With AI, hybrid data centers, and evolving business needs, over 35% of organizations now adopt DevSecOps—a robust method to integrate security into development. Application security tools are central to DevSecOps, identifying vulnerabilities and ensuring secure applications across development phases.
As such, our security experts have curated the top 11 application security testing tools based on scanning capabilities, effectiveness of pentest reports, compliance satisfaction, realistic timelines, and cost.
11 Best Appsec Tools for Security Analysts
- Astra Security
- Qualys
- Rapid7
- Intruder
- Checkmarx
- Mend.io
- Veracode
- ZAP
- OpenVAS
- Nikto
- SQLMap
- Nmap
Comparing the Top 3 Application Security Testing Tools
| Feature | Astra Security | Qualys | Rapid7 |
|---|---|---|---|
| Pentest Capabilities | Web/mobile apps, cloud, API, networks | Web apps, APIs, cloud, LLM models (AI security) | Cloud & web applications |
| Platform | Manual, automated, AI-augmented | Cloud-based, automated | Automated scanning |
| Continuous Vulnerability Scanning | Yes | Yes | Yes |
| Compliance Scanning | Yes | Yes | Yes |
| AI-powered Test Cases | Yes | Yes | No |
| Pentest Reports | Yes | Yes | Yes |
| Publicly Verifiable Certificates | Yes | Yes | No |
| Workflow Integrations | Slack, GitHub, GitLab, Jira, Jenkins, and more | Integrates with ticketing/dev/security tools like Jira, Bamboo, and ServiceNow | JIRA, Slack, GitHub, and more |
| Expert Remediation | Yes | Yes | No |
| Scan Behind Login | Yes | Yes | No |
| Pricing Plan (Starting) | $1,999/year | $2,195/year | Variable, based on specific product and the size of environment |
| Best Suited For | Multi-asset pentesting & continuous scanning | Vulnerability management, compliance, scalable web app/API/cloud security | Vulnerability management pentesting |
| Pros | Certified experts, publicly verifiable certification, seamless CI/CD integration, free rescans, and executive reporting | Automated, customizable, extensive integration, detailed reporting | Top-tier threat intelligence |
| Cons | 1-week trial only | Longer scan times, manual verification needed, resource-intensive | Functionality & support issues |
Evaluation Criteria: Our evaluation criteria for these application security testing tools focused on various factors. We considered the range of scanning capabilities and the extent to which each tool provides coverage for multiple application types and vulnerabilities. Accuracy and the minimization of false positives are essential for effective vulnerability management. The tool should easily integrate with existing development and security workflows and have comprehensive reporting features, which were also key considerations. Finally, we aimed to represent a mix of open-source and commercial tools to accommodate different budgets and organizational needs.
Top 11 Application Security Testing Tools
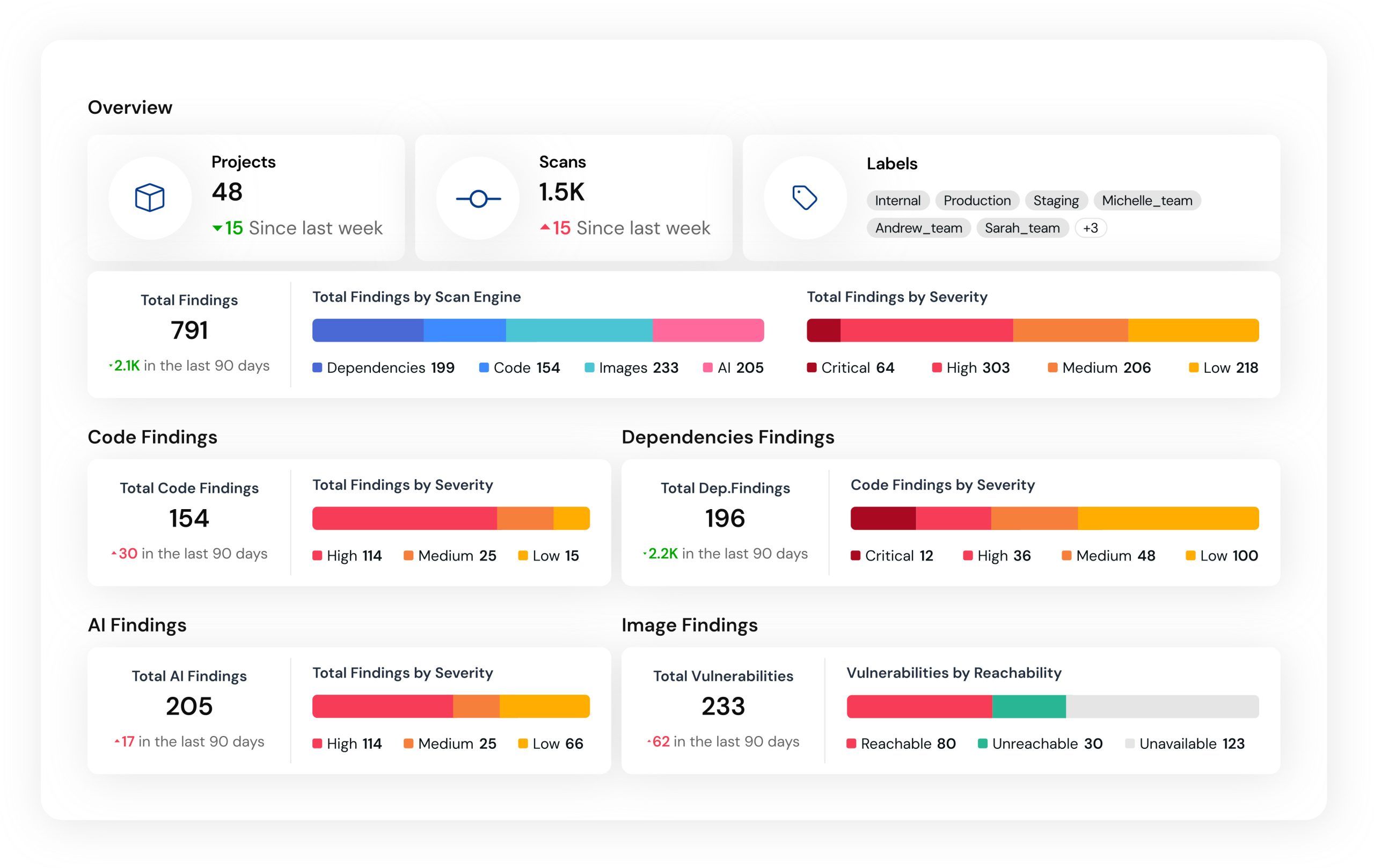
1. Astra Security [Get Started]

Features:
- Type of Scanner: DAST
- Scanner Capabilities: Web and Mobile Applications, Cloud Infrastructure, API, and Networks
- Accuracy: Zero False Positives Assured (Vetted Scans)
- Scan Behind Logins: Yes
- Compliance: PCI-DSS, HIPAA, SOC2, and ISO 27001
- Integrations: Slack, Jira, GitHub, GitLab
- Expert Remediation: Yes
- Deployment: SaaS
- Pricing: Starts at $199/month
- Pros: 10,000+ AI vulnerability tests, intuitive dashboard, continuous DevSecOps integration.
