As businesses transition to cloud-based hosting, cybercrimes are on the rise. Consider the recent Jan’24 Trello data breach, which exposed the personal information of 15 million users. To combat such evolving threats, web application security testing is emerging as a critical line of defense.
Simply put, web app security testing is a controlled practice by security experts that mimics real-world hackers through VAPT to pinpoint bugs before the real hackers find them. But let’s take a deeper look.
What is Web App Security Testing?
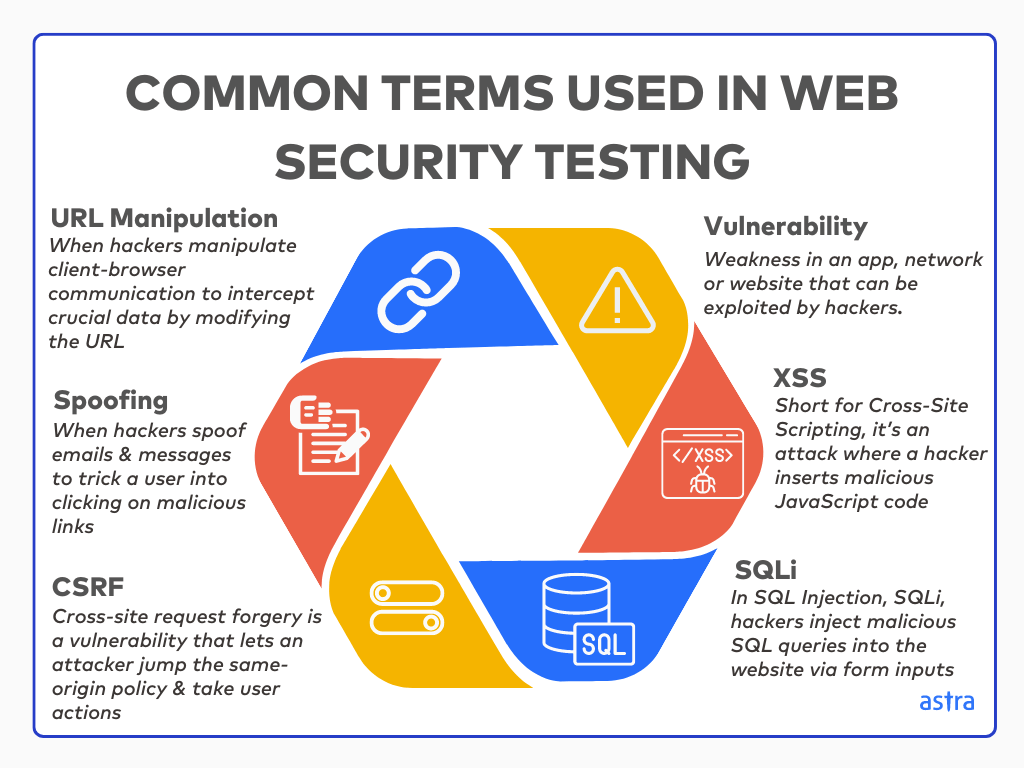
Web application security testing primarily helps identify vulnerabilities that could lead to data breaches, malware attacks, and access control issues, compromising its safety. The application’s code and architecture are analyzed to find vulnerabilities such as XSS, SQL injections, privilege escalation, broken access control, and more.
Conducted in two stages, automated scanning tools are first used to look for CVEs, followed by manual web app pentesting to identify business logic vulnerabilities and test real-world attack scenarios. Lastly, a detailed report provides detailed analysis and remediation guidance for flagged vulnerabilities.
Why Web App Security Testing is Non-Negotiable for You
1. Identify Vulnerabilities in Your Application
Web app security testing has emerged as a crucial step in the Software Development Life Cycle (SDLC), necessitating your developers to be more mindful of security when building applications.
Such a testing process helps identify vulnerabilities like SQL injection attacks or cross-site scripting (XSS) flaws preventatively to deliver a detailed analysis report with an exhaustive remediation plan to resolve the above and mitigate the risk of breaches,
2. Comply With Laws
Compliance regulatory bodies were established to implement laws regulating data security and privacy in web applications. Several countries have mandated web application security testing for different sectors (for example, HIPAA for healthcare-related businesses in the USA and PCI-DSS for payment gateways) to protect user data.
A business owner needs to conduct web app security testing for their application regularly to comply with the laws applicable to their industry and geography. Going beyond, they are equally crucial for developers who release web apps for public use on app distributor platforms or as SaaS (Software as a Service) products.
