According to the recent IBM’s Cost of a Data Breach Report 2023, 45% of breaches are cloud-based, and 80% of companies have experienced at least one cloud security incident in the last year.
Moreover, with the global cloud computing market at $546.1 billion in 2022 and growing, adopting holistic cloud security practices has become critical.
This is where the importance of the AWS Security Audit comes in. An AWS security audit helps you discover all hidden vulnerabilities in your web system that can put your entire system at risk.
What is AWS?
AWS (Amazon Web Services) is Amazon’s implementation of the cloud computing concept. It offers around 175 fully-featured services from data centers globally and is currently a popular choice for cloud-based hosting in the industry. In simple words, AWS will let you host their computers (i.e servers) and thus allow you to:-
- Run Web and application server to host your dynamic websites.
- Securely store information on the cloud to access them over WAN.
- Host your database such as MySQL, PostgreSQL, etc on the cloud.
- Receive solutions for CDN or Content Delivery Network which can be troublesome to host on your network.
- Host SMTP, i.e., the mail server on cloud and send emails in bulk to your customers.
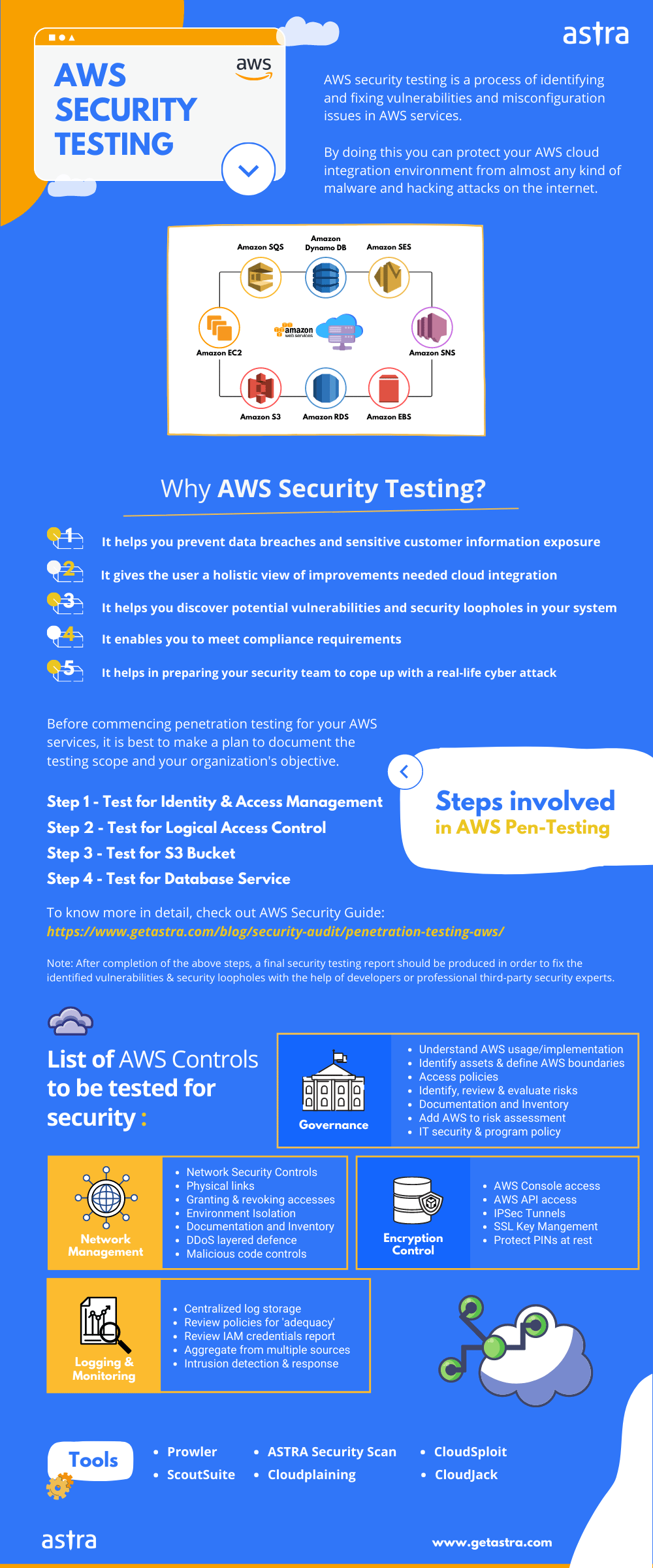
What is AWS Security Audit?
An AWS security audit is a comprehensive assessment of an organization’s AWS cloud environment to identify and mitigate security risks and vulnerabilities. It encompasses reviewing configurations, access controls, encryption, and compliance with AWS security best practices to ensure the protection of data and resources hosted on AWS.
The AWS cloud security audit can be divided into 2 categories:-
1. Security of Cloud
AWS manages the security of the cloud. This includes all the logic flaws or zero days that can be used to exploit the instance of the server. Security audit of the server is Amazon’s responsibility and you need not meddle with that.
2. Security in the Cloud
Security in the cloud is your responsibility. You can control the security of the instance by choosing what you decide to implement and how you do it. If you configure your web app securely, it can lead hackers to gain unauthorized access to the web app.
Why perform an AWS security audit?
An AWS security audit is important for identifying and mitigating security risks, complying with regulatory requirements, and improving your security posture. It can help you identify unauthorized access to AWS resources, detect malicious activity in your AWS environment, and validate your security controls.
Hence, it’s crucial to perform security audits at regular intervals or as and when you make changes to your AWS environment. This also helps you stay compliant with regulatory industry standards like ISO27001, GDPR, SOX, and more.
