With the advent of technology, the number of mobile phones has increased manifold in the past decade. The number of mobile phones is growing at a tremendous rate, and so are the applications running inside these mobile phones. The modern world has become mobile-centric. Apple’s iOS mobile operating system held around 14.1 percent of the global smartphone market share in the second quarter of 2021. There are more than 900 million active iPhones globally, and the Apple App Store has more than 2.22 million available iOS devices.
This means that there is a massive potential for cybercriminals to exploit security vulnerabilities and attack these devices. This is where iOS penetration testing comes in.
With millions of iOS apps in use, even one overlooked flaw can put your users’ data at risk. [Book Your Free iOS Security Demo]
What is iOS penetration testing?
Insecure iOS applications have been a serious concern for a long time. Due to the popularity of these apps, the insecurities have also similarly increased in number.
iOS penetration testing is the process of identifying and exploiting vulnerabilities in iOS applications. The method may include decompiling the application to identify any defects that could lead to bugs or using an automated pentest tool to do this. It is a series of tests designed to exploit vulnerabilities in the iOS operating system and network security, from installation and configuration to identifying and exploiting software and hardware vulnerabilities.
It is one small security loophole v/s your Android & iOS app.
Get your mobile app audited & strengthen your defenses!
Understanding mobile app security issues in iOS
The OWASP Mobile Security Project is a centralized resource intended to give developers and security teams the resources to build and maintain secure mobile applications. This project aims to address the current need for developers to create mobile applications that also include security, as it is crucial for users to know that their sensitive data and access credentials are protected.
According to OWASP Mobile Security Projects, the following is the list of vulnerabilities most commonly found in mobile devices.
- M1: Improper Platform Usage: The issue refers to improper or mismanaged use of mobile platform security controls. This can be anything from file permissions, microphone permissions, application lock to fingerprint sensors.
