CTOs report their main challenges as internal opposition, information overload, evolving threats, and the complexity of achieving full security coverage. Sounds familiar? While your organization reaps the benefits of rapid SaaS adoption, you are left managing an increasingly complex security landscape where traditional perimeter-based approaches simply don’t work.
The reality is that effective SaaS security requires purpose-built tools designed for cloud-first environments. This guide cuts through the noise and lists the top SaaS security tools chosen by CISOs. This covers continuous vulnerability testing to real-time threat detection, helping you build a robust security posture without sacrificing DevOps efficiency.
Protect your SaaS stack from hidden threats. [Book a free demo ->] and see how advanced security and monitoring tools keep your data safe.
Top 7 SaaS Security Tools
- Astra Security
- Intruder
- Cloudflare
- Orca Security
- Rubrik
- TOPIA
- Zscaler
Comparing Top SaaS Security Tools
| Tools | Offerings | Pros | Cons |
|---|---|---|---|
| Astra Security | Continuous vulnerability assessment, manual pentest, compliance assistance | 15000+ tests, CI/CD integration, zero false positives, publicly verifiable certification | Only 1-week free trial available. |
| Intruder | Internal and External Vulnerability Scanning, Continuous Penetration Testing | Pro-active scanning with real-time alerts. Applies latest security patches for safety. | Does not provide manual penetration testing. |
| Cloudflare | Web Application Firewall, Encryption, DDoS Protection | Largest server networks. Scalable services. Provides security to anything from servers to domains and installations. | The main focus is on protecting public-facing applications like websites and APIs. |
| Orca Security | Shift Left Security, Identity Access, Management, Malware Detection. | Aids in compliance enforcement. Provides protection for high-risk data like PII. Provides alert on Slack or other mediums when configured. | Quote available on contact. |
| Rubrik | Cloud Security, Secure backups, Ransomware Protection | Provides security for hybrid, virtual and physical platforms. Unified cloud backups with precise data recovery. | Pricing is only available on demand. |
| TOPIA | Patchless Protection, Network Scanners, 0-Day Detection | Emphasis on vulnerability management. Assured cloud security over multiple vendors. | Much more applicable for larger enterprises. |
