DDOS attacks are becoming increasingly more frequent, and there doesn’t appear to be any signs of slowing down. In fact, according to recent studies, DDOS attacks are expected to increase by over 300% in 2023. This is a major concern for businesses and individuals alike, as these attacks can cause serious damage to both personal and business-related websites.
In this article, we will take a closer look at DDOS attack statistics 2026 and what you can do to protect yourself from these devastating assaults.
Is DDoS Just the Opening Move?
In the last 12 months, Astra uncovered 5.33 vulnerabilities per minute, and many weren’t just about taking services offline. DDoS is increasingly used as a cover while attackers exploit more profound weaknesses.
The State of Continuous Pentesting 2025 shows how:
- Web apps made up 96% of all vulnerabilities
- Cloud misconfigs, API flaws, and leaked credentials are often hit mid-DDoS
- Manual pentests surfaced nearly 20x more unique risks than scanners caught
A spike in traffic might not be the breach, but it’s often the smoke screen for one.
Top DDoS Attack Statistics 2026
Here are some of the top statistics of DDoS attacks from 2020-2026.
- According to Kaspersky’s quarterly report, nearly 57,116 DDoS attacks were reported.
- Cloudflare states that there was a 67% increase in ransom DDoS attacks in 2022.
- In a week Friday was the busiest day of attacks with 15.36% while the percentage of attacks was lowest (12.99%) on Thursday.
- Companies in the U.S., the U.K., and Canada were affected by the DDoS attacks on VOIP providers in 2022.
- In the second quarter of 2021, DDoS attacks later 30 minutes, which in 2022 increased to 50 minutes.
2022 saw some extraordinary DDoS attacks, especially in the third quarter. The world witnessed several record-breaking and ultra-ambitious attacks. These attacks are often politically motivated and can be launched from multiple geographies at the same time.
On June 1 an attack on a Google Cloud Armor customer broke quite a few records.
- A sequence of HTTPS DDoS attacks hit a record-breaking peak at an astonishing 46 million requests per second.
- This is the largest application-level DDoS attack reported to date, larger by 77% than the second-largest attack ever reported.
- This attack was launched from more than 5,000 IP addresses spanning 132 countries.
- 30 percent of the traffic sent during this attack was from four countries, Brazil, India, Russia, and Indonesia.
Before we move forward with more DDoS attack statistics, let us quickly brush up on our knowledge of DDoS attacks.
What is a DDoS Attack?
A DDoS attack is when someone sends a ton of internet traffic to one specific server or network in an attempt to overload the system and cause normal service to be interrupted.
DDoS attacks are successful when they involve many different hacked computer systems that act as sources of traffic for the attack. These machines can be regular computers or other internet-connected devices, such as IoT devices.
Imagine a busy highway with all of a sudden, too much traffic trying to get on it at once. This is what a DDoS attack does; entirely flooding the server so that no incoming/regular traffic can access it.
The movements of DDoS attacks have been quite convoluted since 2022
Since DDoS springs from various socio-political motives, global politics and economics often contribute to the attack patterns. The following are some interesting bits from Cloudflare’s DDoS threat report.