- M2: Insecure Data Storage: Insecure Data Storage happens when the developers avoid encryption of sensitive data and store that in clear text, which is readily available to any hacker/attacker on code decompilation.
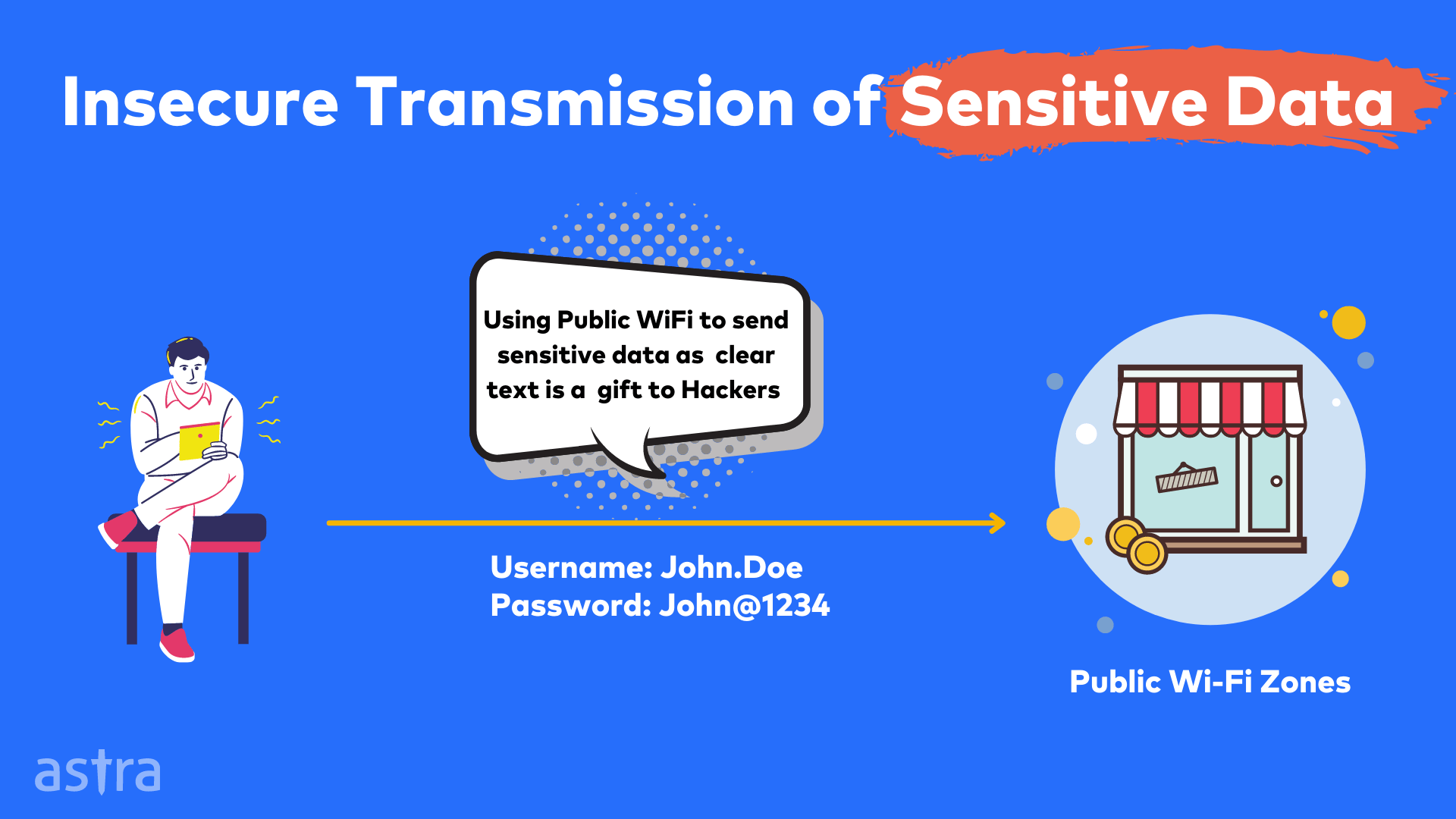
- M3: Insecure Communication: Insecure communication happens when sensitive data such as usernames and passwords are sent over public channels such as WiFi. Hackers use a man-in-the-middle attack to read the unencrypted data from these public networks.
- M4: Insecure Authentication: Weak Authentication is one of the root causes of many security risks. Attack vectors such as authentication bypass, information disclosure via debug messages, session invalidation are typical examples of insecure authentication.
- M5: Insufficient Cryptography: Cryptography is the process of converting plain text data to an unreadable form. Most developers tend to ignore cryptography as it’s complex to implement it and cyber-criminals or hackers, on the other hand, take full advantage of it.
Also Read: API Penetration Testing: What You Need to Know
- M6: Insecure Authorization: Proper authorization is a crucial aspect of the CIA triad. Many mobile applications have improper authorization implemented due to which low-level users can access information of any high privileged user. Improper authorization give rise to many business-level vulnerabilities as well.
- M7: Client Code Quality: Maintaining code quality while developing mobile applications is an essential task. Attacks such as buffer overflow, cross-site scripting, blind XSS happens due to bad code quality, which leads to insecure design.
- M8: Code Tampering: Code Tampering refers to a process in which bad actors such as hackers or attackers exploit code modification via malicious forms of the apps hosted in third-party app stores available over the internet.
- M9: Reverse Engineering: Reverse Engineering is a process to decompile the mobile application to understand the application logic. To prevent attackers from reading the application code and understanding the logic, code obfuscation is done.
- M10: Extraneous Functionality: Bad actors such as cyber-criminals or hackers try to understand the mobile application’s extraneous functionality. The main goal is to understand and explore hidden functionalities of the backend framework.
Inbuilt Security for iOS Applications
Following are the two most crucial inbuilt security features that Apple provides to keep iOS applications secure.