Secure your digital assets using web application penetration testing services designed to detect logic flaws, misconfigurations, and access gaps.
3. Analyze Your Security Posture
Web app security testing runs a litmus test on your current security measures and detects loopholes or gaps in your security system, such as misconfigured security settings, insecure coding practices, and improper access controls.
Security providers also test your firewalls because while it may be dedicated to protecting your web app, it can also have vulnerabilities. Testing helps you spot those weaknesses and fix them before they are exploited.
4. Detect Security Breaches & Behavior Anomalies Early
According to IBM, it takes companies 277 days to identify a data breach in their system. By this time, the damage inflicted could become irrevocable.
A huge benefit of conducting a web application security audit is that it helps you promptly identify security breaches or potential behavior anomalies in your application before they become extensive attacks. Early detection of such foreign activity can help you fight the attack proactively to prevent further damage.
5. Form an Effective Security Plan
Detailed outcomes of an audit can help you better plan and prioritize risk responses against a breach or a hack. Testing helps expose weaknesses in your incident response plan, such as a lack of clear communication protocols, the absence of security systems on every employee’s device, or slow notification procedures.
Thus, to ensure your web application is secure, compliant, and has an effective incident plan, here’s a comprehensive security testing checklist covering various aspects of your application’s security posture.
Web Application Security Testing Checklist
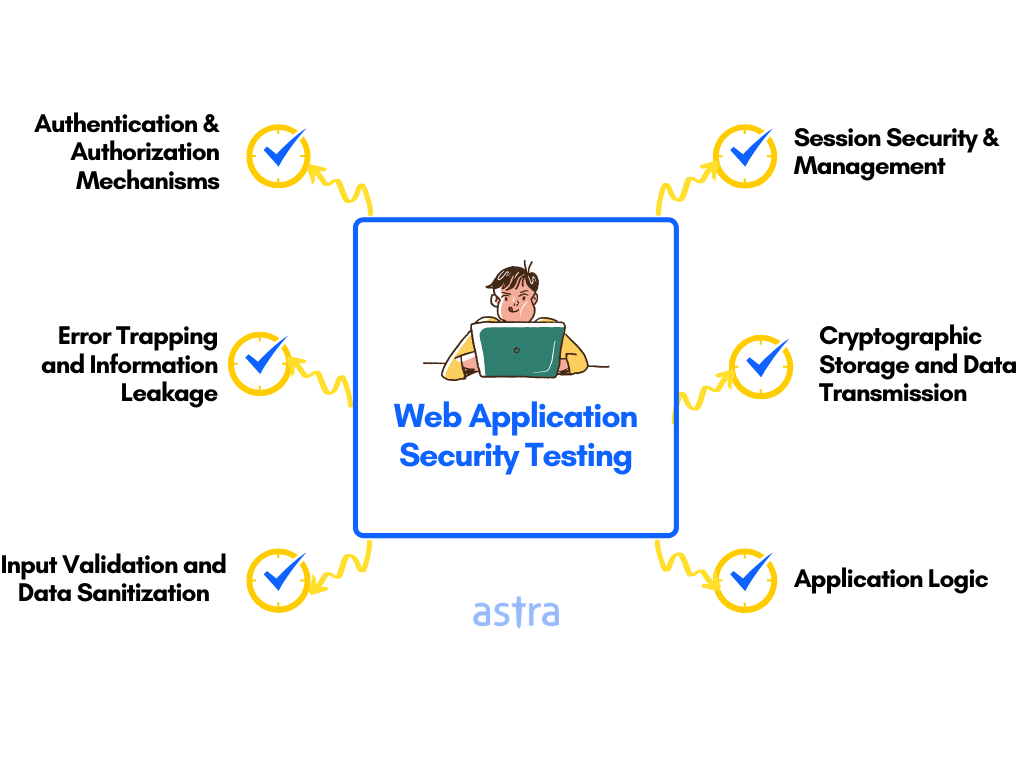
- Data Validation: Sanitize inputs to prevent SQL injection, cross-site scripting (XSS), and other attacks. Ensure all user inputs are properly validated to prevent malicious behavior and security risks.
- Data Protection: Encrypt data at rest and in transit and follow secure storage practices to protect sensitive data like passwords, credit card numbers, and personally identifiable information (PII).
- Error Handling: Proper error handling helps you avoid revealing sensitive information about your application. Error messages should be informative without disclosing system details that attackers can exploit.
- Communication Security: Establish secure communication channels between your application and users or other systems using encryption protocols like HTTPS/TLS to protect data in transit.
