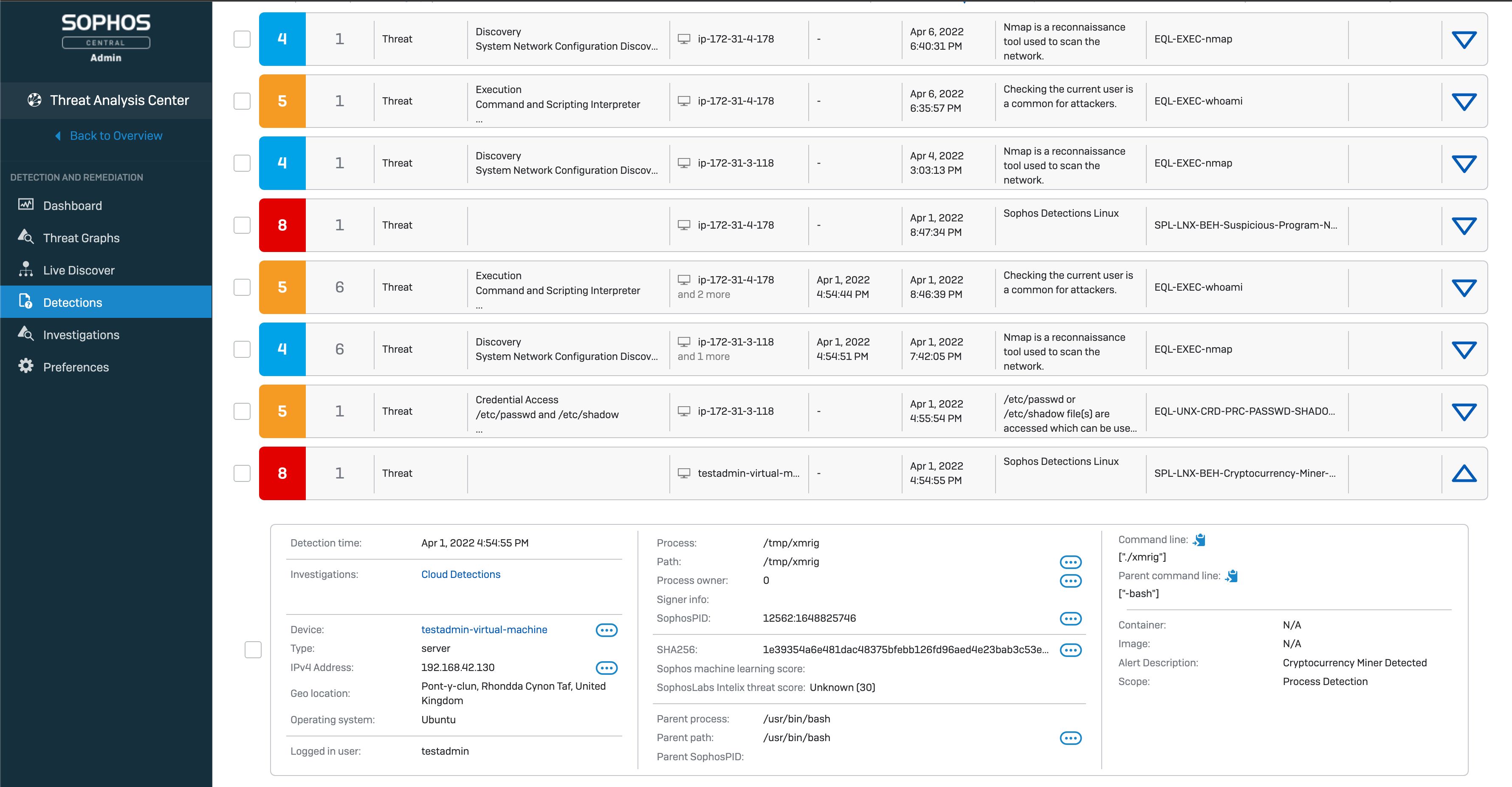
Key Features
- Platform: Online
- Capabilities: Automated traffic analysis to pinpoint network anomalies, insider threats, & zero-days
- Remediation Support: Yes
- Compliance: HIPAA, CIS, PCI-DSS, and SOX
- Integrations: Microsoft, AWS, and Crowdstrike
- Price: Available on quote
- Best For:
As one of the top network security testing tools, Sophos Network Detection and Response (NDR) offers continuous visibility into network activity, detecting threats, rogue assets, devices, and insider threats using AI-augmented detection and deep packet inspection. It helps analyze (un)encrypted traffic, reducing reliance on manual pentesting.
