The Amazon Web Services (AWS) Penetration Testing Tools are a collection of specialized programs and tools used to evaluate the security of AWS environments. AWS pentesting tools aid in identifying vulnerabilities, poor configurations, and possibly vulnerable areas where an attacker could get access.
AWS pentesting tools allow enterprises to dynamically assess their AWS infrastructure’s security posture and take necessary precautions to reduce risks by simulating real-world attacks. In this article, we will go over the best AWS pentest tools, and equip you with the information required to choose the right AWS pentesting tools that match your business goals and requirements.
Top 7 AWS Pentesting Tools
Boundaries To AWS Pentesting
There are Four broad areas are focused on while using AWS penetration testing tools for AWS cloud security:
- External Infrastructure of your AWS cloud
- Application(s) you are hosting/building on your platform
- Internal Infrastructure of your AWS cloud
- AWS configuration review
While AWS allows penetration testing, there are specific boundaries to what an ethical hacker can play with while the rest remains out of bounds for pen-testing. The services that can be tested without prior approval include:
- Amazon EC2 instances
- Amazon RDS
- Amazon CloudFront
- Amazon Aurora
- Amazon API Gateways
- AWS Fargate
- AWS Lambda
- AWS LightSail resources
- Amazong Elastic Beanstalk environments
For User-Operated services that include cloud offerings and are configured by users, AWS permits an organization to fully test their AWS EC2 instance while excluding tasks related to disruption of continuity.
For Vendor Operated services (cloud offerings that are managed and configured by 1 third-party), AWS restricts the pentesting to configuration and implementation of the cloud environment excluding the underlying infrastructure.
7 Best AWS Pentesting Tools In Detail
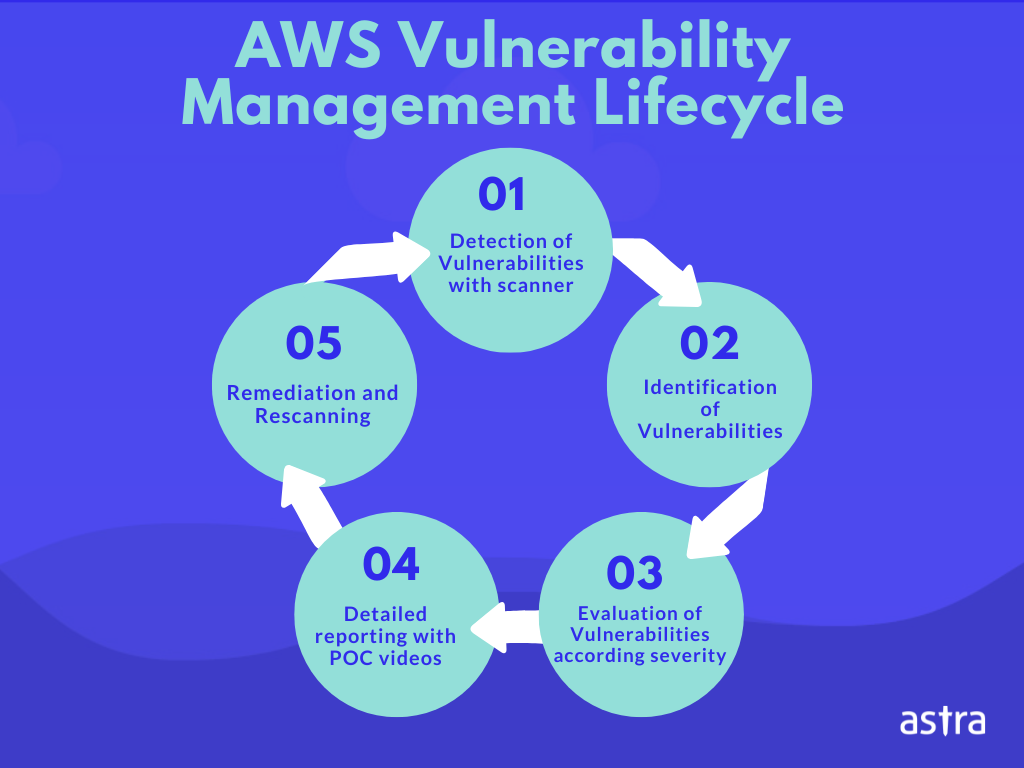
1. Astra Pentest
Astra is one of the most powerful AWS penetration testing tools that provides manual and automated pentesting services. It offers robust scanning capabilities to find flaws, incorrect setups, and potential attack vectors.
Astra simplifies thorough security assessments through automation, offering detailed reports, and helping with industry compliance. With its intuitive interface and wealth of features, Astra enables businesses to bolster their AWS security defenses and safeguard sensitive data proactively. Astra also helps achieve ISO 27001, HIPAA, SOC2, or GDPR compliance by conducting all necessary tests to check for compliance.
Features
- Compliance Checks: Our security engine covers all critical tests to achieve ISO 27001, HIPAA, SOC2, or GDPR compliance.
