Magneto, the 4th most used e-commerce platform, has simplified the way e-commerce is done, and its open-source nature has made it accessible to all. The scalability and flexibility of the platform have attracted a lot of e-commerce stores ranging from fashion to electronics. With more than 2,00,000 live magneto websites worldwide, it makes them a prime target for cyber attacks.
Risks involving financial transactions and leakage of personal information are the reasons why full-fledged Magento penetration testing is important for e-commerce websites to ensure that their users are protected and, in turn, their trust and reputation are protected.
Magento Penetration Testing: Prerequisites
Magento penetration testing is performed using specialized tools to find vulnerabilities in the configurations. A collection of such tools can be found in the Kali Linux OS that allows testing various test cases in a magneto application. It is recommended that Kali Linux must be installed using a VirtualBox for ease of use.
Pro tip:- Always remember to obtain permission before testing to avoid legal consequences, and always test within the authorized scope.
Installing Kali Linux for Magento Security Audit
- Step 1: Firstly, download the Virtual Box from the official site and install it using the instructions (any other emulator of your choice can also be used).
- Step 2: Next step is to download and install the latest version of Kali Linux on Virtual Box for Magento penetration testing.
- Step 3: After the installation is done, install more “guest addition” tools for Kali Linux to function efficiently on Virtual Box.
- Step 4: In case you are still failing to install Kali Linux on the Virtual Box, simply use a Kali VM image for Magento penetration testing.
Magento Penetration Testing: Reconnaissance
Following a Black-Box method, the first step is to try to uncover the maximum underlying technologies. Because Magento core files are not always vulnerable. At times it could be a buggy server. Some great tools to conduct reconnaissance for Magento penetration testing are:
Network Mapper(Nmap)
Nmap can provide a large amount of information regarding the Magento target. It is a must-have tool for complete fingerprinting of the system. Nmap can reveal:
- Open ports on the server.
- Services running on those ports.
- Use NSE scripts for Magento vulnerability detection.
Nmap can do all this quite stealthily and has lots more to offer. To use Nmap, fire your Kali on the VM and in the command line terminal and type ‘nmap‘.

In the above image, the -sV option of the Nmap here enables version detection. In our case, it has found multiple open ports with the Microsoft IIS server running on port 80. Moreover, Nmap has also found the MAC address of our local target. Also, there is a GUI version of Nmap known as Zenmap, which simplifies things further.

OSINT Collection Tool: The Harvester
When it comes to reconnaissance for Magento penetration testing, there is a wealth of information available on the internet. This includes things like ownership info, nameservers, etc. which can help in mapping out the complete organization. This info is known as open-source intelligence and is very helpful for social engineering attacks.
The harvester can collect data from sources like Shodan, Google, Whois, DNS servers, etc. Therefore, the Harvester is a one-stop solution for OSINT. Hence, it is advisable to use the Harvester instead of visiting each of these sites individually.