| Zscaler | Ransomware Protection, Cloud Security, SSL Inspection, Zero Trust Exchange | Offers services like file recovery and integrity monitoring. Inspection of SSL traffic for malicious activity. User-friendly interface. | Pricing options are available only on contact. |
7 Best SaaS Security Tools (2026)
1. Astra Security [Get Started]
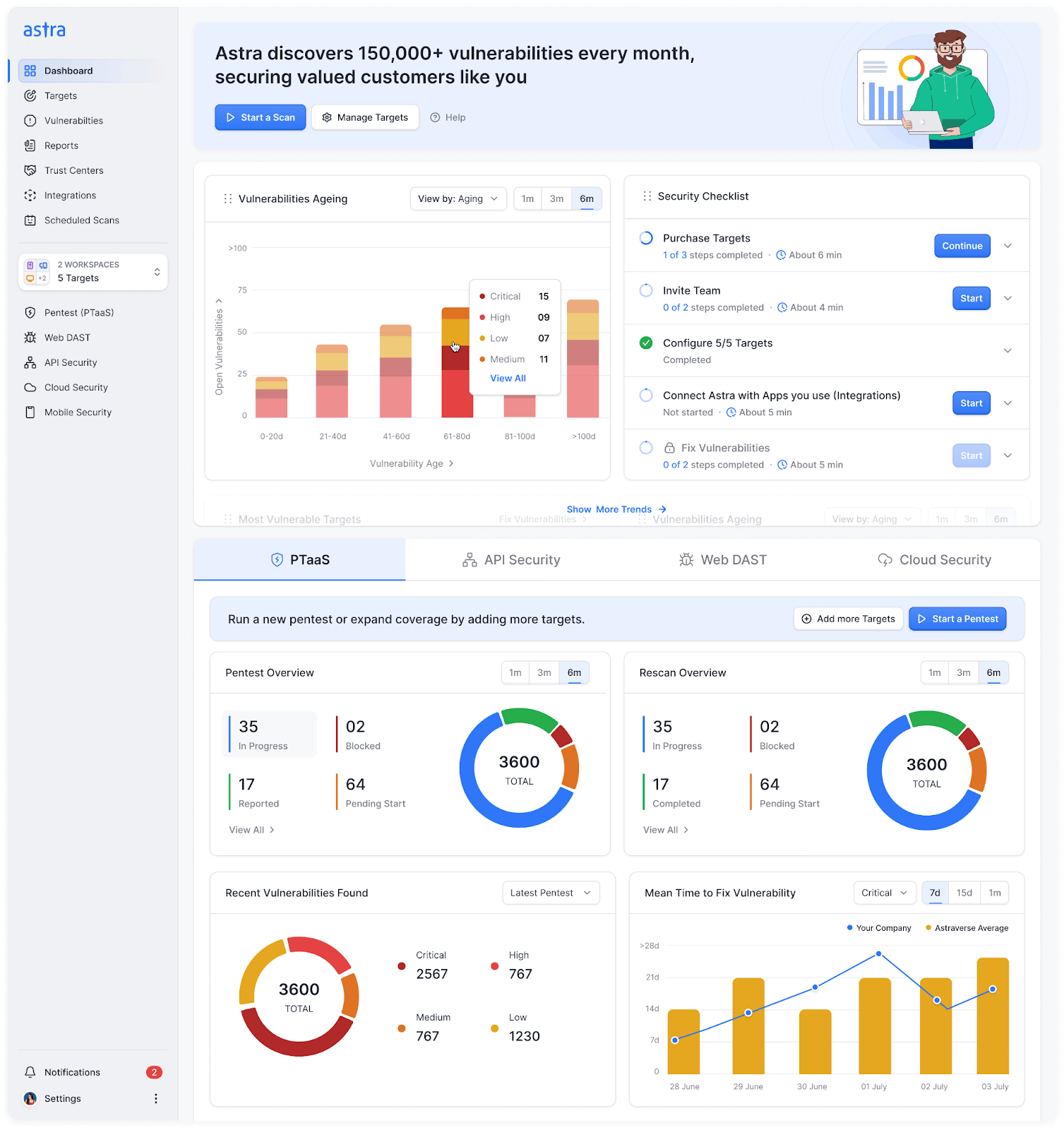
Astra Security is built for teams in Enterprises that need complete visibility and fast fixes without the noise. Astra Security’s PTaaS integrates automated coverage with expert-led testing so you get signal, not guesswork.
Key security features include 15K+ automated tests, a CXO-friendly dashboard, guided remediation, and integrations that fit neatly into release workflows. Customers rate Astra highly for accuracy and support, too.
Key Features:
- Continuous vulnerability assessment across web apps, APIs, cloud, and microservices with expert vetting for zero false positives.
- Industry-mapped tests covering OWASP Top 10 and SANS 25 threats with practical fix paths and developer-ready reports.
- CI/CD integrations that block risky builds and trigger targeted rescans on merges and releases.
- Clear risk scoring and business impact summaries that help teams prioritize the next right fix.
- Compliance support aligned to SOC 2, ISO 27001, HIPAA, and PCI with audit-friendly evidence trails.
- Publicly verifiable certificates that help speed security reviews and close deals faster.
- G2 rating of 4.6 out of 5 from 150+ verified customers.
2. Intruder
Intruder focuses on proactive vulnerability management for lean security teams. It identifies assets, prioritizes exploitable risk, and keeps a lookout between releases so issues do not stay put.
The platform fits SMB and mid-market needs with simple onboarding and useful alerting that lands in your existing tools.
Key Features:
- External and internal vulnerability scanning that tracks your attack surface as services and IPs change
- Contextual risk scoring that surfaces what is reachable and poses a threat first
- Integrations for Jira, Slack, and Microsoft Teams to streamline triage and ownership
- Smart notifications when new CVEs impact your specific assets, so you respond quickly
- Reporting built for stakeholders and auditors with trend lines and remediation status
Curious about better options? Compare leading Intruder.io alternatives with stronger integrations and broader scanning coverage.