- Cons: Trial available only for the DAST scanner
- Best Use Case: SaaS companies, CI/CD environments, businesses in need of continuous offensive web application/API security.
Built on standards like OWASP, NIST, and SANS25, Astra’s automated application security testing tool and proprietary scanner runs over 10,000+ tests to pinpoint new, emerging, and existing vulnerabilities in various types of assets.
Our vetted scans help guarantee zero false positives, and a CXO-friendly dashboard, with AI-powered test case generation and chatbot, delivers a smooth application security testing experience. Moreover, our smart extension helps record logins for simplified scanning of protected screens and user roles.
Experts Review
Why did we choose Astra Security?
Astra Security is a unique tool that can scan multiple platforms like web and mobile applications, cloud infrastructure, APIs, and networks, providing a complete picture of an organization’s security posture. The zero false positive guarantee (through vetted scans) is a significant advantage that ensures that security teams can focus on real threats. Astra’s commitment to compliance (PCI-DSS, HIPAA, SOC2, ISO 27001) and integrations with popular development tools make it a strong choice for organizations with diverse needs.
Open-Source Application Security Testing Tools
2. Zed Attack Proxy (ZAP)
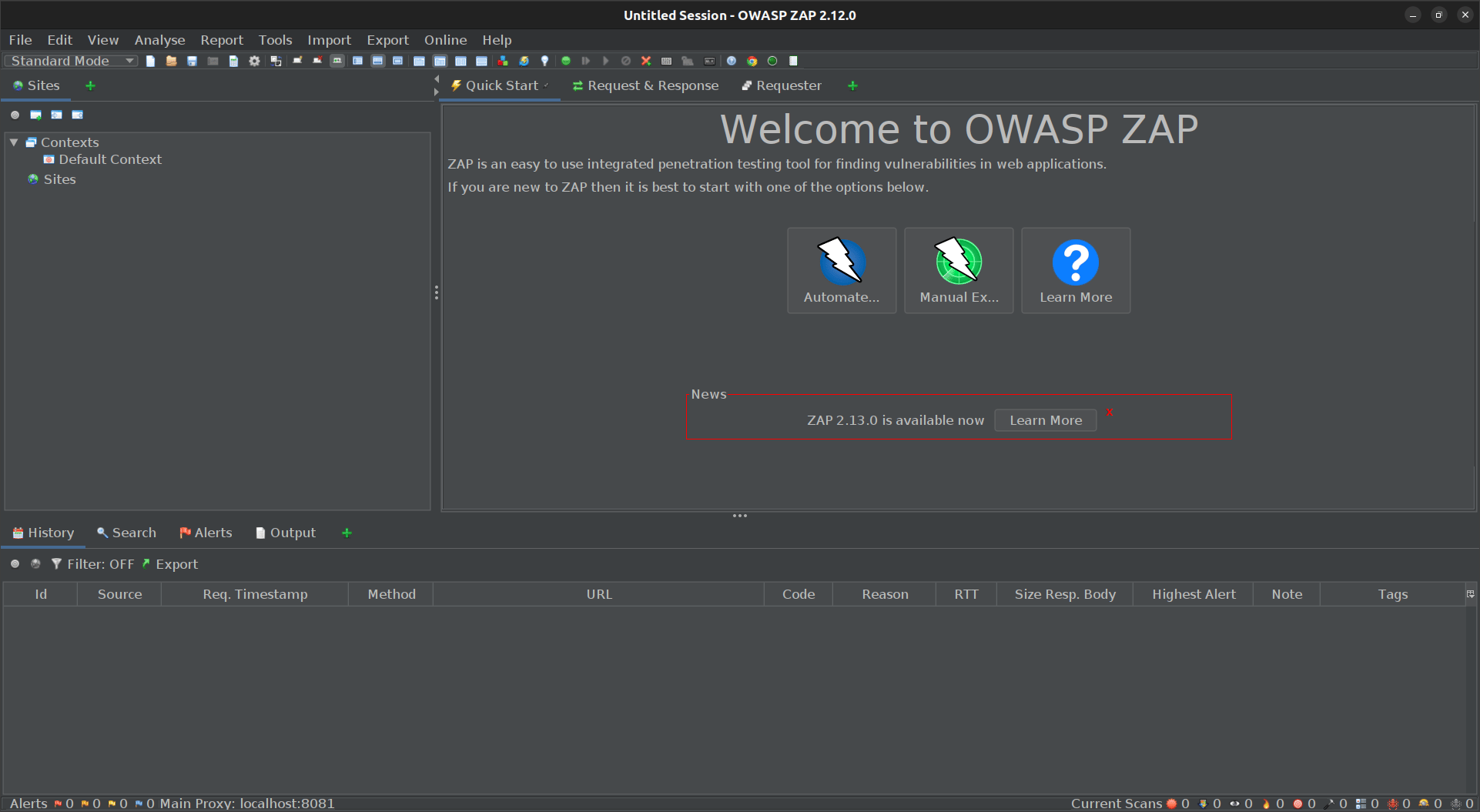
Features:
- Type of Scanner: DAST
- Scanner Capabilities: Web application scanning
- Accuracy: Some false positives are possible
- Scan Behind Logins: Yes
- Integrations: Jenkins, Jira, and other CI/CD tools
- Expert Remediation: No
- Deployment: Local, Docker, and Cloud
- Pricing: Open-Source
- Pros: Open-source, thorough scanning rules, active community, and suitable for authenticated/unauthenticated web app scans.
- Cons: Complex configuration for advanced use cases and can be slow for large apps.
- Best Use Case: DevSecOps and security teams testing web apps, API endpoints, and CI/CD pipelines.
- Security Compliance/Mapping: Useful for checking OWASP Top 10, PCI DSS, and general web app security compliance
ZAP, as one of the most popular open-source web application security testing tools, Zed Attack Proxy (ZAP) is designed according to OWASP guidelines to find vulnerabilities in web apps.
It is a widely used tool by security professionals and can perform automated scans and manual testing, making it versatile for various use cases for your web application security needs.
Experts Review
Why did we choose ZAP?
ZAP is an open-source web application security testing tool, making it an accessible option for organizations with budget constraints. Its alignment with OWASP guidelines and its ability to perform automated and manual testing makes it a versatile tool for web application security.
3. OpenVAS

Features:
- Type of Scanner: DAST
- Scanner Capabilities: Network and web application scanning
- Accuracy: High accuracy, but some false positives are possible
- Scan Behind Logins: Yes
- Integrations: Various SIEM tools
- Expert Remediation: No
- Deployment: Local, Docker, and Cloud
- Pricing: Open Source
- Pros: Large vulnerability database, flexible and customizable scans, and detailed reporting.
