In today’s digital age, with 17.5K CVEs discovered in the first half of 2026 alone, a robust cybersecurity posture is no longer optional. Yet, between deciphering complex frameworks, identifying the right tools, and interpreting cryptic jargon-first reports, the audit process can be quite overwhelming.
Even worse, a poorly executed audit might provide a false sense of security, leaving your organization vulnerable to devastating attacks. Thus, a cyber security audit service not only identifies vulnerabilities but also translates complex technical jargon into actionable insights and helps allocate remediation resources effectively.
Don’t let hidden vulnerabilities slip through the cracks. Get a comprehensive cybersecurity audit that translates risks into action.
[Book your free audit demo →]
Best 10 Cybersecurity Audit Companies
- Astra Security
- Sprinto
- Flashpoint
- CyStack
- SecurityScoreboard
- KROLL
- Romano Security
- Mandiant
- Cobalt
- Synopsys
| Tool | Audit Capabilities | Remediation Support | Compliance | Integrations | Pricing |
|---|---|---|---|---|---|
| Astra Security | Web apps, APIs, cloud, mobile, network | Yes | PCI-DSS, HIPAA, ISO27001, SOC2 | Slack, JIRA, GitHub, GitLab, CircleCI, Jenkins | $1999/year |
| Sprinto | Automated compliance for 20+ frameworks | Yes | ISO 27001, SOC2, HIPAA, GDPR | Slack, GitHub, GitLab, Google, AWS, and more | Quote-based |
| Flashpoint | Threat intel + physical risk insights | Yes | GDPR, PCI DSS | Splunk, ServiceNow, Polarity, IBM QRadar | Quote-based |
| CyStack | Automated scans, manual pentest, performance testing | Yes | OWASP10 | – | $9 per scan |
| SecurityScorecard | Digital forensics, penetration testing | Yes | SOC 2, HIPAA, NIST CSF | CrowdStrike, Archer, OneTrust, Slack, JIRA, ServiceNow | Quote-based |
