SaaS applications comprise 70% of a company’s software usage, and this figure is projected to be 85% by 2025. The average number of SaaS applications used by an organization stood at 80 last year.
We can imagine the importance of Software as a Service in terms of functionality and business success—it’s no wonder the SaaS industry has grown by 500% over the last seven years.
With this rapid growth, the demand for reliable cyber security SaaS companies has surged, ensuring that businesses can scale without compromising security.
However, in a 2019 survey of SaaS users, 93% of the respondents expressed concerns about the security of their data when it is stored with SaaS providers. As a SaaS provider, you can address this issue by partnering with top SaaS security companies that specialize in protecting cloud applications from data breaches and other threats.
What is SaaS Security?
SaaS Security involves practices and policies to protect users’ data privacy in subscription-based cloud applications. It ensures data confidentiality by restricting access to sensitive information like customer and financial data. It also maintains data integrity by preventing unauthorized changes and guarantees data availability by protecting against disruptions.
Access control features such as multi-factor authentication (MFA) and role-based access control (RBAC) are vital to restrict data and function access. SaaS security providers use advanced threat detection tools and develop incident response plans to minimize damage during breaches.
Despite handling sensitive data, many SaaS providers lack adequate security, making strong SaaS security essential as usage grows.

What Makes Astra the Best VAPT Solution?
- We’re the only company that combines automated & manual pentest to create a one-of-a-kind pentest platform.
- The Astra Vulnerability Scanner runs 10,000+ tests to uncover every single vulnerability
- Vetted scans ensure zero false positives.
- Our intelligent vulnerability scanner emulates hacker behavior & evolves with every pentest.
- Astra’s scanner helps you shift left by integrating with your CI/CD.
- Our platform helps you uncover, manage & fix vulnerabilities in one place.
- Trusted by the brands you trust like Agora, Spicejet, Muthoot, Dream11, etc.

Comparison of Top SaaS Security Companies Around the Globe
| SaaS Security Companies | Product/Service Offerings | Key Features |
|---|---|---|
| Astra Security | Vulnerability Assessment and Penetration Testing, Compliance Monitoring, Remediation Support | Continuous Testing, CI/CD Integration, Authenticated Scans, Manual Pentest with 0 False Positives, Vulnerability Management Dashboard |
| Cipher | Managed Detection and Response, Red Teaming, Compliance | Holistic risk management platform, highly certified, global presence |
| Intruder | Internal and External Vulnerability Scanning, Penetration Testing, Cloud Vulnerability Scanning | Attack surface monitoring, Slack and Jira integration, continuous penetration testing |