Pros
- Offers a unified security ecosystem
- AI and cloud-powered threat detection
Limitations
- Steep learning curve for advanced features like orchestration, SD-WAN, and custom policies
8. Snort
Key Features
- Platform: Online
- Capabilities: IDS/IPS, packet logging, real-time analysis, protocol and anomaly detection
- Remediation Support: Yes
- Compliance: HIPAA, CIS, PCI-DSS, and SOX
- Integrations: SIEM, third-party security tools, custom rules
- Price: Open Source
- Best For: Security teams needing flexible IDS/IPS capabilities
Snort is an open-source intrusion detection and prevention tool that relies on protocol analysis to detect worms, network port scanning, and other attempts of intrusion. It describes network traffic with the help of a modular detection engine and fundamental analysis, along with a security engine.
Pros
- Robust open-source IDS/IPS platform
- Flexible rule creation and SIEM integration
Limitations
- Can generate excessive alerts if not tuned properly
9. Intruder

Key Features
- Platform: Online
- Capabilities: Automated, continuous vulnerability management, emerging threat scans, risk prioritization,
- Remediation Support: Yes
- Compliance: GDPR, ISO 27001, supports audit reporting
- Integrations: Slack, Jira, AWS, API for custom workflows
- Price: Starts at $99/month
- Best For: Scaling businesses
Intruder is an automated network vulnerability scanner that helps you continuously monitor and detect threats in your network infrastructure. They offer enterprise-grade vulnerability scanning for businesses of all sizes. It can easily detect issues such as SQL injection and cross-site scripting, as well as prioritize vulnerabilities to help you remediate with real-world impact.
Pros
- Simple cloud-based setup, minimal maintenance
- Scans networks, web, and cloud assets with action-oriented reporting
Limitations
- Advanced features are limited to premium tiers
10. Syxsense
Key Features
- Platform: Online
- Capabilities: Vulnerability scanning, automated remediation, patch management, endpoint management
- Remediation Support: Yes
- Compliance: HIPAA, PCI, and SOX
- Integrations: Active Directory, Okta, ServiceNow, TeamViewer, Ansible, and OpenAPI
- Price: Starts at $5/year per device
- Best For: MSPs, enterprises needing unified endpoint management and continuous compliance
Syxsense is a unique network security tool that leverages patch management, vulnerability scanning, and endpoint protection in a single console, enabling your IT and security teams to proactively identify, assess, and remediate vulnerabilities across all endpoints, including desktops, laptops, servers, and mobile devices.
