Bitcoin worth $72 million was robbed from one of the largest crypto exchanges named Bitfinex due to stolen keys. We’ve seen many instances in the past few years where blockchain solutions were targeted with data theft and cyberattacks – which makes this technology non-immune to cyberattacks even considering its default strong security factor.
In this complete guide, we will be discussing Blockchain technology, how it works, and how to secure it from cyberattacks with the best secure coding practices and Blockchain penetration testing.
What is Blockchain Security?
Blockchain security is a comprehensive risk management procedure achieved via the implementation of cybersecurity frameworks, security testing methodologies, and secure coding practices to protect a blockchain solution. Blockchain security protects blockchain solutions from online fraud, breaches, and other cyberattacks.
Latest on Blockchain Security
The primary benefit of using blockchain technology is that it ensures security in transactions due to its principles of cryptography, decentralization, and consensus. A recent report states that the worldwide blockchain market is expected to be valued at $20 billion in the year 2024.
Right now, 69% of banks are exploring different avenues regarding blockchain tech to make their services safer, consistent, and straightforward. Here are a few examples of recent cyberattacks on blockchain:
- A VC firm named Decentralized Autonomous Organization (DAO) was a target of a code exploitation attack where it lost more than $60 million worth of Ether cryptocurrency.
- Another crypto exchange named Bithumb was recently hacked where the data of 30K users were compromised and $870K worth of bitcoin was stolen in a suspected insider job.
Organizations today are leveraging Blockchain technology for managing distributed databases, digital transactions, cybersecurity, and healthcare to build blockchain-based solutions for their customers. While the adoption of blockchain has brought many advantages for worldwide organizations, it has also attracted many cybercriminals to penetrate the technology and target organizations with cyberattacks.
What is Blockchain?
Blockchain is a technology that allows users and organizations to store and process data with the structured distributed blocks present in a blockchain network. Each new block stores a transaction or a bundle of transactions that is connected to all the previously available blocks in the form of a cryptographic chain.
How Blockchain Works?
Blockchain works as a distributed network that enables decentralization of data which makes it more secure and hard to tamper technology.
It is a decentralized public ledger network that allows organizations to connect to it via nodes for data storage and processing. The data stored in blocks can be accessed with verification, validation and consensus by the original entity that wants to store/process the data.
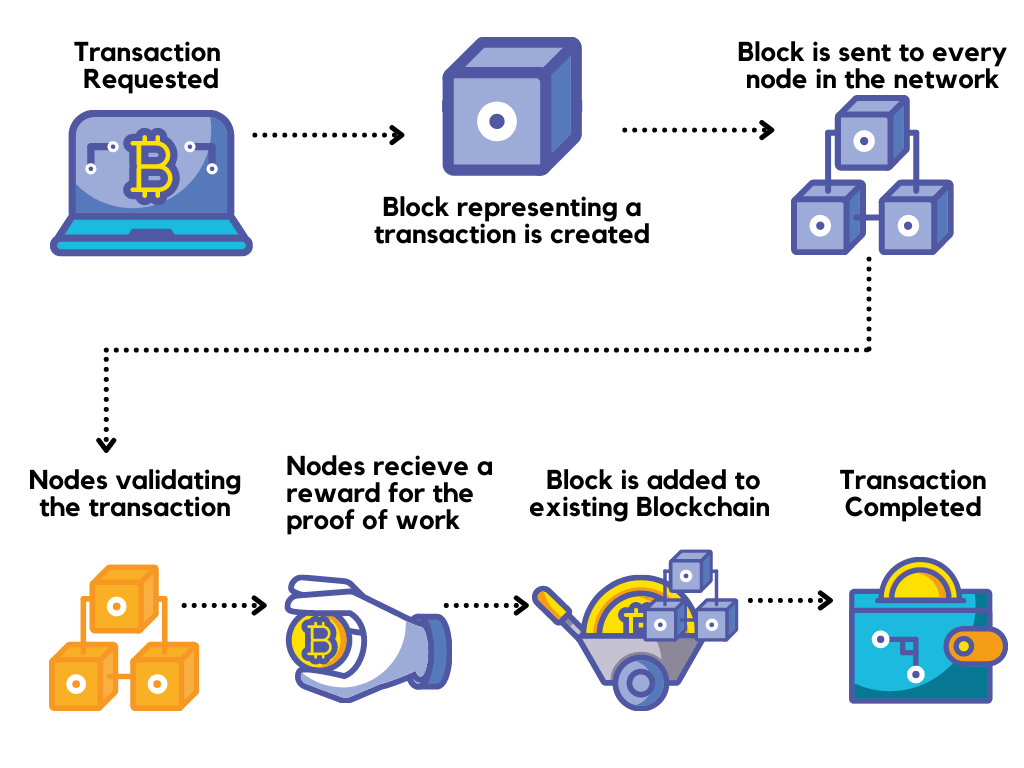
In the above image, as you can see, whenever a transaction is requested by the user using a blockchain-based application, a respective block is created in the blockchain network for storing the data of that transaction. Then that block is sent to every node in the distributed peer-to-peer network that further validates the transaction. After the validation, nodes of the network receive a reward for the proof of work (which is an agreement between the various nodes – also known as distributed consensus). Then, the block gets added into the existing Blockchain and the user gets a successful transaction.