- HTTP DDoS attacks increased by 111% in 2022 from 2021 and Ransomware attacks increased by 67% during the same period.
- The QoQ statistics are a bit different with a 10% decline in Q3 from Q2.
There are some unbelievable deviations from this pattern in certain geographies.
- Taiwan experienced an alarming 200% spike in HTTP DDoS attacks between the second and third quarters of 2022.
- Attacks on Japan increased by 105% in the same period.
The 2017 Attack on Google
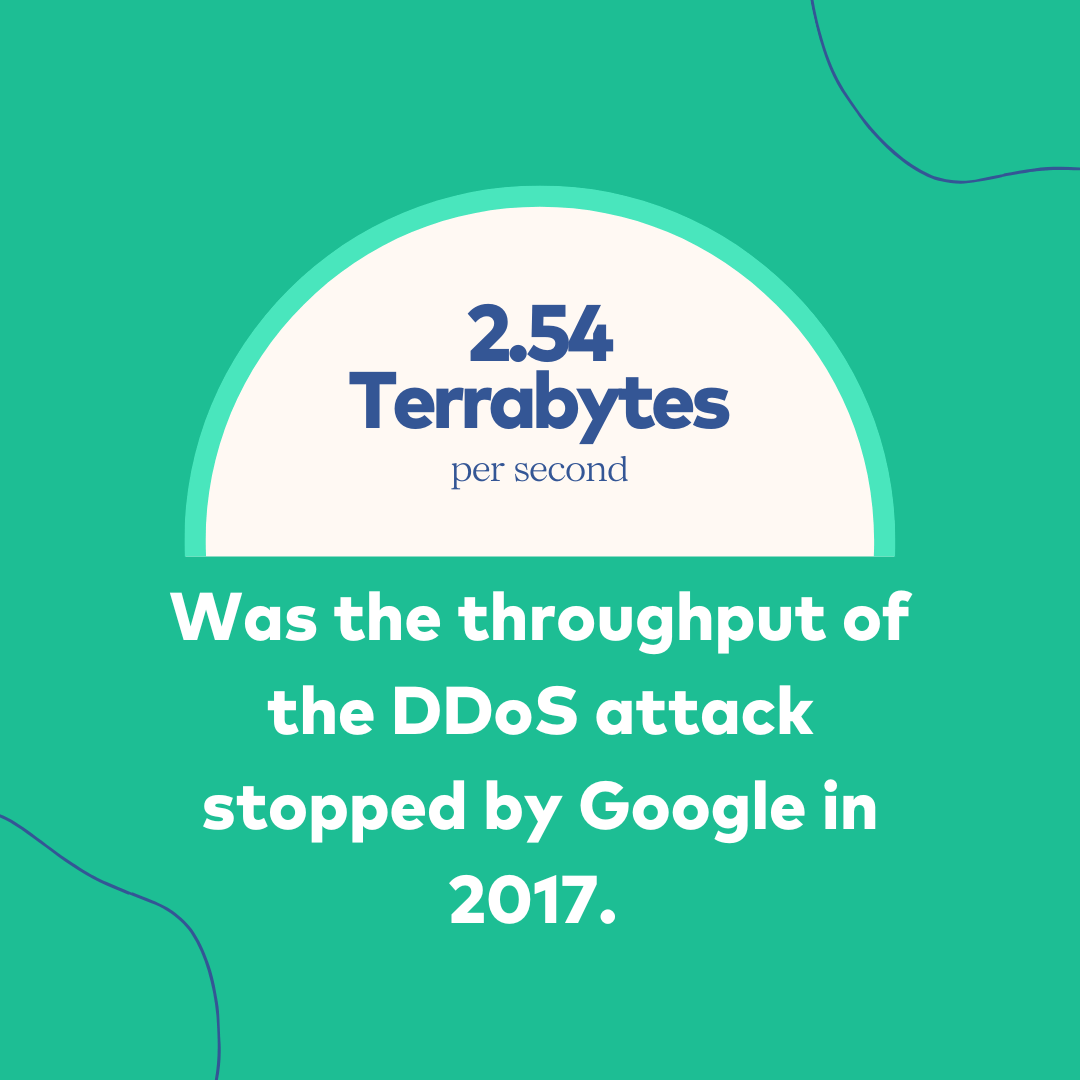
On October 17, 2020, a report by Google cloud revealed that they had stopped a massive DDoS attack in 2017.
- The DDoS stopped by Google had a throughput of 2.54 Terabytes per second.
- The same report also revealed an exponential growth in all metrics related to DDoS attacks.
- Between 2010 and 2020 the number of requests per second recorded in the largest reported DDoS attacks increased 10 folds from 600,000 requests per second to 6 million requests per second.
- In terms of network packet rate, it took just 6 years to reach 690 million pps from 230 million pps.
The 2018 Attack on GitHub
The attack on GitHub on 28th February 2018 employed the Memcached DDoS method where instead of using botnets, the hackers used a database caching system to amplify the attack.
- The attack, at its peak, reached 1.35 Tbps and 126.9 million packets per second.
- Using Memcached, the hackers achieved an amplification factor of 51000.
- For every bit of data sent by the hackers, the GitHub server received 51KB of data.
- In late 2018, the FBI achieved great success by taking down twelve DDoS-for-hire marketplaces. But then in April of 2019, Europol went one better and completely shuttered Webstresser -the world’s most significant hub for DDoS attacks with more than 130 thousand registered users.
The Time of DDoS
- Between 2019 and 2020, attacks that served over 100 GB/s of data increased by 967 percent.
- In Q2 of 2019, Kaspersky discovered an even longer attack while analyzing commands sent to different DDoS networks—this one had lasted 509 entire hours.
- By 2022, DDoS activity levels had increased from prior years and the attacks now lasted longer as well. Previously, in Q2 of 2021, DDoS averaged 30 minutes; by Q2 of 2022 however, they were averaging 50 hours.
- The average DDoS attack only lasted 390 seconds in Q3 2022, but these shorter burst-style attacks are used to test the victim’s defenses more frequently than longer ones.
Corero’s most recent report found that very few DDoS attacks come close to fully occupying uplinks, with
- Only 0.6% reach “full pipe” usage of more than 95%.
- Of those that did reach full usage levels, almost all only lasted 10 minutes or less.
The Attacks Kept Getting Bigger
In February 2020, an AWS customer faced a massive DDoS attack that exploited a vulnerable CLDAP server and launched an attack that amplifies the amount of data sent to the victim’s IP address by 50-70 times.
- The throughput of the attack on the AWS customer peaked at 2.3 Tbps and lasted for 3 days.
In November 2021, Microsoft had to contend with a Distributed Denial of Service (DDoS) attack targeted at an Azure client. The attack was massive by all means.
- The throughput peaked at 3.45 Tbps and the packet rate was 340 million pps.
Activision Blizzard games were attacked again.
- The servers of games like Call of Duty and Word of Warcraft faced DDoS attacks.
- In Q3 2022, network-layer attacks on gaming and gambling companies increased by an astonishing 405% from the previous quarter.
