On average, Astra Security detected 5.33 vulnerabilities per minute in 2025, which is more than 7,000+ vulnerabilities per day in live environments. That’s the brutal math of the Modern attack surface. Without proper pentesting, each deployment cycle introduces multiple entry points for hackers, and each overlooked endpoint increases the risk of cyberattack.
The only way to flip the script is with online penetration testing tools that think like attackers, and hand defenders exactly what they need before the exploit chain completes. But selecting the right online penetration testing tool can be daunting, given the range of capabilities, pricing models, and depth.
To help, we’ve curated and compared the top 7 online penetration testing tools so you can choose the one that best matches your stack, compliance needs, and testing velocity.
Best Online Penetration Testing Tools in 2026
Top 3 Online Pentest Tools (Compared)
| Features | Astra Pentest | Nessus | Burp Suite |
|---|---|---|---|
| Scanner capacity | Unlimited continuous scans | Web apps, mobile & cloud | Web applications |
| Manual Pentest | Yes | No | Yes |
| Accuracy | Zero false positives | False positives are possible | False positives are possible |
| Vulnerability Management | Dynamic dashboard | Available at additional cost | No |
| Compliance | PCI-DSS, HIPAA, ISO27001, GDPR, and SOC2 | HIPAA, ISO, NIST, and PCI-DSS | PCI-DSS, OWASP Top 10, HIPAA, and GDPR |
| Integration | Slack, Jira, GitHub, GitLab, Jenkins, and more | IBM Security, Splunk, GitHub, and GitLab | Slack, Jira, Jenkins, GitLab, and more |
| Price | Starting at $1,999/yr | Starting at $4,236.20/yr | $449/user/yr |
Evaluation Criteria:
We selected only the top online penetration testing tools capable of delivering precise results with high flexibility.
Ranking was determined by
- The tool’s ability to execute complex and authenticated scans(Scanning behind the login mechanism).
- Lowest rates of false positives and false negatives(top priority).
- Support for continuous monitoring.
- Built-in feature for mapping vulnerabilities to local and international compliance standards. (e.g., PCIDSS, HIPAA)
Online penetration testing tools that excelled across these criteria ranked highest.
Before we get into the debate of which online penetration testing tool is the best for you, let’s see the power of online penetration testing in action. Try our free website scanner!

Our scanner detects malware, SEO spam, and security vulnerabilities (e.g., X-XSS-Protection headers) in seconds, without any complex process. Get hands-on experience on how online penetration testing tools can provide valuable insights into your website’s health.
Top 7 Online Pentest Tools To Know [Reviewed]
1. Astra Pentest [Get Started]
Key Features:
- Scanner Capacity: Unlimited continuous scans
- Manual pentest: Yes
- Accuracy: Zero false positives
- Vulnerability management: Offers a dynamic vulnerability management dashboard
- Compliance: PCI-DSS, HIPAA, ISO27001, GDPR, and SOC2
- Integration: Slack, Jira, GitHub, GitLab, Jenkins, and more
- Price: Starting at $1,999/yr. Want Better pricing, tailored to you. Book a call to unlock it
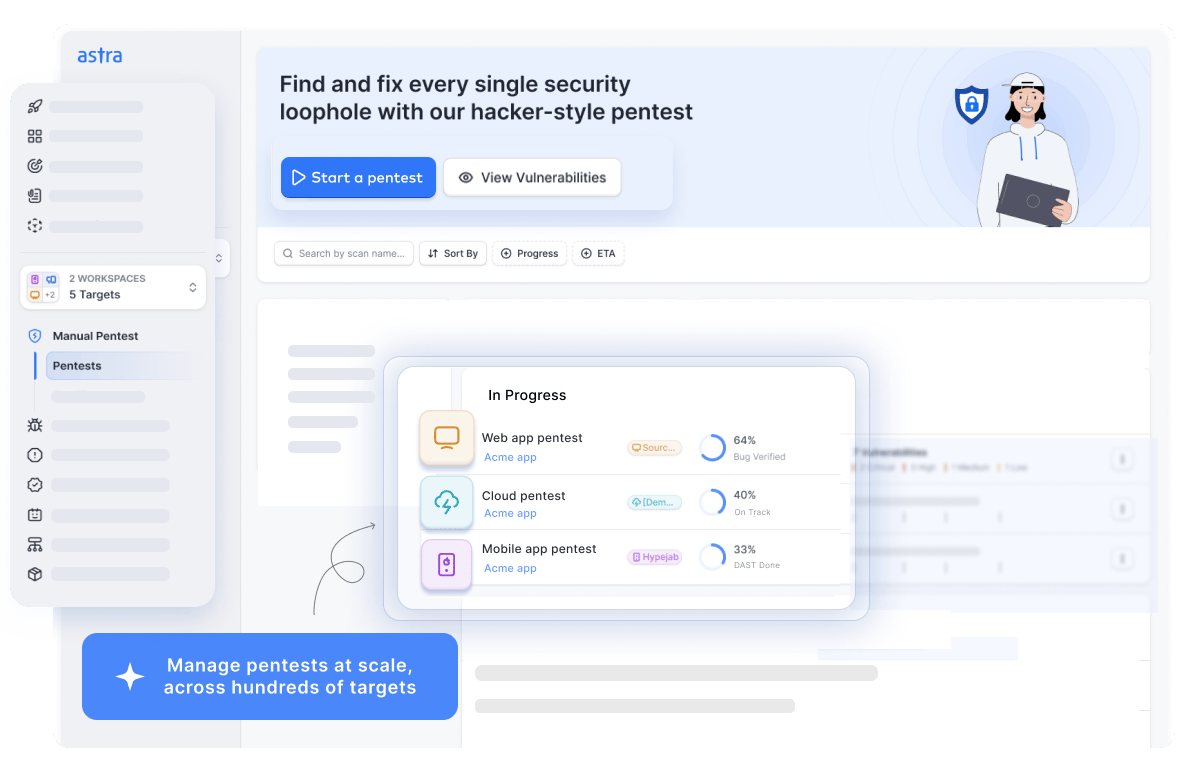
Astra Security stands out as a premier online pentest tool that delivers continuous, AI-enhanced pentesting tailored for organizations ranging from startups to global enterprises.
