In today’s technology-advanced era, many of us know that cloud computing has become an important part of every organization’s IT strategy. Over the past decade, the adoption of cloud has increased immensely. Today, there are many large and small cloud vendors fighting against each other to offer their cloud offerings to worldwide organizations.
When looking at the cloud providers, AWS is the name that comes up first due to its highest (33%) market share in the industry. Amazon Web Services (AWS) offers a set of remote computing services that make up an on-demand distributed computing platform. It is designed to make web-scale computing easier for online businesses. Considering the security aspect of AWS, many security-conscious organizations are taking AWS security measures to make sure their business is safe from today’s highly-skilled cybercriminals.
AWS security of the cloud has become a much-needed practice to keep the cloud infrastructure secure from hackers. A comprehensive AWS penetration testing and its well-written reporting(AWS Penetration Testing Report) can help organizations understand security vulnerabilities in the cloud infrastructure and fix them before a hacker can exploit them.
Introduction to AWS
AWS provides a broad set of global computing, storage, database, analytics, application, and other services. These services help organizations move faster, lower IT costs, and scale applications.
The AWS services include hosted servers (Amazon EC2), database services (Amazon RDS), content delivery (Amazon CloudFront), a service for deploying software applications and platform services (Amazon S3), and other services. It supports software as a service (SaaS), platform as a service (PaaS), and infrastructure as a service (IaaS) models.
The AWS Cloud is a very secure environment. But the fact remains that the cloud is a shared environment, and you must take the proper precautions to help mitigate the risks of utilizing a cloud environment.
What is AWS Security?
AWS Security refers to a range of configurations, tools, or features that make the public cloud service provider Amazon Web Services (AWS) secure. The term is generally used to refer to the security provided at the data center level instead of security at the individual account level. Amazon and not the individual users manage the AWS security controls.
Also Read: SaaS Security Management- A Complete Guide To 6 Best Security Practices
Some of the AWS security tools offered by Amazon are:
1. AWS Inspector
AWS Inspector evaluates the security of applications by reviewing server-side configurations and then testing the live instances for compliance with AWS security best practices.
Inspector performs a wide range of security checks against your applications and infrastructure and provides you with detailed reports about your AWS resources. Security checks include AWS resource inventory checks for EC2 instances, VPCs, IAM users and groups, and IAM policies. Compliance checks for controlling access to AWS resources. AWS best practices checks that ensure that you are following AWS security and compliance best practices.
2. AWS Security Hub
AWS Security Hub is a cloud security posture management service that automates best practice checks, aggregates alerts, and supports automated remediation. The service provides centralized visibility into the security state of your AWS resources and helps you mitigate risks quickly.
One can use AWS Security Hub to monitor and manage multiple accounts, including cross-account access and resources. AWS Security Hub is managed entirely through the AWS Management Console and supports integrations with your existing monitoring tools.
Also Read: API Penetration Testing: What You Need To Know
3. AWS Macie
Amazon Macie helps you discover, classify and protect sensitive data in Amazon S3, Amazon EBS, Amazon Glacier, Amazon Redshift, Amazon Athena, Amazon WorkSpaces, and Amazon Elasticsearch Service. It provides you with a detailed audit trail of data access activity and allows you to control access to data.
What is AWS Penetration Testing?
A proper penetration test in the cloud is a thorough evaluation of the security of a cloud environment. AWS offers a penetration test service for User-Operated Services, including cloud offerings created and configured by the user. This service provides organizations with a better understanding of the security of their AWS resources.
Reading Guide: Complete Guide on AWS Security Audit | 5 Best Cloud Security Companies: Features Offered And Factors To Consider
Does AWS allow Penetration Testing?
In a word: Yes! Or, at least most of the time. However, there are specific boundaries to what an AWS ethical hacker can play with while the rest remains out of bounds for pen-testing.
AWS allows penetration testing on the following resources only:
- Amazon EC2 instances, NAT Gateways, and Elastic Load Balancers
- Amazon RDS
- Amazon CloudFront
- Amazon Aurora
- Amazon API Gateways
- AWS Lambda and Lambda Edge functions
- Amazon Lightsail resources
- Amazon Elastic Beanstalk environments
Learn more about what all is included in the scope of AWS penetration testing.