| Kroll | Threat modeling, penetration testing | Yes | CIS, NYDFS, FARS, GDPR | JIRA, Azure DevOps | Quote-based |
| Romano Security | Vulnerability scanning, penetration testing, consulting | Yes | ISO 27001, NIST, SOX | – | Quote-based |
| Mandiant | Purple teaming, threat modeling, penetration testing | Yes | SOC, FedRAMP, PCI | Slack, Microsoft Teams, GitHub | Quote-based |
| Cobalt | Automated and manual penetration testing | Yes | SOC 2, ISO, CREST, PCI, HIPAA, NIST | JIRA, GitHub, Azure DevOps, JupiterOne | Quote-based |
| Synopsys | SAST, DAST, IAST, penetration testing | Yes | ISO, PCI, FedRAMP, NIST | GitHub, GitLab, BitBucket, JIRA, Slack | Quote-based |
10 Cybersecurity Audit Companies
1. Astra Security – Get Started Now
Key Features:
- Platform: Online
- Audit Capabilities: Third-party audits for Web apps, APIs, cloud, mobile apps and network devices
- Remediation Support: Yes
- Compliance: PCI-DSS, HIPAA, ISO27001, and SOC2
- Integrations: Slack, JIRA, GitHub, GitLab, CircleCI, and Jenkins
- Price: Starting at $1999 per year. Better pricing, tailored to you. Book a call to unlock it
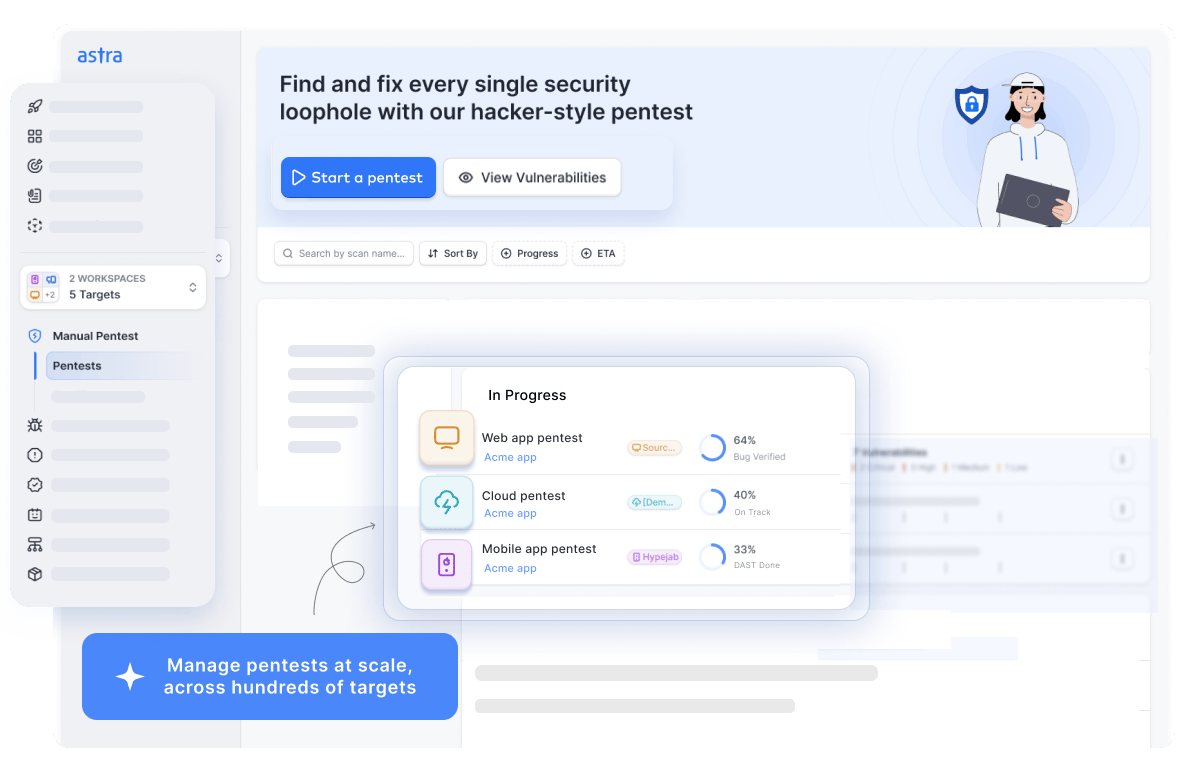
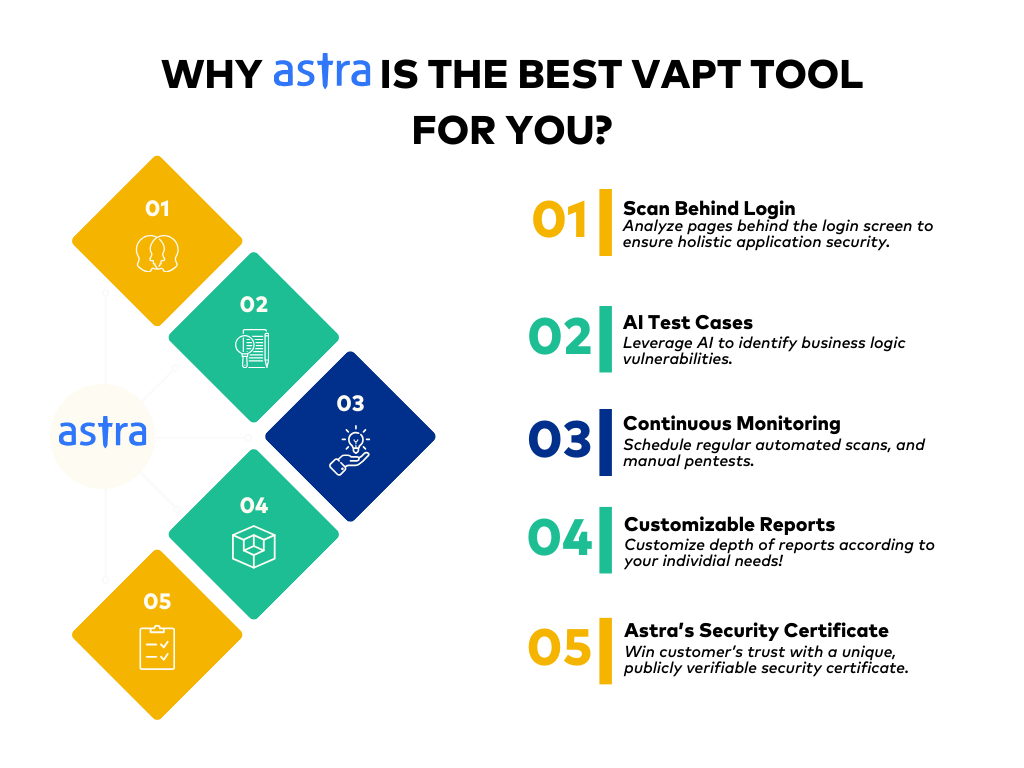
As one of the leading cybersecurity audit services, Astra Security’s PTaaS platform blends automation, AI, and human expertise to provide exhaustive third-party audits. Running over 10,000+ tests, our vetted scans guarantee zero false positives with seamless integrations.
The industry-specific AI-powered test cases, combined with a CXO-friendly dashboard and tailored, exhaustive reports, guarantee a smooth experience while saving you millions of dollars proactively.
Moreover, our round-the-clock support, rescans, and publicly verifiable security certificates make security audits effective and hassle-free. Still don’t believe us? Check out what our customers think!