3. Cloudflare
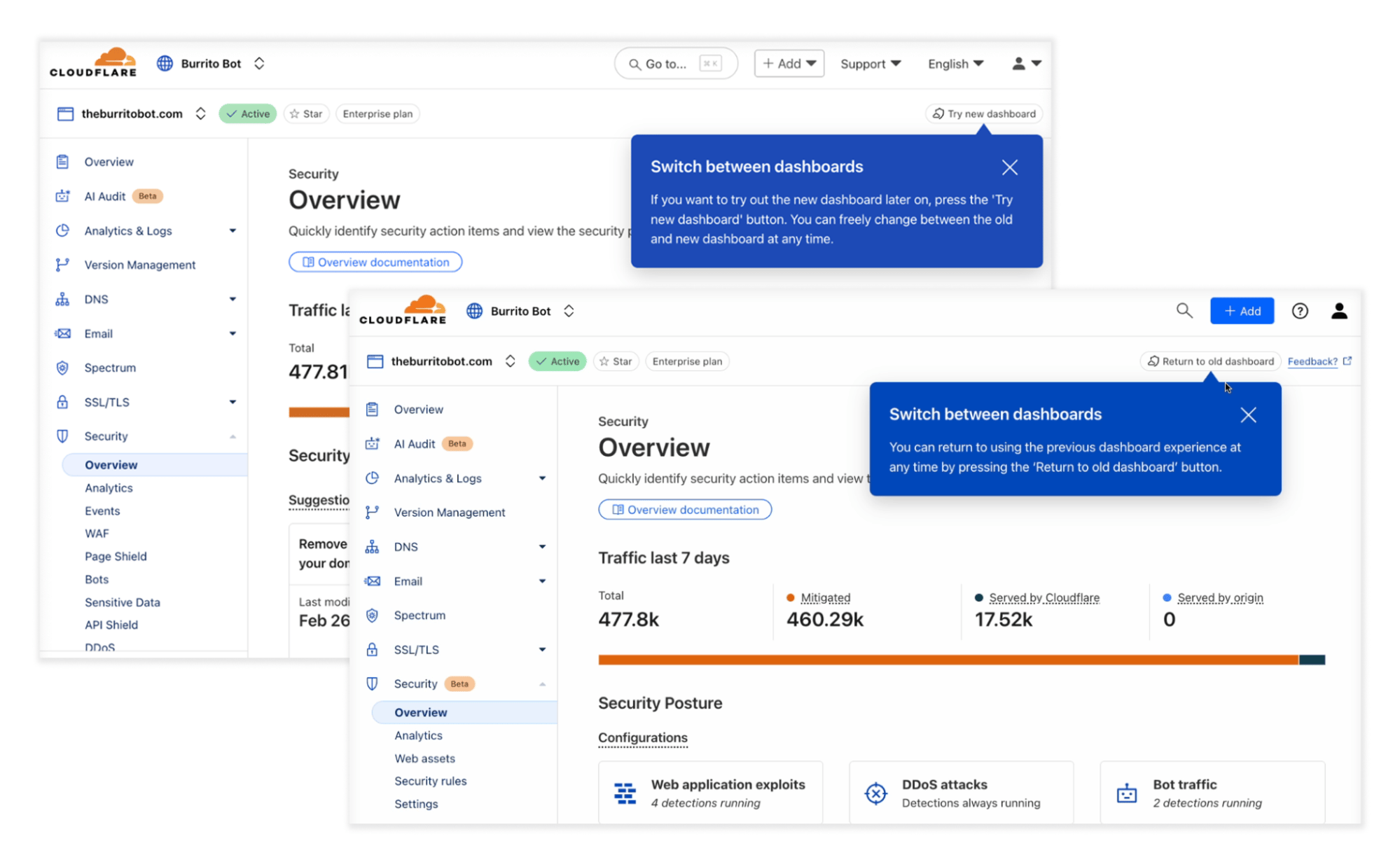
Cloudflare is a foundational layer of security for the modern internet. Its global anycast network acts as a massive shield, sitting between your applications and the chaos of the public web.
Cloudflare goes beyond basic brute force defenses with a smart WAF. It blocks harmful traffic right before it hits your origin servers. Plus, its zero-trust and SASE solutions ensure only approved users and devices get into your internal apps.
Key Features:
- Has the world’s largest server network for superior DDoS protection and low-latency performance.
- Provides secure, high-speed connectivity between devices and cloud applications globally.
- Secures resources like cloud applications, web services, and applications.