At its core, the platform runs over 15,000+ test cases against target assets, with test cases continuously updated to address emerging threats.
The reports are vetted by expert pentesters who provide manual penetration testing services and remediation assistance as needed. The penetration testing tool can seamlessly map discovered vulnerabilities to major local and global compliance( e.g., GDPR, HIPAA, PCI-DSS, and ISO 27001)
Over the past year, Astra has added ICICI, UN, and Dream 11, building on an already strong customer base that features brands like Ford, Gillette, and GoDaddy.
Pros
- Provides gap analysis and continuous scans.
- Leverages unique AI test cases.
- Provides a publicly verifiable certificate.
- Ensures zero false positives.
- Detects business logic errors and scans behind the logins.
Limitations
- 1-week free trial is available for $7.
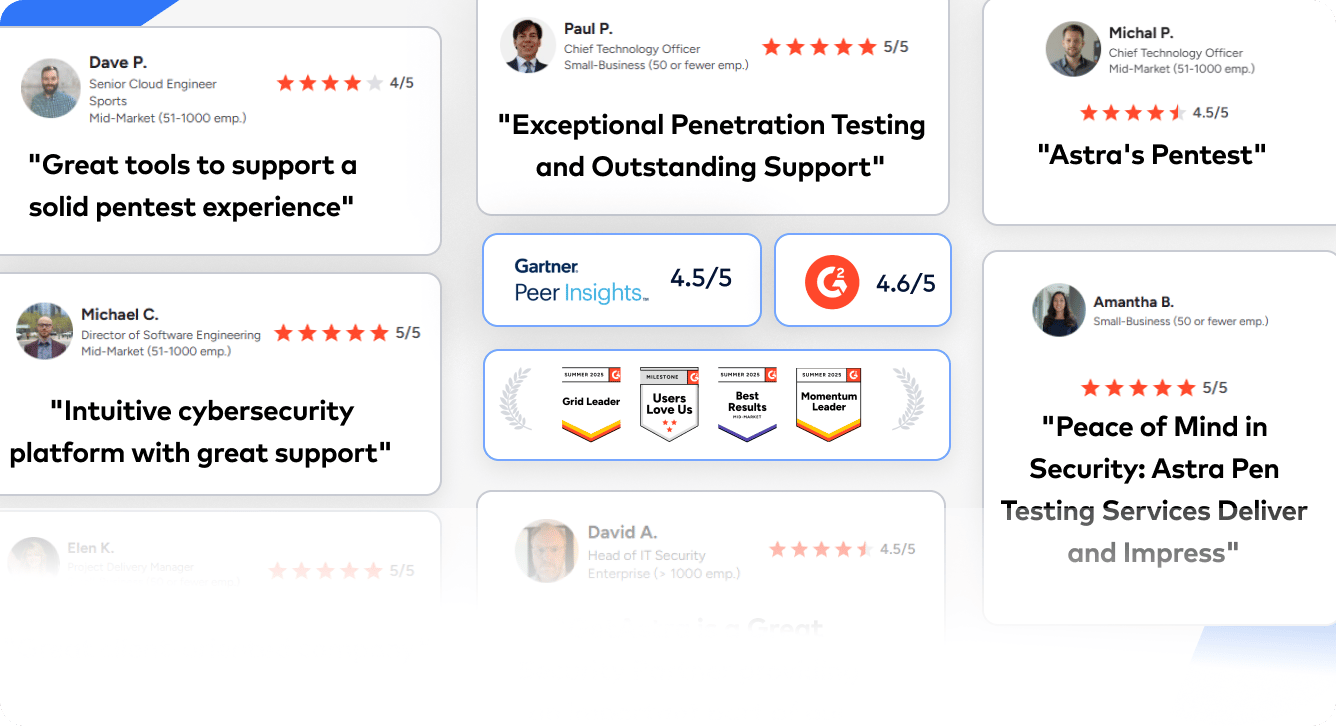
Experts Review
What our Customers Have to Say?