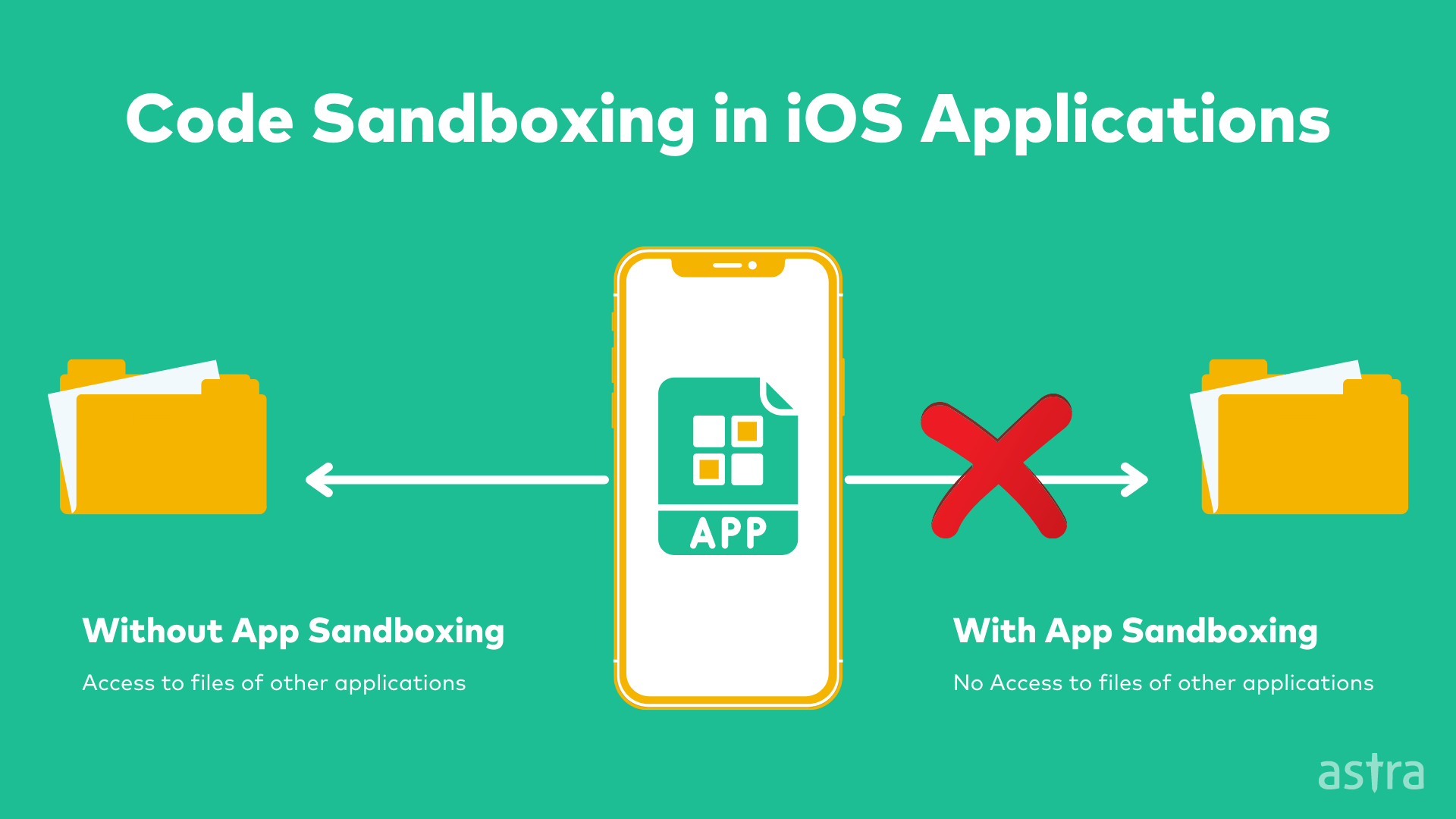
1. App Sandbox
All apps are running on the iOS run in a sandbox. App sandbox protects your app from other apps trying to make unauthorized access to any data you might be storing, such as passwords, payment information, and personal data like photos. No other app can read or modify this data. That’s what sandboxing is all about!
Trusted by 1,000+ global companies to secure their mobile apps from real-world exploits – Get your iOS app tested by experts today. [Book Your Free iOS Security Demo]
2. Data Protection API
iOS has always had a way to protect sensitive data on the device. But now that it is now possible to access this data via the Data Protection API, it is now possible to build apps that can protect their data with encryption, even when the app is not open. This is an essential step for iOS, but it is only one step towards full-device encryption.