- Scan logged-in pages: To guarantee that every aspect of your application is secure, Astra’s scanner also examines the pages that are accessible beyond the login screen.
- Comprehensive scanning: Astra’s thorough scanner runs more than 8000 tests, including looking for known CVEs, the OWASP Top 10, and SANS 25.
- Privilege Escalation Vulnerabilities: If your asset permits users to have various roles, hackers may get around security measures and obtain confidential data. Our analysts make sure that there are no such gaps.
- Payment Flow Testing: Our analysts will examine your payment gateway and payment flow for flaws and make sure that hackers can’t access confidential financial data.
- Pricing: Quote on demand
What is good?
- Support for multiple platforms like Windows, Android, and Mac.
- Comprehensive vulnerability detection
- Sort issues according to their risk level and potential loss.
- Manual vetting to avoid false positives
What could be better?
- Service Costs can be reduced.
2. AWS Config

AWS Config is one of the major AWS pentesting tools that allows you to assess, audit, and evaluate the configuration of your AWS resources. Track resource configuration history and adhere to PCI DSS, ISO/IEC 27001:2013, SOC, and GDPR standards because it continuously monitors and logs configuration changes.
In addition to helping you identify unauthorized changes, by penetration testing AWS, it also defines and enforces desired configurations.
Features
- Compliance: ISO, SOC2, GDPR or HIPAA
- APIs: Secure critical APIs from vulnerabilities.
- Integration: Add security to the CI/CD pipeline
- Pricing: $ 0.003 / Per configuration item.
What is good?
- Check for more than 3,000 vulnerabilities.
- Scan your critical APIs
- Automated and manual pentests
What could be better?
- Not all AWS resources are supported by AWS Config
- Exclusive to AWS.
- AWS Config is region-specific, so you need to enable it separately in each AWS region
3. AWS Inspector

AWS Inspector is a service that Amazon Web Services (AWS) offers for automatic security evaluation and penetration testing AWS. It locates potential security flaws and best practice violations in your AWS resources. Users get access to comprehensive reports, can modify assessment templates, and schedule repeat assessments.
This AWS pentesting tool streamlines security evaluations, minimizes manual labor, and supports compliance auditing. Through integration with other AWS services like Amazon CloudWatch Events and AWS Systems Manager, AWS Inspector enables automatic actions.
Features
- Scanner capacity: It performs continuous vulnerability and exposure scanning.
- Vulnerability Assessment: An accurate vulnerability assessment with a Risk score
- Account Management: Manage Inspector accounts centrally.
- Pricing: $ 13.50/month
What is Good?
- High-impact findings identification dashboard.
- Customizable findings management views
- Integrate findings with systems.
What could be better?
- Integration with services other than AWS should advance.
- Restricted CIS CAT Levels
- The interface Is confusing and glittery
4. ScoutSuite
ScoutSuite is another major player amidst other AWS pentesting solution. It is an open-source security auditing application that is not limited to AWS but is also available for Microsoft Azure, and GCP. It is a Python-based AWS pentesting tool that provides thorough security audits and collects configuration and resource data from cloud providers’ APIs.
This AWS pentesting tool looks at different areas of cloud security, including best practices compliance, network setups, identity and access management (IAM) settings, and storage rights. ScoutSuite offers thorough reports highlighting possible security vulnerabilities and configuration errors. Its modular design allows users to tailor their examinations.
Features
- Compliance: Support with AWS, Azure, GCP, Alibaba, and Oracle cloud environments
- Monitoring: real-time cognition of changes or issues
- One tool: Centralized configuration checks for efficiency
- Pricing: Free
What is Good?
- Allows for continuous monitoring of your cloud environment
- Generates detailed reports with actionable insights
- It offers a wide range of security checks and assessments for cloud environments
What could be better?
- Slow scan speed
- Compatibility issues with newer AWS services
- Lack of Real-Time Monitoring
5. Prowler

Prowler is one of the few open-source AWS pentesting tools for audits, incident response, continuous monitoring, hardening, and forensics readiness for Amazon Web Services (AWS) environments. It does automated security evaluations to look for configuration errors. AWS FTR, ENS, GDPR, HIPAA, FFIEC, SOC2, CIS, PCI-DSS, ISO 27001, and custom security frameworks are among the hundreds of controls included.
Your workstation, an EC2 instance, Fargate or another container, Codebuild, CloudShell, Cloud9, and many other platforms can all run Prowler. Python is used to create Prowler, along with the AWS SDK (Boto3), Azure SDK, and GCP API Python Client.
Features
- Services to: AWS, GCP, Azure, Kubernetes
- Authenticity: Multi-Factor and AWS authentication
- Scope: RBAC roles for subscription scope
- Pricing: Free
What is Good?
- Interactive browser authentication
- High-Level Architecture
- Environment-based service principal authentication
What could be better?