- Cons: High resource usage, steep learning curve, and prone to false positives. Also, the API testing features are limited.
- Best Use Case: Security teams in startups and small businesses requiring budget-friendly vulnerability scanning.
- Security Compliance/Mapping: Regular compliance assessments for PCI DSS, HIPAA, and CIS.
OpenVAS (Open Vulnerability Assessment System) is a comprehensive application security testing tool part of the Greenbone Vulnerability Management (GVM) framework.
It is well-suited for small and large environments and is designed to scan network infrastructure and web applications for security issues and provides detailed reports and vulnerability assessments.
Experts Review
Why did we choose OpenVAS?
OpenVAS is another open-source option that provides comprehensive vulnerability assessments for network infrastructure and web applications. Its inclusion in the Greenbone Vulnerability Management framework makes it suitable for organizations of all sizes.
4. Nikto
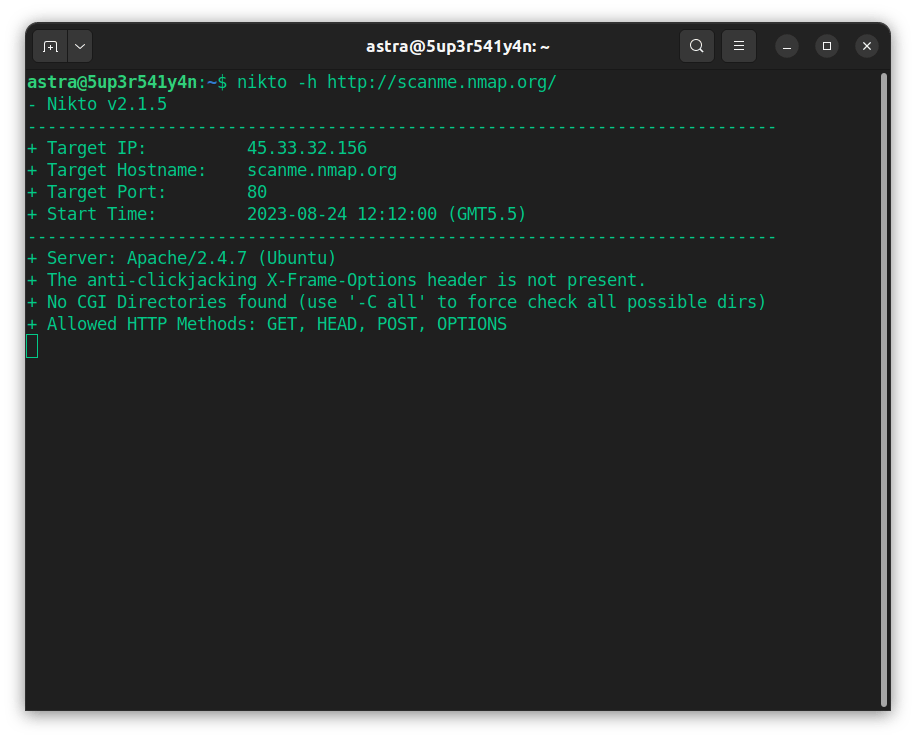
Features:
- Type of Scanner: DAST
- Scanner Capabilities: Web server scanning
- Accuracy: Moderate, false positives possible
- Scan Behind Logins: No
- Integrations: No
- Expert Remediation: No
- Deployment: Local
- Pricing: Open Source
- Pros: Fast web server scanner, comprehensive checks for outdated software/default files, and easy to automate.
- Cons: Noisy scans (easily detected by IDS), CLI-only, and numerous false positives requiring manual verification.
- Best Use Case: Bug bounty, penetration testers, SME/server admins for quick web server misconfiguration/vulnerability checks.
- Security Compliance/Mapping: Helps with scanning for OWASP Top 10, PCI-DSS, and basic server hardening.
Nikto is an open-source web server scanner that performs comprehensive tests against web servers for multiple items, including over 6,700 potentially dangerous files and programs. It also checks for outdated versions of servers and other issues.
As one of the appsec tools, it specializes in penetration testing and identifying security vulnerabilities in web servers.
Experts Review
Why did we choose Nikto?
Nikto’s focus on web server scanning makes it a valuable tool for identifying outdated software and misconfigurations. Its open-source nature and specialized focus make it a good choice for organizations looking for a dedicated web server scanner.
5. SQLmap
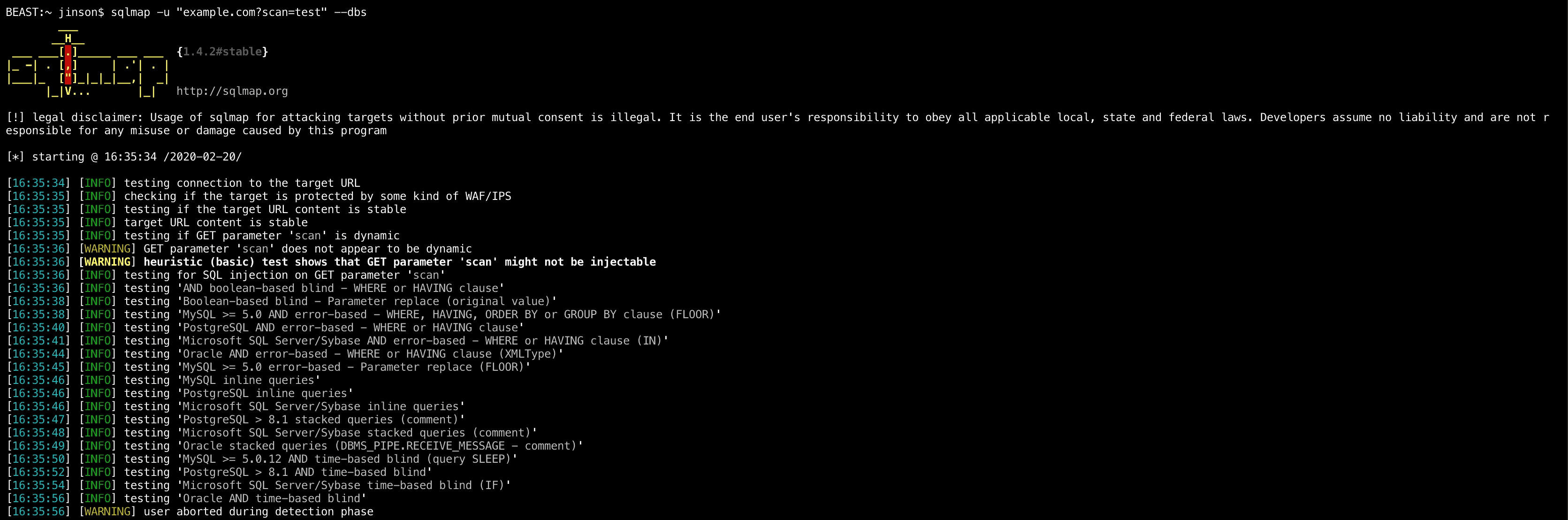
Features:
- Type of Scanner: DAST
- Scanner Capabilities: Web applications
- Accuracy: False positives possible
- Scan Behind Logins: Yes
- Integrations: No
- Expert Remediation: No
- Deployment: Local
- Price: Open-source tool
- Pros: Automated SQL injection detection/exploitation, multi-DBMS support, and advanced features for pentesters.