There’s no way to tell if these attacks were motivated by the potential merger of Microsoft and Activision Blizzard.
Region-Based DDoS Attack Facts
The years 2021 & 2022 saw an uptick in cyber threats from nation-states. For example,
- The government of Montenegro fought off DDoS attacks that were allegedly sponsored by Russia.
- Albania had to deal with a similar issue, but it’s likely that Iran was behind those attacks.
- Large-scale DDoS attacks hit New Zealand hard in Q3 2021.
- In Q3, companies in Britain, Canada, and the US were Ransom DDoS attacks on VoIP providers.
- As the September 26 elections for seats in parliament approached, hackers targeted the website of Germany’s Federal Returning Officer.
- According to Kaspersky, 43.25% of the world’s DDoS attacks in Q2 2022 were directed at the US- more than any other nation.
- China and Germany experienced 7.91% and 6.64% of reported attacks, coming in second and third place respectively.
DDoS Attacks Around the Ukraine War
There has been a lot of give and take in the cyber front between Ukraine and Russia over the last year. For instance, a pro-Russian group of hackers has been active since January 2022 and has taken responsibility for a bunch of attacks.
- More than 200 Estonian sites fell victim to Killnet, including the ESTO AS payment system.
Anti-Russia Hacktivists have Responded in Kind
- Otkritie Bank reported problems with its internet banking facilities and mobile app.
- In the initial two months of Q3, 2022, Sberbank defended itself from a formidable 450 Distributed Denial-of-Service assaults. The number equals the number of DDoS attacks they faced in the last five years.
- A report suggests that more than 20 Russian video conferencing platforms including TrueConf were attacked.
The Cost of DDoS Attacks
- A Ponemon Institute study revealed that during a DDoS attack, every minute of downtime costs $22,000.
- The restoration of services and operations after an attack can cost a small or midsize business $120,000.
- Application-layer DDoS attacks caused online industries more damage than any other type of attack, with a 131% increase from the previous quarter (and 300% year over year).
During a DDoS attack, every minute of downtime costs $22,000.

Multivector DDoS attacks are the norm
- In 2020 Link11 security researchers discovered an attack that used 14 different vectors.
- In the first quarter of 2019, more than half of all cyberattacks included two or more vectors. In addition, almost 50 percent were composed of three distinct vectors. This is a vast increase from only 11 percent recorded in 2018 and 8.9% documented in 2017.
- Over 62% of all DDoS attacks are the result of UDP assaults. Even though SYN is still a large threat at 20.25%, TCP has recently become much more popular, with 11.4%.
To launch a DDoS attack, botnets are typically used to target a single server with requests from various locations.
- There are over 15 million “DDoS weapons”, or infected IP addresses being utilized for these types of attacks currently in circulation globally.
- The most common malware employed to create botnets for DDoS purposes is Mirai; however, other variants do exist as well.
Steps to Take to Prevent DDoS Attacks
Create a DDoS Response Plan
To ensure your staff members are responsive and efficient if a DDoS attack arises, it’s critical to create an incident response plan that outlines:
- Knowing precisely how to respond during and after a DDoS attack is of vital importance.
- Maintaining business operations.
- Key stakeholders and go-to staff members.
- Escalation protocols.
- Team responsibilities.
- A list of required tools.
- A list of systems essential to achieving our mission.
Ensure High Levels of Network Security
The following are types of network security that can protect your business from DDoS:
- Firewalls stop unapproved people from accessing specific computer networks. Intrusion detection systems watch for unusual or unauthorized activity, alerting network administrators to possible security breaches.
- Endpoint security is an effective way of safeguarding laptops, desktops, and smartphones from malware infection and further spread. This type of protection helps secure the devices that are connected to a network from malicious activities.
Continuous Monitoring of Network Traffic
The advantages of using continuous monitoring (CM) to analyze traffic in real-time are as follows: CM provides an objective and expedient method for detecting early signs of DDoS activity.
- DDoS protection doesn’t just defend your website during an attack, but it also prevents attacks before they even happen.
- By creating a pattern of regular network activity and traffic, the team can rapidly detect any unusual behaviors.
- With the 24/7 continuous surveillance of up-to-date tools, signs of any potential attack are not only detected during normal office hours but also on weekends and after hours.
The CM tool can be configured to either automatically contact administrators if a problem arises or follow prescribed scripts in response to an issue.
Regular Vulnerability Scans and Penetration Testing
DDoS attacks often leverage dormant vulnerabilities in applications and networks. These vulnerabilities may be introduced by code updates, third-party risks, outdated software, etc. With regular vulnerability scans and penetration testing, you can ensure that none of these vulnerabilities can take root.
Bottomline
Distributed denial of service attacks are common, and their effects can be devastating. As a CISO or CIO, it is your responsibility to keep any possibilities of a DDoS attack at bay – if there is a vulnerability, it will be exploited at some point.
The best course of action for you would be to partner with a security solution provider like Astra Security, which can offer you deep insight into your security posture, detect vulnerabilities, and help you fix them, and at the same time help you set up solid preventive security measures to thwart any attempt by malicious actors to launch a DDoS attack in 2026.