- Enforces zero-trust access controls for secure remote access to internal tools and applications.
4. Orca Security
Orca provides agentless coverage across AWS, Azure, and Google Cloud. It creates a full context graph from workloads, identities, data, and configurations to surface toxic combinations.
Security teams choose Orca to consolidate CSPM, CWPP, and DSPM into one platform with prioritized findings.
Key Features:
- Agentless deployment that scans workloads, containers, and serverless without friction.
- Unified findings that merge misconfigurations, vulnerabilities, IAM risk, and data exposure into one view.
- Data discovery for sensitive PII and secrets with blast radius context for faster decisions.
- Shift left rules for IaC and CI/CD to catch issues before deployment.
- Integration with ticketing and messaging tools for streamlined remediation loops.
5. Rubrik
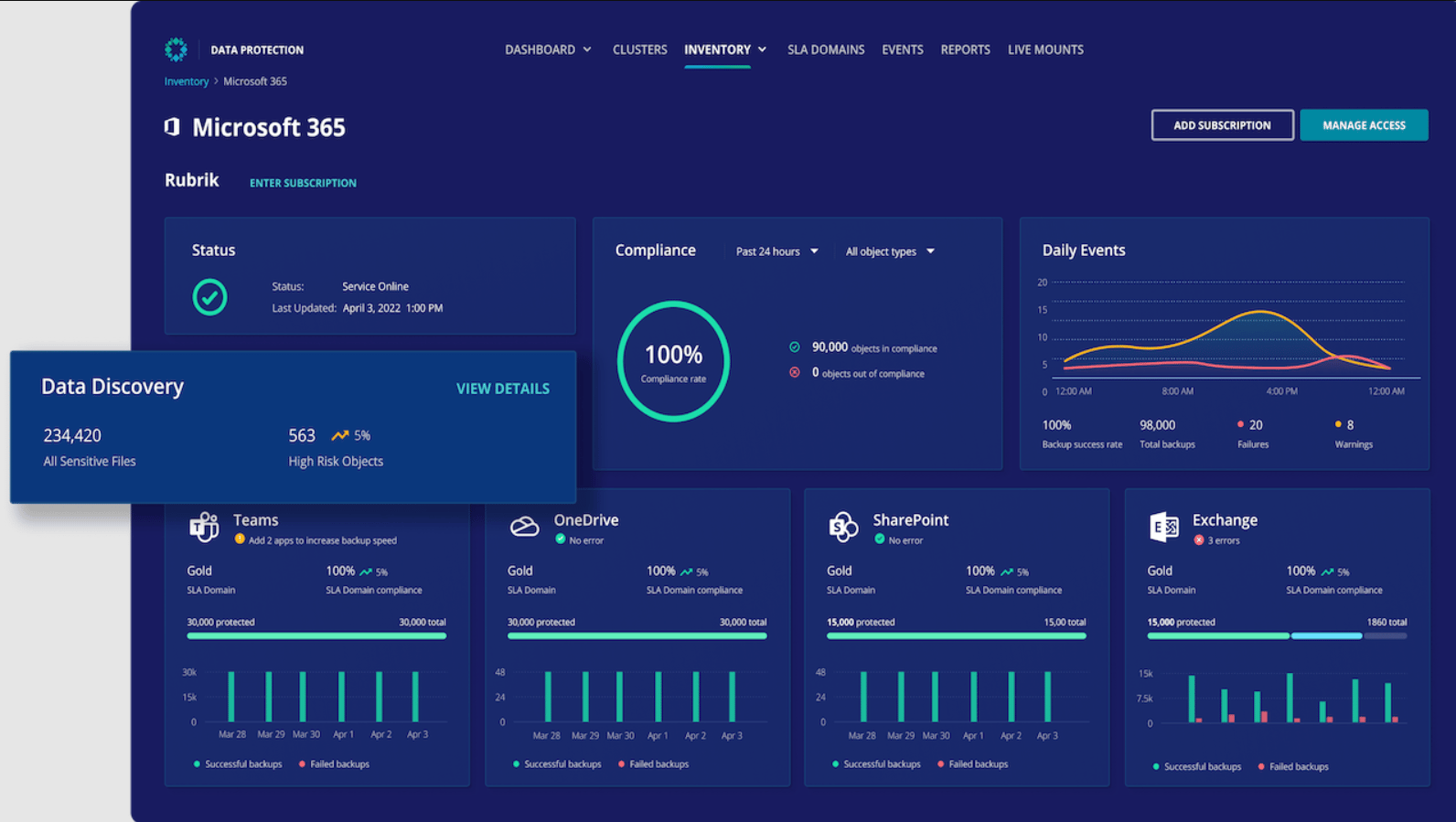
Rubrik focuses on data security for hybrid and cloud environments. It gives you immutable backups, rapid recovery, and threat-aware analytics. This way, ransomware has less room to harm your business.