“I like how Astra Pentest provides everything from onboarding to certification in one dashboard, and I appreciate the responsive pentesters. It’s great not having to switch contexts; our team can track vulnerabilities, manage rescans, and pull certificates without leaving the platform. The initial setup was good, and I like that we can manage pentests across multiple surfaces without juggling different vendors”- SMB owner (Source: G2)
Searching for pentest companies online? 1000+ engineering teams picked Astra
2. Nessus
Key Features:
- Scanner capacity: Automated vulnerability scans for web apps, mobile & cloud
- Manual pentest: No
- Accuracy: False positives are possible
- Vulnerability management: Available at additional cost
- Compliance: HIPAA, ISO, NIST, and PCI-DSS
- Integration: IBM Security, Splunk, GitHub, and GitLab
- Price: Starting at $4,236.20/yr
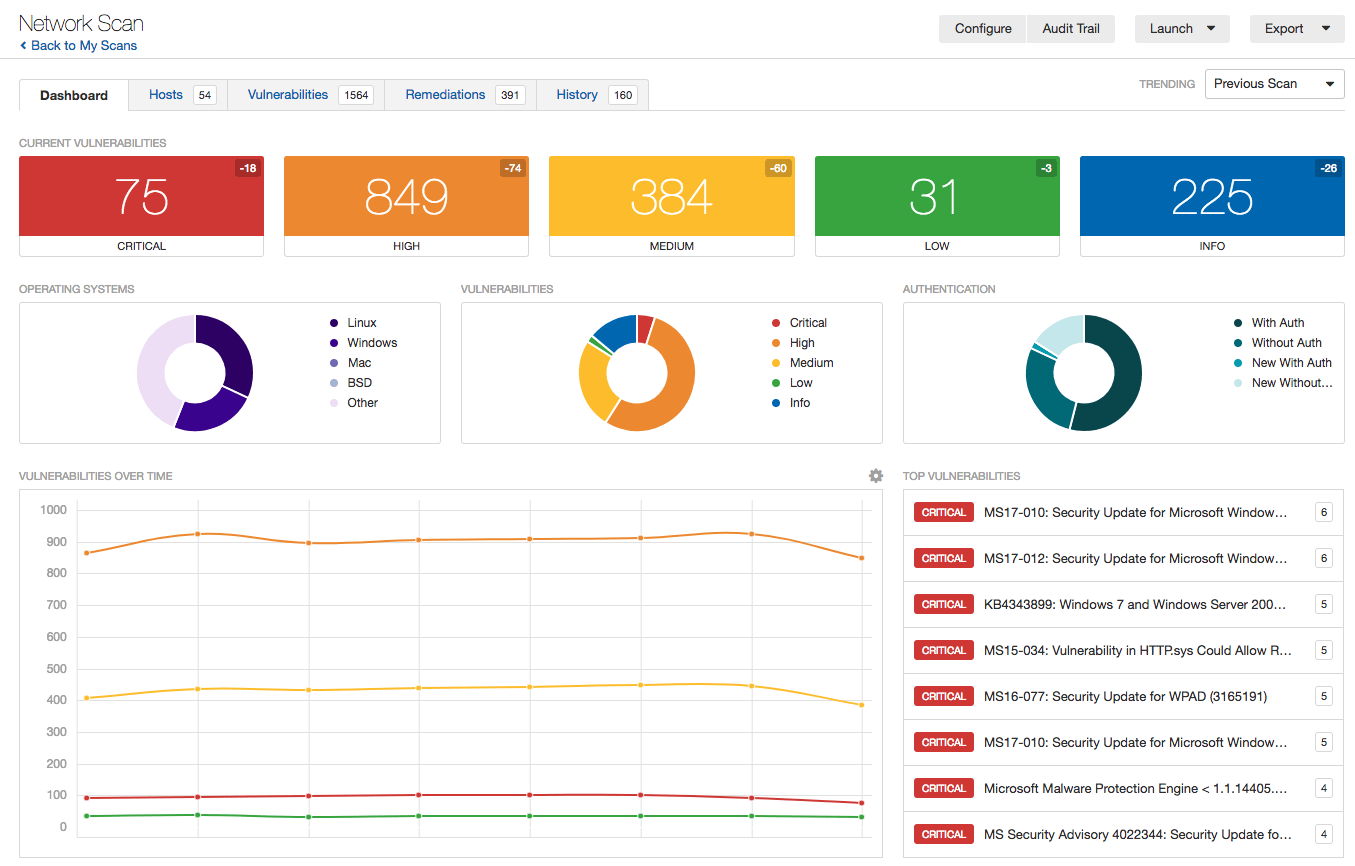
Nessus, developed by Tenable, is widely regarded as the industry gold standard for vulnerability scanning and assessment. Originally starting as an open-source project in 1998, it evolved into a leading commercial tool that helps organizations proactively identify security weaknesses across diverse environments.