- Cons: Specialized (SQLi only), and can disrupt DB performance if misused. Also, requires expertise for efficient use.
- Best Use Case: Pentesters in need of in-depth database security validation on web apps/API endpoints.
- Security Compliance/Mapping: Supports validations for OWASP Top 10, assists in compliance audits for PCI DSS.
SQLMap is a free application security tool that helps identify potential vulnerabilities to SQL injection.
It boasts a resilient testing mechanism that accommodates various attacks and is compatible with several database servers, such as MySQL, Microsoft Access, IBM DB2, and SQLite
Experts Review
Why did we choose SQLmap?
SQLmap’s strength lies in its ability to identify SQL injection vulnerabilities. Its open-source availability and exhaustive testing mechanisms make it a crucial tool for organizations concerned about this specific type of attack.
6. Mend.io
Features:
- Type of Scanner: SAST, SCA, Container, AI Security, DAST
- Scanner Capabilities: Custom Code, Open Source, Containers, AI Components
- Accuracy: False positives possible
- Scan Behind Logins: Yes
- Compliance: PCI-DSS, HIPAA, and other compliance frameworks
- Integrations: Azure DevOps, GitHub, Jira
- Expert Remediation: No
- Deployment: Cloud-Based
- Pricing: Quote Upon Request
- Pros: Top-notch SCA, robust CI/CD and container support, along with accurate vulnerability tracking.
- Cons: Reporting needs enhancement
- Best Use Case: Development organizations managing open-source dependencies in CI/CD pipelines, scalable to all sizes.
Mend.io is an AI-native application security platform designed for modern development pipelines. It combines static code analysis, open-source risk detection, and unique capabilities for securing AI-generated code and testing AI components (static detection and red teaming).
Its built-in dependency updater (Mend Renovate) and AI-powered remediation help teams fix critical risks faster and reduce overall application exposure.
Experts Review
Why did we choose Mend.io?
Mend.io delivers a unified approach to application security, enabling teams to secure their entire codebase, from custom code to embedded AI components. Its automation-first design, intelligent prioritization, and developer-centric integrations make it a standout choice for companies looking to get a holistic view of their applications’ risk.
7. Nmap
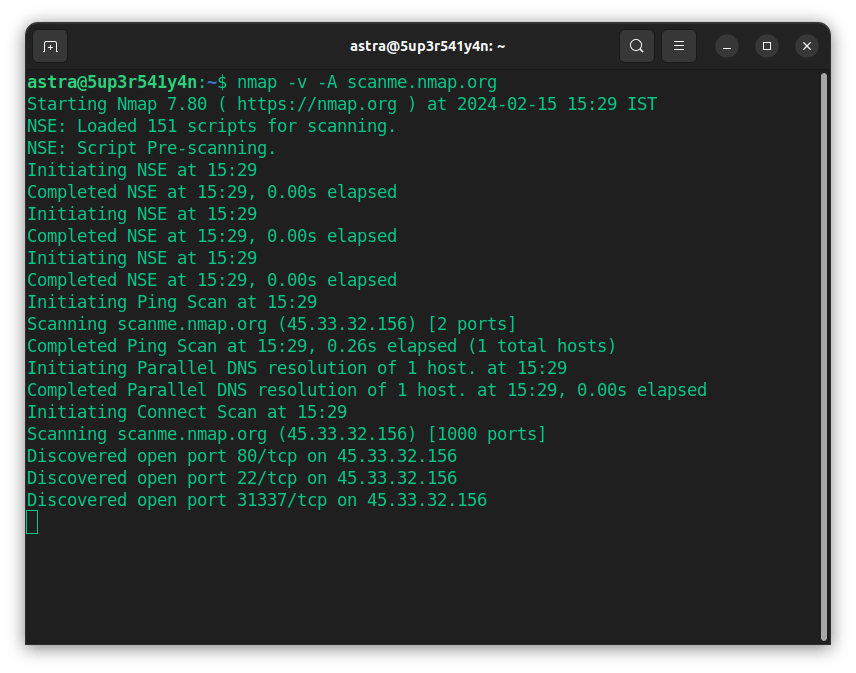
Features:
- Type of Scanner: DAST
- Scanner Capabilities: Network scanning
- Accuracy: False positives possible
- Scan Behind Logins: No
- Compliance: No
- Integrations: No
- Expert Remediation: No
- Deployment: Local/Command Line Tool
- Pricing: Open Source
- Pros: Fast/efficient network mapper and robust host/service/OS/vulnerability discovery.
- Cons: Steep learning curve for advanced features, and can trigger security alerts (intrusive).
- Best Use Case: Security/network teams for asset discovery, port/service audit, and vulnerability/penetration test prep.
Nmap is an open-source vulnerability scanner that helps with cloud network discovery, management, and monitoring. It is designed to scan large cloud networks. However, it also works fine against singlet networks.
The AST tool can be used for port scanning, network mapping, service detection, and firewall evasions. For an analyst, the results from NMAP can be quite helpful during the reconnaissance phase of a pentest.
Experts Review
Why did we choose Nmap?
Nmap is a versatile open-source tool for network discovery, management, and monitoring. Its ability to scan large networks and identify open ports and services makes it an essential tool for understanding network security posture.