- Authentication: Validate user identities before granting access to sensitive information or functionalities by implementing authentication mechanisms like multi-factor authentication (MFA) and secure password hashing practices.
- Authorization: Use access controls based on the principle of least privilege, ensuring that users only have the minimum permissions necessary to perform their tasks.
- Session Management: Manage user sessions securely by setting timeouts and using strong, unpredictable session identifiers to prevent unauthorized session hijacking and other session-related attacks.

What Makes Astra the Best VAPT Solution?
- We’re the only company that combines automated & manual pentest to create a one-of-a-kind pentest platform.
- The Astra Vulnerability Scanner runs 10,000+ tests to uncover every single vulnerability
- Vetted scans ensure zero false positives.
- Our intelligent vulnerability scanner emulates hacker behavior & evolves with every pentest.
- Astra’s scanner helps you shift left by integrating with your CI/CD.
- Our platform helps you uncover, manage & fix vulnerabilities in one place.
- Trusted by the brands you trust like Agora, Spicejet, Muthoot, Dream11, etc.

Who Performs Web Application Security Testing?
You can hire a professional web application security testing expert to audit your application or have an in-house team regularly perform security testing using automated tools. If you’re a solopreneur or an app developer, you can independently perform preliminary web application security testing.
Note: Owing to the complex nature of security testing, there are too many ways one can falter. Hence, it is advised that you go with professional security testing for the best results and better protection of your app and its users.
Types of Web Application Security Testing
| Factors | Black-Box Penetration Testing | Gray-Box Penetration Testing | White-Box Penetration Testing |
|---|---|---|---|
| Intel of the target system | No intel. | Partial intel. | Complete intel. |
| Environment tested | Tests only the exposed environment. | Tests exposed & internal environments. | Thorough testing of all assets - external, internal, and code. |
| Depth of testing | Provides a surface-level view of security posture. | Fairly in-depth. | Very in-depth. |
| Guesswork | Consists of guesswork, and hit & miss sessions. | Very limited use of guesswork involved. | No guesswork involved. |
| Automation | Automation is heavily used. | Automation is used sparsely. | Automation is used only as an aid to the manual process. |
| Completion time | Unpredictable completion time. | Predictable. Takes several days to a couple of weeks to complete. | Predictable. Takes a couple of months to complete. |
| Cost | Is usually more affordable. | Costs lie between the two extremes. | Is costly. |
1. Black-Box Security Testing
In black box pentesting, our security experts emulate real-world hacker behavior that would be used to break into a system with limited knowledge of the target and publicly available information, such as URLs.
This testing relies heavily on automation, involves guesswork, can have unpredictable completion times, and only tests the target’s external surface. Nonetheless, it’s the most cost-effective method of the three.
2. White-Box Security Testing
White box security testers have complete system knowledge and thoroughly test internal and external assets, base code quality, API documentation, and designs. Through this method, the pentest can identify even remotely located vulnerabilities.
This in-depth testing method involves no guesswork and only uses automation to aid the manual process. It features a predictable completion time but can be the most expensive of the three testing methods.
3. Gray-Box Security Testing
With gray-box security testing, the tester has limited system knowledge of the infrastructure, internal codebase, and architecture. The testing is conducted on both the internal and external environments. The limited information provides the tester with a more focused area of attack and thus avoids any trial-and-error method of attack.
Gray box testing uses very little guesswork and sparse automation. Regarding cost and timelines, this type of testing falls in the mid-range of the three.
But is such a grey-box web app security test different from a grey-box web app pentest? Let’s take a look.
Difference Between Web Application Security Testing & Web Application Penetration Testing
| Feature | Web Application Security Testing (WAST) | Web Application Penetration Testing (Pen Testing) |
|---|---|---|
| Depth | Less deep, focuses on application logic and common vulnerabilities | Highly comprehensive, tests application logic, underlying infrastructure (servers, cloud), and external APIs |
| Scope | Narrower and focuses primarily on the web application itself | Wider, can encompass servers, cloud infrastructure, and external APIs |
| Frequency | It can be automated and run frequently | Requires manual intervention by security professionals, making it less frequent |
| Cost | More cost-effective, often automated | More expensive due to the manual effort involved |
Astra Pentest is built by the team of experts that helped secure Microsoft, Adobe, Facebook, and Buffer

How Can You Manually Perform Web Application Security Testing?
1. Asset discovery: Identify your application’s security areas and the complementary assets included in the testing. Open ports and important user information, such as admin emails and S2 bucket URLs, are a few findings from the asset discovery stage.