What is covered in the AWS security audit?
An AWS security audit typically covers the following areas:
1. AWS Identity and Access Management (IAM):
This includes reviewing IAM users, groups, roles, and policies to ensure that they are configured correctly and that users and software have only the permissions they need.
2. AWS resources:
This includes analyzing all of your AWS resources, such as EC2 instances, S3 buckets, and RDS databases, to ensure that they are configured securely and that they are not vulnerable to known attacks.
3. AWS security services:
This includes looking into your use of AWS security services, such as AWS GuardDuty, AWS Inspector, and AWS CloudTrail, to ensure that they are configured and used correctly.
4. AWS network:
This includes evaluating your AWS network configuration to ensure that it is secure and that it is meeting your security requirements.
5. AWS logging and monitoring:
This includes reviewing your AWS logging and monitoring configuration to ensure that you are collecting the necessary data and that you can detect and respond to security incidents promptly.
In addition to these general areas, an AWS security audit may also cover specific areas of interest, such as compliance with specific regulatory requirements or the security of specific applications or systems.
AWS Security Audit 101
Step 1: Identity and Access Management
The first step is to identify the assets and instances of data stores, applications, and the data itself. Assets on the public cloud are categorized under in-house environments. In some cases, the situation can be less complex to inventory as AWS provides visibility of the assets under management.
Some of the major points to keep in mind during asset identification are:-
- Remove all keys for the root account
- Do not use the root account for any automation or daily task
- Implement 2FA authentication for the root
- Allow the usage of only one key per user
- Change all SSH and PGP keys regularly
- Remove all unused security accounts
Common Vulnerabilities
- Absence of 2FA
- Over-permissive IAM policies
Step 2: Enable Logical Access Control
Logical Access Control is the process of assigning what type of actions can be performed on the resource (read, write, execute, etc) and by whom. The major part of this step involves controlling access to AWS resources, users, and processes.
The major portion of this step focuses on identifying how users and permissions are set up for the service in AWS. It is essential to ensure that the management of the credentials associated with the AWS accounts is well-secured.
Some significant points to keep in mind while testing access control are :
- Restrict access to sensitive resources
- Audit access control lists for misconfigurations
- Remove access for inactive accounts promptly
- Enforce periodic session timeouts
Common Vulnerabilities
- Misconfigured ACLs lead to unauthorized access
- Missing access control policies
Step 3: Secure S3
In simple words, the S3 is essentially a cloud folder commonly called a “Bucket”. It is a storage server that supplies you with robust such as region exceptions, versioning, access logging, encryption, and access control.
Some major points to keep in mind while testing S3 Buckets:-
- Permissions for HTTP methods, such as LIST, GET, PUT, DELETE, etc., should only be granted to specified users.
- The bucket should have versioning enabled.
- The bucket should have logging enabled.
Common Vulnerabilities
- Lack of encryption for stored data
- Publicly accessible S3 buckets exposing sensitive information
Step 4: Optimize Database Services
Databases are used in most web services. Thus, you must make sure that your database follows the security standards. A single flaw in your cloud service can cause you to have a data breach.
Some major points to keep in mind the following key points during the AWS security audit:-
- Back up your data regularly.
- The backup retention time should be set to more than a week.
- Use of the Multi-AZ deployment method is recommended.
- Instance storage should have some encryption enabled.
- Allow access to only a few specified IP addresses.
- The Database snapshots should not be publicly accessible.
Common Vulnerabilities
- Unencrypted data stored in databases
- Open database ports on the internet
Step 5: Employ Vulnerability Scanners
Once you have finished securing your service in the cloud according to the security standards, running a vulnerability scanner is recommended. This will show you if you have any missing assets or CVE.
Popular vulnerability scanners such as CloudSploit can help you with the process. It scans every public region of the AWS instance, including the ones you don’t actively use.
Some major points to keep in mind while using vulnerability scanners:
- Regularly scan your AWS environment for vulnerabilities
- Schedule automated scans whenever you update you AWS environment
- Ensure all resources like databases and containers are included in the scans
AWS Security Audit Provider – Astra
Astra’s solution provides an in-depth AWS security audit under our VAPT program. Astra performs an in-depth audit of static code & dynamic code and other 10,000+ test cases that include business logic errors, payment security flaws, price manipulation testing, network misconfigurations, tests for known CVEs, insecure roles and permissions, and more.
From the time you sign up to the completion of the audit, it’s a smooth process and can be visualized in the following picture:

Our experts not only report the vulnerabilities but also provide remediation methods to fix them. Not only this, Astra engineers are known to go the extra mile, so they also assist you/your developer in patching the vulnerabilities and are quick to do a re-scan for you to ensure everything is in place.

Final Thoughts
With the rising adoption of cloud platforms like AWS, the security of these cloud environments is very crucial. An AWS security audit allows you to stay on top of the potential threats and enables you to strengthen your security posture. By auditing key areas like IAM, database configurations, S3 buckets, and network controls, you can stay compliant with regulatory standards.
FAQs
How do I conduct an AWS audit?
To conduct an AWS audit, start by reviewing your AWS configurations, permissions, and access controls. Use AWS pen testing tools like AWS Config and IAM to assess compliance with best practices, identify vulnerabilities, and monitor for suspicious activities. Collaborate with security experts and leverage third-party auditing tools for a comprehensive evaluation of your cloud.
Which AWS service is used for auditing?
The AWS service used for auditing is AWS Audit Manager. It is a cloud-based audit service that helps you automate the collection and analysis of audit evidence to meet your compliance requirements. AWS Audit Manager provides pre-built and custom audit frameworks that you can use to assess your AWS environment against a variety of standards