List of AWS controls to be Audited for Security
1. Governance
- Understand AWS usage/implementation
- Identify assets & define AWS boundaries
- Access policies
- Identify, review & evaluate risks
- Documentation and Inventory
- Add AWS to risk assessment
- IT security & program policy
2. Network Management
- Network Security Controls
- Physical links
- Granting & revoking accesses
- Environment Isolation
- Documentation and Inventory
- DDoS layered defence
- Malicious code controls
3. Encryption Control
- AWS Console access
- AWS API access
- IPSec Tunnels
- SSL Key Mangement
- Protect PINs at rest
4. Logging & Monitoring
- Centralized log storage
- Review policies for ‘adequacy’
- Review IAM credentials report
- Aggregate from multiple sources
- Intrusion detection & response
What is an AWS Penetration Testing Report?
AWS Penetration Testing Report is the outcome of penetration testing performed on the AWS environment, done by penetration testers. It is written in the format of a report which includes all the findings of the penetration testing performed so that the management or the clients can take corrective actions to patch vulnerabilities on time.
AWS Penetration Testing Report is an in-depth review of your critical AWS infrastructure with actionable recommendations for improvement. It includes a full review of your account configuration and security settings, detailed scan results, and a summary of findings, including an extensive POC (Proof of Concept) for each finding.
The report is based on the findings in your AWS account, and it includes recommendations for improvement. The report is delivered in PDF, HTML, and email formats.
Also Read: Sample Penetration Testing Report
Importance of AWS Penetration Testing Report
AWS penetration testing report is a comprehensive report that gives you a complete overview of vulnerabilities with a POC (Proof of Concept) and remediation to fix those vulnerabilities on priority.
An AWS penetration testing report contains all the findings in a well-organized, easy-to-understand format. The AWS penetration report is created in a way that will help you or your organization in fixing the found vulnerabilities in the AWS environment.
The AWS penetration testing report will highlight any way in which an attacker could gain access to your AWS environment. It also provides you with a ranking of the found vulnerabilities that will help you prioritize. The AWS penetration testing report highlights the vulnerabilities that are present in your AWS environment and gives you ways to fix them.
AWS penetration testing report will enable you to understand the security posture of your AWS environment and help you prioritize vulnerabilities that need to be addressed with a penetration test.
An AWS penetration testing report is a great way to prove to your auditors that you have taken security seriously. It can be a great document to demonstrate your compliance with the EPA, PCI, SOX, etc.
Also Read: Cloud Penetration Testing: A Complete Guide

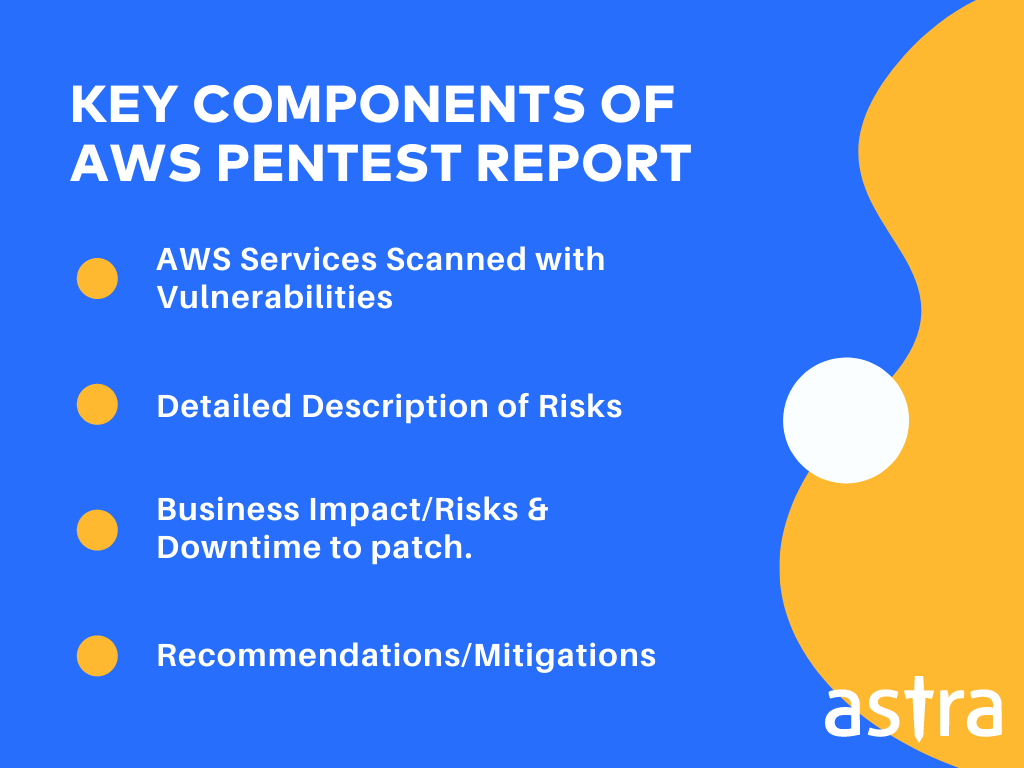
What’s inside a perfect AWS Penetration Testing Report?
A penetration testing service report should be clear and precise so that anyone can read and understand the security posture of the cloud infrastructure. The AWS penetration testing report is a critical document, a result of a penetration test, a set of notes, and questions to be answered.