Paid Application Security Testing Tools
8. Qualys
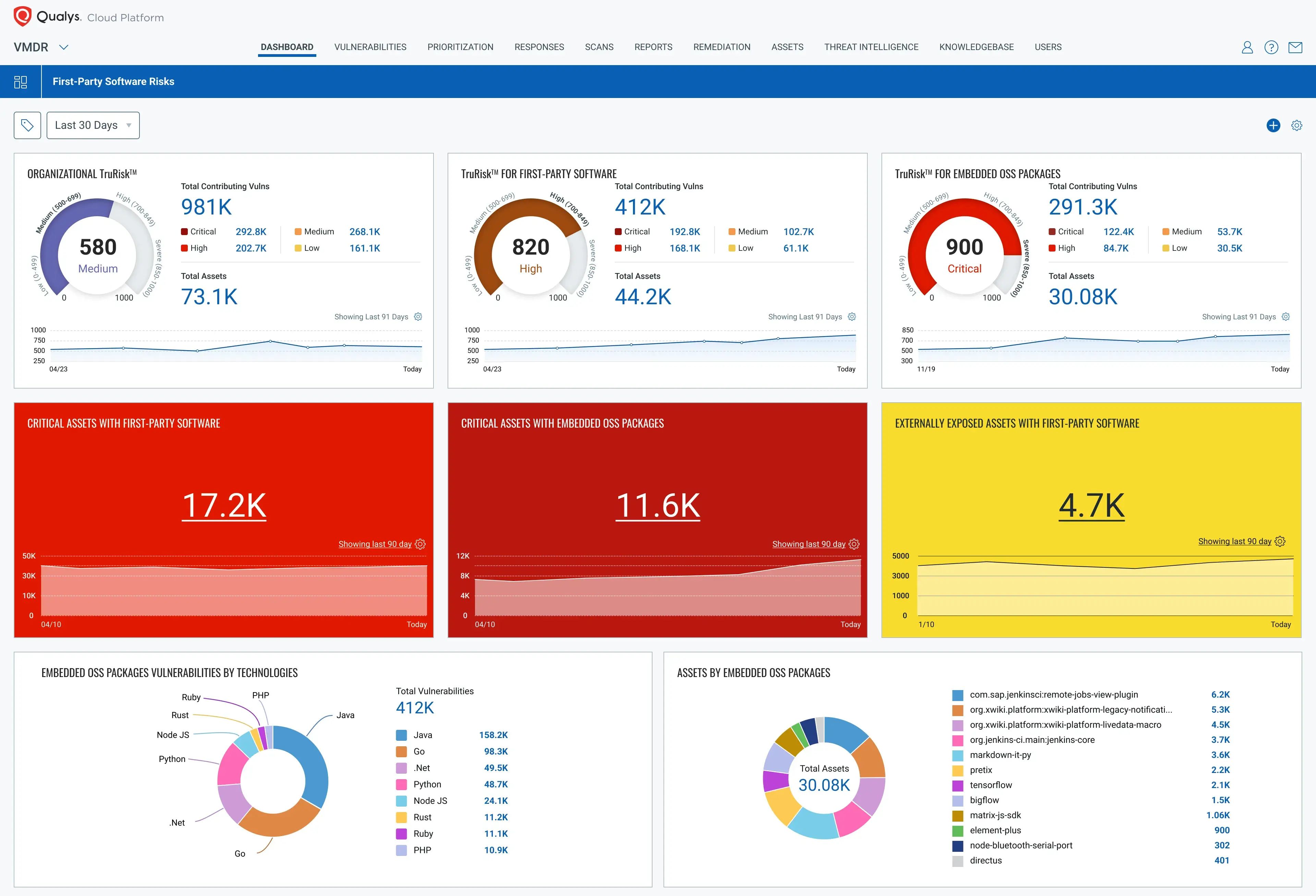
Features:
- Type of Scanner: DAST
- Scanner Capabilities: Cloud, web applications
- Accuracy: False positives possible
- Scan Behind Logins: Yes
- Integrations: Cisco, IBM, Splunk
- Expert Remediation: Yes
- Deployment: SaaS or Private Cloud-based option
- Pricing: Quote Upon Request
- Pros: Automated compliance audits, real-time monitoring, and strong reporting. Covers most enterprise compliance needs.
- Cons: Setup can be complex. Pricing is high for small businesses, and templates are less flexible.
- Best Use Case: Enterprise vulnerability & compliance management for regulated verticals like finance, healthcare, and government.
- Security Compliance/Mapping: SOC 2, ISO 27001, PCI DSS, HIPAA, GDPR, and custom policy mapping.
Qualys WAS is a cloud-based website vulnerability scanner platform that assesses cloud assets, vulnerabilities, and compliance status.
It constantly updates its database of over 20,000 vulnerabilities across various asset types and Operations systems. Its scalability, accuracy, and user-friendly interface are some of the reasons that make this tool a popular choice.
Experts Review
Why did we choose Qualys?
Qualys WAS is a cloud-based platform that offers end-to-end web application scanning and vulnerability management. Its scalability, accuracy, and user-friendly interface make it a popular choice for organizations looking for a robust commercial solution.
9. Rapid7
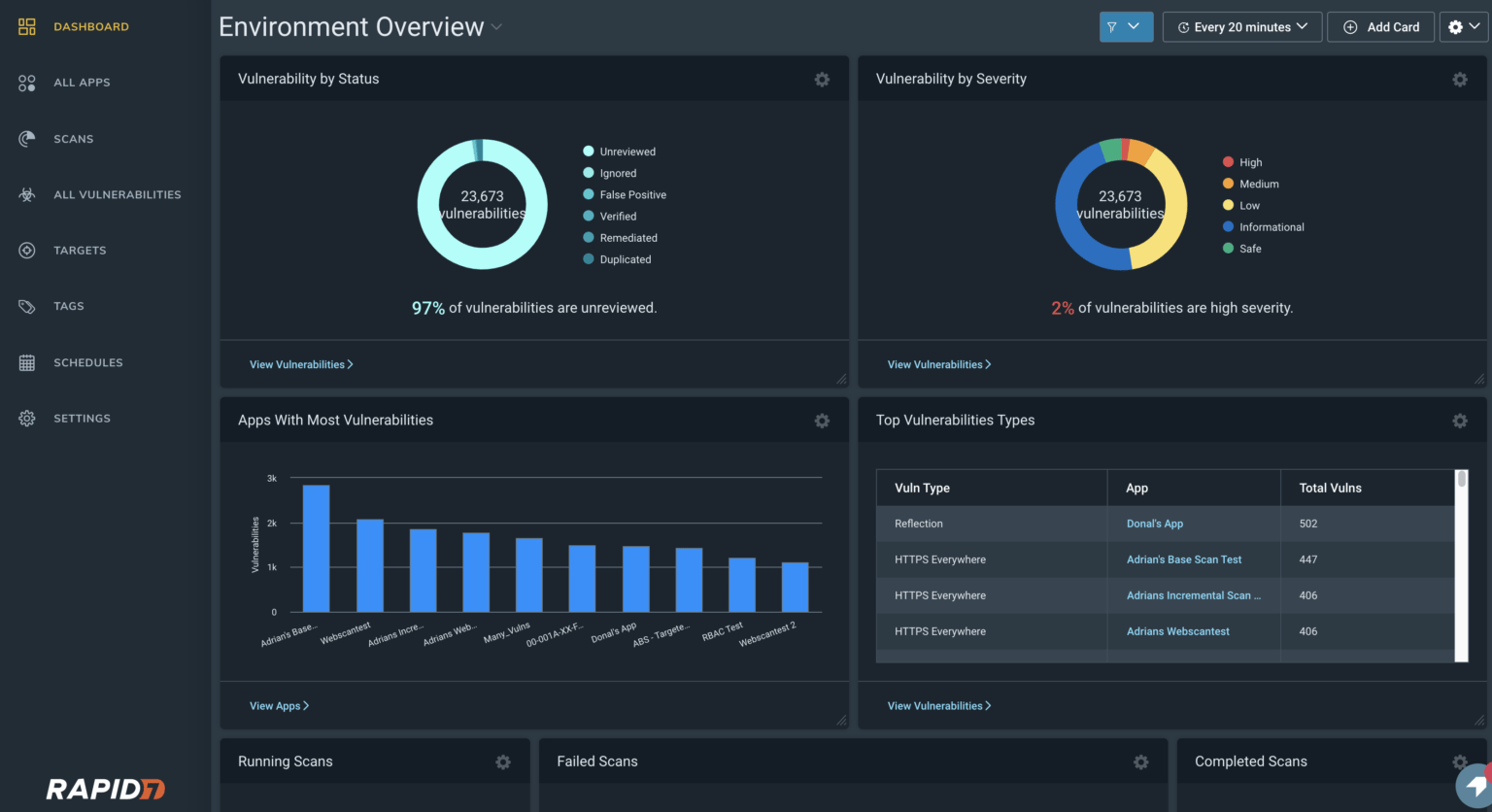
Features:
- Type of Scanner: DAST
- Scanner Capabilities: Network, Cloud, and Web Applications
- Accuracy: False Positives Possible
- Scan Behind Logins: No
- Integrations: Splunk, AWS, Microsoft
- Expert Remediation: No
- Deployment: On-Premise
- Pricing: $175/month
- Pros: Comprehensive coverage (VM, DAST, SIEM, SOAR), customizable dashboards, strong asset discovery and compliance features.