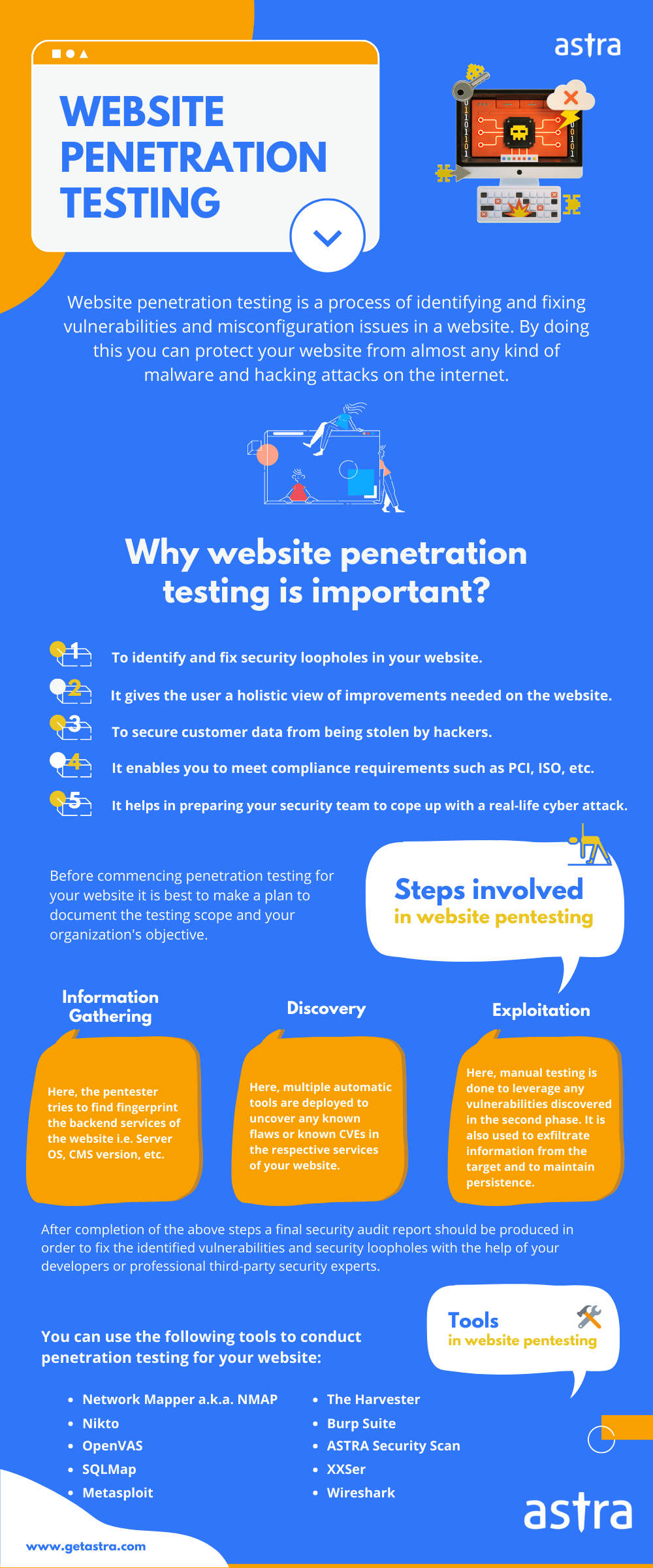
Magento Penetration Testing: Discovery
Now once, the technologies have been identified, the next step is to look actively for Magento website vulnerabilities. Although earlier, there was an open-source Magento-specific vulnerability scanner, post-2018, it went commercial and is no longer maintained. Some other helpful tools are:
OpenVAS
One of the best tools for discovering vulnerabilities on any Magento site is the OpenVAS framework. Moreover, most part of the OpenVAS is GNU general public license. This framework is a powerful vulnerability scanner that conducts some 50,000-odd Network Vulnerability Tests to find loopholes. OpenVAS is a free framework that gives the feel of a commercial security solution.

Nikto
Nikto is an open-source vulnerability scanner that offers around 6700 test for server misconfigs and 1250 test for outdated server versions. Not only this, Nikto can scan for server-specific vulnerabilities of around 270 servers. However, for best results, disable your WAF or firewall before using Nikto for Magento penetration testing. To scan a target using Nikto, simply open Kali and type in the command terminal:
nikto -h 'your-target'
Magento Penetration Testing: Exploitation
Now once the vulnerabilities are identified, it is time to remove false positives. This is done during the exploitation process. Only a serious vulnerability could exploit a Magento store. This can be done via the following tools:
Metasploit
Written in Ruby, Metasploit is one of the most popular frameworks used for exploitation. Rapid 7, the company that owns Metasploit, maintains and keeps updating a large database of exploits that can be run from the Metasploit framework. Metasploit can be updated for your Kali Linux by typing the command ‘msfupdate’. Metasploit can also be accessed via GUI from the Armitage tool of Kali Linux. To launch Metasploit from the terminal, type:
msfconsole
Sqlmap
Started by Stamparm on Github, Sqlmap is one of the best SQL injection exploitation tools available today. Sqlmap can be used to fuzz and find vulnerable targets automatically. Not only vulnerable parameters but SQLmap can also be injected into data fields and forms on a web page. Sqlmap can exploit SQLi vulnerabilities to read the contents of a database, alter them, and, in some cases, even get a reverse shell from the Magento store. To test a target for SQLi using this tool, type:
sqlmap -u 'your target URL' --batchThe –batch command automates the task and chooses default values during the testing process, as shown in the image below.