Pros
- Supports compliance checks for standards like PCI-DSS, HIPAA, and ISO 27001.
- Scalable across small businesses to large enterprise environments.
- Malware detection and sensitive data discovery.
Limitations
- Can be resource-intensive and slow on large scans.
Experts Review
What do Customers Have to Say?
“It’s very user-friendly to start a basic scan of IP addresses. As a non-developer, I was able to learn the interface quickly and run the scan without much effort. The reports are audit-friendly, and we were able to submit them for compliance purposes.”- Senior Manager (Source: G2)
3. Burp Suite
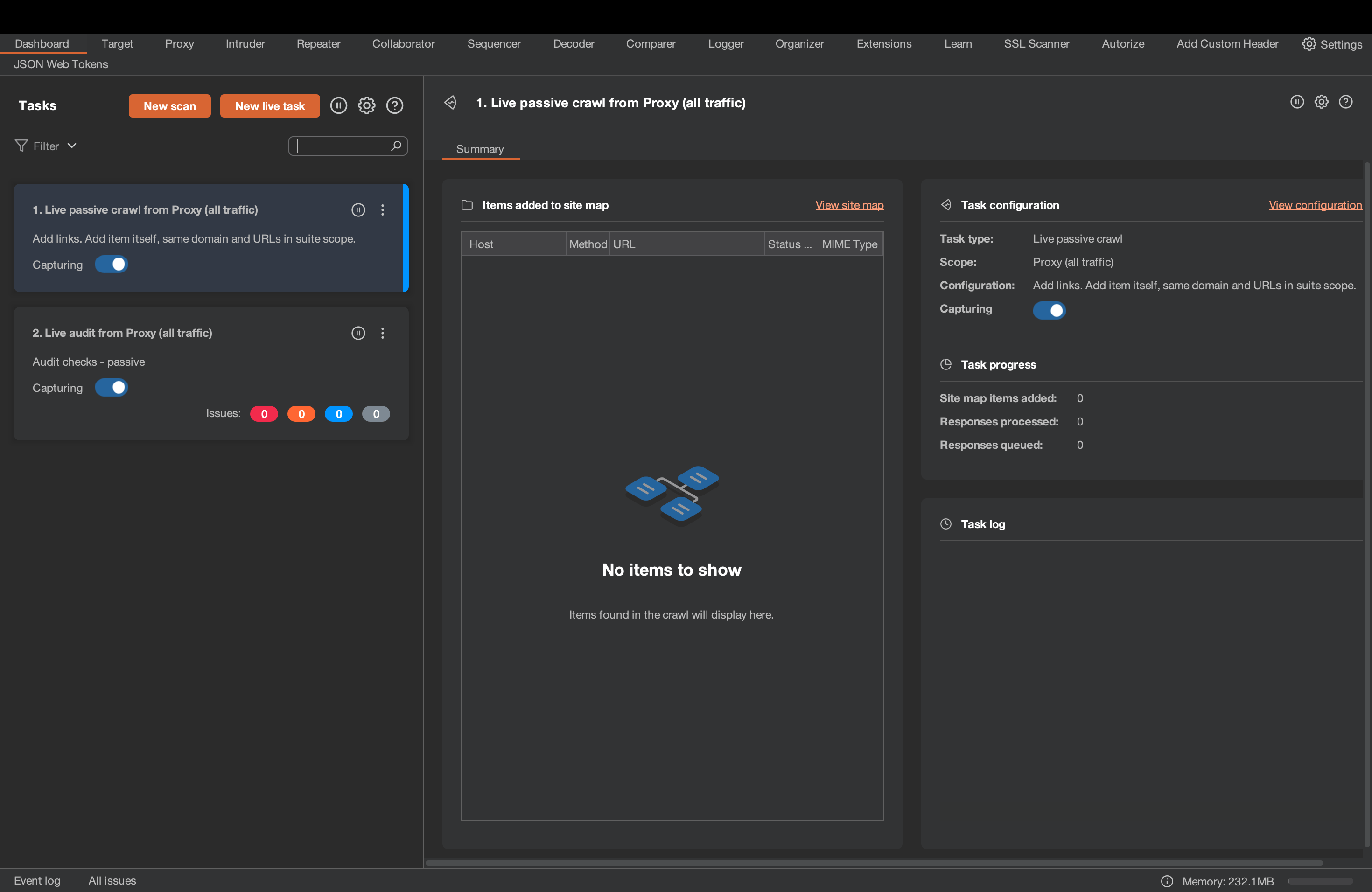
Key Features:
- Scanner capacity: Web applications
- Manual pentest: Yes
- Accuracy: False positives possible
- Vulnerability management: No
- Compliance: PCI-DSS, OWASP Top 10, HIPAA, and GDPR
- Integrations: Slack, Jira, Jenkins, GitLab, and more
- Price: $449/user/yr
Burp Suite is the industry-standard tool for web application penetration testing, developed by PortSwigger. It includes an intercepting proxy, repeater, intruder, decoder, comparer, and more for manual and (in paid editions) automated testing of web apps/APIs.