| Fidelis | Incident Response, Network Security, Data Loss Prevention, Vulnerability Management | Cloud security compliance, integrated cloud security platform |
| Tenable | Application Security, Cloud Security, Compliance, Vulnerability Management | Reduced remediation time, DevSecOps enablement |
| Symantec | Endpoint Security, Information Security, Network Security | Integrated cyber defense index, coordinated security across cloud and on-premise assets |
| Acunetix | Vulnerability Scanning, Remediation Support. | Scans for more than 7000 vulnerabilities including zero-day. |
| HackerOne | Continuous Security Testing, Triage, Attack Resistance Management | Keen use of hacker insights, cloud protection against multiple attack vectors |
| Indusface | Web App Scanning, Mobile App Scanning | Business logic checks, malware monitoring, and blacklisting detection, zero false positives. |
| 4Armed | Application Pentesting, PCI-DSS Compliance, Security Migration | Team of qualified hackers, continuous security improvement cycle for users. |
10 Best SaaS Security Companies
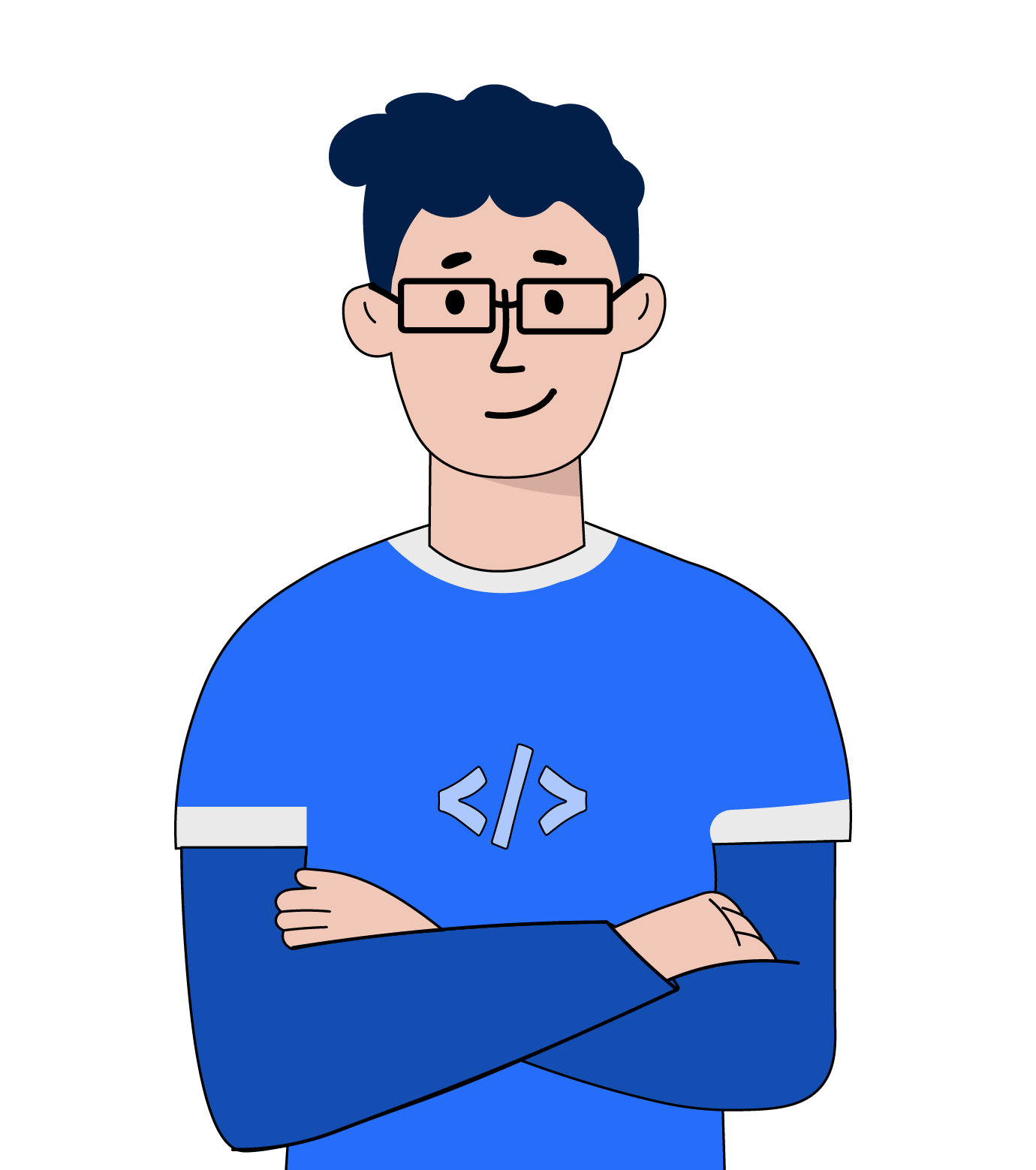
1. Astra Security
- Scanner Capabilities: Web and Mobile Applications, Cloud Infrastructure, API, and Networks
- Accuracy: Zero False Positives Assured (Vetted Scans)
- Scan Behind Logins: Yes
- Compliance: PCI-DSS, HIPAA, SOC2, and ISO 27001
- Integrations: Slack, Jira, GitHub, GitLab
- Expert Remediation: Yes
- Deployment: SaaS
- Pricing: Starts at $199/month
- Rating on G2: 4.6 out of 5
Built on standards like OWASP, NIST, and SANS25, Astra vulnerability scanner runs over 10,000+ tests to find new, emerging, and existing vulnerabilities in different types of assets, including mobile apps, web apps, cloud infrastructure, APIs, etc.
Astra Security offers a pentest suite that combines the automated vulnerability scanner with manual penetration testing solutions for SaaS applications. It also includes an intuitive vulnerability management dashboard that allows users to monitor and assign vulnerabilities.
You can integrate the pentest tool with your CI/CD pipeline to ensure automatic scanning of all application updates. The vulnerability scans take place in the cloud, thus putting zero pressure on your servers. Astra is one of the leading cyber security SaaS companies, trusted by businesses globally to secure their SaaS environments effectively..

2. Cipher
Cipher, a cloud security company, is currently part of Prosegur, a publicly traded private security company with operations in 26 countries. Cipher’s team of security experts provides risk assessments, data governance, incident response management, and compliance services.
Cipher also offers a red-teaming solution, providing vulnerability assessment, ethical hacking, and penetration testing.
3. Intruder

Intruder is an online vulnerability scanner designed to test digital infrastructures for security vulnerabilities. Intruder helps you evaluate security risks in endpoint devices, web servers, and the cloud.