The penetration testing report helps to answer questions for a security team to improve the security posture of an AWS Cloud infrastructure.
Here are a few things that should be inside the AWS penetration testing report:
1. AWS services scanned with vulnerabilities
2. Detailed description of each vulnerability
3. Severity & CVSS score
4. Business Impact
5. Downtime to fix the risk
6. Steps to fix the vulnerability
Who prepares the AWS Penetration Testing Report?
An AWS penetration testing report is prepared by a team of penetration testers who do the work. There is a lot of work involved in a penetration test, and it takes a very specific skill set to do this job well.
Interestingly, the AWS penetration testing report will be written by a completely different person than the testers. This is because an AWS penetration testing report is a document that a variety of different audiences will understand. These could include the client, the client’s team, management, or even the client’s lawyers.
Regardless of the audience, the report needs to be clear and easy to understand for anyone who reads it. The report will also be used as a reference for future testing, so it must be written in a very clear and easy to follow.
Astra’s AWS Penetration Testing Solution
Cyber Security is one of the biggest worries for organizations today. With the massive adoption of cloud infrastructure and the growing usage of cloud-based services, it is important to keep your cloud infrastructure secure.
Astra is a cyber security company that offers a cloud-based security testing solution that provides a full spectrum of threat simulation capabilities that can be used to test security controls across the entire AWS platform. The solution delivers the next generation of cloud security testing, providing a wide variety of attack vectors, an inherent AWS knowledge base, and a range of customizable attack types to mimic the actions of the most sophisticated adversaries.
Astra’s AWS Penetration Testing Solution has been designed to merge the best practices of penetration testing and red team exercises. It can cover the full life-cycle of the penetration testing process, from initial preparation for the assessment, through assessment preparation to the final report.

Checkout Astra’s AWS Security Audit and Penetration Testing Checklist
Conclusion
The security of the Amazon Web Services (AWS) cloud environment is a top concern for enterprises, jumping at the chance to migrate their IT infrastructure to the cloud. However, many are getting frustrated when they find that their AWS security posture is not what they expected. The big question is: How can you be sure that your AWS cloud environment is secure? The good news is that AWS penetration testing can help you determine your security posture.
AWS penetration testing is a critical task in the securing cloud infrastructure. We know that you don’t like to spend time and effort on security tasks, and we’re ready to help. Our team has extensive experience in the cloud security, and we’re here to help you with any security problems, no matter how complex they may be. We’re also here to provide you with a detailed report to help you understand your risks and how to fix them.
















