Article Summary
SQLi Vulnerability found in Magento’s version 2.1, 2.2, 2.3, mended and patched versions- 2.1.17, 2.2.8, 2.3.1 are available.
Magento is one of the popular and trusted names in the e-commerce space. The website owners were shocked when it disclosed multiple vulnerabilities a few days ago in versions 2.1, 2.2 and 2.3. The vulnerabilities reported include cross-site request forgery, unauthenticated SQL inscription, cross-site scripting and arbitrary code execution (remote code execution).
Although, Magento has done quite a bit to make its security structure impeccable in the past. It has restricted the access to random people trying to perform the listed hacks by allowing only authenticated people on its website. It has been doing well by offering rewards to its vulnerability reporters till now. This news came as a shocker. The details of the vulnerabilities and risks attached to it is in the following lines.
Risk Status
The risk has been mitigated as Magento was quick to mend the backdoor and update its security with the newer patched versions – 2.1.17 for 2.1, 2.2.8 for 2.2, 2.3.1 for 2.3.
To protect your sites on Magento :
- You can install patch PRODSECBUG-2198
- Update the themes
- Reset the old passwords
NOTE: The full information about these installations were made live by Magento on 26th of march itself.
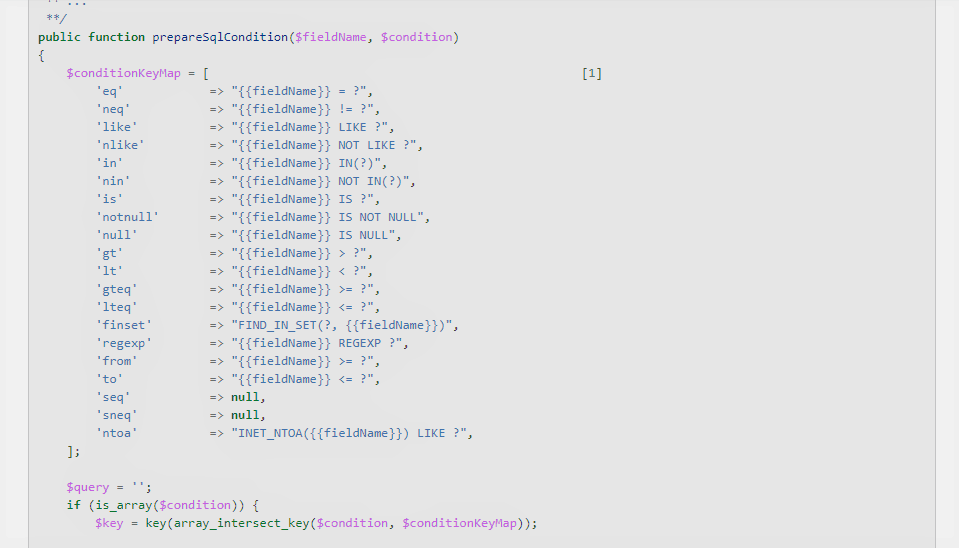
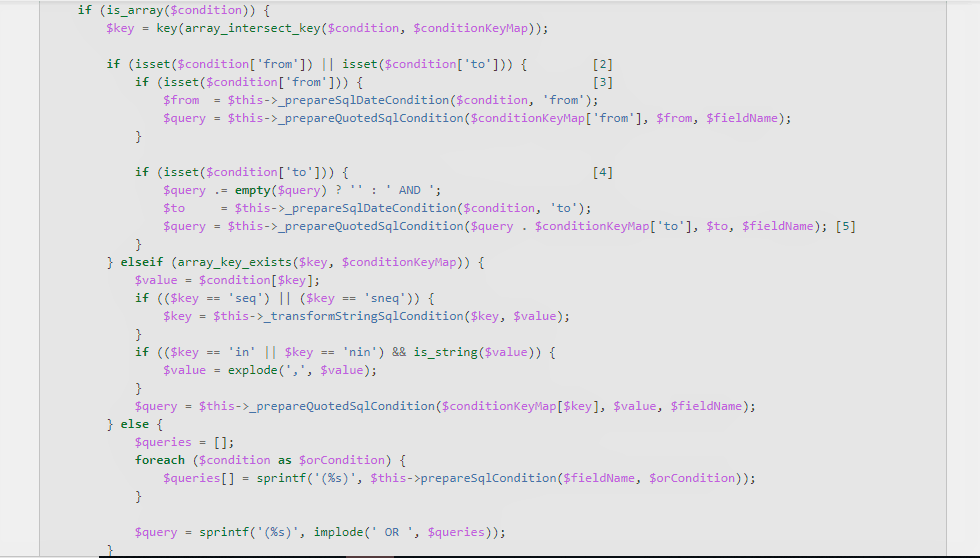
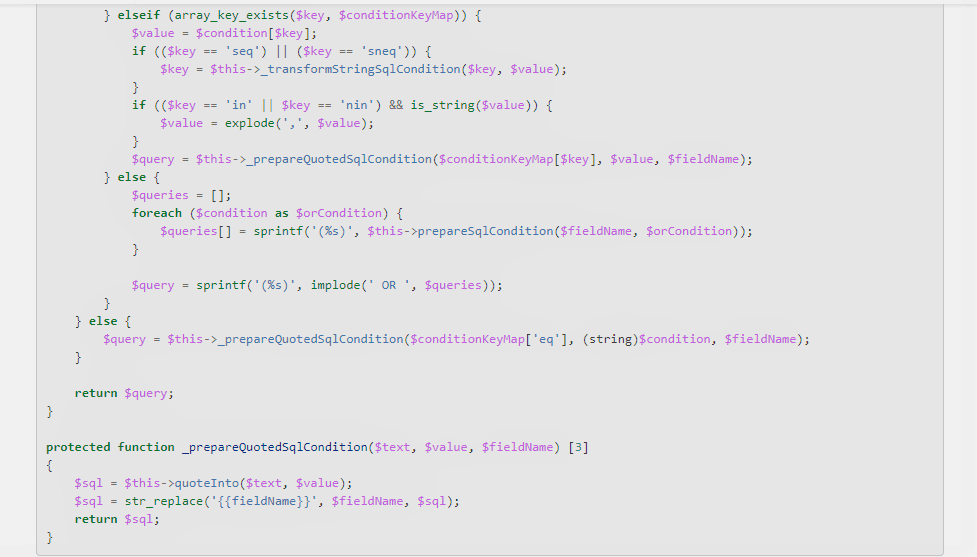
The vulnerabilities were founded by Netanel Rubin, who manually audited the billions of PHP lines in Magento and reached the conclusion that the key vulnerabilities found in ORM and DB were basically targeting two things:
Codes compromised
Some of the bugs that were found were in the following lines of codes.
Your Security
It is best that you are alerted as soon as possible and follow up with the guidelines plus the basic security updates like updating themes and resetting passwords. Avoid any negligence and be as vigilant as you can with the coding standards and other measures.
Related Blog Post – Magento SQL injection.
Astra Magento Firewall & Vulnerability Assessment & Penetration Testing
Astra’s Magento Security Suite is everything security solution that your store ever needs. We offer Web Application Firewall, Immediate Malware Removal & VAPT (Vulnerability Assessment & Penetration Testing). Thousands of customers (likes of Gillette, African Union, Jet Airways, Akeneo – Founded by former CTO of Magento etc.) use Astra to secure their websites.
Astra’s vision is to make cyber security a five minute affair for businesses. It’s a promise to a business owner that their business would be secure without any ifs or buts. If a business is using Astra, they will be secure – no questions asked