- Cons: Setup is complex, can be expensive, and gives false positives at times.
- Best Use Case: Enterprises requiring integrated vulnerability and incident response across cloud, endpoints, and apps.
- Security Compliance/Mapping: PCI DSS, HIPAA, GDPR mapping in scans, compliance-centric reporting.
Rapid7 is also a vulnerability scanner and tool for application security testing that provides vulnerability testing, risk management, and threat intelligence on various assets.
Their vulnerability scanner can detect over 1,80,000 vulnerabilities, from informational to critical level vulnerabilities, and more than 4,000 exploits under their Metasploit framework.
Experts Review
Why did we choose Rapid7?
Rapid7 provides a suite of security tools, including a vulnerability scanner that detects various vulnerabilities. Its comprehensive approach to vulnerability testing, risk management, and threat intelligence makes it a valuable tool for organizations seeking to improve their security posture.
10. Intruder

Features:
- Type of Scanner: DAST and ASTaaS
- Scanner Capabilities: Websites, servers, and cloud.
- Accuracy: False Positive Present
- Scan Behind Logins: Yes
- Integrations: GitHub, GitLab, Slack, Jira
- Expert Remediation: No
- Deployment: Cloud
- Pricing:$1,958/ year
- Pros: Easy setup, user-friendly, and automated compliance reporting.
- Cons: CLI focus can discourage GUI-oriented users, authentication domain lock-in for 30 days, and not effective for deep custom scans.
- Best Use Case: SMEs, IT/security teams needing fast vulnerability scans and ready compliance evidence.
- Security Compliance/Mapping: SOC 2, ISO 27001, PCI-DSS with one-click audit-ready reports and integrations to Drata & Vanta.
Intruder is a top-notch online vulnerability scanner and AST tool that helps avoid costly data leaks and breaches through vulnerability scanning. It offers continuous vulnerability management, compliance reporting and monitoring, and attack surface monitoring.
Intruder is a scalable solution that is flexible enough to scan websites for vulnerabilities, regardless of your company’s size or industry.
Explore the top Intruder.io alternatives and competitors to identify the best fit for your attack surface management strategy.
Experts Review
Why did we choose Intruder?
Intruder is a cloud-based vulnerability scanner that offers continuous vulnerability management and attack surface monitoring. Its scalability and focus on proactive security make it a good choice for organizations looking to identify and address vulnerabilities before they are exploited.
11. Checkmarx
Features:
- Type of Scanner: SAST and SCA
- Scanner Capabilities: Web applications
- Accuracy: False positives possible
- Scan Behind Logins: No
- Integrations: Jira, Slack, GitHub
- Expert Remediation: No
- Pricing: Quote on request
- Pros: Offers SAST/DAST/IAST leading to early vulnerability detection, seamless CI/CD integration, and strong compliance coverage.
- Cons: High false positives unless custom-tuned. Slow scans, expensive enterprise licensing, and complex setup.
- Best Use Case: Enterprise DevSecOps, securing web/mobile apps, regulated development (OWASP, PCI DSS).
- Security Compliance/Mapping: PCI-DSS, OWASP Top 10, GDPR, HIPAA, custom policy mapping in detailed reports.
Checkmarx is an enterprise-grade software exposure web application security testing tool used by over 14000 organizations worldwide, including government bodies. This SAST tool helps your developers accelerate their work in finding and fixing vulnerabilities.
The tool can scan across 25+ development frameworks, provides interactive AppSec training for developers, and is scalable with scope for collaboration for enterprise-level security testing.
Experts Review
Why did we choose Checkmarx?
Checkmarx is an enterprise-grade SAST tool that helps developers find and fix vulnerabilities early in the software development lifecycle. Its support for multiple frameworks and its focus on developer training make it a valuable tool for organizations looking to integrate security into their development processes.
Bonus: Veracode
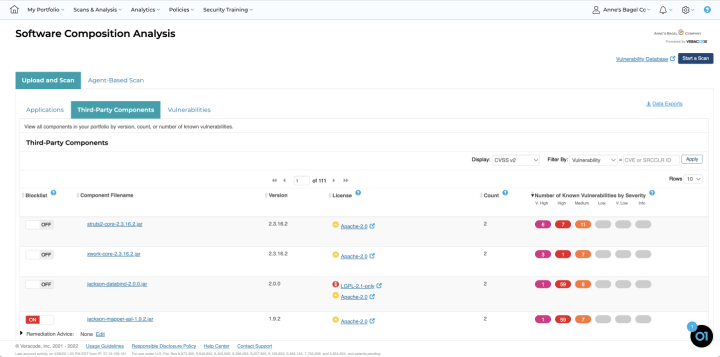
Features:
- Type of Scanner: DAST
- Scanner Capabilities: Web applications and Source Code Review
- Accuracy: False positives possible
- Scan Behind Logins: Yes
- Expert Remediation: Yes
- Deployment: SaaS
- Price: Quote upon request
- Pros: Comprehensive AST suite (SAST, DAST, SCA), strong governance, and detailed compliance analytics.
- Cons: Slow feedback cycles, alert fatigue from false positives, high cost for smaller orgs, and setup can be complex.
- Best Use Case: Enterprises seeking centralized governance, secure SDLC, and strict compliance mapping.
- Security Compliance/Mapping: PCI DSS, HIPAA, GDPR, industry policy templates, and audit-ready compliance reports.
Veracode is a popular scanner that offers multiple types of security testing: SAST, DAST, software composition analysis (SCA), and penetration testing. This online web application security testing tool is designed to cope with the speed of development that comes with DevOps.
The tool lets you scan hundreds of apps and APIs simultaneously, making it the perfect web application analysis tool for large enterprises. It can detect vulnerabilities in over 10 languages and popular libraries, such as RPM, Maven, PyPi, and NPM.
Experts Review
Why did we choose Veracode?