Ideally, by the end of this phase, you should have a map of all the assets related to the web app.
Tools used: Nmap, OWASP Amass
2. Check for outdated versions: Verify if your application is up to date and repeat with other assets. Assets discovered during the previous stage can be a goldmine of possible vulnerabilities through which the web application can be exploited.
The first step is to check for known CVEs for the assets discovered. Companies often use old versions of open-source libraries, which may not have an updated list of current CVEs. Tools like CVE Bin can help identify this gap.
Tools used: Astra Pentest, Nessus, Nmap, OWASP Dependency-Check
3. Check permissions: Ensure your app follows secure user permission and role rules. In this phase, a thorough check should be done to highlight broken access control, an OWASP Top 10 vulnerability. In the context of web app security testing, broken access control can be of two types: horizontal and vertical.
Horizontal refers to when one user can access the data of another user, and vertical broken access control is when a basic privileged user can access the information available to an admin-privileged user.
4. Check security protocols: Check if security measures, such as a firewall, malware scanner, SSL, etc, are in place. This is especially important for the underlying encryption libraries, such as OpenSSL.
In November 2022, two high-severity vulnerabilities (CVE-2022-3602 and CVE-2022-3786) were discovered in OpenSSL. While not as widespread as the infamous Heartbleed bug, these vulnerabilities could allow attackers to control systems using specially crafted certificates.
A successful attack could have resulted in stolen data, disrupted operations, or even complete system compromise.
Tools used: TestSSL, SSL Labs
5. Analyze code rigidity with a penetration test: Analyze your code for CVEs, code injection, SQLi, and other common attacks (this would require more hands-on experience with security testing).
In this stage, human pentesters emulate hacker behavior by attempting to breach a system using a combination of all the vulnerabilities mentioned above, such as broken access control, outdated versions, improper security protocols, and XSS attacks.
Tools used: Astra Pentest, Burp Suite, OWASP ZAP
6. Test database security: Check if your database is hardened against malicious SQL queries. If an attacker discovers a weak point in your login system, they might try injecting malicious code into the login form to trick the database into revealing usernames and passwords.
By simulating these attacks (without harming your data), you can identify vulnerabilities and implement safeguards to prevent them.
Tools used: Astra Pentest, SQLMap, Ghauri, SQLninja
7. Run configuration tests: Check your application and network’s configuration structure and determine if they are secure by reviewing key security settings such as network segmentation, firewalls, and essential permissions.
Analyze your web server software’s settings, verifying that only essential features are enabled and security headers are properly configured.
Assess your operating system’s configuration for unnecessary services, strong privileged account passwords, and up-to-date security patches. Finally, reviewing your network setup is important to ensure that only authorized devices can access your application and that sensitive data travels over encrypted connections.
Tools used: Nessus
8. Business logic: Check your application for vulnerabilities in terms of design and implementation. You should examine how the application processes and validates user input, enforces authorization rules and handles sensitive data.
Tools like Burp Suite or OWASP ZAP can intercept and analyze application traffic, helping identify potential logic flaws.
Tools used: Burp Suite, OWASP ZAP
9. Client-side logic: Check if the JavaScript loading on browser web pages follows the correct rule. Look for issues like improper input validation (e.g., not sanitizing user input before displaying it) and insecure DOM manipulation techniques.
Tools used: Burp Suite, XSStrike
10. Input validation: When accepting user data on your web app, check if input validation is in place. Verify that your application properly validates all user input to prevent attackers from injecting malicious code or data by validating data types, lengths, and formats.
Tools used: Burp Suite
11. Authentication & session management: Check authentication rules and ensure that session management is not vulnerable. Assess the strength of your authentication mechanisms (e.g., login protocols) and session management practices.
In this phase, you should implement strong password hashing algorithms, enforce complex password requirements (characters used, length), implement 2FA, and use secure session cookies. You should also check if appropriate session timeouts have been established to prevent unauthorized use after a period of inactivity.
Tools used: Burp Suite, OWASP ZAP
12. Configuration: Verify that your web application configuration files and settings are secure. Disable unnecessary functionalities in your web server, enable essential security headers and disable unused services in your operating system.
Tools used: Nikto, Burp Suite
13. Authorization check: Analyze if your application enforces proper authorization rules to prevent unauthorized access to sensitive functionalities and data. Verify that users can only access resources and perform actions based on their assigned permissions.