Why is iOS Penetration testing necessary?
iOS applications are becoming more and more complex, with several different frameworks, layers of security, and features. This makes it very difficult for anyone to know the vulnerabilities in an iOS application before it is released. iOS penetration testing is used to find security flaws in applications that can be exploited or lead to vulnerabilities.
iOS penetration testing is an essential part of any security audit. This is because of the nature of the devices and the use of the applications. iOS penetration testing allows you to test all the security aspects of the applications and verify that they don’t have any security loopholes. This will enable you to confirm that your application is free from any security vulnerabilities. Some of these vulnerabilities will allow attackers to perform data theft, information leakage, and even sensitive data theft, which can be disastrous for the business.
What is iOS Jailbreaking? Why do you need that?
The word jailbreak has come from the words jail and break. Jailbreaking is a popular term used by Apple users. Jailbreaking refers basically to removing limitations from Apple devices such as iPhones or iPads. Jailbreaking gives you access to features not allowed by Apple. These include installing new third-party apps without having to go through Apple’s App Store, downloading music for free from non-approved sources, or being able to customize your device so that it appears exactly how users want.
To perform an iOS penetration test, you need to jailbreak the phone. Jailbreaking is of multiple types. Let’s understand all of them in detail:
1. Untethered Jailbreak
Untethered jailbreak is a type of Jailbreaking in which the device remains jailbroken even after rebooting the device. This is also known as permanent jailbreak.
2. Tethered Jailbreak
Untethered jailbreak is a type of Jailbreaking in which the device gets back to normal after rebooting the device. This is also known as temporary jailbreak.
3. Semi-tethered jailbreak
A semi-tethered jailbreak, as the name implies, is a jailbreak that relies on a tethered boot to re-patch the kernel. Semi-tethered jailbreaks have traditionally been a popular option for those who would like to have a jailbreak but don’t want to be bothered with a tethered boot. In the past, semi-tethered jailbreaks have been released as “bootstrapping” jailbreaks. This means that after the device boots up, the user would have to run a small app or click a button to re-patch the kernel.
4. Semi-untethered jailbreak
A semi-untethered jailbreak is similar to an untethered jailbreak in that it allows the device to boot up on its own, but it does require that the user run an app on their computer that helps to re-jailbreak the device. semi-untethered jailbreaks are more stable than tethered jailbreaks, but they are still considered to be more complicated to use
Focus Areas for iOS Penetration Testing
iOS penetration testing is performed to examine the security of an application, which involves both the server-side and the client-side components. While doing iOS penetration, four major areas need to be tested.
1. Network Traffic Analysis
Most of the applications communicate with the server using Clear text transmission, such as HTTP, so attackers or hackers can steal the sensitive data in transit.
2. Error and Debug Messages
Most developers ignore error messages, and hackers or attackers use these error messages to understand the internal architecture. To avoid this, developers use standard and short error messages.
3. Local Data Storage
To avoid encryption, iOS developers tend to use plain text to store sensitive data. This attack is also known as Clear Text Storage of sensitive data. This information might include sensitive API Keys, JWT tokens, Credentials, etc.
4. Code Tampering
The term “code modification” refers to the unauthorized modification of executable program code. When the modification is made to malicious code (i.e., code designed to disrupt, destroy, or gain unauthorized access), the resulting software is known as malware. Attackers usually re-sign the applications and publish the malicious version to third-party app marketplaces.
5. Weak authorization and authentication
3A’s of Information Security are Authentication, Authorization, and Accounting. Proper implementation of authentication and authorization is an essential part of every development process. Insufficient access controls lead to various security vulnerabilities that are not usually detected by automated scanners.
iOS Penetration Methodology
iOS penetration testing is more complex than Android penetration due to complex iOS application architecture, but the pentest methodology remains the same.
Step 1: Analysis Phase
In the first phase of ios penetration testing, penetration testers analyze the architecture of the iOS application. In this phase, penetration testers also find the tech stack used to develop the application, information gathering via various open-source tools. If the white box or gray box penetration testing is conducted, the security is also provided with the required documentation and resources to perform iOS penetration testing.