Pros
- Combines vulnerability scanning with endpoint patch management
- Offers automated remediation and workflow builder
Limitations
- Advanced reporting may require premium licensing
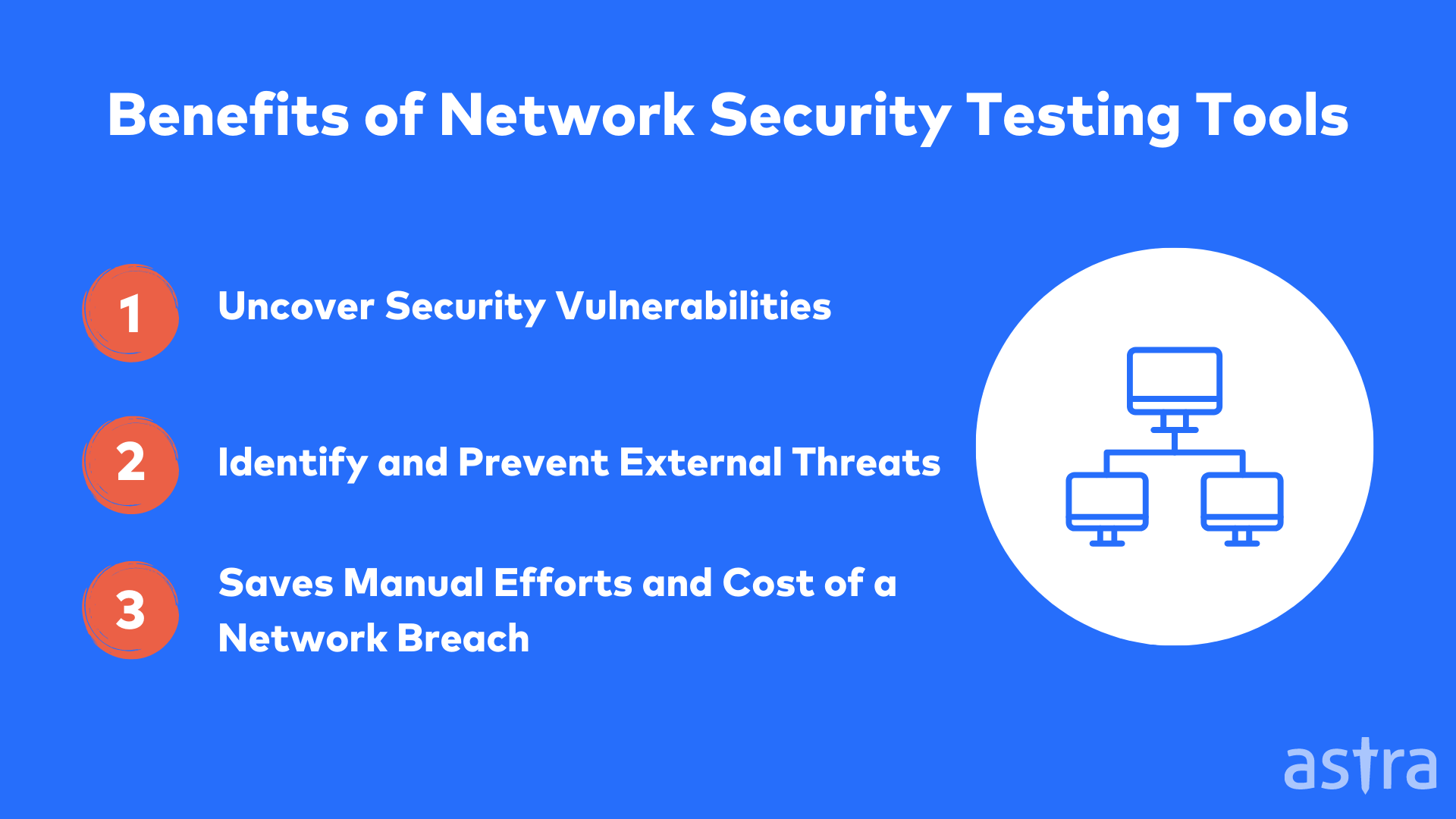
Benefits of Using Network Security Testing Tools
Network security testing tools are an essential part of an information security plan as they offer the following benefits:
- Expose critical weaknesses that could lead to costly breaches or compliance violations.
- Quantify risk to prioritize remediation where it has the highest business impact.
- Test defenses under realistic attack scenarios to reduce operational disruption.
- Optimize security investment by focusing on controls that materially reduce risk.
- Provide actionable metrics for stakeholders to justify security spending.
Simply put, investing in network security testing tools is a strategic decision as the insights gained translate directly into stronger defenses, more efficient resource allocation, and measurable reduction in potential financial and reputational losses.
5 Techniques used to Perform Network Security Testing
1. Network Scanning
The Network Scanner is a powerful tool for scanning a network and gathering information about it. The network scanning tool can monitor the network, identify hosts connected to it, and detect services running on the network, such as FTP, HTTP, POP3, and SMTP. The Network scanner also identifies the operating system running on the host and its version.