Pros
- Can crawl through complex targets with ease based on URLs and content.
- Cross-platform (Windows/macOS/Linux), easy install.
Limitations
- Crashes and socket connection errors have been reported.
- Can’t generate CISO-friendly reports like Astra Security’s scanner or multiple versions of reports for various audiences.
- It does not provide vetted online pentesting and scanning reports.
Experts Review
What do Customers Have to Say?
“Burp Suite is a powerful, user-friendly tool for web security testing. It combines awesome automated scanning feature with deep manual control, making it ideal for both beginners and pros. Its strong community support and all-in-one features make it a must have toolkit for ethical hackers and penetration testers.” – Security Researcher(Source: G2
“Although, open-source tools support testing various types of assets, choosing the right paid vulnerability scanners in combination with open-sources tools for your asset goes a long way in helping you stay ahead of vulnerabilities and be compliant towards various standards.”
4. Probely
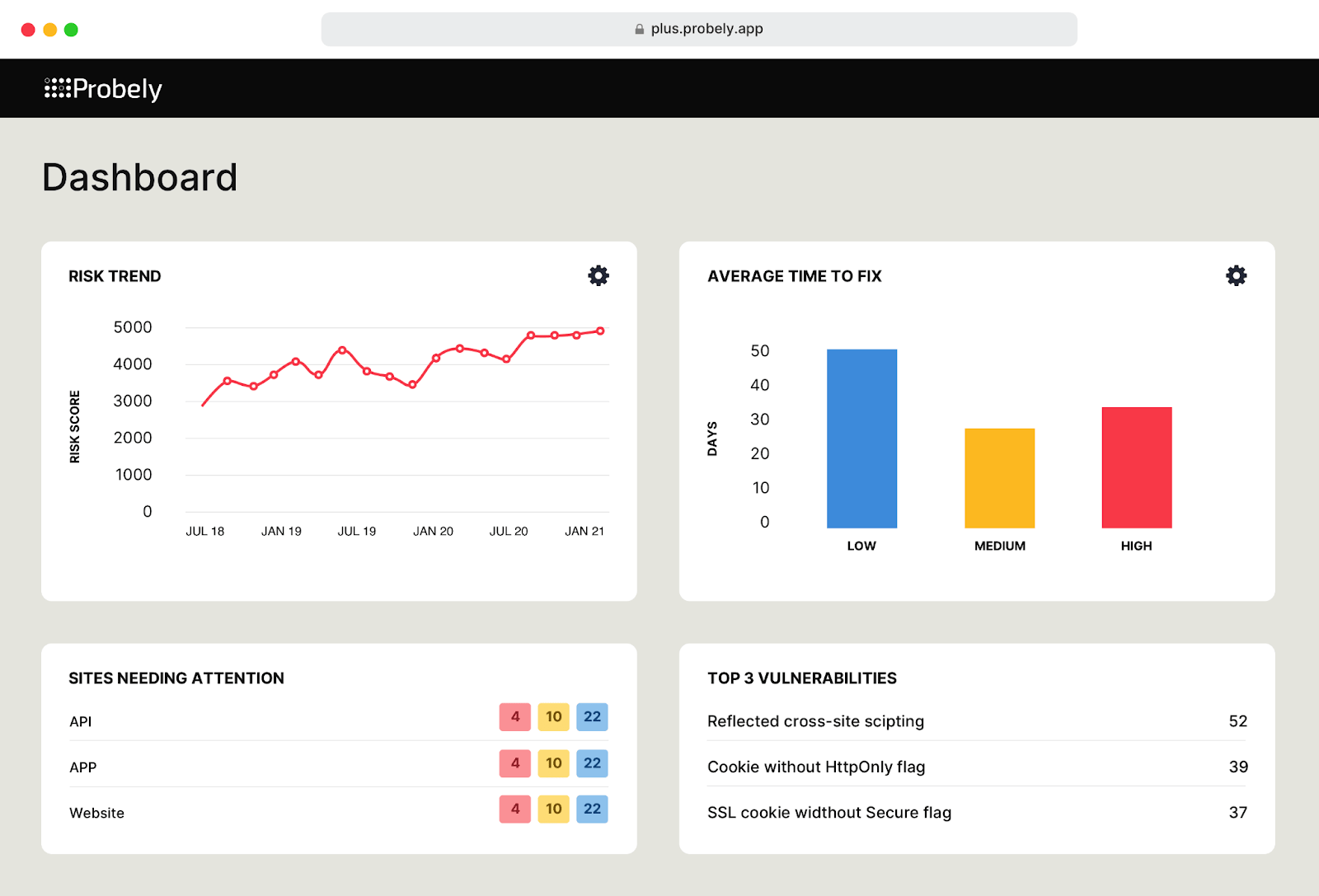
Key Features:
- Scanner capacity: Web applications and APIs
- Manual pentest: No
- Accuracy: False positives possible
- Vulnerability management: Patch management and zero-day mitigation
- Compliance: PCI-DSS, ISO27001, HIPAA, GDPR
- Integrations: Slack, JIRA, Jenkins, and GitHub
- Price: Starting at $1,180 / year
Probely is an online penetration testing tool for web applications and API scanning. It offers partial and incremental scans that automatically prioritize vulnerabilities based on risk and provide proof of legitimacy for each issue.