Enterprises use it to protect critical SaaS, cloud, and on-prem data and to prove cyber readiness to the board.
Key Features:
- Sensitive data discovery and scanning so you understand exposure in backups and live systems.
- Threat monitoring that ties indicators to backup snapshots for clean recovery points.
- Posture management to harden configurations across clouds and SaaS data sources.
- Role-based access and MFA with detailed audit trails for compliance evidence.remediation loops.
6. Vicarius TOPIA
Vicarius TOPIA (vRx) targets vulnerability remediation speed. It analyzes assets, ranks threats by exploitability, and protects critical apps while patches are planned.
Teams like the lightweight rollout and the ability to buy time with in-memory protection for high-risk apps.
Key Features:
- Real-time asset discovery with risk-based prioritization that highlights exploitable paths.
- Patchless protection that protects applications in memory via binary instrumentation.
- Dashboards for vulnerability trends and remediation throughput that help drive SLAs.
- Integrations with ticketing and collaboration tools to automate ownership and status.
7. Zscaler
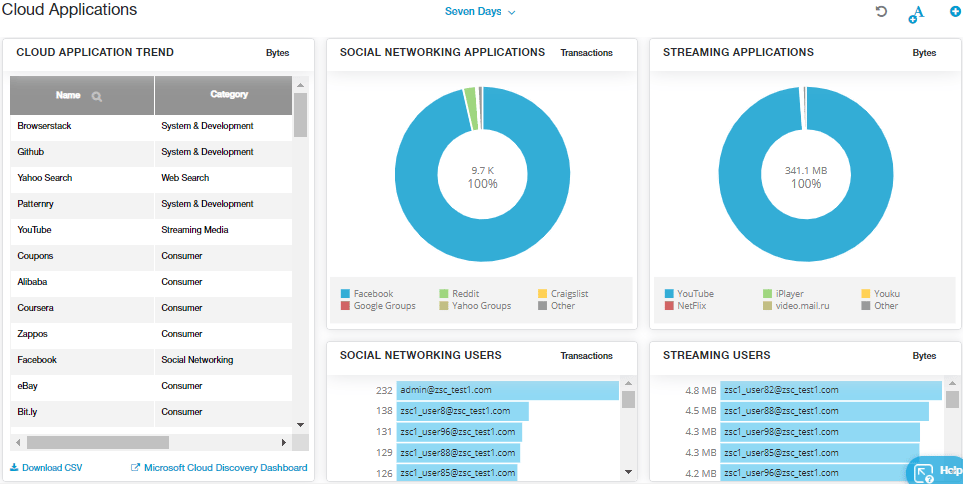
Yet another leading cybersecurity provider, Zscaler, provides users with a tight zero-trust security posture that can be managed across all aspects, thus making navigation easy and the security posture more secure.
Large organizations adopt Zscaler to reduce attack surface, inspect encrypted traffic, and simplify branch and remote security.
Key Features:
- Distributed cloud-based security for web, email, and mobile computing regardless of client locations.
- Zero Trust access to private applications with identity-centric policy and segmentation.
- Sandboxing and advanced threat protection to detonate risky files before delivery.
- Rich compliance reporting to support audits and third-party reviews across frameworks.
Why is SaaS Security Important?
1. Compliance
Securing SaaS forms an important part of maintaining compliance with regulatory standards and laws like ISO 27001, HIPAA, or PCI-DSS. Compliance is becoming crucial for all companies globally.
SaaS security ensures the continued compliance of the SaaS server and application, thus reducing the risk of non-compliance and subsequent penalties or other charges. Because of their compliance, SaaS or cloud service providers are attractive candidates for potential customers.
