Amazon Web Services (AWS) has over a million customers. It is a trusted provider of scalable and modular solutions for global businesses. However, the digital landscape comes with its own threats if not protected properly. It is important you employ security best practices to ensure the safety of your assets.
This AWS cloud security checklist will come in handy as you work towards securing your AWS environment. We cover all bases to ensure that your data remains intact, confidential, and readily available.
Unlocking AWS Cloud Security Potential with Reliable Checklists
In this day and age, where everything is interconnected, the necessity of security in cloud apps and cloud platforms has moved from being just an optional add-on to a non-negotiable component, particularly for firms relying on the might of platforms such as AWS. AWS cloud security stands paramount in its purpose to secure crucial data, preserve the esteem of the business, and maintain the customers’ confidence while ensuring the business keeps operating smoothly and adhering to regulatory guidelines.
However, AWS cloud security isn’t something you just set up once and then forget. It calls for continual vigilance, governance, and updates to stay ahead of emerging threats. This is where the practicality of a dependable checklist becomes evident. An all-encompassing AWS cloud security checklist acts as a tactical guide, enabling businesses to cover all the bases and not miss any detail while securing their AWS environment.
A checklist is more than just a prioritization tool for tasks in managing cloud security; it also facilitates progress tracking and pinpoints any possible gaps in your security status. It delivers a systematic security method, ensuring that every facet, from IAM and VPC security to data defense and incident response, gets the attention and security it needs. Besides, it assists in fulfilling compliance mandates and getting ready for audits, as the checklist can function as a document for the security controls in place.
The AWS Shared Responsibility Model helps differentiate security tasks between AWS and its users, i.e., you. Understanding this model can help you identify your key responsibility areas and actively work towards protecting those resources.
Within this model, AWS takes the responsibility for “Security OF the Cloud”, which involves protecting the foundation that powers all AWS services. This infrastructure consists of hardware, software, networking facilities, and more. To ensure these components are resilient against potential threats, AWS adheres to a rigorous set of security policies and guidelines.