Veracode offers a comprehensive platform for application security testing, including SAST, DAST, SCA, and penetration testing. Its ability to scan hundreds of applications and APIs simultaneously makes it a suitable solution for large enterprises.
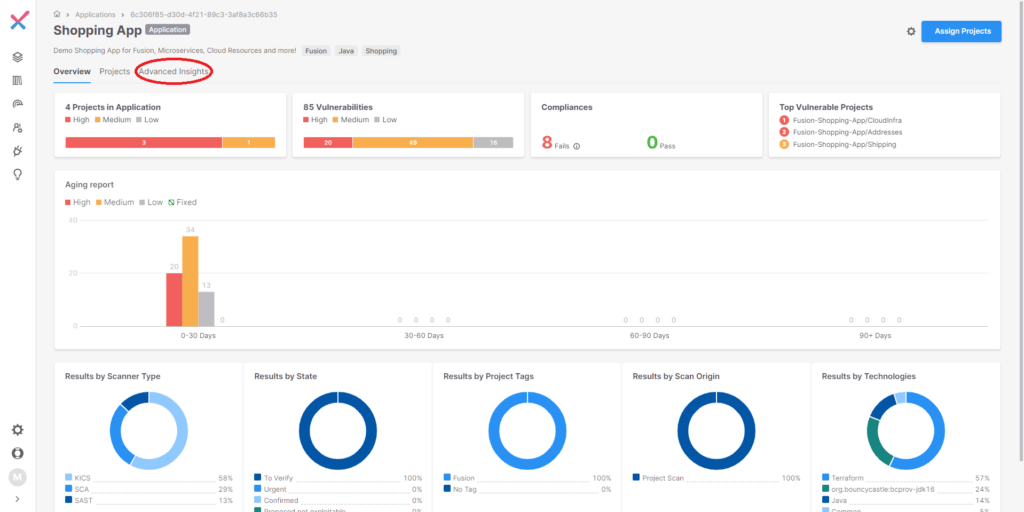
Types of Application Security Testing Tools
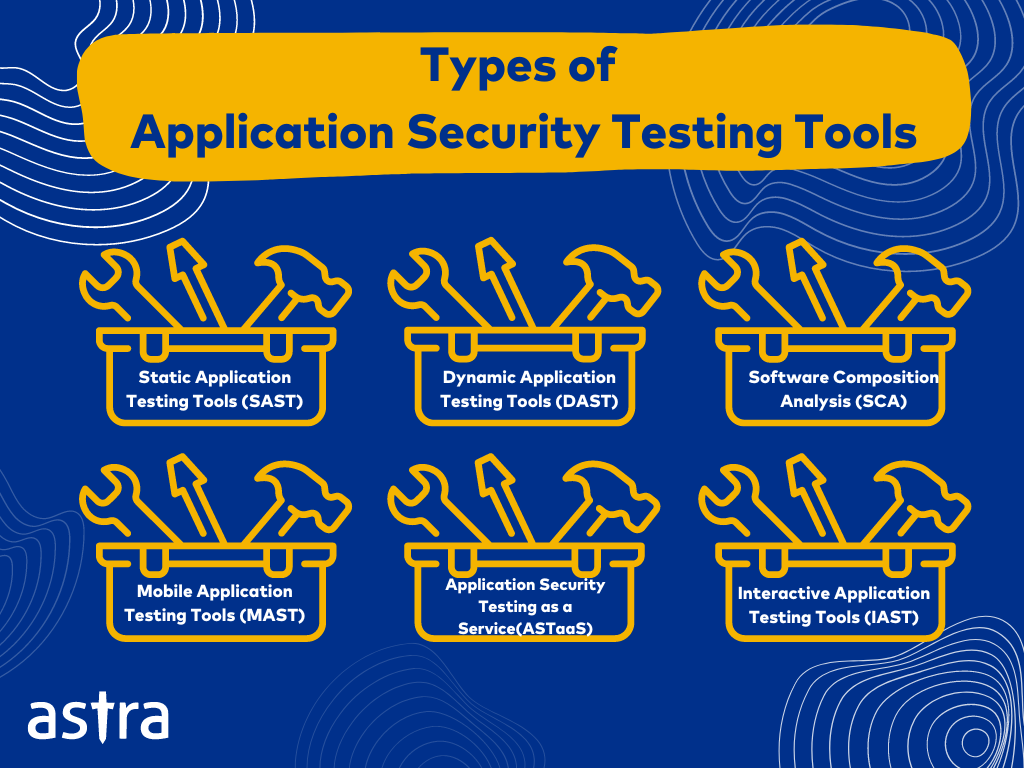
1. Static Application Security Testing (SAST)
Without executing the program, SAST tools help analyze the source code for weaknesses, vulnerabilities, and compliance violations. They are ideally used during the development phase by feeding them with the source code and architecture, like in a white-box test.
They help detect vulnerabilities like misconfigurations, defects in input validation, path traversal issues, etc., and are best for software development firms. Depending on the application’s size and features, these tools can complete the testing in a few hours or take up to a day.
2. Dynamic Application Security Testing (DAST)
DAST tools analyze applications in their running state for weaknesses and vulnerabilities. These tools are ideally used during the beta testing phase on the deployed environment to look for runtime vulnerabilities like server misconfigurations or CVEs like SQL Injection or XSS.
These tools are best for e-commerce websites, consumer applications, and other online services. Since they perform comprehensive tests on applications, a scan can take a few hours to a few days to complete.
3. Software Composition Analysis (SCA)
SCA tools help find weaknesses and vulnerabilities in software components, such as open-source components and libraries used in applications.
As such, these tools are best for applications using open-source and third-party dependencies to look for known vulnerabilities. They are easily integrated with the CI/CD pipeline to allow continuous monitoring during the development phase.
4. Database Security Scanning
Database security scanning tools scan database systems for vulnerabilities and weaknesses. Such tools are generally used for applications that process sensitive information, such as financial, personal, or health information.
These tools look for security misconfigurations, SQL Injections, authentication, and authorization issues to protect the data against breaches or misuse.
5. Interactive Application Security Testing (IAST)
IAST tools combine SAST and DAST tools, allowing a more hybrid approach to testing vulnerabilities in both the code and the executed application. These tools help identify static vulnerabilities, such as misconfigurations and information in source code, and dynamic vulnerabilities, such as injections or authorization errors.
6. Mobile Application Security Testing (MAST)
MAST tools identify weaknesses and vulnerabilities unique to the mobile environment. They help pinpoint weak encryption, insecure data storage, or other platform-specific vulnerabilities.
These tools could be SAST, DAST, or even both and can be used in various development life cycle stages. They can be integrated with the CI/CD pipelines for continuous monitoring during the development phase.
7. Application Security Testing as a Service
ASTaaS tools are vendors that provide security testing services on demand, allowing organizations to stay on top of vulnerabilities and compliance regulations.
Such tools cover a broad range of types of testing and provide comprehensive security assessments tailor-made for your applications’ needs.