Pros
- Detailed management reports to assist compliance audits.
- Interactive dashboard.
- Scalable application scanning.
Limitations
- Limited functionality for detecting vulnerabilities.
- Custom vulnerability scoring does not align with general scoring.
Experts Review
What do Customers Have to Say?
“The implementation was fast, and it was easy to configure. It can take a subnet or a range for scanning in one go and gives a full report,t including the URL when scanning a web application.” – Senior Manager, Automotive (Source: G2)
5. Intruder
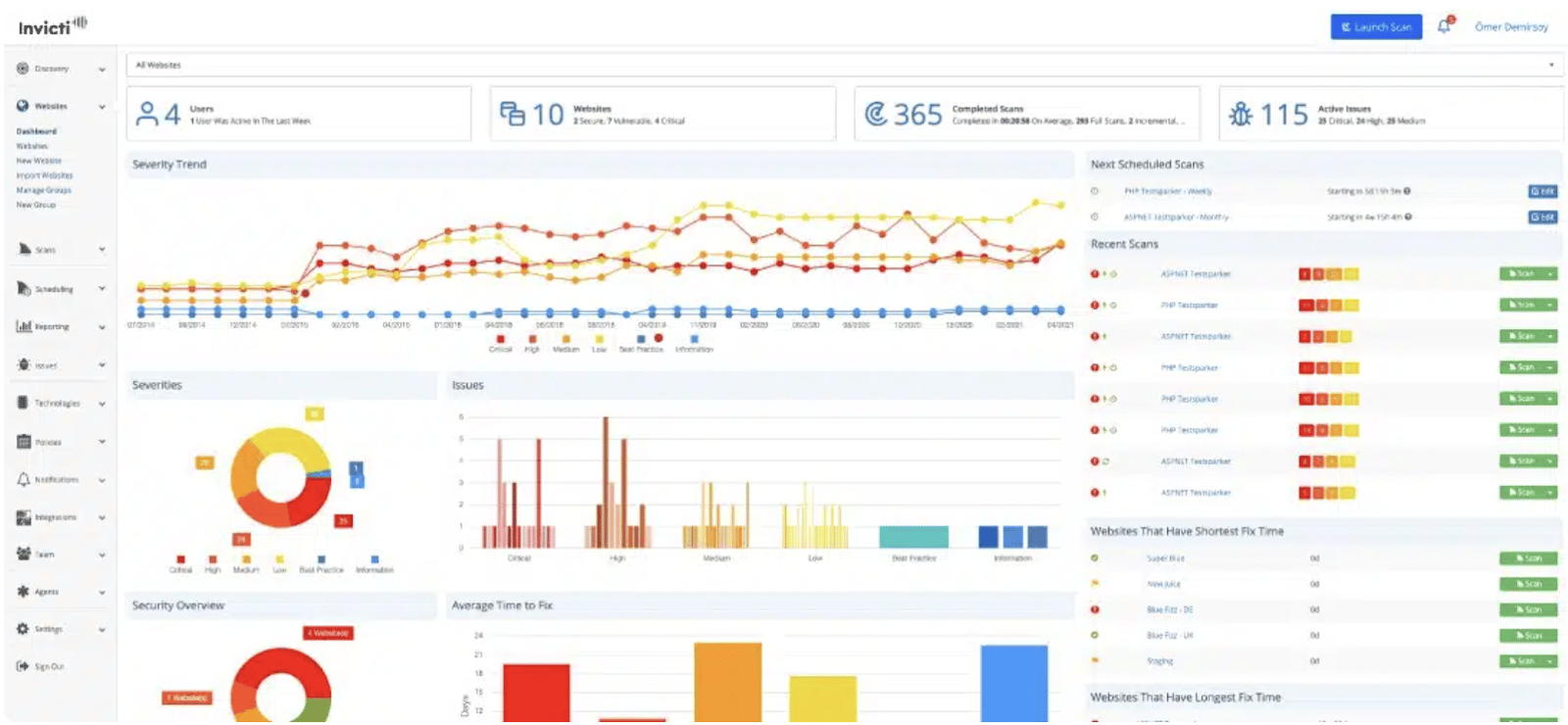
Key Features:
- Scanner capacity: Websites, servers, and cloud.
- Manual pentest: No
- Accuracy: False positives possible
- Vulnerability management: No
- Compliance: SOC 2 & ISO 27001
- Integrations: GitHub and JIRA
- Price: Starting at $1,958/yr
Intruder is an automated penetration testing software and vulnerability scanner that earned its name in cost-effective data protection. With effortless scaling capabilities for businesses of all sizes, it ensures continuous monitoring, compliance reporting, and attack surface scanning.