Conversely, the user is responsible for “Security IN the Cloud”. This relates to the security configurations of customer-specific data, platforms, applications, and networks that operate within AWS. This may involve tasks such as administering AWS IAM, opting for suitable firewall settings, encrypting data, or ensuring compliance with regulations specific to the industry. The execution of these security steps is integral to the protection of user data and to the overall security standing of the environment hosted by AWS.
AWS Cloud Security Checklist
This AWS Cloud Security Checklist will provide a clear pathway, outlining key measures to help strengthen your security posture.
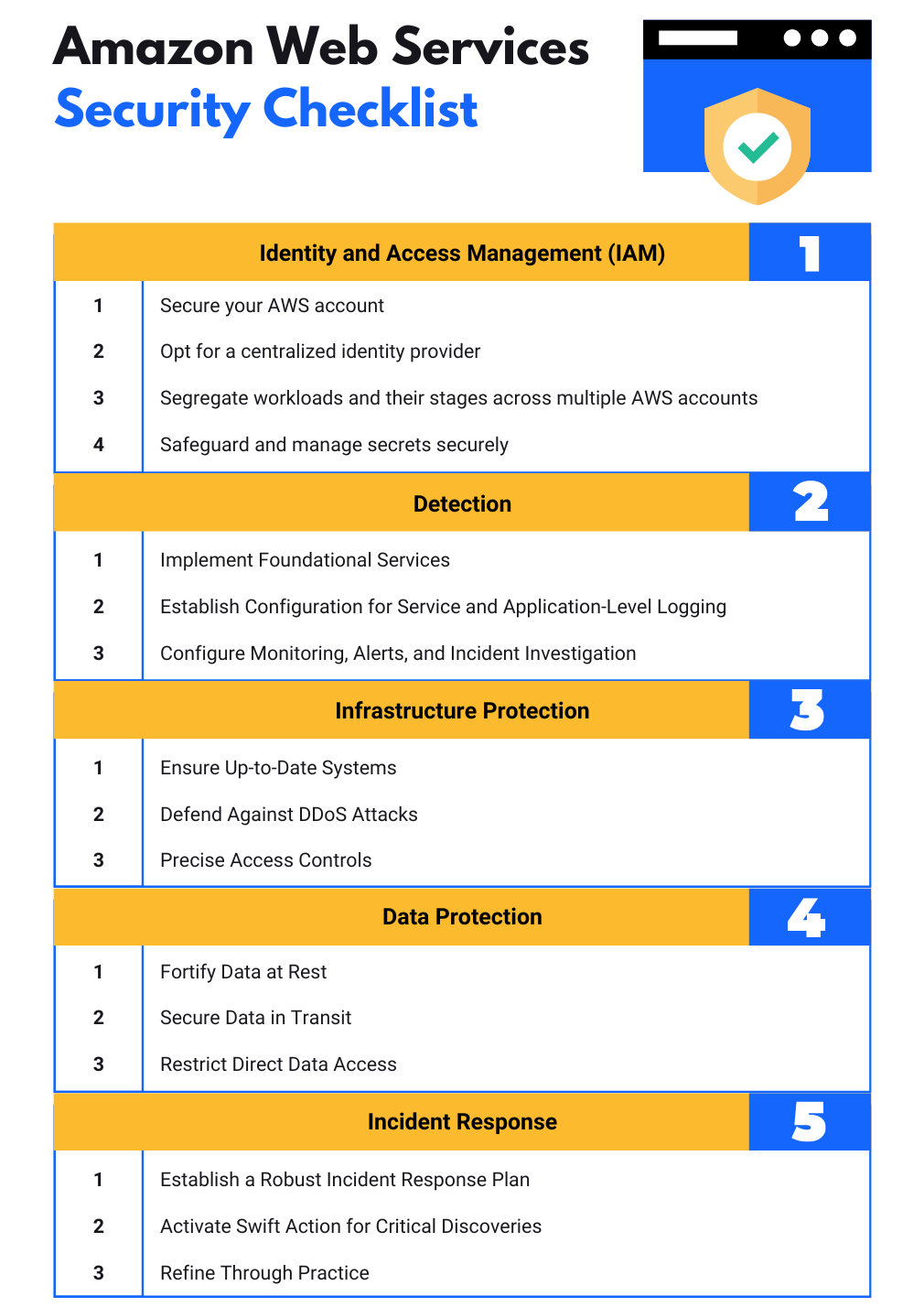
AWS Cloud security checklist #1 Identity and Access Management (IAM)
Effective security originates from stringent control over access to your resources and the operations they can execute. This is done using AWS Identity and Access Management (IAM).
- Adopting least privilege access: Providing only the necessary permissions required for users to carry out their tasks is vital. By adhering to the principle of least privilege, the possibility of an attacker accessing sensitive resources is diminished.
- Using Multi-Factor Authentication (MFA): MFA introduces an additional security layer to your AWS environment. Even if user credentials get compromised, MFA ensures that without the second factor of authentication, an attacker cannot access your resources.
- Using roles for applications that run on Amazon EC2 instances: Rather than sharing security credentials amongst resources, AWS recommends the use of IAM roles. Roles offer a secure method to assign permissions to applications operating on EC2 instances.
- Regularly auditing and rotating credentials: The practice of auditing and rotating IAM credentials regularly can drastically decrease the risk of a potentially compromised, older credential being used for unauthorized access.
AWS Cloud Security Checklist #2 VPC Security
Securing your Virtual Private Cloud (VPC), which is the foundation of your AWS network, ensures your resources are well protected from unauthorized access.
- Security groups and Network Access Control Lists (NACLs): These function as virtual firewalls for your instances to regulate incoming and outgoing traffic. While security groups operate on an instance level, NACLs work at the subnet level. Proper configuration allows only trustworthy and required traffic to reach your instances.