2. Data Security
One of the primary reasons for implementing SaaS or cloud security solutions is data safety. This can be client data or software-related information, all of which are highly confidential in nature and, as such, require continuous monitoring, vulnerability assessments, and regular patch updates to ensure their continued safety.
Continuous assessments form the crux of maintaining the safety and security of data in SaaS.
3. Reliability
Having SaaS security and implementing the best measures makes the cloud service provider seem more reliable and trustworthy. It raises the bar for customer confidence due to increased vigilance in place to protect their applications and data throughout.
4. Something Sales Team Can Be Proud Of
Having good SaaS security tools in place is a vital component for companies that are looking for a SaaS provider. Here, cloud services with a great SaaS security system with continuous scans, monitoring, and safety measures have the upper hand.
This is because the sales team can use this as an attribute that appeals to potential customers.
Key Features of SaaS Security Tools
1. Data Security
Ensure that the SaaS security tools you have shortlisted have good measures in place to ensure data safety. This can include enabling data encryption like Transport Layer Security (TLS) to protect data in transit. It can also be enabled for data at rest, along with multiple levels of security.
Another method is to allow the encryption keys to remain with SaaS customers, thus ensuring that server-side employees can not gain access to confidential data. Continuous vulnerability assessments are also crucial in ensuring the data remains safe since the discovered vulnerabilities will be immediately fixed.
2. Continuous Assessments
Continued vulnerability assessments help identify vulnerabilities in the security system. If such vulnerabilities are discovered, they are mentioned in a detailed report with remediation measures. Vulnerability assessments are much easier to carry out frequently.
A good vulnerability scanner should be able to detect any known vulnerabilities, OWASP 10 and SANS 25. Vulnerability assessments should also be done every time a feature is updated or introduced into the platform form, as it could have hidden vulnerabilities. These are also relevant to maintaining compliance.
3. Security Audits
This is a systematic analysis of the security protocols in place to protect your organization. Cloud security tools that provide audits analyze every aspect of the security measure, unlike a vulnerability assessment or a penetration test, which works to find and exploit vulnerabilities.
It generally focuses on hardware and software configurations, physical security measures, devices used, etc. SaaS security auditors are crucial for achieving and maintaining compliance with regulations like SOC2 and ISO 27001 and standard laws like HIPAA and PCI-DSS.
To ensure maximum safety, audits must be conducted at least once or twice a year.
4. Compliance
As mentioned earlier, compliance is an important aspect of SaaS. Therefore, when choosing a SaaS security tool, it is crucial to assess what compliances they adhere to and whether they align with regulatory compliances standards such as HIPAA, GDPR, PCI-DSS, SOC2, and ISO 27001.
With each regulatory body, the standards that need to be met may vary. SOC2 is a certification that focuses more on cloud security solutions and continuous monitoring of the safety protocols implemented. Therefore, ensure your SaaS security tool provides continuous compliance checks.
5. Integration
Make sure that the SaaS security tools you are considering provide integrative possibilities. This will enable you to integrate the SaaS security tool and its testing features into your CI/CD pipeline. This ensures that every code update is scanned for vulnerabilities automatically before hitting the production phase.
This essentially allows your organization to move from DevOps to DevSecOps, a methodology where security is also given prime importance. A SaaS security tool’s integrative capacities allow it to provide security and testing to your projects across multiple platforms.
Best SaaS Security Practices To Follow
1. SaaS Security Checklist
Keep a tight, action-oriented checklist that covers encryption, access controls, backups, compliance status, and incident playbooks. Make it a living document and review it after every major release or architecture change.
2. Access Management
Enforce least privilege with role-based access and require MFA for all admin and remote logins. Automate user provisioning and run quarterly access reviews so old permissions do not become attack paths.