Experience seamless, AI-powered security audits with Astra. Sign up for a personalized demo today and see why we’re rated 4.6/5 on G2.
2. Sprinto
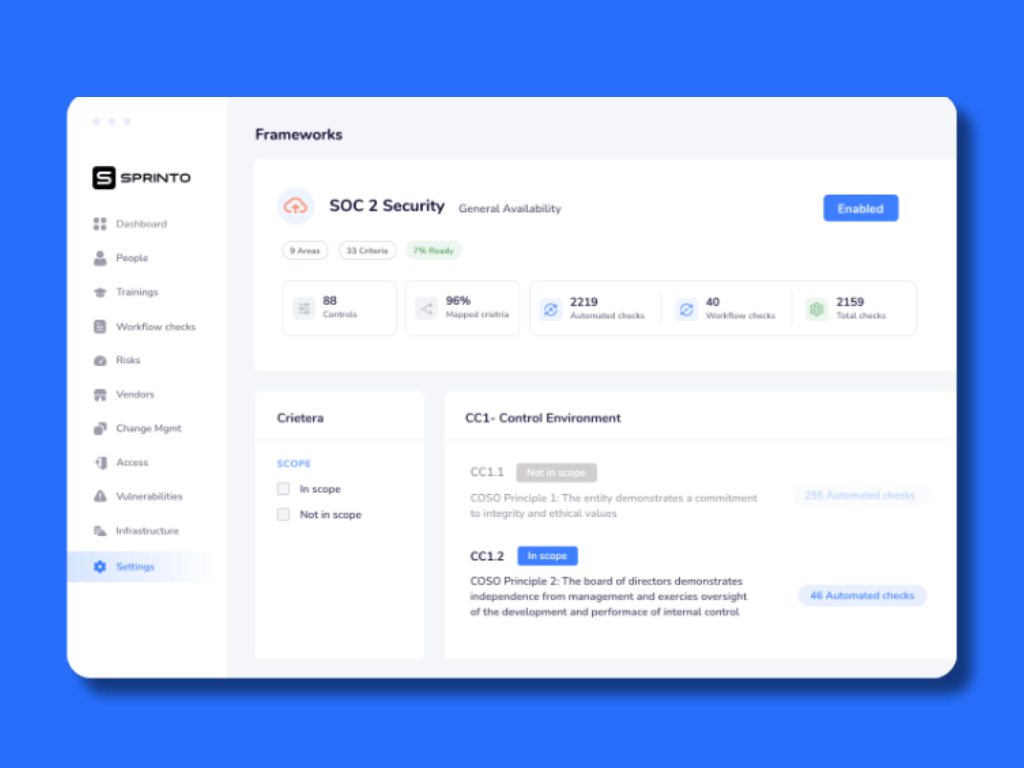
Key Features:
- Platform: Online
- Audit Capabilities: Automated compliance solution for 20+ frameworks
- Remediation Support: Yes
- Compliance: ISO 27001, SOC2, HIPAA, and GDPR
- Integrations: Slack, GitHub, GitLab, Google, AWS, and more
- Price: Available on quote
As a security compliance automation platform, Sprinto offers exhaustive cyber security audit services. With automated evidence collection, control monitoring, and intelligence alerts, it simplifies and speeds up the process.
Sprinto offers compliance services for 20+ compliance frameworks, including SOC 2, ISO 27001, GDPR, HIPAA, and PCI-DSS, as well as custom frameworks with 200+ integrations.