- Configuration of Subnets and Route Tables: Resources that don’t require internet access should use private subnets, and those that do require it should use public subnets. A properly configured route table guarantees the accurate direction of network traffic.
- VPN Connections and Direct Connect: Utilize a VPN or AWS Direct Connect when a secure connection between your AWS VPC and the remote network is necessary. These methods provide encrypted and private connections powering the risk of data exposure.
AWS Cloud security checklist #3 Data Protection
AWS offers numerous tools that help ensure your data’s integrity, confidentiality, and availability.
- Encrypting Data at Rest and In-Transit: Encryption converts sensitive information into an incomprehensible format that can only be read with specific keys, making encryption essential to protect any sensitive data in storage or moving across networks. AWS Key Management Service (KMS) offers services specifically dedicated to encryption management; sensitive data must always remain encrypted throughout its lifecycle for protection and confidentiality purposes.
- Routine Data Backups: Regular backups are vital in order to safeguard business continuity and disaster recovery plans; AWS offers services such as AWS Backup and Amazon S3 versioning that enable regular and automated data backup, decreasing the chances of data loss.
AWS Cloud Security Checklist #4 Monitoring and Logging
Step four in our AWS cloud security checklist entails setting up comprehensive monitoring and logging measures within your AWS environment to maintain transparency for better insight, quickly detect any abnormal activities or illegal acts that might take place, and allow rapid resolution.
- Make use of AWS CloudTrail for audit purposes: CloudTrail records every AWS API call made for your account through AWS Management Console, SDKs, command line tools, and other AWS services – including those made via SDKs, command line tools, or any other source – providing valuable security analysis data, tracking resource changes over time and audit compliance assessments.
- Take Advantage of AWS Config to Inventory Resources: With AWS Config, you can assess, audit, and check the configurations of all AWS resources in real-time, recording their setup and monitoring changes continuously so as to automate an assessment against preferred settings.
- Leverage Amazon CloudWatch for real-time monitoring: CloudWatch allows you to continuously track AWS resources and applications in real time by gathering log files, tracking metrics, and reacting to alarm conditions you set.
AWS Cloud security checklist #5 Incident Response
Being prepared for potential security incidents is a crucial element of maintaining a strong AWS security stance. Implementing solid incident response mechanisms can assist in reducing the impact of a security breach.
- Developing a plan for dealing with security incidents: Your incident response plan should clearly indicate how to recognize, investigate, and bounce back from security incidents. AWS offers the AWS Incident Response Guide to help you shape this plan.
- Using AWS GuardDuty for spotting threats: GuardDuty is a service that detects threats by continuously overseeing malicious activities and unauthorized behavior. By switching on GuardDuty, you can fortify your AWS environment with an additional protection layer.
- Implementing AWS Shield for mitigating DDoS: AWS Shield is a managed service that protects against Distributed Denial of Service (DDoS) attacks. Shield employs continuous detection and automatic inline mitigation strategies to reduce application downtime and latency.
AWS Cloud security checklist #6 Compliance
Finally, following the necessary industry and legal norms is important to maintaining the overall security of your AWS surroundings.
- Conformity to compliance prerequisites: You might need to adhere to specific regulations like HIPAA for healthcare and GDPR for data protection in Europe, among others, depending on your business domain. AWS provides features that assist you in meeting these compliance needs.
- Employing AWS Artifact for instant access to AWS compliance reports: AWS Artifact is your centralized hub for accessing pertinent compliance-related information. It offers on-demand availability of AWS’ security and compliance documents and selected online contracts.
Automating Security Tasks
Automation minimizes the likelihood of human mistakes and allows for faster detection and reaction to potential threats. AWS Security Hub and Astra Security, a prominent third-party provider, are two effective tools for automation.