3. Regular Penetration Tests
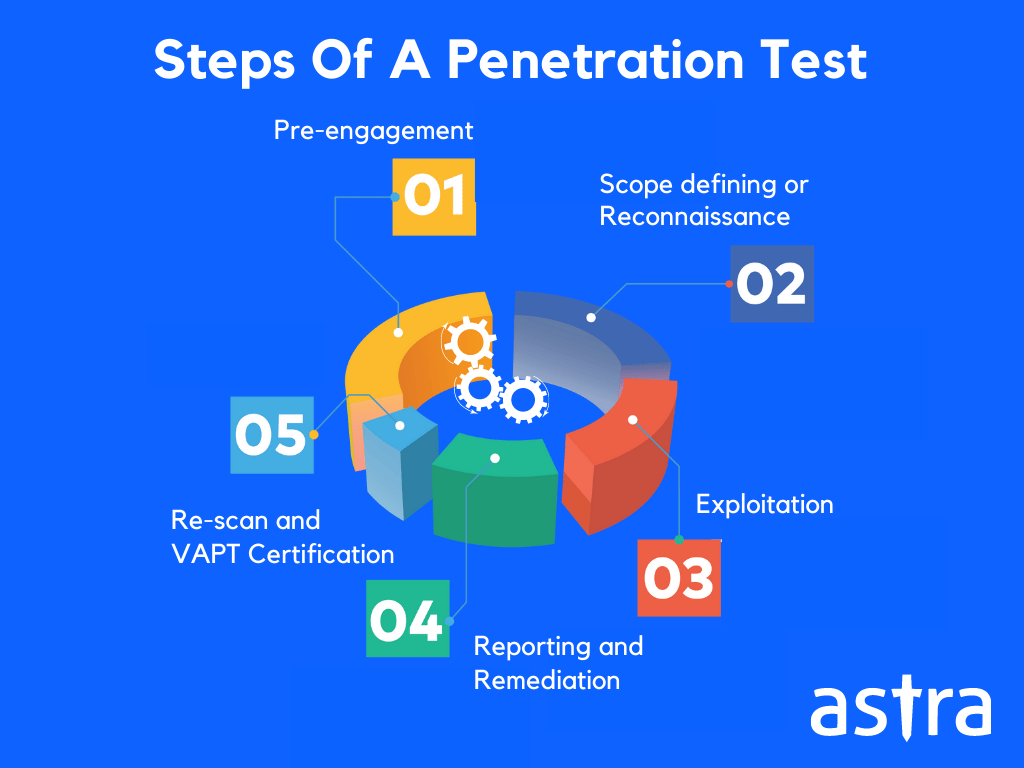
Run automated scans on every build and schedule human expert-led pentests at least twice a year or after big changes. Treat findings as tickets with SLAs and verify fixes with targeted rescans.
4. Incident Response Planning
Define clear roles, runbooks, and communication templates for internal and customer notification. Back up critical data with immutable snapshots and practice recovery drills regularly so the response is fast and confident.
Final Thoughts
Keeping your SaaS application secure doesn’t have to be a headache. Leveraging a SaaS security tool can streamline security measures, ensure compliance, and gain peace of mind.
From vulnerability assessments to real-time threat detection, while the above list is not exhaustive, tools like Astra Security can help fulfill your specific security needs. Moreover, with the right security partner in place, you can confidently embrace the convenience and cost savings of SaaS, knowing your data is safe.
FAQs
1. Why is SaaS more secure?
Software as a Service or SaaS is more secure since it most often employs Transport Layer Security to protect data in transit, while encryption is also offered for data at rest.
2. Who is responsible for SaaS security?
Generally, SaaS vendors are responsible for security, as they must ensure that their cloud servers, physical infrastructure, and application security are top-notch. However, SaaS customers must also do their due diligence before opting for a SaaS vendor to ensure the maximum safety of sensitive data.
3. What is the relevance of SaaS security?
SaaS security is relevant as it ensures application compliance and data security and helps in incident recovery if good policies are implemented. It also makes applications less vulnerable to external attacks.
Additional Resources on Security Testing
This post is part of a series on Security Testing. You can
also check out other articles below.

- Chapter 1: What is Security Testing and Why is it Important?
- Chapter 2: Security Testing Methodologies
- Chapter 3: What is Web Application Security Testing?
- Chapter 4: How to Perform Mobile Application Security Testing
- Chapter 5: What is Cloud Security Testing?
- Chapter 6: What is API Security Testing?
- Chapter 7: What is Network Security Testing?
- Chapter 8: A Complete Guide to OWASP Security Testing?
- Chapter 9: What is DAST?
- Chapter 10: What is SAST?