(Rated 4.8/5 on G2)
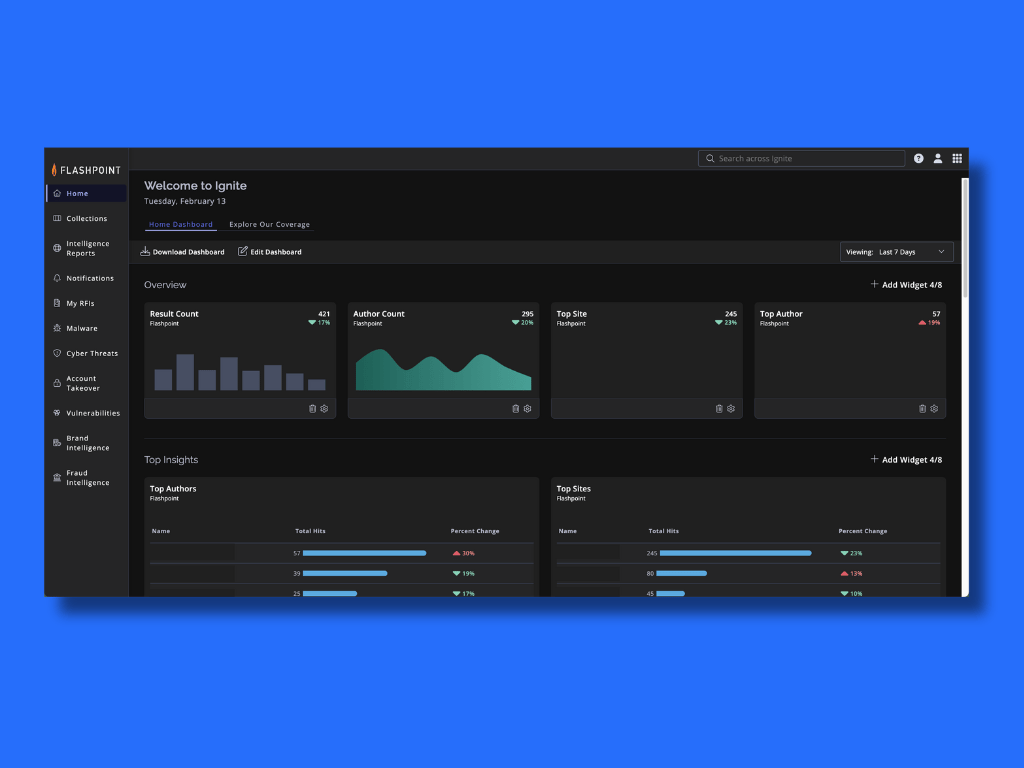
3. Flashpoint
Key Features:
- Platform: Online
- Audit Capabilities: Identify and remediate vulnerabilities and physical security risks
- Remediation Support: Yes
- Compliance: GDPR and PCI DSS
- Integrations: Splunk, ServiceNow, Polarity, IBM QRadar
- Price: Available on quote
Flashpoint.io doesn’t directly perform cybersecurity audits, but it can significantly enhance your audit process. Its external threat intelligence, combined with extensive data collection and processing capabilities, helps prioritize vulnerabilities based on real-world threats and identify potential attack vectors.
Moreover, the platform’s AI-powered continuous monitoring of suspicious activity on authorized accounts also facilitates the early detection of insider threats.
(Rated 4.5/5 on G2)
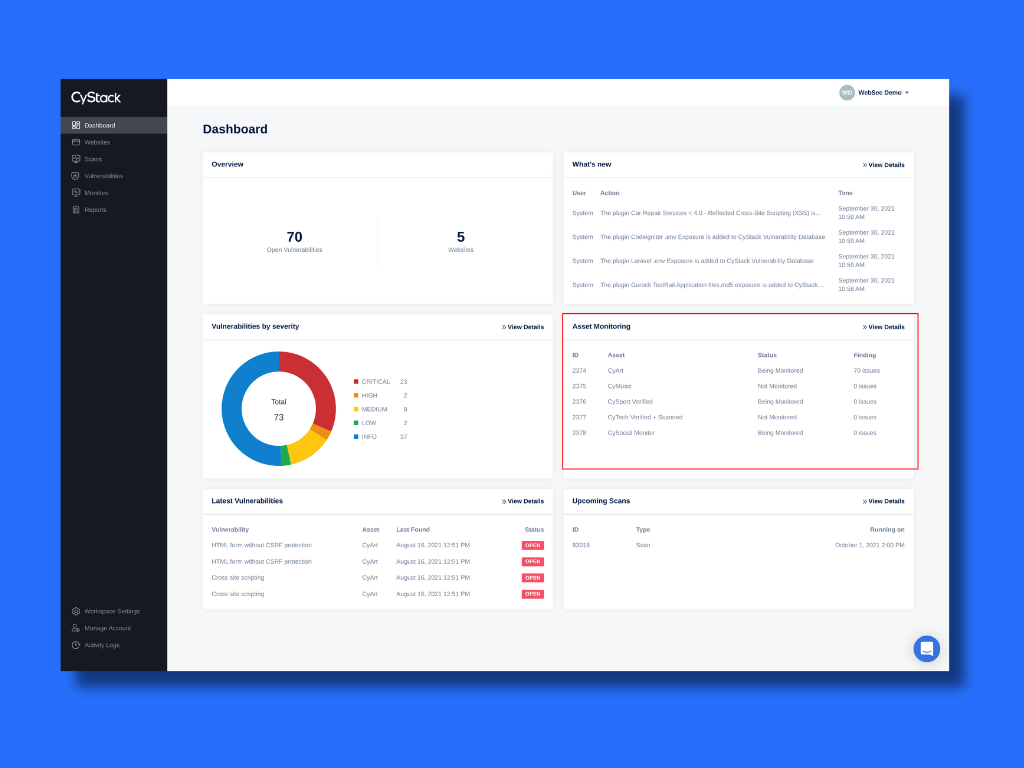
4. CyStack
Key Features:
- Platform: Online
- Audit Capabilities: Automated scanning, manual penetration, and performance testing
- Remediation Support: Yes
- Compliance: OWASP10
- Integrations: –
- Price: Starting at $9 per scan
CyStack offers granular cybersecurity audit services relying primarily on comprehensive VAPT offerings. Designed by experts, it simulates hacker behavior to find and analyze critical CVEs across your systems, applications, and network configurations.