The reason why the blockchain has acquired such a lot of adoration is that:
- It’s anything but claimed by a single entity, therefore it is decentralized
- Blockchain stores data cryptographically
- Data tampering in Blockchain is nearly impossible
- The blockchain is transparent which makes it untraceable
What are the different types of Blockchain?
There are three types of blockchains that exclude traditional databases and DLT. As follows:
Type 1. Public Blockchains
All transactions that happen on public blockchains are completely transparent, implying that anybody can analyze the transaction subtleties. Ex: Bitcoin and Ethereum.
Type 2: Private Blockchains
All transactions that occur on private blockchains are private and are simply accessible to the members of the system that have been allowed to join the private blockchain network. Ex: Hyperledger and R3 Corda.
Type 3: Consortium Blockchains
Consortium blockchains are quite similar to private blockchains. The main difference between them is that consortium blockchains are not governed by a single entity, it is governed by a group. Participants in consortium blockchains could incorporate anybody from national banks to governments, to supply chains.
Best Practices for building secure Blockchain solutions?
- Define and enforce endorsement agreements based on business contracts.
- Enable identity and access management (IAM) controls to handle data access in the blockchain.
- Execute suitable tokens like OAUTH, OIDC, and SAML2 to perform user authentication, verification, and authorization.
- Securely store identity keys.
- Use a privileged access management (PAM) solution to secure blockchain ledger entries after suitable business logic.
- Safeguard API-based transactions with API security best practices.
- Use a data classification approach to safeguard data or user information.
- Use privacy-preserving technologies for sensitive information.
- Use standard TLS for internal and external communications.
- Implement multi-factor authentication.
- Keep strong cryptographic key management.
- Leverage hardware security module (HSM) and security incident and event management (SIEM).
- Do regular vulnerability assessment and penetration testing (VAPT)
- Patch security loopholes to protect blockchain-based applications from vulnerabilities and data breaches.
- Get an industry-recognized security certification for your Blockchain solution.
- Enforce compliance and other security controls for the solution.
What is Blockchain penetration testing?
Blockchain penetration testing is a security assessment process done by ethical hackers or security professionals to test the security strength of the blockchain-based solution or application.
The main aim of blockchain penetration testing is to uncover vulnerabilities and security loopholes and identify misconfiguration errors in the solution. By performing Blockchain penetration testing, organizations get insights on the overall security posture of their blockchain security and also allow them to fix the potential weaknesses for their blockchain-based solutions or applications.
How to do Blockchain Penetration Testing?
To make it easy to understand, we’ve divided the blockchain penetration testing into the following 3 phases:
Phase 1: Information Gathering and Threat Modeling
In this phase, you can understand and analyze the business and functional requirements.