Step 2: Initial Exploitation
In the second phase of iOS penetration testing, the team decompiled the target application. The pentest team plans how to get into the application and a proper way to simulate attacks on the application. Behind the scenes, the team starts automated scanners also to find vulnerabilities in the application.
Step 3: Penetration Testing
In the third phase of a 3rd party penetration testing, the team starts getting into the application. Real-time attacks are launched to understand the behavior of the application. Publicly available CVE’s for known components are also tested in this phase.
Step 4: Reporting
In the fourth phase of iOS penetration testing, the team prepares a summary of attacks that were launched along with a list of CVE’s that were exploited. The report also contains the steps to reproduce and fix the vulnerabilities to help the development team.
5 Best Practices for iOS Application Security
Secure Coding is a must while developing applications nowadays. Following are the top 5 best practices for ios application security:
1. Encrypt all the data
Encryption is one of the essential parts of security for any app. The thing is, encrypting data is not enough. To protect the customers using the iOS application, every single unit of data exchanged over your app must be encrypted. This includes any information that is being sent through your server or your APIs.
2. Avoid Hardcoded Credentials
Hardcoded credentials are the passwords or keys that are hardcoded or embedded in the application’s source code, executable, or library files that are accessible to the end-users. The hardcoded credentials are used in the application to access the network resources or the application server. The hardcoded credentials are usually located in the application’s source code and can be accessed quickly during application inspection.
3. Use Tamper detection techniques
Tampers are used by hackers to alter the code of your application. The aim is to inject their malicious code into your application. This code can be used to steal information from your application or even to take over your servers. Tampering is undoubtedly not a new problem in the IT world, but it has gotten more attention in the last few years after discovering the first high-profile attacks. The most common way of detecting tampering is by looking for the changes in the application’s source code.
4. Code Obfuscation to avoid Reverse Engineering
Code obfuscation is a method of obscuring or scrambling source code – that is, converting source code into some other form – to make it unreadable to humans. Code obfuscation is a preventative measure to avoid hackers reverse engineer your iOS application.
5. Use secure communication protocols (HTTPS)
HTTPS, or Hypertext Transfer Protocol Secure, is a protocol for secure communication over a computer network. The primary goal of HTTPS is to provide privacy and data integrity between two communicating computer systems. It guarantees that the information is not altered or intercepted while in transit between two systems. This protocol is primarily used on the servers for secure transactions.
5 Open Source Tools for iOS Penetration Testing
- Cydia Impactor: Cydia Impactor is a Graphical User Interface (GUI) that lets you install IPA files on iOS devices.
- Frida-ios-dump: Frida ios dump is used to pull a decrypted IPA from a jailbroken device.
- MobSF: Mobile Security Framework (MobSF) is a must-have tool for iOS penetration testing. It’s a static and dynamic binary analyzer capable of quickly enumerating security issues.
- Frida: Frida is a dynamic instrumentation toolkit for developers, reverse-engineers, and security researchers.
- Checkra1n: Checkra1n is a community project to provide a high-quality semi-tethered jailbreak to all, based on the ‘checkm8’ bootrom exploit.