2. Vulnerability Scanning
Vulnerability scanning is a network security process that detects and analyzes flaws in computers and computer systems, reporting the findings to administrators. This information helps plan security patches or upgrades. It can also help in determining the security status of a network.
Vulnerability scanners have been around for a long time. Still, they have been made more effective by using sophisticated techniques, such as fuzzing, and they are now considered an essential tool in supporting compliance with regulatory standards.
3. Ethical Hacking
Ethical hacking is the practice of testing a computer system, network, or web application to find security weaknesses (holes) before a malicious hacker does. It is the surface area testing of a system, network, or web application. Ethical hacking aims to find security weaknesses before a malicious hacker does.
4. Password Cracking
Password cracking is of two types:
Dictionary Attack: This method uses a dictionary (a word list) to crack passwords. The word list has all the possible passwords. So the computer compares the password given by the user to the word list to find the matching password.
Brute Force Attack: This method uses an automatic program to crack passwords. The program tries all possible combinations of characters until it finds the correct password. A brute force attack is a time-consuming process.
5. Penetration Testing
Penetration testing evaluates computer security by simulating an active attack on a computer system or network. Network penetration testing services are typically performed by ethical hackers, also known as white-hat hackers, or by security professionals attempting to determine the extent of damage or risk before an actual attack.
Penetration testing differs from vulnerability scanning and compliance auditing in that its primary aim is to exploit potential vulnerabilities in a given target. In contrast, vulnerability scanning and compliance auditing are more passive forms of testing.
How much do Network Security Testing Tools Cost?
Network security testing tools can range from free open-source to $100,000, depending on the tools you are using, the number of networks you are scanning, and a lot more factors that are usually discussed before signing a contract.
A network security scan should be conducted at least twice a year to assess the network’s security and ensure it remains secure against potential threats. On average, the cost of a network security tool usually ranges from $500 to $2500 per network scan.
How to Choose Your Network Security Testing Tools?
With the numerous network security testing tools available, businesses face a bewildering array of choices when selecting the best network security testing solution. To help, we have prepared a list of key considerations to keep in mind when purchasing a network security testing tool.
1. Ease of use and Friendly UI
One of the critical factors for organizations to choose a network security testing tool is the ease of use. A simple interface and easy-to-follow instructions are always appreciated. Even the most advanced tools are rendered useless when the user does not know how to use them. A good tool will have an intuitive interface, clear step-by-step instructions, and a comprehensive user guide.
2. Comprehensive scan report
Understanding the threats to your business is crucial for effective risk management. A comprehensive security testing report is essential to keeping your business safe. A comprehensive security testing report can uncover high-risk vulnerabilities, help you better understand your network, and achieve compliance.
3. Updated with Latest Vulnerabilities
No automated security testing tool is perfect. Hackers are constantly finding and releasing new vulnerabilities. An automated network penetration testing tool should have an updated database of security vulnerabilities so that no vulnerability is left unnoticed.
Astra’s Pentest Solution: All-in-One Security Solution
Regardless of your company’s size, hiring a penetration testing company to protect your network and applications is crucial. Hiring a good pen testing solution will not only protect your business but also your data. Astra Security is an excellent solution for your business.