Moreover, its evidence-based reporting format and clear remediation steps help promote a proactive cyber risk education strategy.
Pros
- Real-time alerts for exposed ports.
- Vulnerability risk assessment and prioritization.
Limitations
- No publicly verifiable certificates.
- Lacks assurance of zero false positives.
Experts Review
What do Customers Have to Say?
“It does what we need it to do and requires very little interaction or maintenance on our part. We haven’t had any issues with it so far—it just works.” – (Source: G2)
6. Acunetix
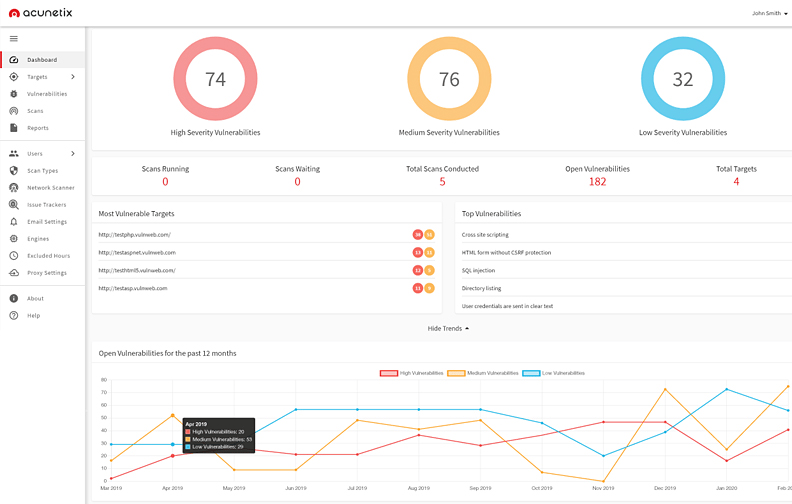
Key Features:
- Scanner capacity: Web applications
- Manual pentest: No
- Accuracy: False positives possible
- Vulnerability management: No
- Compliance: OWASP, ISO 27001, PCI-DSS, NIST
- Integrations: GitHub, JIRA, and Atlassian
- Price: Available on quote
Acunetix is a vulnerability scanner that offers effective online website penetration testing services. It effectively scans for over 4,500 vulnerabilities, including SQL injection and XSS scripting variants from the OWASP Top 10.
Pros
- Reduces false positives with proof of concept.
- Automates regular scans.
Limitations
- Lack of transparency with no official pricing plans.
- Vulnerability proof of exploits can be complex for beginners.
Experts Review
What do Customers Have to Say?
“This is a very good product that is also user-friendly. Its accuracy in finding vulnerabilities is impressive.” – Senior Security analyst (Source: G2)“
7. Rapid7
Key Features:
- Scanner Capacity: Web Applications and Cloud Infrastructure
- Manual pentest: Yes
- Accuracy: False positives possible
- Vulnerability management: Yes
- Compliance: CIS, ISO 27001, and PCI DSS
- Integrations: ServiceNow Security Operations, LogRhythm NDR, and ManageEngine
- Price: Available on quote
Last but not least, Rapid7 is a popular online pentesting tool that offers vulnerability scans, pentests, and Security Orchestration and Automation Response (SOAR) as part of its diverse portfolio.
Pros
- Perfect for beginners and experts alike.
- Continuous addition of risk checks.
Limitations
- Customer support turnaround can be slow.
- No expert remediation is available.
Experts Review
What do Customers Have to Say?
“We’ve used Rapid7 for our Vulnerability Testing and Alert Messaging, Threat Intelligence, Risk Management, Endpoint Protection, etc. They have proved to be invaluable in providing a complete and effective solution.”- Enterprise user (Source: G2)
Are there any Free Online Penetration Testing Tools?
Yes, there are many free and open-source penetration testing tools available at no cost. However, these tools are not suitable for business. Most tools are standalone rather than an all-in-one suite and require technical expertise to run a pentest.
As a result, they are generally more suitable for experienced penetration testers than for organizations looking for a streamlined, enterprise-ready security solution.
| Primary Scanning Approach | Black-box crawling + active fuzzing (payload injection into forms/URLs) | YAML template-based detection | recon → service detection → targeted checks + auto-report generation |
|---|---|---|---|
| Coverage Focus | 30+ modules: SQLi, Log4Shell/Spring4Shell, Shellshock, subdomain takeover, CMS fingerprinting etc | 12,000+ community templates: CVEs, misconfigs, exposed panels, default creds, etc | subdomain enum, exposed services/panels, misconfigs API discovery. etc |
| Depth vs. Breadth | Deep per-app fuzzing (form/parameter injection, auth support) | High-precision, targeted checks | High breadth for internet-facing assets |
| Reporting & Output | Multi-format: HTML, XML, JSON, TXT, CSV; session resume (sqlite3) | JSON/structured output, integrations (dashboards in Pro) | Outstanding auto-generated human-readable reports |
| Use Case Strengths | Simple, set-it-and-forget-it black-box testing for injection flaws in web apps/APIs | Rapid CVE/misconfig hunting, CI/CD gates | CSIRT/large-org recon, automatic vuln notification & posture improvement |
| Maintenance Status (2026) | Actively updated (v3.2.10+ in late 2025, Python 3.13/3.14 compat) | Very active (v3.7.0+ in 2026, frequent releases, 12K+ contributors) | Actively maintained by CERT PL (v2.7.0+ docs, GSoC support, ongoing modules) |
| Limitations | Higher noise | Template quality varies | Not a deep DAST & setup requires Docker/K8s familiarity |
What are the Benefits of Using Online Penetration Testing Tools?