Intruder offers solutions like:
- Internal and external vulnerability scanning.
- Continuous penetration testing.
They also help you attain compliance with SOC2 and ISO 27001.
Dive into how top Intruder.io alternatives and competitors stack up in terms of detection accuracy, asset discovery and compliance support
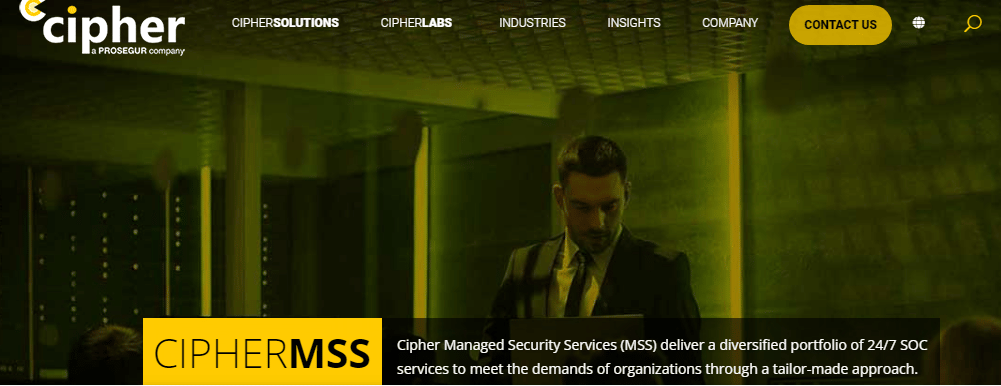
4. Fidelis
Fidelis has acquired CloudPassage, one of the leading cloud security service providers, and integrated its offerings. Fidelis has a robust application security platform, which is especially suitable for cloud-hosted applications.
The cloud security platform by Fidelis is called Cloudsecure, and it is focused on:
- Fast detection and inventory of assets.
- Detection of security compliance risks and malicious activity.
- Quick remediation for reduced exposure.
Fidelis stresses quick and accurate remediation of security vulnerabilities, a quality that makes it one of the top five SaaS security companies.
5. Tenable
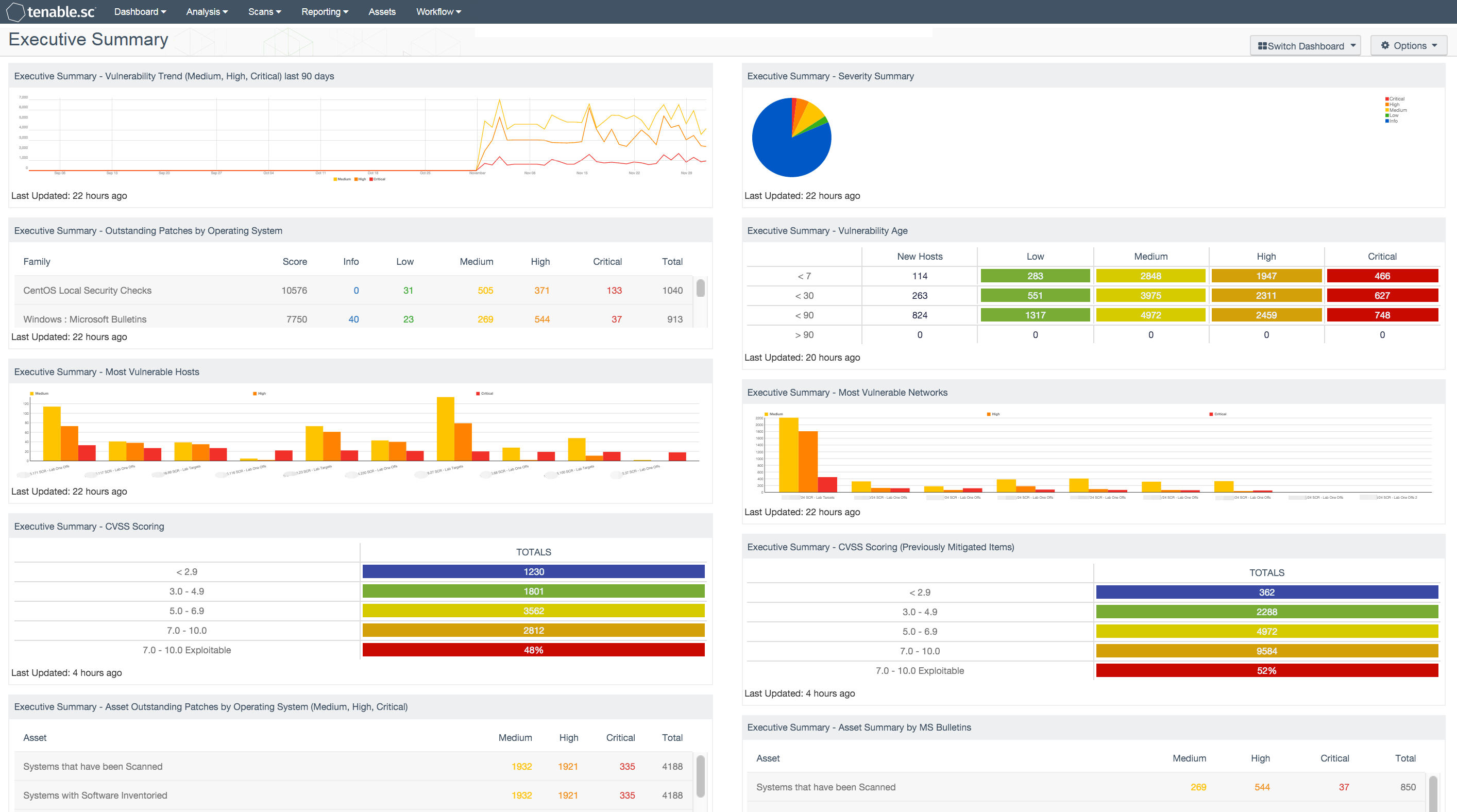
Tenable is a vital contributor to cybersecurity development. Although it is not entirely focused on SaaS security, it offers a fair contribution.
Tenable’s vulnerability assessment tool is Nessus, widely used for scanning applications for security loopholes. Nessus automatically scans for vulnerabilities whenever software is updated, or a new plugin is added.
Discover how leading Tenable alternatives stack up in terms of reporting depth, integrations, and enterprise readiness.
6. Symantec

Symantec identifies and tackles emerging threats, helping companies comply with regulations while minimizing the risks in a SaaS environment. It uses artificial intelligence to contextualize threat data and provide better security insights for its users.
Symantec’s offerings include:
- Endpoint Security
- Identity Security
- Information Security
- Network Security