Tools used: Burp Suite, OWASP ZAP
Testing Methodology for Web Application Security Testing
Phase I: Initiation
The initiation phase begins by defining the scope of testing for an application and documenting initial testing requirements. This involves clearly outlining which parts of the application will be tested and which won’t.
Our security expert then develops an ongoing testing and scanning schedule, ensuring the process continuously evolves to catch the latest zero-day vulnerabilities.
After this, they analyze the implemented functionalities in an application, get a sample of browser-server traffic flow, and finalize the format of testing deliverables.
Phase II: Evaluation
With a solid plan, the evaluation phase examines the application’s security posture. The process starts with static code analysis, which helps uncover potential security weaknesses within the application’s code.
Then, server infrastructure testing is conducted as part of the DevOps cycle, ensuring security is prioritized in the development process. Our experts look for business logic vulnerabilities and complete authorization checks for user access.
You can then schedule manual and automated tests using different tools – either commercial or open-source.
Phase III: Discovery
The discovery phase focuses on actively exploiting vulnerabilities. Dynamic analysis tools simulate attacks to probe for exploitable security loopholes. Pentesters also conduct manual penetration tests, emulating hacker behavior.
Industry-specific scenarios are then explored, such as payment manipulation testing and testing for known CVEs (Common Vulnerabilities and Exposures) to determine whether the application is susceptible to publicly documented vulnerabilities.
Technology-specific attack vectors and payloads are also tested. The testers then verify the findings and examine potential vulnerabilities to eliminate false positives. This phase also involves collecting screenshots and logs or creating video proofs-of-concept (POCs) to demonstrate each vulnerability’s exploitability.
Phase IV: Reporting
The reporting phase turns the raw findings from the discovery phase into actionable insights. The first step involves determining the ease of exploiting each vulnerability and prioritizing remediation efforts, focusing on the most critical issues.
This report, which includes detailed documentation of the app’s vulnerabilities, should be clear, concise, and easy to understand for both technical and non-technical audiences. It should provide a comprehensive overview of each vulnerability, including its location, potential impact, and steps to reproduce it.
The above also includes a remediation plan for fixing the identified vulnerabilities, after which you are advised to conduct an independent quality review. Depending on the service provider, you will then be issued a pentest certificate and a plan on how often rescans are needed to prevent vulnerabilities from arising.
Web App Security Testing Tools
Top 3 Vulnerability Assessment Tools For Security Experts
| Features | Astra Pentest | Wireshark | Burp Suite Professional |
|---|---|---|---|
| Scanner Capacity | Run 9300+ automated tests on web applications and API | Vulnerability detection, deep packet inspection, and traffic analysis for networks | Scan for over 2500+ test cases in web apps and APIs |
| Accuracy | Zero False Positives Assured (Vetted Scans) | False positives present | False positives present |
| Vulnerability Management | Custom detailed reports with remediation assistance and PoC videos | No | Yes |
| Continuous Monitoring | Yes | No | Yes |
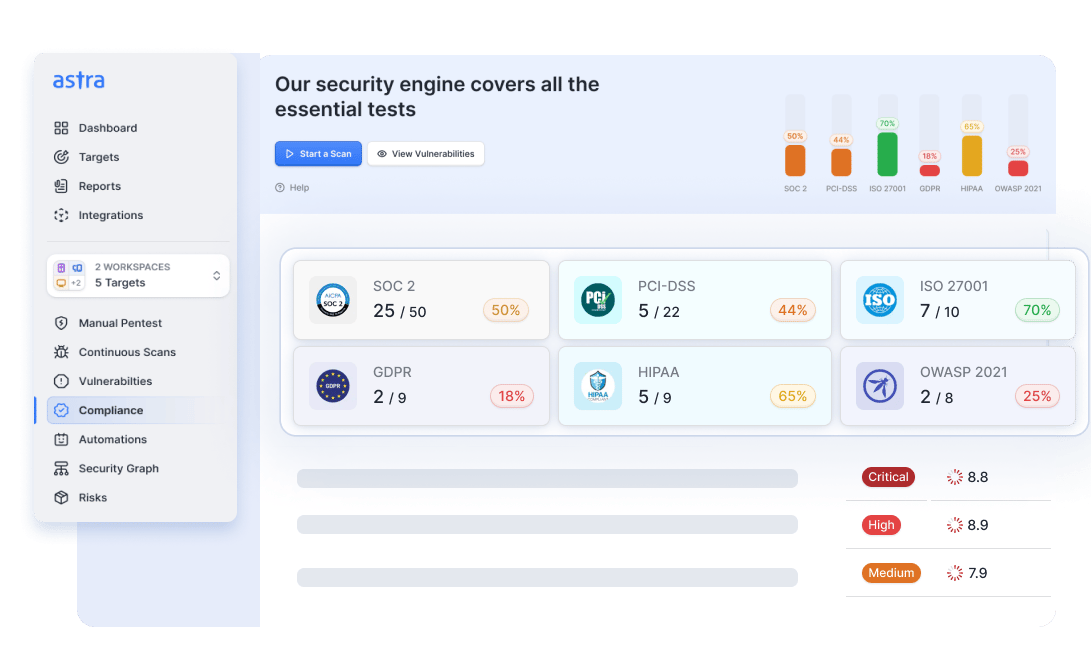
| Compliance Scanning | OWASP, SANS25, GDPR, PCI-DSS, HIPAA, ISO27001, and SOC2 | None | PCI-DSS, HIPAA, and GDPR |
| Integrations | GitHub, GitLab, Jenkins, JIRA, CI Circle, and Slack | None | Slack, JIRA, Jenkins, GitLab, and more |
| Price | Starts at $1999/yr | Open-source tool | $449/yr/user |