This phase includes:
- Understanding Blockchain architecture
- Finding threat entry points within the organization
- Gathering of publicly available data on potential exploits
- Evaluate Smart Contract Business Logic
- Setting objectives for conducting security testing
- Full test strategy designing
- Checking Compliance readiness
- Setting up the testing environment
- Creation of test data
Phase 2: Testing/Discovery
In this phase, you can use the data acquired in the first phase to play out the active testing of your blockchain to decide its development level estimated against best practices and industry guidelines.
This phase includes:
- API Security Testing
- Functional Testing
- Automatic and Manual Blockchain Security Analysis
- Blockchain Static and Dynamic Testing
- Network Vulnerability Assessment
- Application Vulnerability Assessment
- Blockchain Integrity Assessment
- Documenting Testing Discoveries
Phase 3: Exploitation
In this phase, the objective is to use any weaknesses or security loopholes found in the Discovery stage. This is frequently done manually to get rid of false positives. The exploitation phase also involves the exfiltration of data from the target and looking after perseverance.
This phase includes:
- Verifying Security Weaknesses and Vulnerabilities
- Exploiting Security Weaknesses and Vulnerabilities
- Network Penetration Testing
- Web Application Penetration Testing
- Test against Social Engineering Attacks
- Review and Document Discoveries
Make your Blockchain solution the safest place on the Internet.
Secure it using this ultimate blockchain security checklist.

What are the Blockchain Security Testing tools?
- SWC-registry – Smart contract weakness classification and test cases.
- MythX – It is a smart contract security analysis API that supports Ethereum, Quorum, Vechain, Roostock, Tron, and other EVM-compatible blockchains.
- Echidna – It is a Haskell program designed for fuzzing/property-based testing of Ethereum smarts contracts.
- Manticore – It is a symbolic execution tool for the analysis of smart contracts and binaries.
- Oyente – A static analysis tool for smart contract security.
- Securify 2.0 – Securify 2.0 is a security scanner for Ethereum smart contracts.
- SmartCheck – Static smart contract security analyzer.
- Octopus – It is a security analysis framework for the WebAssembly module and blockchain smart contract.
- Surya – Surya is a utility tool for smart contract systems.
- Solgraph – Generates a DOT graph that visualizes the function control flow of a Solidity contract and highlights potential security vulnerabilities.
- Solidity security blog – Contains a comprehensive list of crypto-related hacks, bugs, vulnerabilities, and preventative measures.
- Awesome Buggy ERC20 Tokens – A collection of vulnerabilities in ERC20 smart contracts with tokens affected
Professional Blockchain Security Audit by Astra Security
Astra Security offers a wide range of cybersecurity solutions including security audit and penetration testing for Blockchain-based solutions and applications. Security engineers at Astra Security perform hacker-style security testing that covers real-life attack scenarios and vulnerability exploitation on a Blockchain network. In-depth security audit and penetration testing for Blockchain include a thorough audit of static & dynamic code, business logic errors, payment manipulation flaws, misconfigurations, testing for known CVEs, and much more.
Moreover, the security expert team of Astra makes sure that no vulnerability goes unseen during the testing process.
Further, Astra’s collaborative VAPT dashboard gives you detailed vulnerability reporting and steps to fix each vulnerability. You can also talk to your designated security expert directly.
After every successful audit or pentest, you can get the industry-recognized publicly verifiable VAPT certificate from Astra.
Conclusion
Blockchain offers multiple security measures for the solutions that are built on it. However, due to lack of governance and exploitable vulnerabilities makes it not immune to cyberattacks. Therefore, performing a Blockchain security audit or penetration testing becomes important for your business. The sooner you identify blockchain security loopholes the sooner you can fix them and protect your blockchain solutions from hackers.









Thanks for sharing the blog. Blockchain technology provides a level of security but not complete. The technology is susceptible.