The tool also offers threat intelligence, performance tests, and real-time monitoring. Lastly, for deeper analysis, CyStack offers in-depth smart contract/protocol audits specifically tailored to cloud infrastructure and blockchain projects.
5. SecurityScoreboard
Key Features:
- Platform: Online
- Audit Capabilities: Digital forensics and penetration testing to identify and fix bugs
- Remediation Support: Yes
- Compliance: SOC 2, HIPAA, NIST CSF, and more
- Integrations: CrowdStrike, Archer, OneTrust, Slack, JIRA, and ServiceNow
- Price: Available at quote
SecurityScorecard doesn’t offer a cybersecurity audit, but complements it with extensive continuous monitoring. Its automated pentests, digital forensics, third-party risk assessment, and threat intelligence help identify CVEs, such as control gaps and misconfigurations.
The platform’s data-driven security risk ratings benchmark your organization against industry peers, guiding remediation efforts and streamlining audits.
(Rated 4.3/5 on G2)
6. KROLL
Key Features:
- Platform: Online
- Audit Capabilities: Threat modeling and penetration testing
- Remediation Support: Yes
- Compliance: CIS, NYDFS, FARS, GDPR, and more.
- Integrations: JIRA and Azure DevOps,
- Price: Available at quote
Blending penetration testing and threat modeling, Kroll’s cybersecurity audits pinpoint weaknesses across your entire infrastructure (people, data, operations, and technology). Built on industry best practices, its cutting-edge security assessments prioritize remediation efforts.
The security-first tool even offers specialized assessments for evolving threats like ransomware and conducts incident response planning exercises.
(Rated 4.5/5 on G2)
7. Romano Security Consulting
Key Features:
- Platform: Online
- Audit Capabilities: Vulnerability scanning, penetration testing, and security consultancy
- Remediation Support: Yes
- Compliance: ISO 27001, NIST and SOX
- Integrations: –
- Price: Available at quote
As one of the cyber security audit services, Romano Security offers a range of audits, from a quick one-day Basic Security Audit to a deep two-day Advanced Audit that analyzes both physical and technical controls. They even assess third-party vendors for you.
Their extensive experience and certifications, including ISO27001 Lead Auditor, guarantee in-depth expertise to uncover hidden risks. Public sector organizations can leverage their G Cloud 13 approval for an easier procurement process
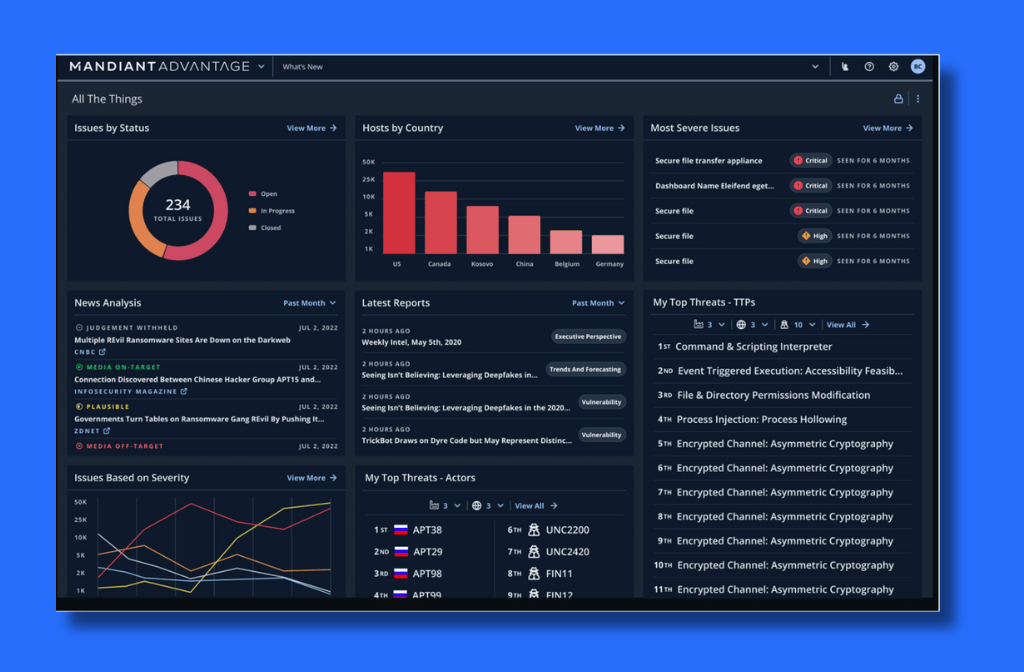
8. Mandiant
Key Features:
- Platform:
- Audit Capabilities: Purple teaming, threat modeling, and penetration testing
- Remediation Support: Yes
- Compliance: SOC, FedRAMP, and PCI
- Integrations: Slack, Microsoft Teams, and GitHub
- Price: Available at quote
Mandiant offers an exhaustive audit with a multi-faceted approach. They combine technical assessments, using their threat intelligence-powered Cyber Defense Assessment, with red team penetration testing to uncover vulnerabilities and prioritize fixes.