Astra’s Pentest Solution
Key Features:
- Platform: SaaS
- Pentest Capabilities: Continuous automated scans with 10,000+ tests and manual pentests
- Accuracy: Zero false positives (with vetted scans)
- Compliance Scanning: OWASP, PCI-DSS, HIPAA, ISO27001, and SOC2
- Expert Remediation Assistance: Yes
- Customizable Reports: Yes
- Publicly Verifiable Pentest Certification: Yes
- Workflow Integration: Slack, JIRA, GitHub, GitLab, Jenkins, and more
- Price: Starting at $1999/yr
Astra Security is a web app security testing provider that offers round-the-clock vulnerability assessment and penetration testing (VAPT) services. We incorporate both automatic and human techniques to identify vulnerabilities. We also provide VAPT for networks, mobile apps, APIs, and cloud infrastructures.
Astra’s vulnerability scanner runs over 10,000 tests to detect zero-day vulnerabilities, including security control checks, static and dynamic code analysis, configuration tests, server infrastructure testing, DevOps, and business logic testing.
We add new tests to its list every two weeks. Our CXO-friendly dashboard allows direct platform interaction with development teams and provides continuous vulnerability tracking.
Make your Web Application the safest place on the Internet.
With our detailed and specially
curated Web security checklist.

Final Thoughts
Web applications are the backbone of many businesses but are also vulnerable to attacks. As such, web app security testing protects you against vulnerabilities like XSS and SQL injections, configuration flaws, privilege escalation, and insecure file uploads.
By continuously testing your application’s code and functionalities, you can identify such CVEs before hackers exploit them preventively. This helps you maintain a good security posture and protects your application, users’ data, and business reputation.
To help you take advantage of the multiple benefits, including compliance, we’ve also provided a detailed guide to manually performing a pentesting and a checklist to help you protect your application preliminarily.
FAQs
1. What is the timeline for web application security testing?
Web application security testing takes 7-10 days. However, the vulnerabilities start appearing on your Astra security audit dashboard on the third day, so you can start working on the fix.
2. How much does security testing cost?
Security testing for web applications costs between $1999 and $10000 annually, depending on the testing service provider, the number of scans included, and whether it only uses automation or includes manual testing.
3. What is a web application security test?
Web application security testing helps identify vulnerabilities that could lead to data breaches, malware attacks, and access control issues, compromising safety. The application’s code is analyzed to find vulnerabilities like XSS, SQL injections, privilege escalation, broken access control, and more.
4. What are the three types of web application testing?
The three types of web app testing are black box, gray box, and white box testing. Black box tests are conducted blindly with only publicly available information, gray box tests with some target information, and in a white box test, the tester goes very in-depth and knows all the details about the target.
Additional Resources on Security Testing
This post is part of a series on Security Testing. You can
also check out other articles below.

- Chapter 1: What is Security Testing and Why is it Important?
- Chapter 2: Security Testing Methodologies
- Chapter 3: What is Web Application Security Testing?
- Chapter 4: How to Perform Mobile Application Security Testing
- Chapter 5: What is Cloud Security Testing?
- Chapter 6: What is API Security Testing?
- Chapter 7: What is Network Security Testing?
- Chapter 8: A Complete Guide to OWASP Security Testing?
- Chapter 9: What is DAST?
- Chapter 10: What is SAST?