AWS Security Hub
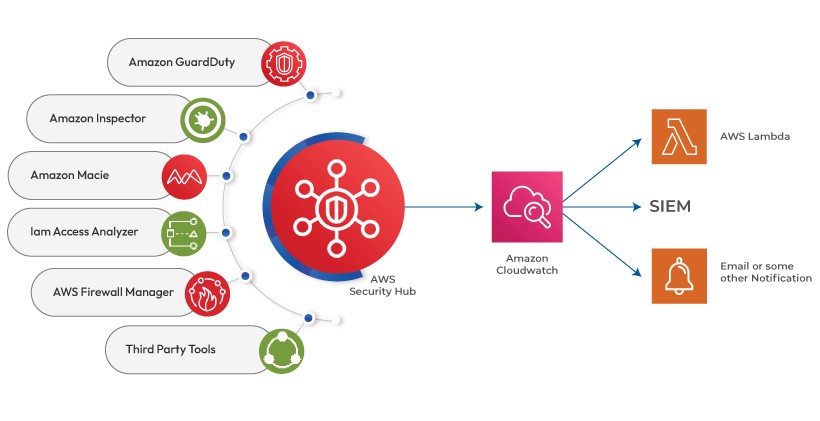
AWS Security Hub offers a complete view of your top-priority security warnings and compliance status across AWS accounts. Several benefits come from using Security Hub:
- Central Security Findings: Security Hub compiles security data from AWS services such as Amazon GuardDuty, Amazon Inspector, Amazon Macie, AWS Firewall Manager, and other AWS Partner solutions.
- Automated Compliance Verifications: It consistently conducts automated, rule-guided compliance verifications based on industry norms and best practices.
- Insights and Unified Dashboards: This service provides insights that assist you in recognizing trends and identifying potential issues, along with integrated dashboards for an unambiguous view of your security status.
Astra Security
Astra Security is a vulnerability assessment and penetration testing company that provides round-the-clock security testing services to assess internet-facing assets as quickly and efficiently as possible to detect vulnerabilities.
- Cloud Security Assessment: Astra Security’s team of specialists executes a thorough examination of your cloud infrastructure. They assist you in assessing your present security position and underlying vulnerabilities and providing strategic suggestions for enhancement.
- Compliance-Friendly Certificates: Apart from enhancing security, Astra Security also aids with regulatory compliance. They deliver Compliance Friendly Certificates as evidence of your adherence to different security standards. This can significantly facilitate the process of demonstrating compliance to auditors or stakeholders.
Conclusion
Secure your AWS environment through constant vigilance, governance, and the appropriate tools. This AWS cloud security checklist presents an exhaustive AWS security checklist covering everything from identity and access management (IAM), data protection and compliance, and collaboration with experts such as Astra Security to improve your security posture and use AWS services to strengthen it further. Get ahead in cloud security now; team up with professionals today so they can assist in protecting digital presences like Astra Security does for theirs.
Frequently Asked Questions
What do you mean by security controls in AWS?
Security controls in the AWS security checklist are technical or managerial safety measures used in an AWS set-up to protect the security, secrecy, and availability of data and systems. These controls stop, tell about, and reduce security risks, including possible threats and weak spots.
Which security services in AWS let you use a collection of safety measures?
AWS Identity and Access Management (IAM) is a tool you can use to tightly manage access to AWS resources and services. It caters to your AWS users, groups, and roles, offering a secure environment. With IAM, you have the power to establish individual access controls with permissions, letting you dictate who can access specific services and resources and set out the conditions of that access.
What are the various types of security services?
Security services cover a wide range and include many types in different areas. Here are some common types of security services:
1. Firewalls: Firewalls help keep your network safe by managing data coming in and going out of your network.
2. Intrusion Detection Systems (IDS): IDS systems check the network or systems for any harmful activities or breaking of rules.
3. Virtual Private Networks (VPN): VPN gives a safe connection over a public network, making sure the data sent is coded and safe.
4. Data Loss Prevention (DLP): DLP tools can stop people from sending private information outside the network.