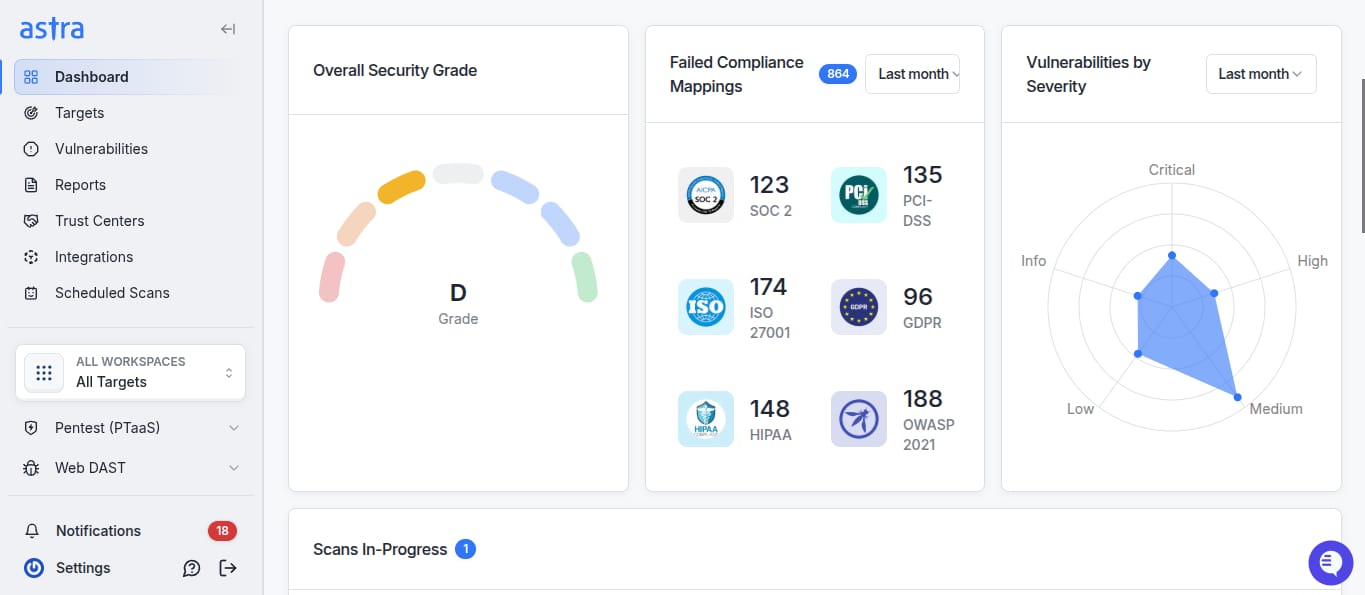
Astra Security has been in the industry for many years, offering multiple penetration testing solutions, including Network, Web, API, Mobile, Blockchain, and Cloud penetration testing.
The Astra Penetration Testing Solution is a next-gen penetration testing software used by thousands of organizations worldwide. Astra’s pentest solution is renowned for its comprehensive vulnerability scanner, featuring tests for over 8,000 CVEs in networks, making it an ideal choice.
Final Thoughts
Network security testing is a vital part of the information security management process. It involves testing the security of an organization’s network infrastructure, applications, systems, and services to find vulnerabilities that could be exploited by a malicious individual, hacker, or group.
Various organizations utilize network security testing tools to safeguard their networks against hackers. Secure your network too before it’s too late, get in touch with Astra today.
FAQ’s
1. What is Network Security Testing?
Network security testing identifies security vulnerabilities in the network by using software applications and tools designed to detect and protect the network from malicious attacks.
2. What are Network Security Testing Tools?
Network security testing tools are software solutions designed to identify, assess, and simulate vulnerabilities in networks. They help you detect potential threats, evaluate system defenses, and ensure robust protection by testing firewalls, protocols, configurations, and overall network resilience.
3. Is it legal to scan any Network for security risks?
The question about the legality of port scanning is quite frequent. The law is quite clear about it: you can not scan any network without the owner’s permission legally.
4. Can Astra help me with Network Security Testing?
Astra’s network security testing service is a top-notch way to improve your security, and we can even help you out if you’re just getting started. We have the tools and experience to find vulnerabilities and help you implement security to make sure your network stays safe. It’s time to get proactive and keep your business safe.
Additional Resources on Security Testing
This post is part of a series on Security Testing. You can
also check out other articles below.

- Chapter 1: What is Security Testing and Why is it Important?
- Chapter 2: Security Testing Methodologies
- Chapter 3: What is Web Application Security Testing?
- Chapter 4: How to Perform Mobile Application Security Testing
- Chapter 5: What is Cloud Security Testing?
- Chapter 6: What is API Security Testing?
- Chapter 7: What is Network Security Testing?
- Chapter 8: A Complete Guide to OWASP Security Testing?
- Chapter 9: What is DAST?
- Chapter 10: What is SAST?