8. Correlation Tools
Correlation application security testing tools help you correlate findings from different AST tools to reduce the noise from false positives and validate and prioritize critical vulnerabilities.
These tools benefit large enterprises with complex IT environments by helping with better vulnerability management and enhancing your overall security posture.
9. Test-Coverage Analyzers
Test-coverage analyzers determine what percentage of an application’s code is tested. These tools help organizations understand the efficiency of their AST process, and if they are running behind, they can try to optimize and accelerate the process. They play a crucial role in identifying lines of code that the SAST tools might fail to reach.
Why is Application Security Testing Important?
1. Continuous Assessment
These appsec tools allow applications to be monitored and analyzed continuously by seamlessly integrating with CI/CD pipelines.
This allows your developers to analyze security issues in the code in real-time, facilitating security at every stage of the development lifecycle.
2. Proactive Vulnerability Assessment
Proactive vulnerability assessment means identifying potential vulnerabilities in an application before attackers can exploit them.
Your development team can prevent application breaches and cyber attacks by conducting regular scans before attackers can exploit common vulnerabilities such as SQL injections.
3. Speed of Testing
Traditional code reviews and test plans are very slow to fit into the DevSecOps application development model. These tools perform comprehensive scans much faster than manual tests, which lets developers roll out new releases faster and without compromising the security of the applications.
Features in Application Security Testing Tools
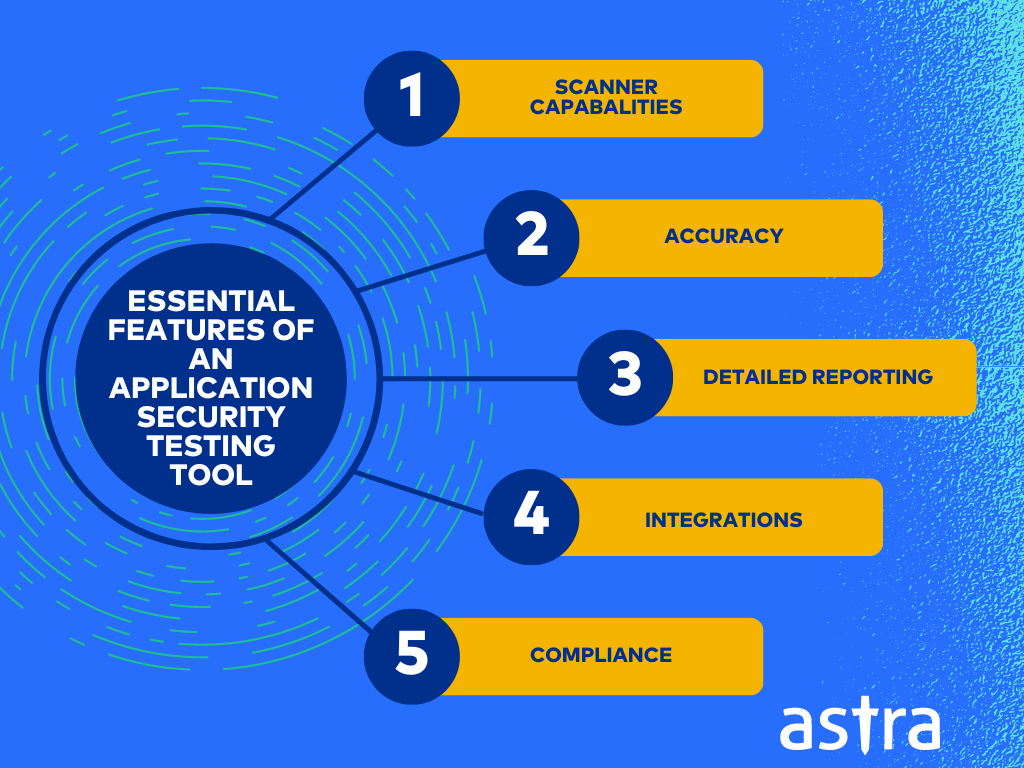
1. Scanner capabilities: The tool you choose should cover various vulnerabilities across different types of assets and environments.
2. Accuracy: The ideal tool is accurate, i.e., it should detect actual security issues and have fewer false positives. This ensures that security efforts are focused on genuine vulnerabilities.
3. Detailed Reporting: The application security testing tool should provide comprehensive reports prioritizing and remediating vulnerabilities. Check whether these tools have compliance reporting.
4. Integrations: The tool you choose should offer stable integrations with various security tools, such as SIEM and vulnerability management systems. This allows you to manage and remediate vulnerabilities efficiently.
5. Compliance: Your tool should facilitate adherence to compliance requirements of standards like GDPR, PCI-DSS, HIPAA, ISO27001, and others. Maintaining compliance allows you to build customer trust by securing their data and avoiding legal charges.
Final Thoughts
By integrating application security testing throughout the software development lifecycle, you can proactively identify and address vulnerabilities, significantly reducing the risk of cyberattacks. Using the right tools at every development phase can benefit the developers by saving them time and effort for security testing.
While selecting application security tools, consider features like robust scanning capabilities, high accuracy to minimize false positives, and seamless integration with your development environment to ensure efficient vulnerability detection and a smooth workflow.
FAQs
What are Application Security Testing Tools?
Application Security Tools are software solutions that help find, assess, and fix vulnerabilities in applications across development and deployment. They range from scanning source code to simulating attacks on running apps, enabling teams to strengthen security early and often.
What tool is recommended for Application Security testing?
Astra Security stands out as a hybrid VAPT platform offering both automated and manual penetration testing. It has benefits like zero false positives, CI/CD integrations, compliance coverage, expert remediation, and is also trusted by brands like SpiceJet and Dream11.
How do I choose the right application security tool for my team and app?
Choose tools based on your app’s architecture, tech stack, budget, and compliance needs. Combine SAST for early coding, DAST for live testing, IAST for deeper insights, and SCA for dependency scanning.
What are the different types of AppSec testing methods?
Important AppSec methods include SAST (white-box code scanning), DAST (black-box runtime testing), IAST (hybrid real-time analysis), MAST (mobile-specific security), and SCA (third-party component scanning).
How do Application Security testing tools fit into DevSecOps workflows?
AppSec tools integrate into DevSecOps by shifting left. They automate SAST, DAST, and SCA early in CI/CD pipelines. They enable continuous scanning, compliance, and collaboration between dev, security, and ops teams.
Additional Resources on Security Testing
This post is part of a series on Security Testing. You can
also check out other articles below.

- Chapter 1: What is Security Testing and Why is it Important?
- Chapter 2: Security Testing Methodologies
- Chapter 3: What is Web Application Security Testing?
- Chapter 4: How to Perform Mobile Application Security Testing
- Chapter 5: What is Cloud Security Testing?
- Chapter 6: What is API Security Testing?
- Chapter 7: What is Network Security Testing?
- Chapter 8: A Complete Guide to OWASP Security Testing?
- Chapter 9: What is DAST?
- Chapter 10: What is SAST?