It integrates easily with other third-party products and helps you coordinate security for different asset types. It is one of the top cloud security companies.
7. Acunetix

Acunetix offers a powerful vulnerability scanner for web applications. Given its speed and scalability, it is a well-suited SaaS security solution.
Acunetix’s vulnerability scanner scans for 7000+ vulnerabilities and categorizes them according to severity, helping you prioritize remediation efforts.
- It covers the OWASP top 10.
- Scans for SQL injection and XSS.
- Detects out-of-band vulnerabilities.
- Detects exposed databases and security misconfigurations.
8. HackerOne
This cybersecurity platform is based on the philosophy that security solutions must tap into the knowledge of top-notch hackers to stop malicious hackers from ruining your business.
- They provide a platform for perpetual testing of your product.
- They uncover critical vulnerabilities that other tools miss.
- HackerOne offers vulnerability assessment and remediation of your cloud assets.
9. Indusface
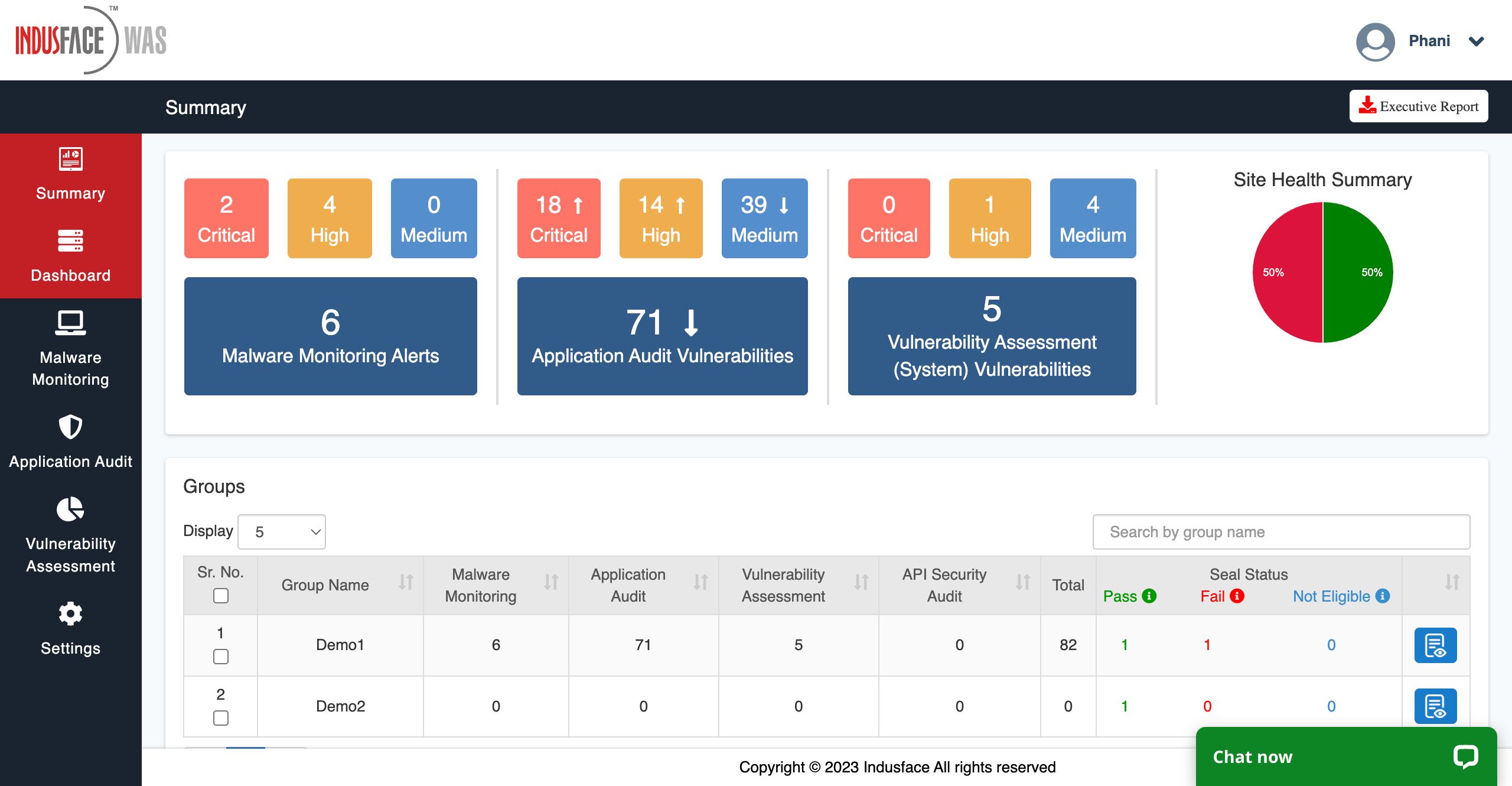
Indusface offers a web application firewall (WAF) called AppTrana for SaaS providers and users. It is designed for cloud security.
- AppTrana is easy to set up.
- It helps you control bot activity.
- Creates a multilayered defense strategy for your app.
- Identifies a wide range of threats
- Quick response to zero-day vulnerabilities.
10. 4Armed
4Armed is focused on creating cloud-based security solutions for cloud-native applications. Their offerings include:
- Application penetration testing.
- Secure migration to the cloud.
- Deployment of code using DevSecOps.
- PCI-DSS compliance.
On top of these, they also offer vulnerability scanning and SaaS penetration testing services.
Best Practices for Maintaining SaaS Safety
1. Understanding the Shared Responsibility Model