As one of the security audit companies, Mandiant is known for its supply chain and external system security. It provides an encyclopedic roadmap for a stronger security posture.
(Rated 4.5/5 on G2)
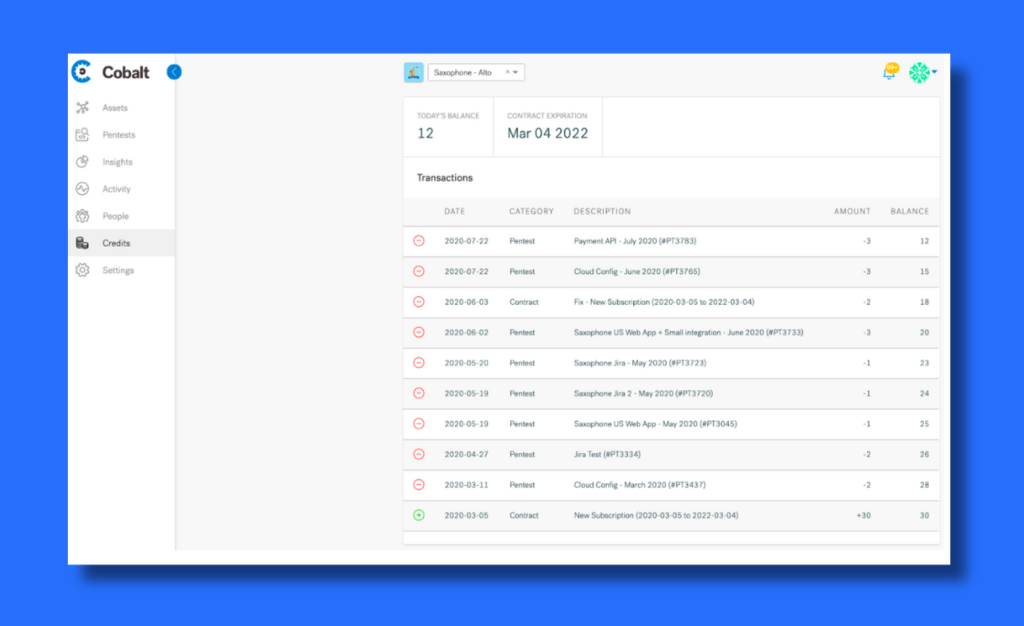
9. Cobalt
Key Features:
- Platform: Online
- Audit Capabilities: Automated and manual penetration testing
- Remediation Support: Yes
- Compliance: SOC 2, ISO, CREST, PCI, HIPAA, and NIST
- Integrations: JIRA, GitHub, Azure DevOps, and JupiterOne
- Price: Available at quote
Cobalt’s PTaaS platform delivers on-demand pentesting for cybersecurity audits. It employs an effective combination of DAST, SAST, and network security testing techniques to uncover vulnerabilities across your systems.
Its compliance-first processes ensure your security posture aligns with relevant regulations. By integrating seamlessly with your SDLC, Cobalt promotes a left shift, finding and fixing issues from the get-go.
Explore leading Cobalt alternatives and competitors offering broader coverage across applications, APIs, and cloud.