- Possibility of false positives
- Limited capacity for automation
- Not very attractive native output
6. CloudSploit

CloudSploit is a cloud security monitoring and assessment tool for (AWS), Microsoft Azure, and Google Cloud Platform (GCP) environments. It checks cloud resources for security flaws, improper setups, and regulatory infractions.
It has flexible output formats with default console tables for seamless integration with other best AWS penetration testing tools. It checks your AWS IaaS accounts’ state of service configuration for potential security flaws and continuously scans the activity in your accounts for suspicious activity and insider threats.
Features
- Deployment: Self-Hosted and Hosted at Aqua Wave
- Providers: AWS, OCI, GCP, and GitHub
- Configuration file: (JSON file) and Environment Variables
- Pricing: 8 USD/ per month
What is Good?
- AWS credential detection
- Specify the correct format for Credential File Usage.
- Environment variable support
What could be better?
- Dependency on API permissions
- Lack of comprehensive reporting
- No real-time monitoring
7. Pacu
Pacu is an open-source, free AWS exploitation framework for security and penetration testing. An extensive collection of tools and modules is available for evaluating the security posture of AWS accounts, and testing the efficacy of security controls. It supports various AWS penetration testing services and offers a flexible and extensible framework for advanced security assessments in AWS environments.
Features
- Modules: Exploitation modules with diverse capabilities
- Post-Exploitation: Credentials compromised; dominance unleashed after exploitation
- Cloud-Centric: multi-faceted cloud exploitation capabilities
- Pricing: Free
What is Good?
- Various privilege escalation techniques
- AWS SSM for remote code execution
- Confirmed account permission enumeration.
What could be better?
- Possible false-positive results
- Pacu may not always support the newest AWS features.
- Pacu could have a challenging learning curve.
How To Choose The Best AWS Pentesting Tools
- Reputation and experience: Consider AWS pentesting tools or the company’s track record and expertise. Look for the best AWS penetration testing tools or organizations with a history of providing dependable and efficient security solutions.
- Features: Look for capabilities for automation, compliance checks, API testing, vulnerability scanning, security configuration assessments in these AWS pentesting tools. Think about the usability, scalability, reporting options, and integration possibilities.
- Vulnerability Scanning: Ensure that the AWS pentesting software that is being considered by you, provides vulnerability scanning for your AWS assets and infrastructure for the quick detection of vulnerabilities. A great example of such a tool would be Astra Security which provides automated vulnerability scans, pentest, and cloud configuration reviews for your AWS infrastructure.
- Customer support: See how the community actively supports and develops the tools. Look for AWS testing tools with a thriving user base, frequent updates, and ongoing developer support.
- Detailed reports: Reports are essential for understanding the vulnerabilities. Look for the best AWS penetration testing solution that deliver thorough reports with detailed descriptions of identified problems, their effects, suggested corrective actions, and a severity-based ranking of vulnerabilities.
- User Interface: An intuitive and user-friendly interface can significantly improve the effectiveness and efficiency of your penetration testing efforts. The user interface (UI) should be neat, well-designed, and straightforward.
- Intuitive Dashboard: The dashboard should provide a centralized view of the AWS penetration testing operations, tests, and essential metrics. You can track vulnerabilities, track progress, and spot trends or patterns using an easy-to-use dashboard.
- Integration Capabilities The AWS pentesting tools you use should be able to integrate with other security tools, DevOps pipelines, and existing security frameworks in your company. Automation, workflow simplification, and increased security practice efficacy can all be achieved through integration with other systems.
Conclusion
AWS pentesting tools assist organizations in maintaining a strong security posture by providing a wide range of capabilities, such as vulnerability scanning, configuration assessment, and compliance monitoring. Security teams can proactively resolve security issues using AWS pentesting tools like Astra Pentest, AWS Inspector, and ScoutSuite.
AWS offers various integration opportunities to your application with some in-built security features for the increased overall security posture of your AWS cloud. Performing AWS cloud penetration testing is extremely important to ensure business continuity. If you have further queries on AWS pentesting tools and the process itself, get in touch with our security experts.
FAQs
What is AWS penetration testing?
AWS penetration testing is when an enterprise evaluates the security of the infrastructure and applications hosted on Amazon Web Services (AWS) to find flaws and vulnerabilities that malicious actors might exploit; it involves simulating actual attacks with proper permission and controls.
Why do we perform penetration testing in my AWS environment?
Penetration testing can help you find and address vulnerabilities in your AWS infrastructure before attackers find and exploit them. Penetration testing in the AWS environment will check the efficiency of your security controls, configurations, and policies and ensure your AWS resources’ privacy, integrity, and availability.
What are the specific tools recommended for AWS penetration testing?
1. AWS native technologies like AWS Security Hub, AWS CloudTrail, and AWS Config
2. Tools from outside sources, such as Astra Pentest, Burp Suite, Nessus, Nmap, and OpenVAS
3. Techniques like OSSTMM, NIST SP 800-115, and the OWASP Testing Guide
