Most cloud services employ the shared responsibility model; in the same way, all SaaS apps should do the same. This approach divides data security into two parts: the user is responsible for protecting their data, and the SaaS app secures the infrastructure.
2. The Importance of Continuous Security Monitoring
A penetration test of your SaaS applications gives you a point-in-time snapshot of the security posture. The moment the SaaS vendor releases an update, the pentest loses credence. That is why you must implement continuous monitoring for utmost security, aside from conducting pentests and scans from time to time.
3. Adopting Proactive SaaS Protection Strategies
You cannot wait for an issue to emerge before increasing your SaaS security efforts. While setting up appropriate measures for SaaS security takes time, effort, and help from SaaS security companies, their absence can wreak havoc.
Final Thoughts
It is always better to work with a SaaS security company that has a tap on emerging SaaS security issues and new vulnerabilities. You want a tool designed by competent security engineers to defend your application and your business from threats invited by third-party applications you use.
This list of SaaS security companies should be a good starting point for your search for the perfect SaaS security service for your company.
Frequently Asked Questions
1. How long does it take to complete a SaaS security audit?
The initial security scans and pentest take 7-10 days. After you have fixed the issues, the rescan may take half as much time.
2. What is the cost of a SaaS security assessment?
The cost can be between $200 and $500 monthly, depending on the assessment’s scope and the testing frequency.
3. What should we look for in a SaaS security company?
Apart from the company’s track record, you should look for features that can help you build a sustainable security assessment workflow—CI/CD integration, vulnerability management dashboard, collaborative potential, etc.