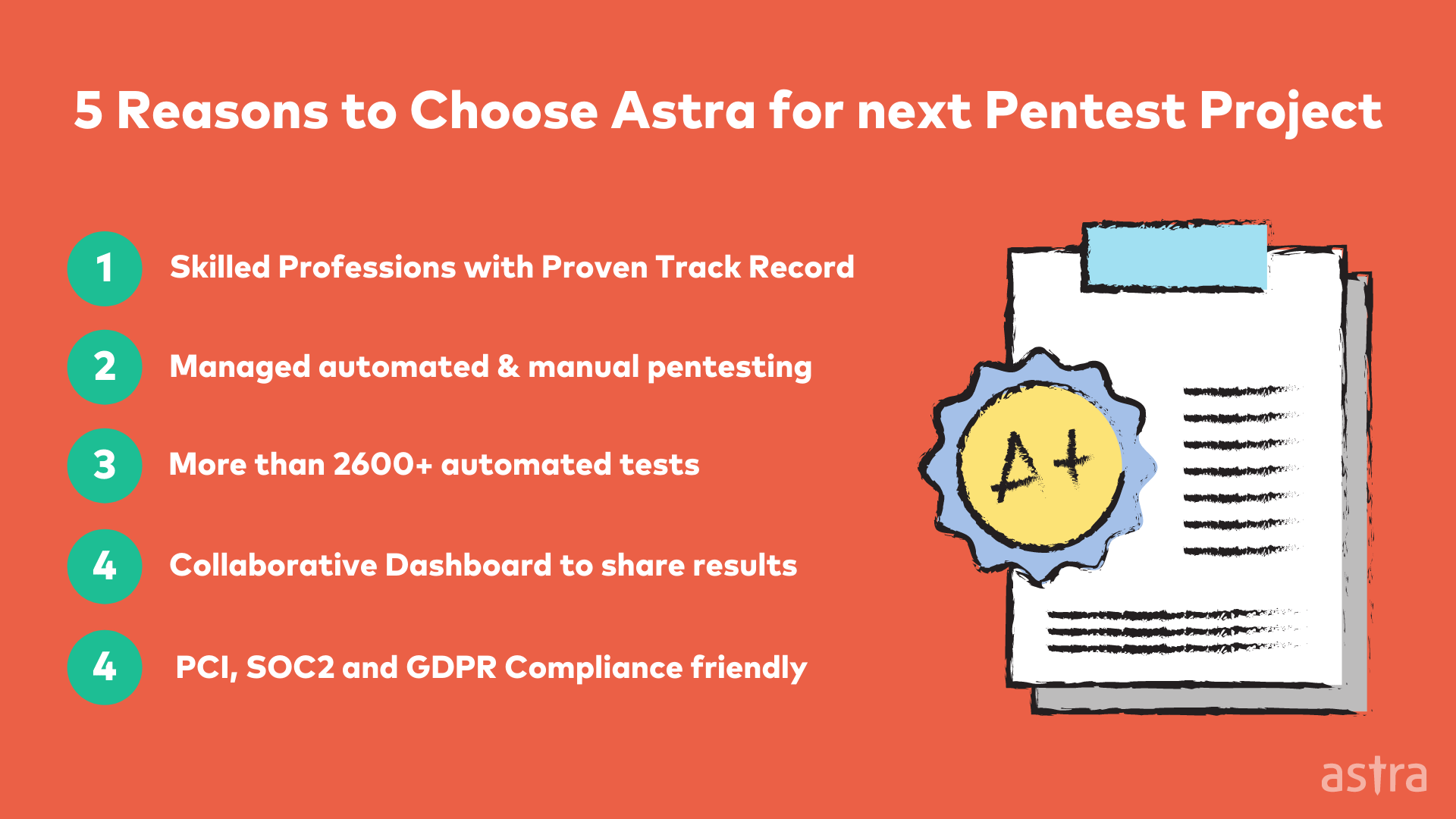
Astra’s Solution to your Insecure iOS Apps
Penetration testing on iOS is more complex than it would be on other platforms. iOS penetration testing is complicated because of the vast range of devices, iOS versions with different security levels, and various vulnerabilities.
Astra is a team of professional security experts that help you with the tedious task of finding security vulnerabilities in your iOS application. We understand the importance of securing your applications, and we make sure that none goes unnoticed. The best part about it is that you don’t need to know all the technical aspects of security testing. All you have to do is provide us with your application, and we will test, discover and report all the risks in your app.
Learn More about Astra’s iOS Penetration Testing Solution
Conclusion
iOS penetration testing is a valuable asset in any organization planning to launch an iOS application or already own an application. By hiring a firm specializing in this type of security, you help your organization protect its valuable data and information. If you are looking to do an IOS penetration testing service, get in touch with the professionals at Astra today.
It is one small security loophole v/s your Android & iOS app.
Get your mobile app audited & strengthen your defenses!