(Rated 4.7/5 on G2)
10. Synopsys
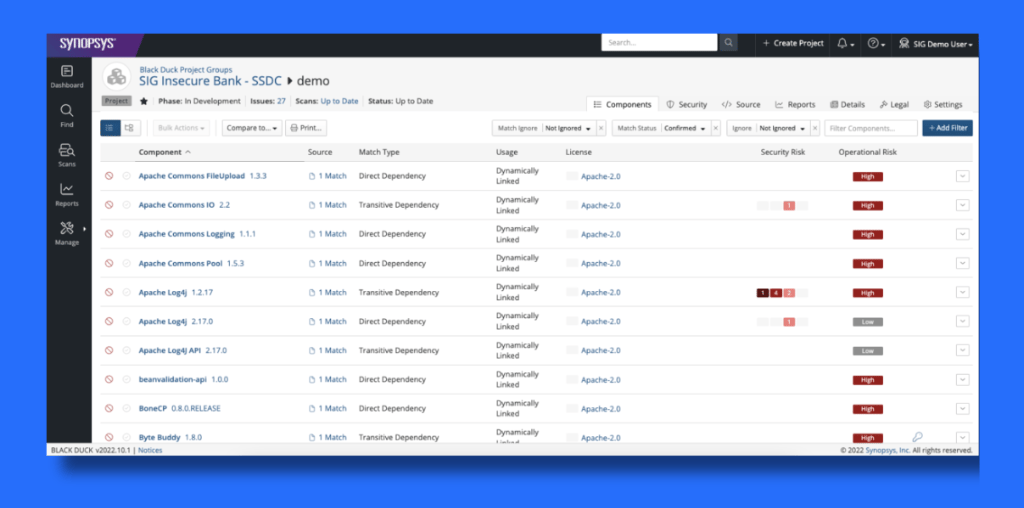
Key Features:
- Platform: Online
- Audit Capabilities: SAST, DAST, IAST, and penetration testing
- Remediation Support: Yes
- Compliance: ISO, PCI, FedRAMP, and NIST
- Integrations: GitHub, GitLab, BitBucket, JIRA and Slack
- Price: Available at quote
Synopsys streamlines your cybersecurity audit with a suite of tools that seamlessly integrate with your SDLC. It uncovers vulnerabilities in your code, third-party libraries, and open-source dependencies by combining automated static code analysis and penetration testing.
As one of the top cyber security audit services, it also offers specialized audits for open-source components to pinpoint risks and potential licensing issues, which can be invaluable during mergers and acquisitions due diligence or internal audits.
(Rated 4.3/5 on G2)
Features to Look For in a Cybersecurity Audit Companies

Experience and Qualifications
Seek out auditors with relevant certifications (CISSP, CISA, OSCP) and at least 3+ years of experience in conducting security audits in your industry and with similar assets. These credentials not only guarantee deep industry knowledge but also a well-executed audit.
This translates to actionable insights that provide a more exhaustive review and save time and resources in remediating vulnerabilities. For example, an experienced auditor familiar with HIPAA regulations can delve deeper into specific controls around electronic protected health information (ePHI).
Audit Methodology
A well-defined audit methodology is the cornerstone of a successful cybersecurity assessment. Look for a company that leverages a standardized framework as a roadmap but is flexible enough to customize it to your specific needs.
A strategy built on standardized frameworks like the NIST Cybersecurity Framework (CSF) or ISO 27001 helps categorize security controls into key areas like risk management, incident response, and access control, ensuring a systematic and thorough approach.
Cybersecurity Tools
An effective cybersecurity audit goes beyond rudimentary vulnerability scanners. While these tools provide a baseline assessment, truly comprehensive network security audit companies leverages a robust toolkit.
Choose companies that employ advanced PTaaS platforms built on vulnerability scanners to offer automated penetration testing tools that simulate real-world attacker methods to pinpoint vulnerabilities and chain attacks and security posture assessment platforms to enable data-driven decision-making.
Communication and Reporting
Look for information security audit services that establish a secure communication channel upfront and keep you informed at every stage. This includes transparent updates on progress, findings, and potential roadblocks and extends to custom yet exhaustive reports.
Detailing vulnerabilities with prioritization based on risk and criticality, such transparency allows you to grasp the audit’s scope and make informed decisions about resource allocation for fixing vulnerabilities. Companies with experience in your industry also use relevant industry benchmarks and metrics to perform an extensive comparative analysis.
Remediation Support
Cyber security audit services are more than a process of providing you with a laundry list of vulnerabilities. As such, remediation support also goes beyond detailed reports and generic guidance.
Prioritize companies that provide quick turnaround on technical and remediation bottlenecks and offer extensive rescans to ensure the viability of patches released. This ensures holistic security for your firm and a clean report for your stakeholders.
Compliance Support
A cybersecurity audit service with compliance expertise is invaluable for organizations in regulated industries. Their compliance expertise can help map the audit findings to the specific control requirements mandated by the relevant regulations, such as HIPAA, GDPR, and SOC 2.
This mapping facilitates a better understanding of how your security posture aligns with regulatory requirements. Furthermore, they can provide practical insights on implementing appropriate controls and processes to achieve and maintain compliance year-round, potentially avoiding hefty fines.