Studies consistently proves that more than 60% of successful cyberattacks stem from unpatched simple vulnerabilities rather than sophisticated zero-day exploits. Online penetration testing tools directly address this gap by continuously scanning digital assets for exploitable flaws before adversaries can weaponize them.
Below are some of the most impactful benefits organizations gain from adopting online penetration testing solutions.
- Proactive Risk Identification – Detect vulnerabilities like SQLi, exposed APIs, before they become breach vectors.
- Easy to Use – Online pentesting tool eliminates the complex installation and infrastructure setup. Security teams can launch scans quickly through a centralized dashboard with little configuration.
- Data-Driven Security Posture – Online pentesting platforms provide measurable insights into vulnerability trends, risk scores, and recurring issues. This allows the team to track security maturity over time.
How to Choose an Online Pentest Tool?
The pentest tool you choose becomes a core component of your security validation strategy and directly influences your overall security posture. A poorly selected tool can generate excessive noise, overlook critical attack paths, or fail to integrate seamlessly with your operational workflows.
Here are some essential features you should look for in your online penetration testing tool.
☐ AI-powered vulnerability detection
Does the tool use AI or adaptive intelligence to detect emerging threats, business logic flaws, and exploit chains?
Pro Tip: Astra offers in-depth AI-powered vulnerability scanning capabilities, and test cases are updated regularly to help keep pace with new and emerging CVEs.
☐ Context-Aware Risk Prioritization
Does it prioritize vulnerabilities based on exploitability and business impact rather than just CVSS scores?
☐ Low False Positive & False Negative Rates
Are findings vetted by security experts to eliminate false positives?
☐ Scan Behind Login Functionality
Can the scanner test authenticated areas without constant re-authentication issues?
Pro Tip: Astra’s login recorder Chrome extension uses your credentials once and keeps the scanner running
☐ Built-In Compliance Mapping
Does the tool automatically map vulnerabilities to frameworks like PCI-DSS, HIPAA, ISO 27001, SOC 2, and GDPR?
☐ Audit-Ready Reporting
Does it generate multiple reports for various stakeholders involved in penetration testing?

☐ CI/CD Pipeline Integration
Does it integrate seamlessly with Jenkins, GitHub, GitLab, Jira, Slack, and other tools?
Final Thoughts
A strong security strategy is incomplete without an online penetration testing tool. The top 7 online penetration testing tools highlighted above provide structured ways to identify and remediate vulnerabilities quickly.
Organizations can choose from these comprehensive platforms or, if they have the expertise, experiment with open-source tools to conduct testing independently.
In short: prioritize a tool (Suite or combination of tools) that offers strong coverage across compliance mapping, centralized vulnerability management, automated remediation workflows, and seamless integrations with your existing development and operations stack.
FAQs
What is the timeline for a comprehensive pentest?
A comprehensive penetration test typically takes 10-15 business days from scoping to final report, including 5–10 business days of active testing and 3–5 business days for reporting and retesting. Small applications may finish in 5 business days, while large or complex environments often require 20+ business days of hands-on effort
What is the cost of online pentesting?
One-time traditional pentests generally range from $5,000 to $50,000+, while subscription-based online PTaaS platforms usually cost $3,000–$12,000+ per month, depending on scope, assets, and depth.
Pricing varies widely based on organization size, testing intensity, compliance needs, and various other factors.
How often should you perform online pentesting?
For organizations with frequent code changes, cloud expansions, or high-risk profiles, regular pentesting is strongly advised to catch vulnerabilities introduced by updates and maintain a strong security posture against evolving threats.
Explore Our Penetration Testing Series
This post is part of a series on penetration testing.
You can also check out other articles below.

Chapter 1: What is Penetration Testing?
Chapter 2: Different Types of Pentest Testing
Chapter 3: Top 5 Pentest Methodology
Chapter 4: Top Pentest Companies to Consider in 2026
Chapter 5: Best Pentest Online Tools – Top List
Chapter 6: A Super Easy Guide on WordPress Pentest
Chapter 7: Average Penetration Testing Cost in 2026
Chapter 8: Pentest Reporting (Sample Report)
Chapter 9: Web App Pentest Guide
Chapter 10: Pentest Website Guide