Xsser
To exploit an XSS vulnerability in the Magento store, Xsser is one of the best and most lightweight tools. To obtain the GUI interface of Xsser, in the terminal type:
xsser –gtkFor more help, type:
xsser -h
Commix
Commix is a tool that exploits command injection vulnerabilities in a Magento store. For further info, fire up your Kali, and in the terminal, write: commix -h

Magento Security Audit
PCI Compliance
Magento store owners can choose from a wide variety of payment methods like PayPal, SagePay, Google Checkout, etc. However, the important thing here is that the payment methods need to be PCI compliant, which means that the method has adequate security measures to protect the transaction data from hacking.
Secure Hosting and SSL
Another crucial thing to check during the Magento security audit is the hosting provider. Is the hosting service safe? Is there subnetting on the shared web space? Going for VPS would be a recommendation here. Moreover, the use of certified SSL certificates needs to be checked. Remember to take an SSL certificate only from a valid certifying authority.
Software Version
Ensure that the site is running on the latest version of Magento. Magento stops releasing security patches for older versions, so outdated sites are a security risk. Moreover, check that all the extensions are up to date. If the site is using the latest version, then ensure that all the security patches are installed.
Two-Factor Authentication
Enabling two-factor authentication adds an extra layer of security to the Magento store. You can implement this via services like Google Authenticator, Authy, U2F Keys, Duo Security.
Users and File Permissions in Magento
Make sure to set a limit on the resources different users can access. In Magento 2.3, set permissions through the following instructions. Visit:
System>Permission>User Roles>Click “Administrators”>Role Information>Role Resources>Role Access>Custom
From here on, assign roles accordingly. Moreover, file permissions are also necessary. To set them, log into the server and use any file manager to assign file permissions.
Backup
If the Magento store logs every activity, this can help determine the cause of a hack. Moreover, check for the availability of website backups during a Magento security audit. Ensure that at least 3-4 backups of the Magento store and its database are available. While using cloud hosting for the Magento store, make use of automatic backup provided by the service provider.
Automation Prevention
Make sure that the Magento store is safe from bots and spam. To do this, you can implement a captcha on every input form like contact, feedback form, etc. In Magento 2.3, add a captcha by visiting:
Stores>Configuration>Customer>Customer Configuration>Captcha
Security Solution
Ensure that the Magento store uses a firewall to filter bad requests. If not then get one today. Astra offers just the right security solution customized for Magento users. Moreover, Astra is an expert in Magento penetration testing and security auditing. A vetted team of hackers will scan your Magento store in and out for any vulnerabilities. Experience Magento security like never before.
Final Thoughts
Magneto penetration testing is a vital step for ensuring the security and reliability of your eCommerce store. Using tools like Nikto, OpenVAS, Metasploit, SQLmap, and more, you can identify vulnerabilities and mitigate them efficiently. Regular audits and following best practices allow defense against cyber threats and meet regulatory compliances.
FAQs
What is the timeline for Magento Penetration Testing?
The timeline for a comprehensive Magento Pentest is 7-10 days, depending upon the scope and requirements of the scan. Once the vulnerabilities are fixed, the application goes through rigorous rescanning for up to 3 more days to verify the fixes applied to the vulnerabilities.
How much does penetration testing cost?
The cost for penetration testing ranges between $99 and $399 per month for websites. The cost of pentesting for cloud infrastructure and mobile apps differs based on the scope of the pentest. The price may also differ based on the services provided by the pentest provider.
To learn more about the topic, check out our guide to penetration testing cost.
Why choose Astra for penetration testing?
1250+ tests, adherence to global security standards, an intuitive dashboard with dynamic visualization of vulnerabilities and their severity, security audit with simultaneous remediation assistance, and multiple rescans are the features that give Astra an edge over all competitors.
Do I also get rescans after a vulnerability is fixed?
Yes, you get 1-3 rescans based on the type of Pentesting and the plan you opt for. You can avail of these scans within 30 days from the initial scan completion, even after the vulnerabilities are fixed.