Cybersecurity Audit vs Compliance Audit
| Feature | Cybersecurity Audit | Compliance Audit |
|---|---|---|
| Focus | Overall security posture and vulnerability identification | Adherence to specific regulations and standards |
| Methodology | May use a variety of frameworks (e.g., NIST CSF, ISO 27001) or a custom approach based on risk assessment | Follows a standardized framework mandated by the relevant regulation (e.g., HIPAA, PCI DSS) |
| Deliverables | A report outlining vulnerabilities, risk assessments, and remediation recommendations | A report confirming compliance or non-compliance with the specific regulation |
| Outcome | Improved security posture and reduced risk of cyberattacks | Fulfills regulatory requirements and avoids potential fines |
| Frequency | Can be conducted regularly or as needed | Typically conducted annually or at specific intervals mandated by the regulation |
| Cost | Varies depending on scope and complexity | May have fixed costs based on the specific compliance framework |
| Performed by | Internal security team, external cybersecurity professionals, or a combination | External auditors accredited for the relevant compliance framework |
Cybersecurity Audit Checklist
Preparation:
- Define Scope: Identify critical systems, data, and applications to be tested. Consider legal and regulatory requirements.
- Schedule Assessment: Choose a time with minimal disruption to business operations. Communicate downtime or access limitations clearly.
- Identify Stakeholders: Include IT staff, management, department heads, and any other stakeholders in data security.
Policy & Planning:
- Cybersecurity Policy: Draft a policy outlining security protocols, access controls, and incident response procedures if one doesn’t exist.
- Testing Tools & Techniques: Based on the scope and risk profile, select appropriate tools and techniques. Consider vulnerability scanners, PTaaS platforms, and social engineering simulators.
Testing & Reporting:
- Test Environment Preparation: Set up a dedicated testing environment to avoid impacting production systems.
- Conduct Testing: Execute planned tests according to chosen tools and techniques. Document findings meticulously.
- Analyze Results: Evaluate vulnerabilities, categorize risks based on severity and likelihood, and prioritize remediation efforts.
- Cybersecurity Audit Report: Create a comprehensive report detailing the scope, methodology, findings, risks, and clear recommendations for improvement.
Action & Improvement:
- Implement Recommendations: Develop a remediation plan and prioritize actions based on identified risks. Assign ownership and track progress.
- Monitor & Review: Regularly monitor security controls, conduct follow-up assessments, and review the effectiveness of implemented solutions.
Additional Considerations:
- Third-Party Vendors: Assess the security posture of third-party vendors handling sensitive data.
- Employee Training: Integrate security awareness training for all employees to identify and mitigate security threats.
Please note that while the above checklist applies to businesses of all sizes, it has been streamlined for small/mid-sized firms with simpler systems and smaller security teams. Larger organizations may need broader stakeholder involvement and diverse testing tools.
Top-rated by our customers





(Rated 4.6/5 on G2)

Final Thoughts
With the rising cyber threat landscape, a thorough cybersecurity audit is no longer a luxury; it’s a necessity. While choosing your audit partner, look beyond the shiny awards. Evaluate their experience, audit methodology, tools, communication, and remediation support.
Although the given list is far from exhaustive, it provides a detailed overview of some of the leading vendors to get you started. For example, Astra Security provides holistic audits, but Sprinto can be a good choice for compliance-focused testing.
Partnering with qualified cyber security audit firms helps you identify and address vulnerabilities, minimize risk, and ensure your organization remains cyber-resilient. Don’t wait for an attack to happen—take control of your security posture today.
FAQs
How much does a cyber security audit services cost?
A cybersecurity audit services can cost anywhere from $3,000 to $50,000, depending on various factors, such as the scope and complexity of the audit, the methodology, the experience of the auditor, geographic locations, additional costs of compliance, and more.
How long does a cyber security audit take?
A basic audit or scan can be completed in as little as 4-5 hours; however, for a more comprehensive assessment involving in-depth analysis of physical controls, technical infrastructure, and third-party vendor security, a cybersecurity audit can take several 15-20 business days.
What is the scope of an IT security audit?
An IT security audit examines an organization’s IT infrastructure, policies, and procedures to identify vulnerabilities and assess overall security posture. The number of targets varies based on the need and size of your firm.
Explore Our Cybersecurity Series
This post is part of a series on Cybersecurity. You can also check out other articles below.

- Chapter 1: 160 Cybersecurity Statistics 2026 [Updated]
- Chapter 2: Top Cybersecurity Trends Shaping 2026
- Chapter 3: How Cybersecurity Audits Can Help Organizations Being Secure?
- Chapter 4: How to Respond to a Cybersecurity Breach?
- Chapter 5: 6 Practical Cyber Security Tips for Startups on a Budget
- Chapter 6: Top 10 Cyber Security Audit Companies
- Chapter 7: Top 9 Cyber Security Assessment Companies
- Chapter 8: What Is a Cyber Security Report?
- Chapter 9: AI in Cybersecurity: Benefits and Challenges
- Chapter 10: How to Build a Cyber Security Culture?
- Chapter 11: What is CTEM (Continuous Threat Exposure Management)?